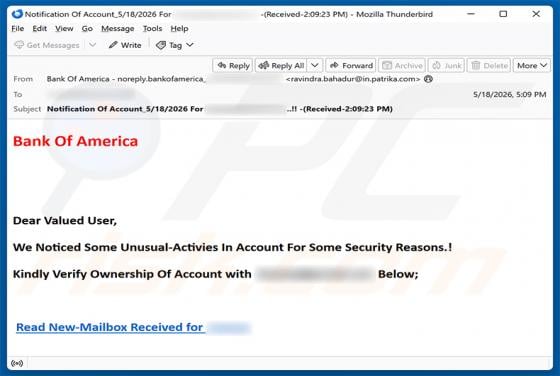
Bank Of America - Unusual Activities In Account Email Scam
We have inspected this email and found that it is a phishing scam. While it poses as a security alert from Bank of America, the link it contains leads to a fraudulent page intended to steal email account credentials rather than banking details. Recipients should ignore and delete the email to avoi