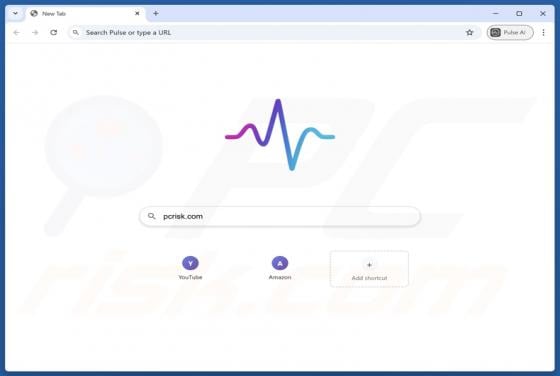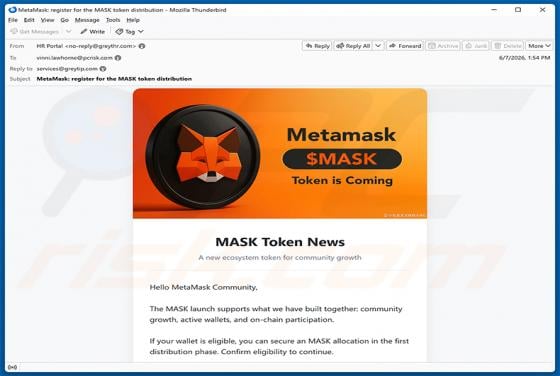
MetaMask ($MASK) Token Allocation Email Scam
We have inspected this email and found that it is a phishing scam impersonating MetaMask. The message announces the launch of a so-called MASK token and invites recipients to register their wallet to secure an allocation. The scheme is designed to steal cryptocurrency wallet recovery phrases and d