Removal instructions for software detected as "Trojan.Hulk"
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What kind of is "Trojan.Hulk"?
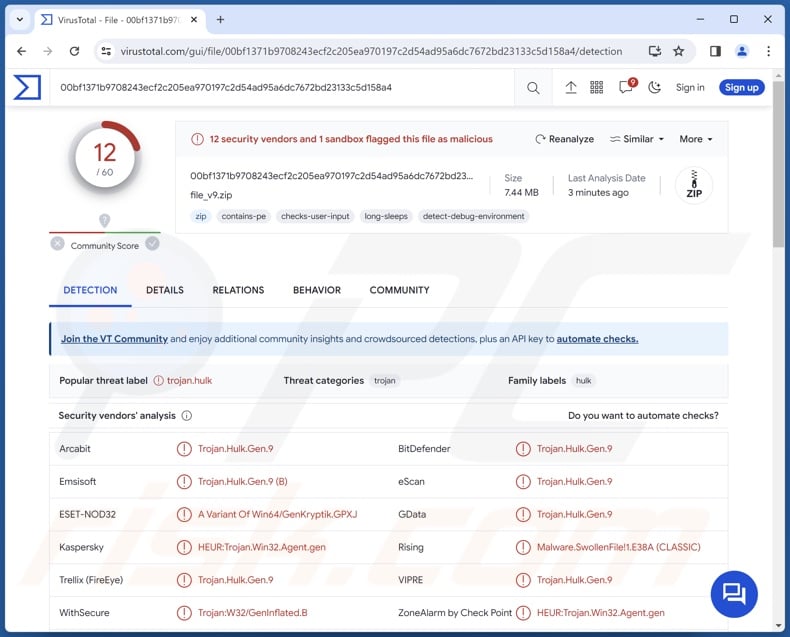
"Trojan.Hulk" is a detection name used by multiple security vendors for identifying rogue installers or illegal software ("cracks") tools, which are bundled with malicious content. Note that other detection names can be used for these setups. Content detected as "Trojan.Hulk" may include unwanted, harmful, and even outright malicious programs.
"Trojan.Hulk" overview
Malicious installation setups that are detected as "Trojan.Hulk" can contain PUAs, adware, browser hijackers, trojans, ransomware, and other malware. It is noteworthy that these setups may include multiple pieces of undesirable and dangerous software.
To elaborate on these program classifications – unwanted software such as PUAs, fake anti-viruses, adware, and browser hijackers are typically presented as legitimate and useful tools.
This software may also offer a wide variety of "handy" features, e.g., system protection, media playing, file format conversion, easy access to online content, website dark mode, and many, many others. In most cases, the functionalities do not work as promised or are utterly nonoperational. Yet even if a piece of software works as advertised – that is not definitive proof of either legitimacy or safety.
Unwanted software usually has harmful capabilities. Adware is designed to display advertisements (e.g., pop-ups, banners, coupons, overlays, etc.) on visited websites and/or other interfaces. This third-party graphical content primarily endorses online scams, unreliable/hazardous software, and even malware. When clicked on, some of these adverts can execute scripts to perform stealthy downloads/installations.
Browser hijackers modify browser settings to generate redirects landing on fake search engines. These websites cannot provide search results, so they lead to genuine Internet search sites (e.g., Bing, Google, Yahoo, etc.). In the rare cases where illegitimate search engines can generate search results – they are inaccurate and may include sponsored, deceptive, and potentially malicious content.
Most unwanted apps and extensions (e.g., adware, browser hijackers, etc.) have data-tracking abilities. This information can then be sold to third-parties or otherwise abused for profit.
Installers detected as "Trojan.Hulk" can include malware. They could contain trojans, and "trojan" is a broad term defining malicious programs with various capabilities.
This umbrella term includes: backdoors – that open an avenue for further infection; loaders – that download/install additional malicious programs/content; injectors – that inject malicious code to programs/processes; grabbers – that exfiltrate system/user files; stealers – that extract/exfiltrate data from systems or installed apps; spyware – that records content (e.g., audio/video via microphones/cameras, live-streams desktops, etc.); keyloggers – that record keystrokes; clippers – that replace clipboard content; and others.
Ransomware is another popular malware type. Programs within this classification encrypt files and/or lock the device's screen to demand ransoms for its decryption or access recovery.
To summarize, the presence of software detected as "Trojan.Hulk" on devices can lead to multiple system infections, data loss, severe privacy issues, financial losses, and identity theft.
| Name | Trojan.Hulk virus |
| Threat Type | PUA (Potentially Unwanted Application), Adware, Browser Hijacker, Redirect, Search Hijacker, Trojan, Password-stealing Virus, Banking Malware, Spyware. |
| Detection Names | Avast (Win32:AdwareX-gen [Adw]), Combo Cleaner (Gen:Variant.Strictor.287102), ESET-NOD32 (A Variant Of Win32/Kryptik.HVKA), Kaspersky (HEUR:Trojan.Win32.Ekstak.gen), Microsoft (Trojan:Win32/Sabsik.FL.B!ml), Full List Of Detections (VirusTotal) |
| Symptoms | Seeing advertisements not originating from the sites you are browsing. Intrusive pop-up ads. Rogue redirects. Changed browser settings. Decreased Internet browsing speed. Diminished system performance. |
| Distribution methods | Torrenting, malicious online advertisements, social engineering, software 'crack' sites, spam emails/posts. |
| Damage | Decreased computer performance, browser tracking - privacy issues, stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Examples of content detected as "Trojan.Hulk"
Rogue installation setups and software "cracking" tools that include malicious content could be detected under other names aside from "Trojan.Hulk". For example, program "cracks" are often identified as "HackTool:Win32/Crack".
The following are a few examples of content detected as "Trojan.Hulk": Web Resource Viewer, Gamelogger for Windows (PUA); Magnifying Glass Zoom, Skip Those Ads (adware); Zodiac Search, Volume Extra (browser hijackers), and SoundCloud virus, DataEngine (malware).
How did "Trojan.Hulk" infiltrate my computer?
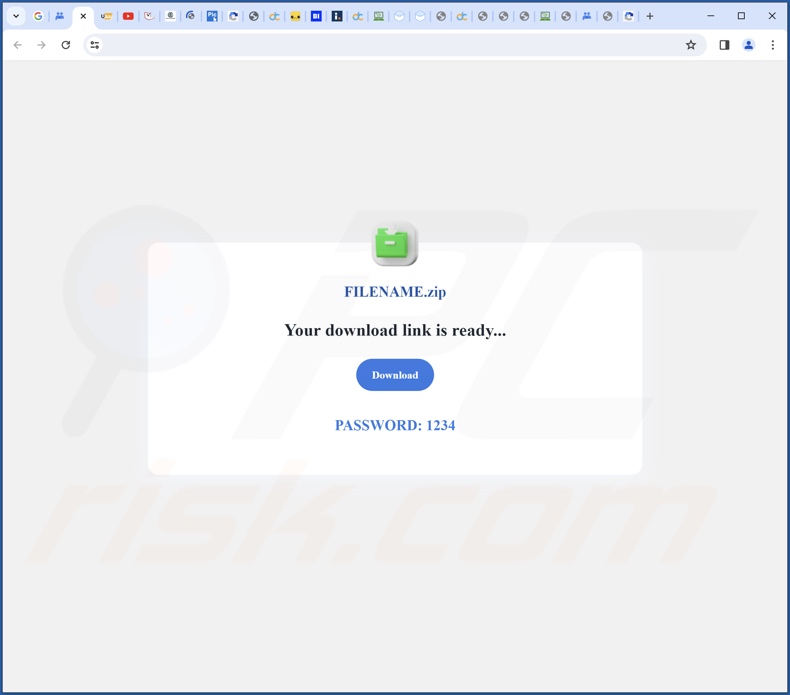
Content detected as "Trojan.Hulk" can be acquired from a variety of untrustworthy download channels, such as deceptive promotional webpages, freeware and free file-hosting websites, Peer-to-Peer sharing networks (e.g., Torrent clients, eMule, Gnutella, etc.), and other third-party sources.
Online scams, malvertising, and spam (e.g., browser notifications, emails, DMs/PMs, SMSes, social media posts, etc.) can also be utilized in the promotion. It is pertinent to mention that deceptive webpages can be accessed via redirects generated by sites using rogue advertising networks, mistyped URLs, intrusive ads, and adware.
How to avoid installation of content detected as "Trojan.Hulk"?
Caution is key to preventing harmful content like "Trojan.Hulk" from infiltrating devices. It is essential to be vigilant when browsing since fake and malicious material hosted on the Web typically appears legitimate and harmless. We advise against opening attachments or links found in suspect/irrelevant mail, as they can be infectious.
Another recommendation is to download only from official and trustworthy sources. Additionally, all programs must be activated and updated using genuine functions/tools, as illegal activation tools ("cracks") and third-party updates can contain malware.
We must emphasize that having a dependable anti-virus installed and kept up-to-date is crucial to device/user safety. Security software must be used to run regular system scans and to remove detected threats and issues. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Screenshot of a deceptive website used to promote an installer detected as "Trojan.Hulk":
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is Trojan.Hulk?
- STEP 1. Uninstall unwanted applications using Control Panel.
- STEP 2. Remove malicious extensions from Google Chrome.
- STEP 3. Remove hijacker homepage and default search engine from Mozilla Firefox.
- STEP 4. Remove rogue redirects from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Unwanted software removal:
Windows 11 users:
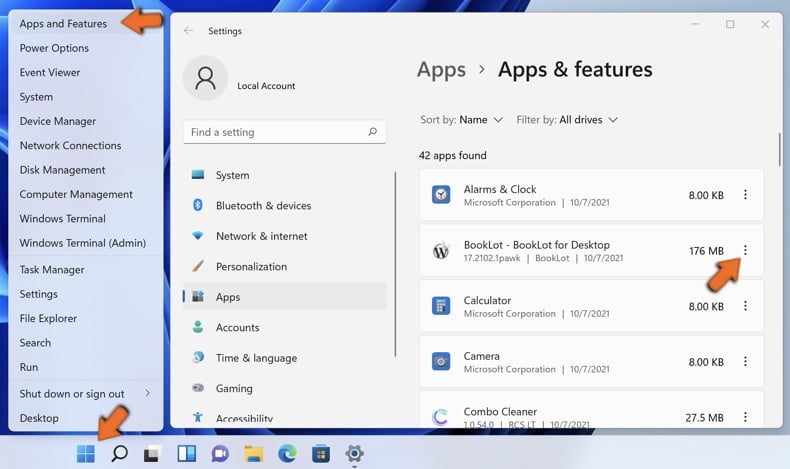
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
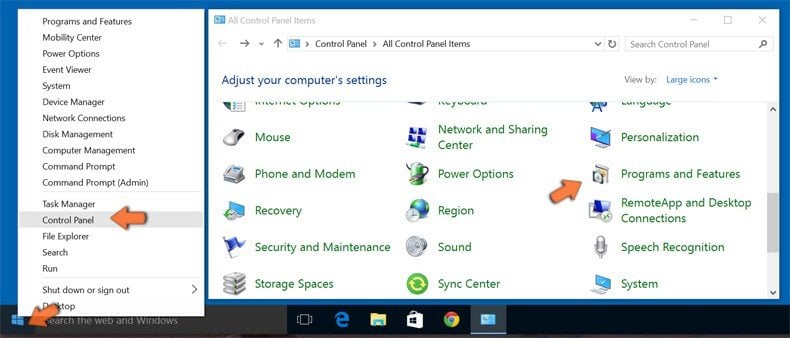
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.
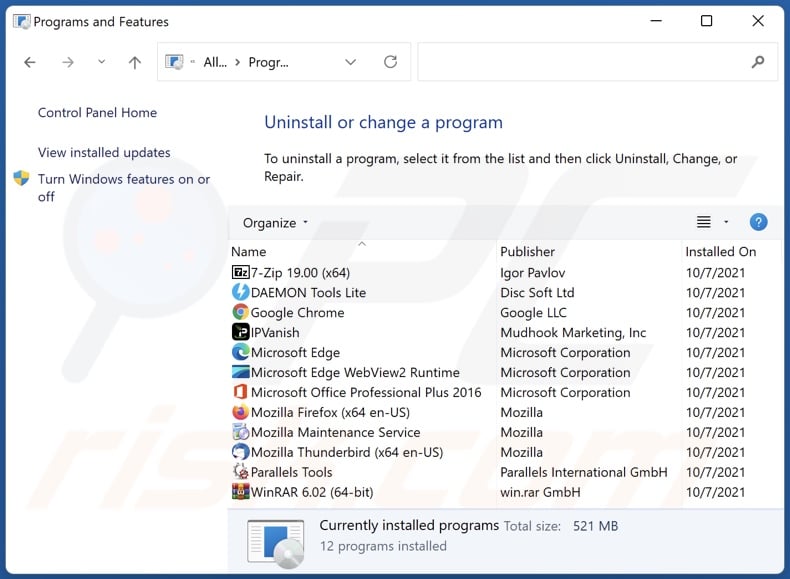
In the uninstall programs window: look for any recently installed suspicious applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the potentially unwanted applications, scan your computer for any remaining unwanted components. To scan your computer, use recommended malware removal software.
Malicious extension removal from Internet browsers:
Video showing how to remove browser redirects:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
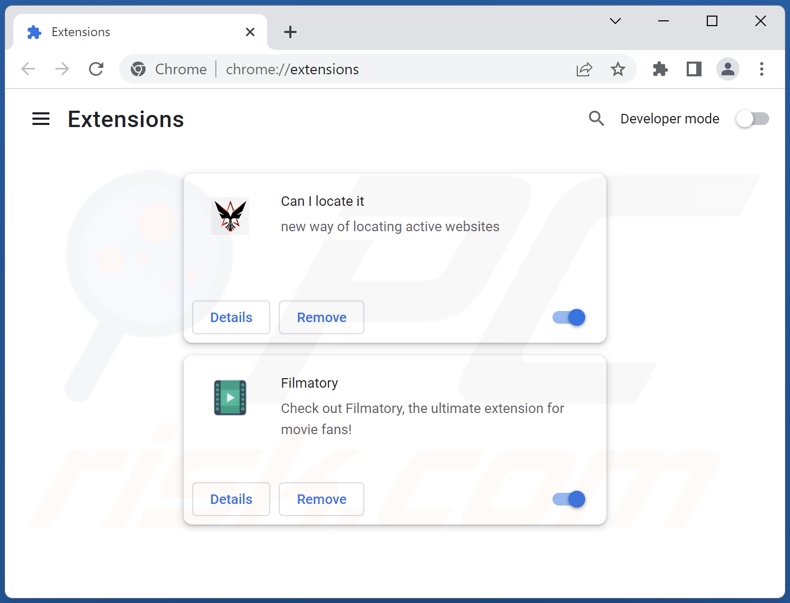
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate recently-installed suspicious extensions, select these entries and click "Remove".
Change your homepage:
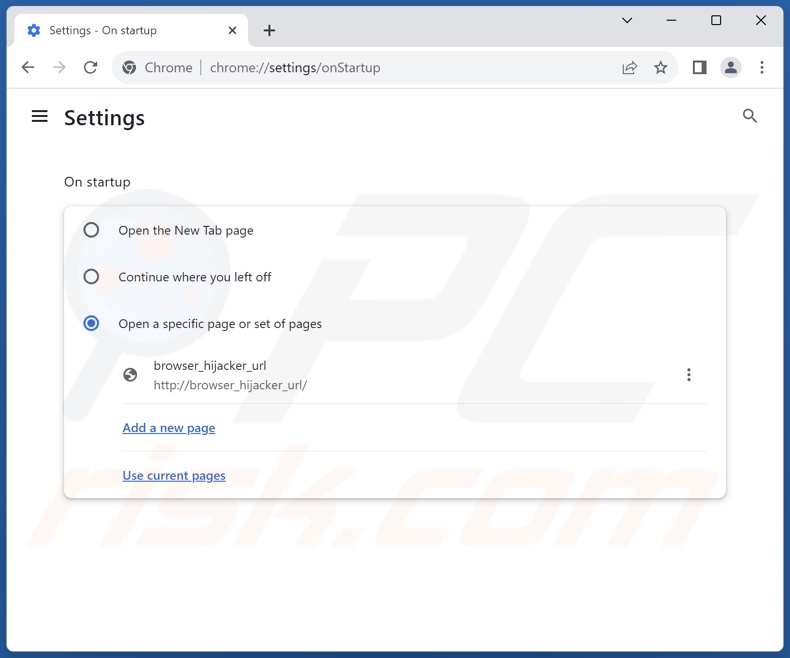
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Settings". In the "On startup" section, disable the suspect extension, look for the promoted URL below the "Open a specific or set of pages" option. If present click on the three vertical dots icon and select "Remove".
(at the top right corner of Google Chrome), select "Settings". In the "On startup" section, disable the suspect extension, look for the promoted URL below the "Open a specific or set of pages" option. If present click on the three vertical dots icon and select "Remove".
Change your default search engine:
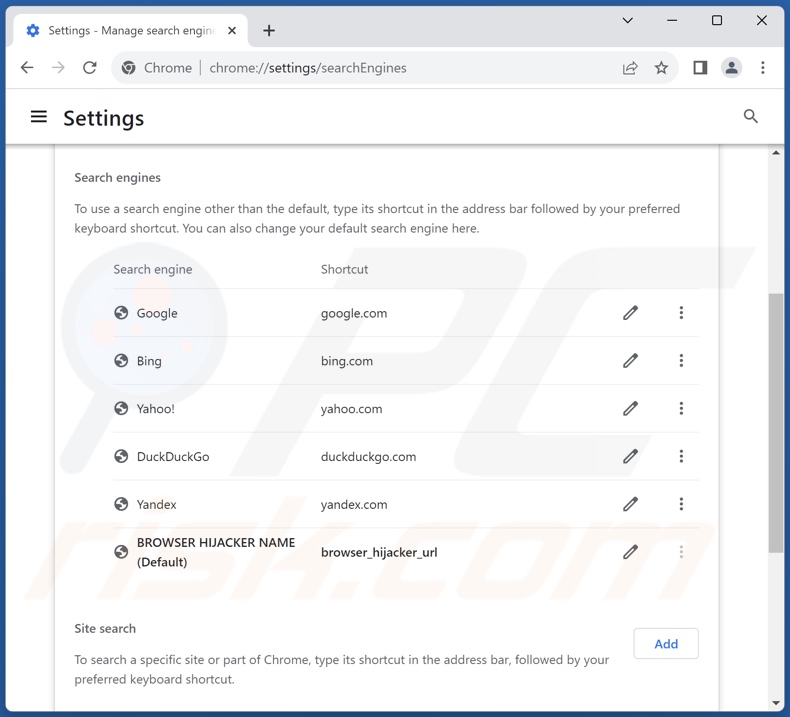
To change your default search engine in Google Chrome: Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Settings", in the "Search engine" section, click "Manage search engines...", in the opened list look for the promoted URL, when located click the three vertical dots near this URL and select "Delete".
(at the top right corner of Google Chrome), select "Settings", in the "Search engine" section, click "Manage search engines...", in the opened list look for the promoted URL, when located click the three vertical dots near this URL and select "Delete".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
Optional method:
If you continue to have problems with removal of the trojan.hulk virus, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
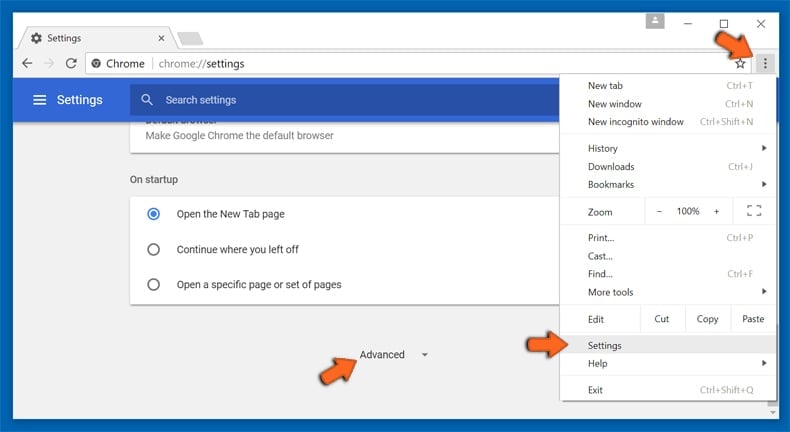
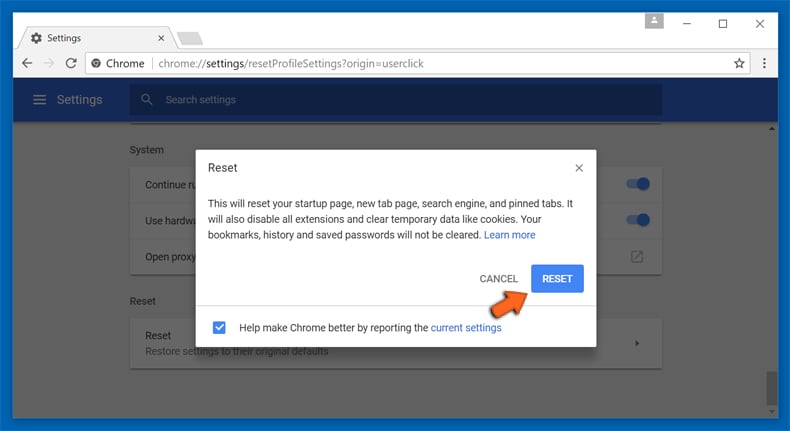
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
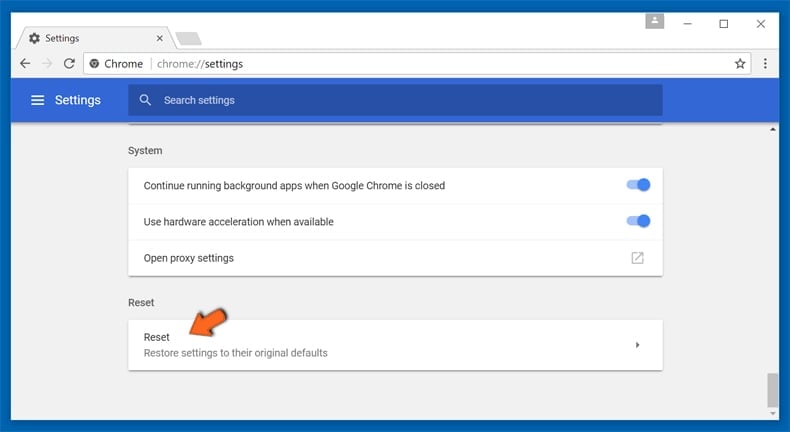
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
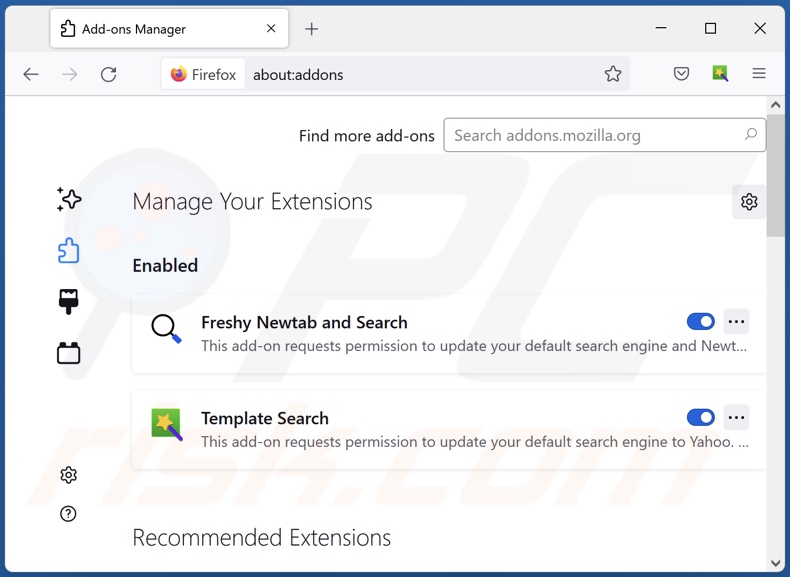
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate recently-installed suspicious extensions, click on the three dots and then click "Remove".
Change your homepage:
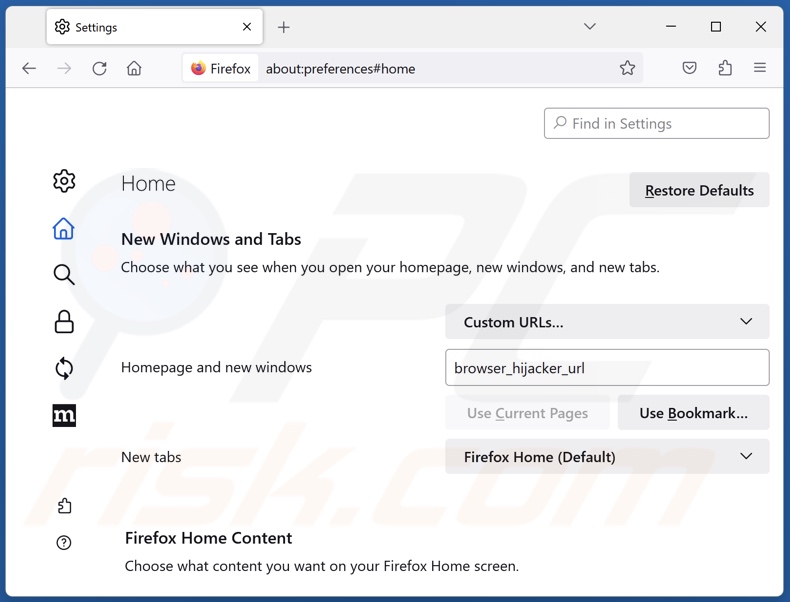
To reset your homepage, click the Firefox menu ![]() (at the top right corner of the main window), then select "Settings", in the opened window disable the suspect extension, remove the promoted URL and enter your preferred domain, which will open each time you start Mozilla Firefox.
(at the top right corner of the main window), then select "Settings", in the opened window disable the suspect extension, remove the promoted URL and enter your preferred domain, which will open each time you start Mozilla Firefox.
Change your default search engine:
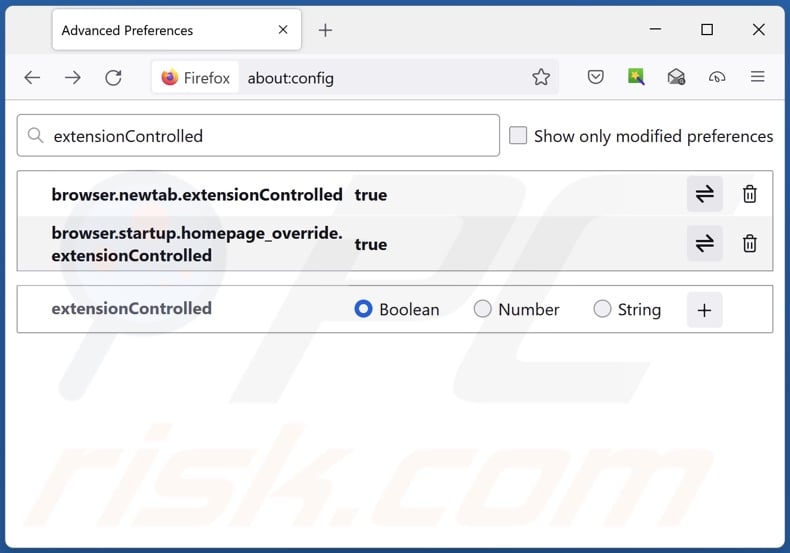
In the URL address bar, type "about:config" and press Enter. Click "Accept the Risk and Continue".
In the search filter at the top, type: "extensionControlled". Set both results to "false" by either double-clicking each entry or clicking the ![]() button.
button.
Optional method:
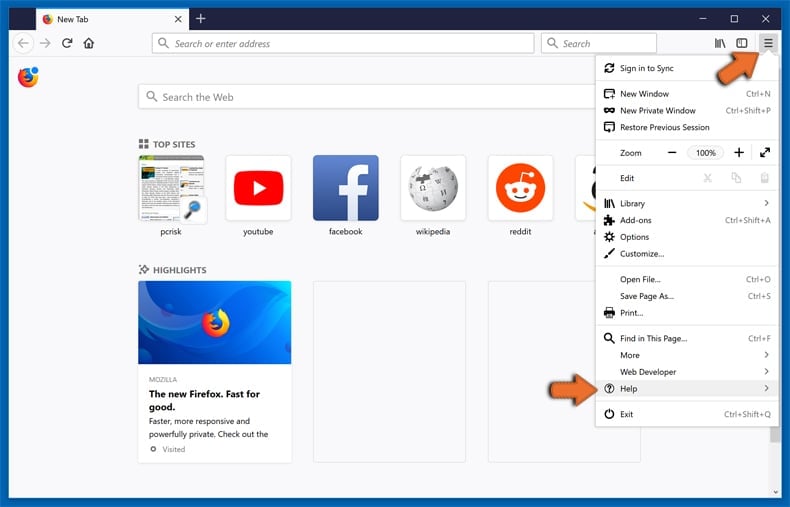
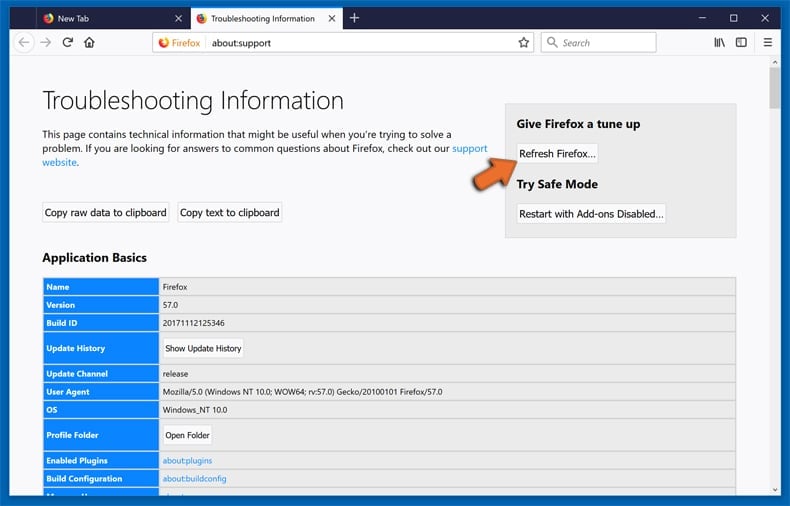
Computer users who have problems with trojan.hulk virus removal can reset their Mozilla Firefox settings.
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
Select Troubleshooting Information.
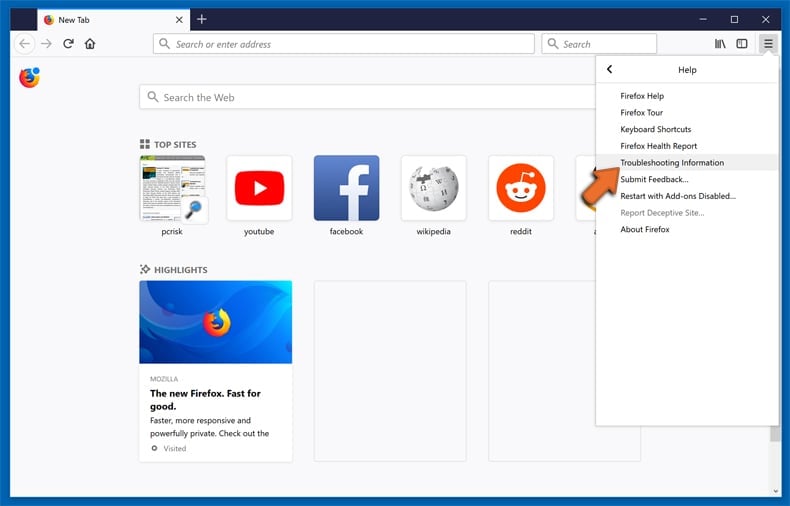
In the opened window, click the Refresh Firefox button.
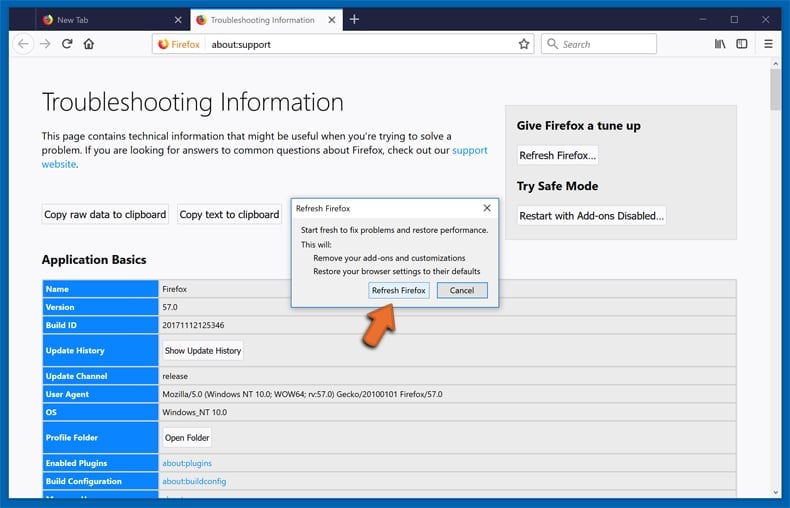
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
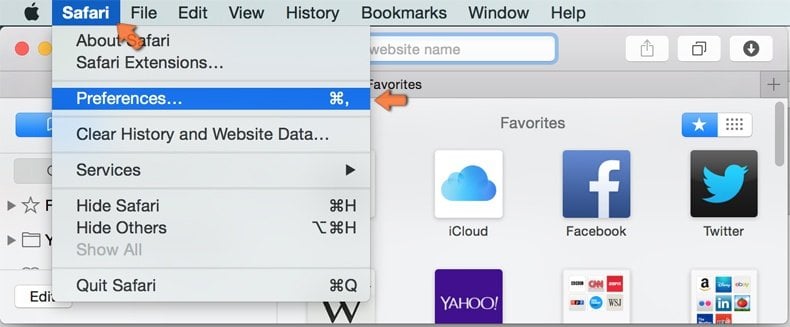
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
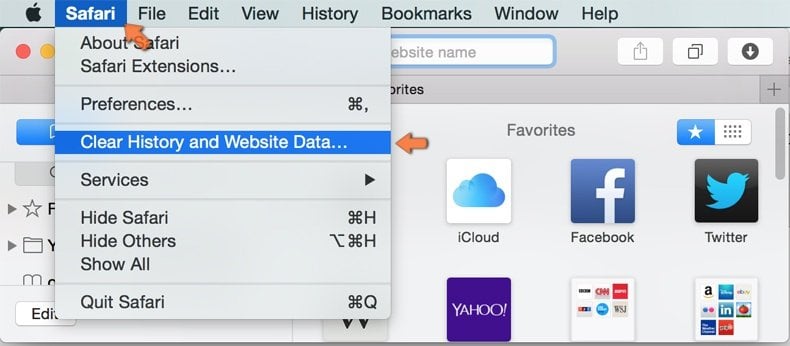
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
In the opened window select all history and click the Clear History button.

 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
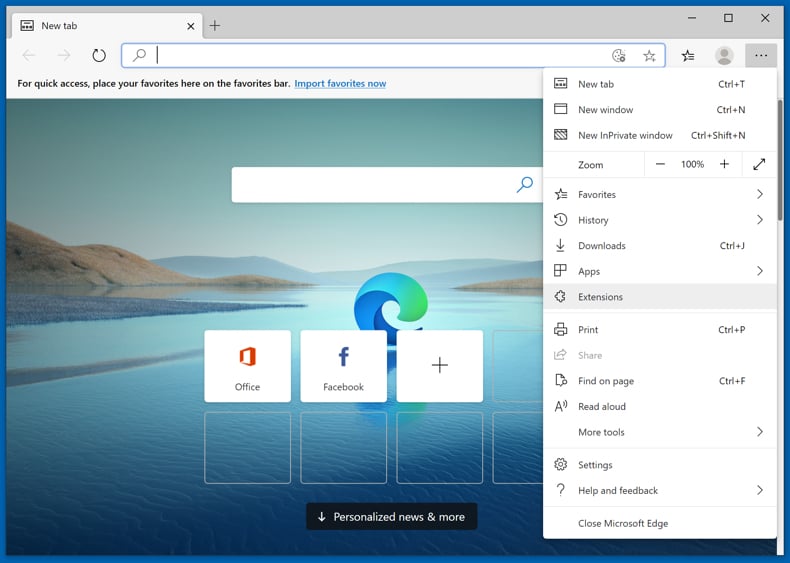
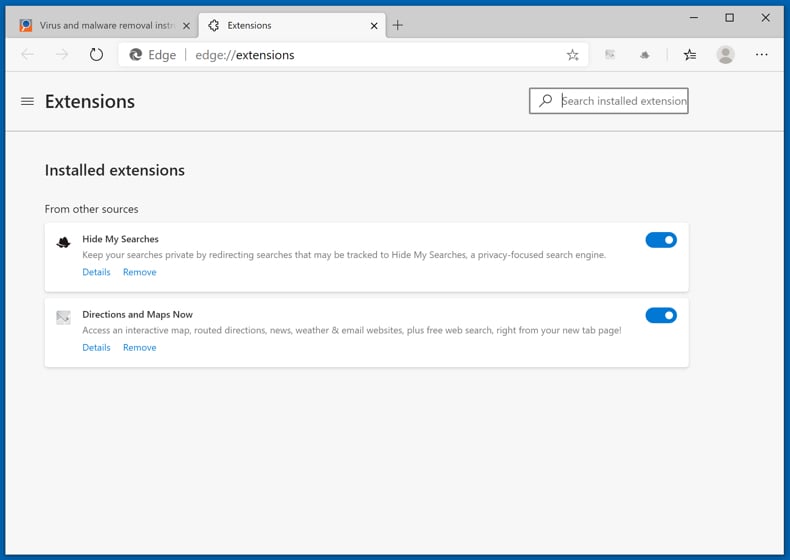
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
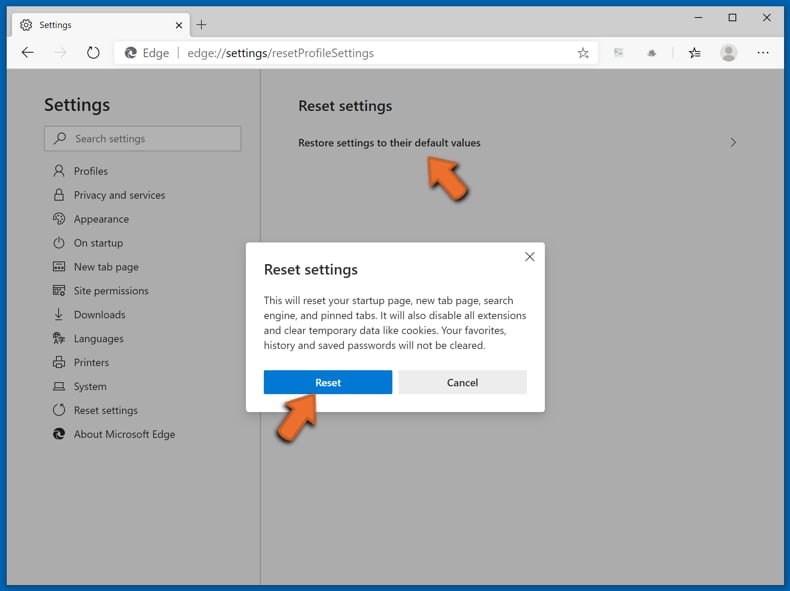
Optional method:
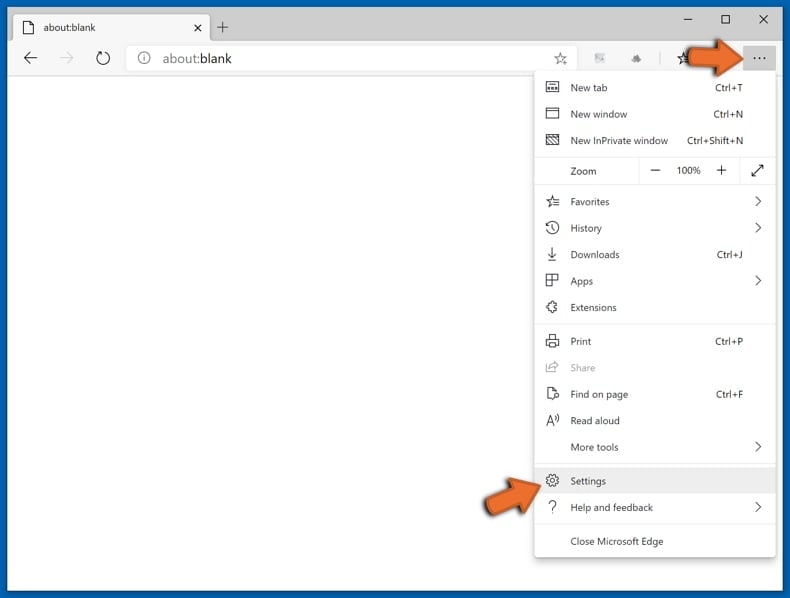
If you continue to have problems with removal of the trojan.hulk virus, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
In the opened settings menu select Reset settings.
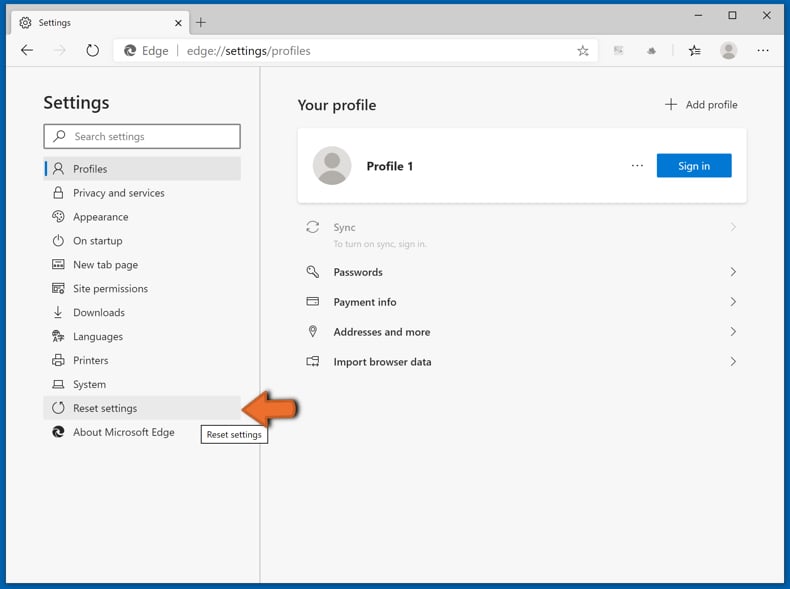
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Frequently Asked Questions (FAQ)
What is "Trojan.Hulk"?
"Trojan.Hulk" is a detection name used by many security engines to identify rogue installers or illegal program activation ("cracking") tools, which include unwanted/malicious content.
What are the biggest issues that "Trojan.Hulk" can cause?
The threats posed by unwanted/malicious software depend on its capabilities. Installation setups detected as "Trojan.Hulk" may include PUAs, adware, browser hijackers, trojans, ransomware, and other harmful programs. The greatest dangers are posed by sophisticated malware, including multiple system infections, data loss, serious privacy issues, financial losses, and identity theft.
What is the purpose of "Trojan.Hulk"?
"Trojan.Hulk" setups include unwanted/malicious programs, which are typically used to generate revenue. Profit could be made through the promotion of in-app purchases, displayed ads, caused redirects, or sale/abuse of collected data.
It is noteworthy that malware may generate revenue through complex processes, but it might also be used for other purposes. Malware attacks can be motivated by financial gain, cyber criminals' amusement, realization of personal grudges, process disruption (e.g., websites, services, etc.), and political/geopolitical reasons.
How did "Trojan.Hulk" infiltrate my computer?
Content detected as "Trojan.Hulk" is primarily distributed through dubious download channels (e.g., freeware and free file-hosting sites, P2P sharing networks, etc.), online scams, spam (e.g., social media posts, emails, PMs/DMs, SMSes, browser notifications), and malvertising.
Will Combo Cleaner protect me from content under the "Trojan.Hulk" detection?
Yes, Combo Cleaner is capable of detecting and eliminating all manner of threats. It must be stressed that since high-end malware usually hides deep within systems – running a full system scan is paramount.
▼ Show Discussion