Removal instructions for the EuphractusSexcinctus malicious extension
AdwareAlso Known As: EuphractusSexcinctus unwanted browser extension
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of software is EuphractusSexcinctus?
EuphractusSexcinctus is the name of a malicious browser extension. Our researchers discovered this piece of software during a routine investigation of untrustworthy websites. After analyzing the extension, we determined that it is capable of modifying browsers and collecting sensitive user information.
It is pertinent to mention that installation setups like the one used to promote EuphractusSexcinctus are commonly bundled with additional unwanted and potentially dangerous software.

EuphractusSexcinctus overview
EuphractusSexcinctus can make alterations to browsers' apps, extensions, themes, and other settings. This allows the extension to manage and modify browsers' appearance and behavior. How these capabilities are applied may vary.
Furthermore, EuphractusSexcinctus abuses the "Managed by your organization" feature (in Google Chrome and Microsoft Edge) to gain further control of the browser and ensure persistence by complicating its removal.
It is worth mentioning that this malicious extension might be used to detect existing vulnerabilities and exploit them to cause further infections.
What is more, EuphractusSexcinctus has data-tracking functionalities. Information of interest may include: visited URLs, viewed webpages, searched queries, Internet cookies, usernames/passwords, personally identifiable details, finance-related data, and so on. This vulnerable information can then be monetized via sale to third-parties.
To summarize, the presence of software like EuphractusSexcinctus on devices may result in system infections, severe privacy issues, financial losses, and even identity theft.
| Name | EuphractusSexcinctus unwanted browser extension |
| Threat Type | Malicious Extension, Unwanted Extension |
| Browser Extension(s) | EuphractusSexcinctus |
| Detection Names (installer) | Kaspersky (Not-a-virus:HEUR:AdWare.Win32.WebCo), Rising (Adware.WebCompanion!8.171BF (CLOUD)), Varist (ABRisk.WYZS-3), Zillya (Adware.WebCompanion.Win32.23), ZoneAlarm by Check Point (Not-a-virus:HEUR:AdWare.Win32.WebCo), Full List Of Detections (VirusTotal) |
| Symptoms | The "Managed by your organization" feature is activated in Chrome or Edge browser, decreased Internet browsing speed, your computer becomes slower than usual. |
| Distribution Methods | Dubious websites, malicious installers, deceptive pop-up ads, free software installers (bundling), torrent file downloads. |
| Damage | Decreased computer performance, browser tracking - privacy issues, possible additional malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similar software examples
SusScrofa, HostaSieboldiana, PelargoniumHortorum, and DelphiniumElatum are merely a few examples of extensions similar to EuphractusSexcinctus.
Data-tracking abilities are not the only common harmful functionalities possessed by rogue browser extensions. Other standard features include displaying advertisements (adware) and generating redirects (browser hijackers).
Malicious browser extensions may appear legitimate and innocuous. They can also offer a broad range of handy and advantageous functions. However, these functionalities seldom work as advertised, and in most cases – they do not work at all.
It must be stressed that even if a piece of software operates exactly as indicated by its promotional material – that is not a guarantee of legitimacy or safety.
How did EuphractusSexcinctus install on my computer?
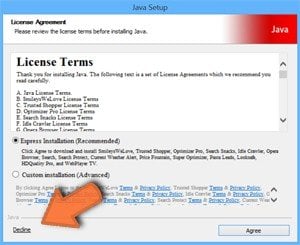
We downloaded an installer containing EuphractusSexcinctus from a dubious software-promoting webpage. Sites that push such extensions can appear legitimate or use false claims to lure visitors into download/installation (online scams).
Most users access these pages via redirects caused by websites employing rogue advertising networks, misspelled URLs, intrusive ads, spam browser notifications, or installed adware.
"Bundling" – the marketing technique that involves packing regular program installation setups with unwanted/malicious supplements – is also used to distribute such software.
The threat of unintentionally allowing bundled content into the system is increased by downloading from dubious channels (e.g., freeware and free file-hosting sites, Peer-to-Peer sharing networks, etc.) and by treating installations with negligence (e.g., ignoring terms, skipping sections, using "Easy/Express" settings, etc.).
Additionally, rogue software is proliferated by intrusive adverts. Some of these advertisements can be triggered (i.e., by being clicked) to execute scripts that perform stealthy downloads/installations.
How to avoid installation of unwanted software?
We strongly recommend researching software and downloading it only from official/verified sources. Furthermore, installation processes must be treated with caution. Therefore, we advise reading terms, inspecting available options, using the "Custom/Advanced" settings, and opting out of all additional apps, extensions, etc.
Another recommendation is to be careful while browsing since fake and dangerous online content usually appears genuine and harmless. For example, despite their ordinary/innocuous appearance – intrusive ads redirect to highly questionable websites (e.g., scam-promoting, gambling, adult dating, pornography, etc.).
In case of continuous encounters with such adverts/redirects, inspect the system and immediately remove all suspicious applications and browser extensions/plug-ins. If your computer is already infected with EuphractusSexcinctus, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate this rogue software.
Screenshot of a deceptive website used to promote EuphractusSexcinctus:

Screenshot of EuphractusSexcinctus extension's detailed information:

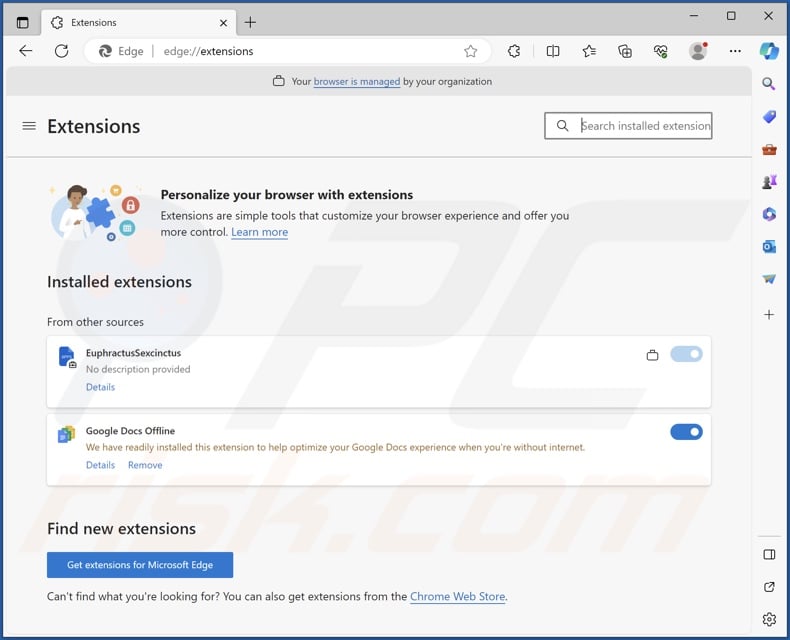
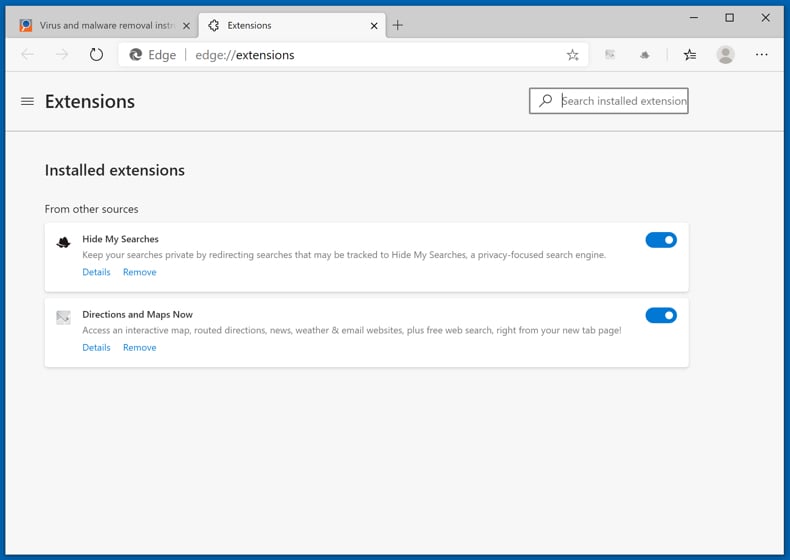
Screenshot of EuphractusSexcinctus installed on the Microsoft Edge browser:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is EuphractusSexcinctus?
- STEP 1. Uninstall unwanted applications using Control Panel.
- STEP 2. Remove rogue extensions from Google Chrome.
- STEP 3. Remove rogue extensions from Mozilla Firefox.
- STEP 4. Remove rogue extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Unwanted software removal:
Windows 11 users:
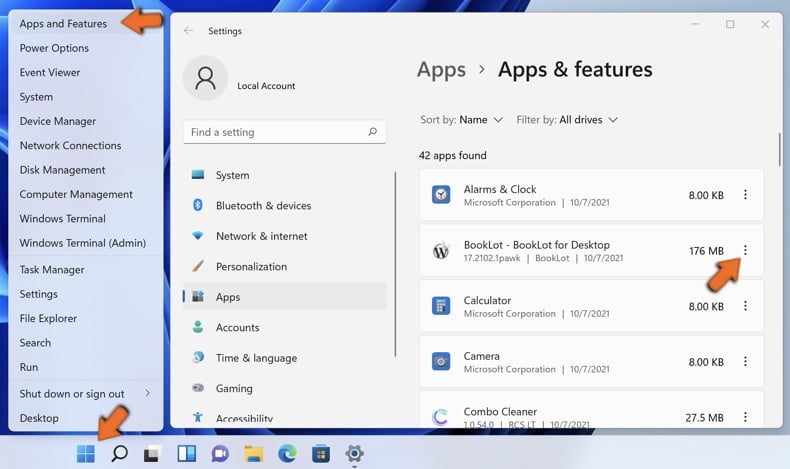
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
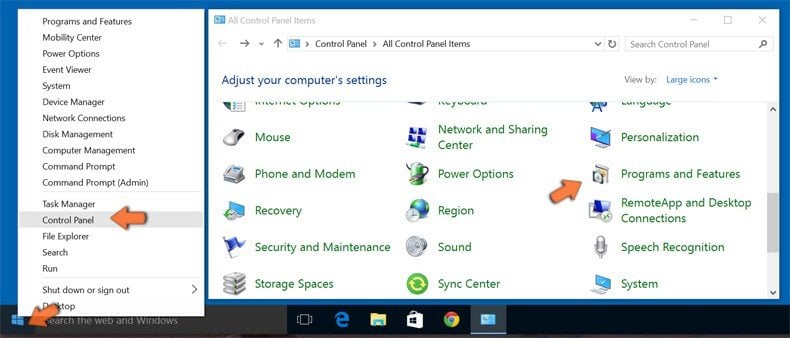
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.

In the uninstall programs window, look for any unwanted applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the unwanted applications, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove rogue extensions from Internet browsers:
Video showing how to remove potentially unwanted browser add-ons:
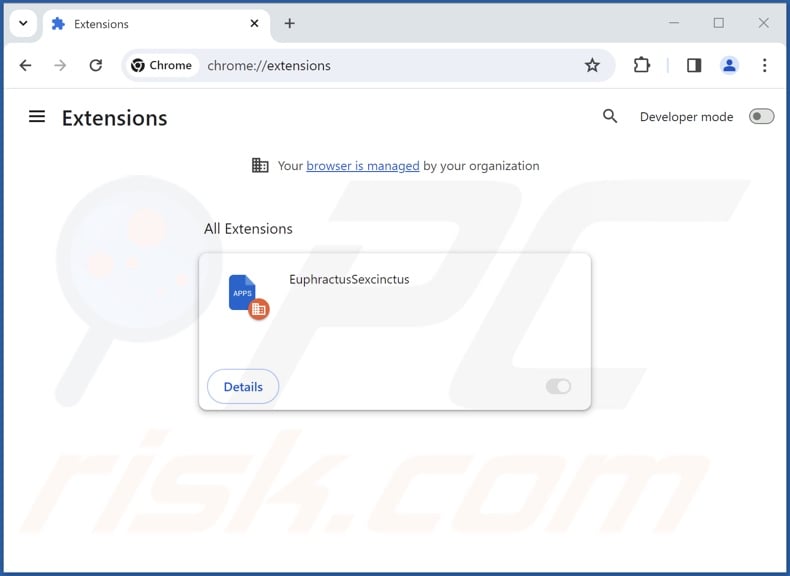
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:

Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate "EuphractusSexcinctus" and all other recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate "EuphractusSexcinctus" and all other recently-installed suspicious extensions, select these entries and click "Remove".
Optional method:
If you continue to have problems with removal of the euphractussexcinctus unwanted browser extension, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
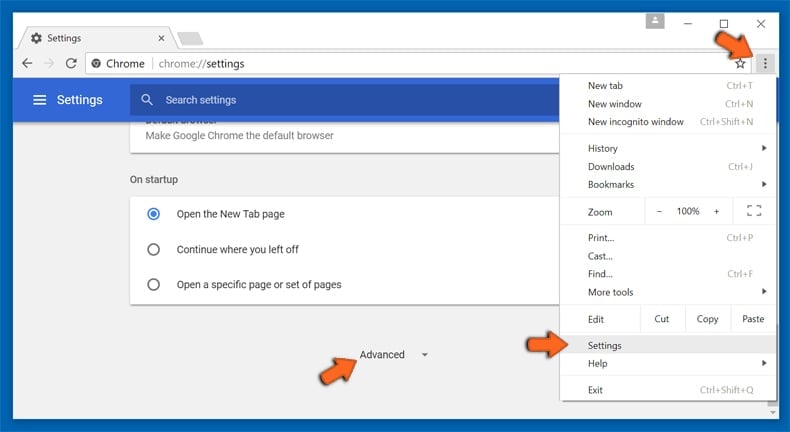
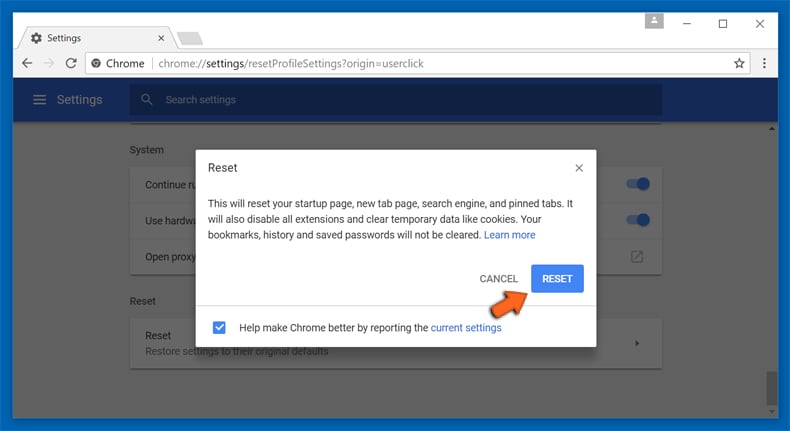
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
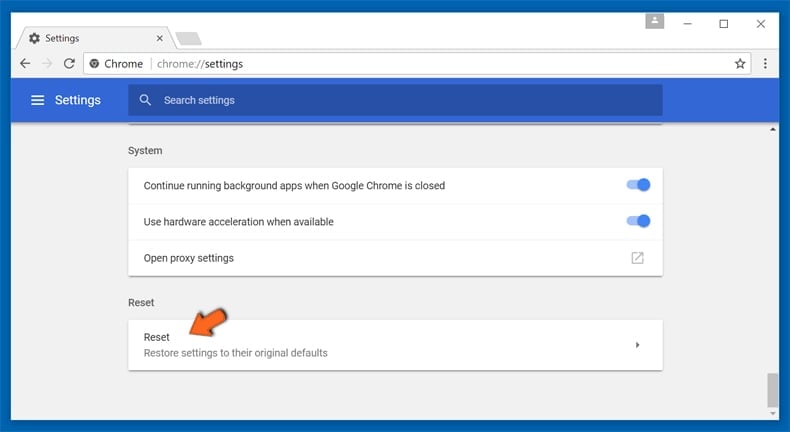
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
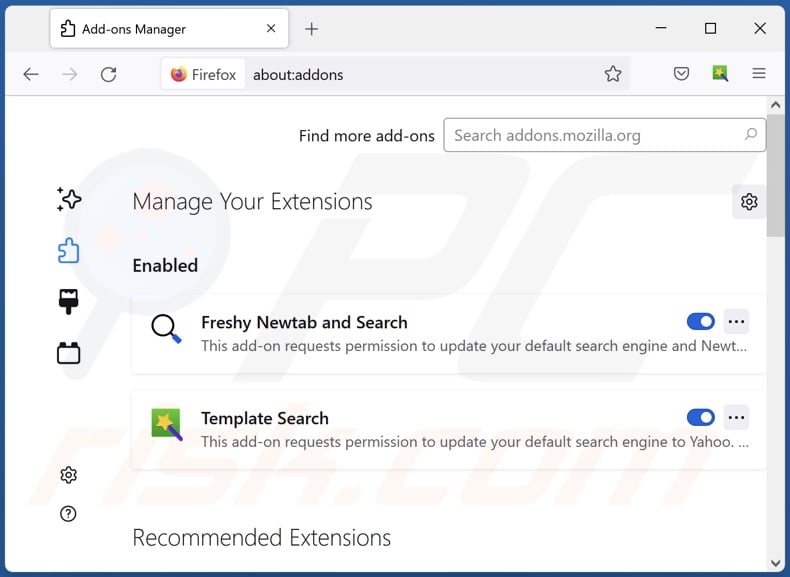
 Remove malicious plugins from Mozilla Firefox:
Remove malicious plugins from Mozilla Firefox:
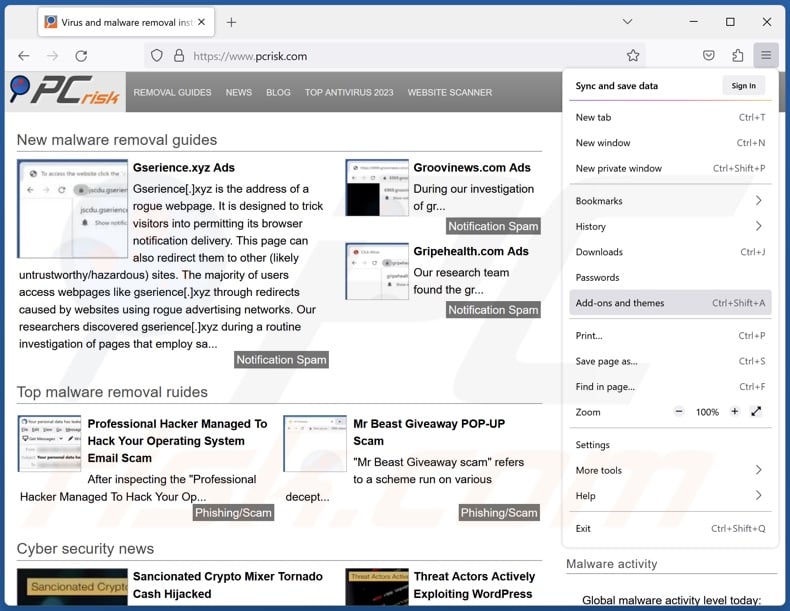
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate recently-installed suspicious extensions, click on the three dots and then click "Remove".
Optional method:
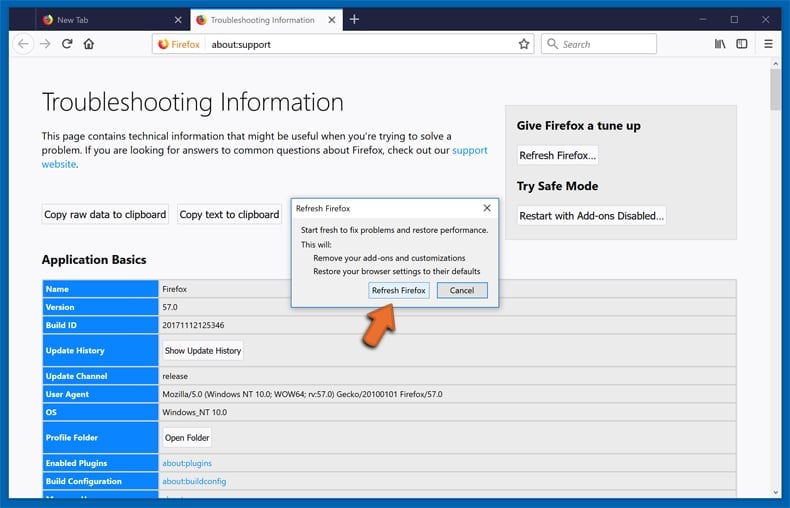
Computer users who have problems with euphractussexcinctus unwanted browser extension removal can reset their Mozilla Firefox settings.
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
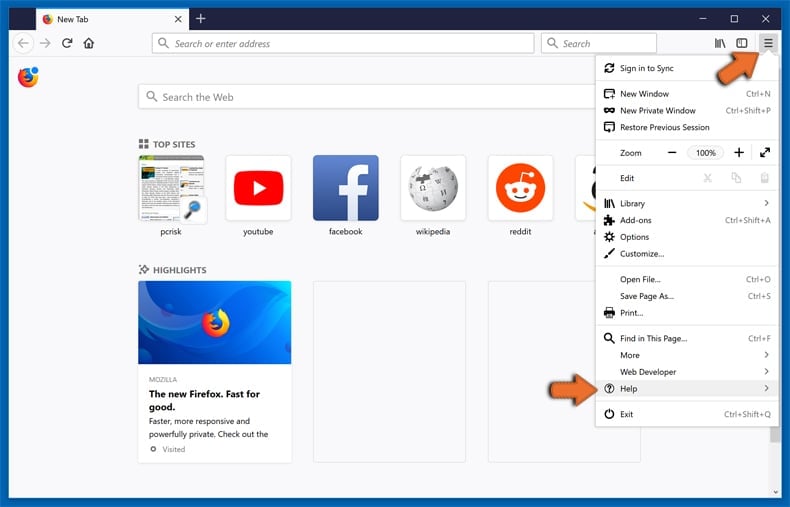
Select Troubleshooting Information.
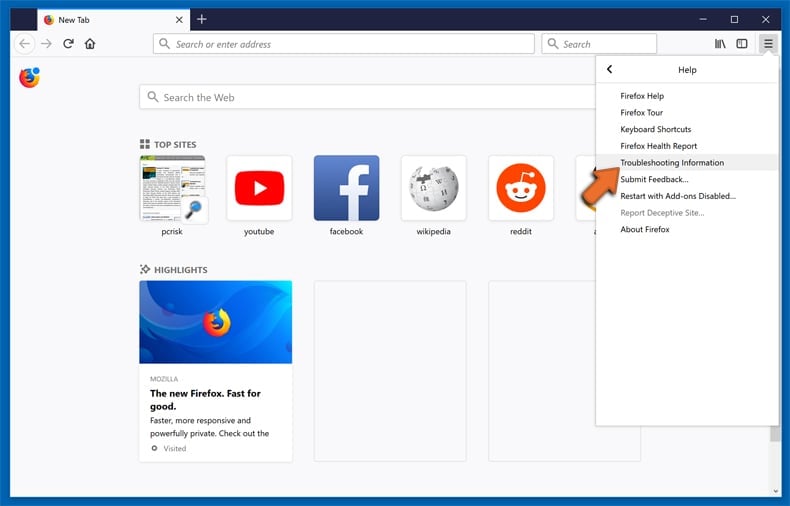
In the opened window, click the Refresh Firefox button.
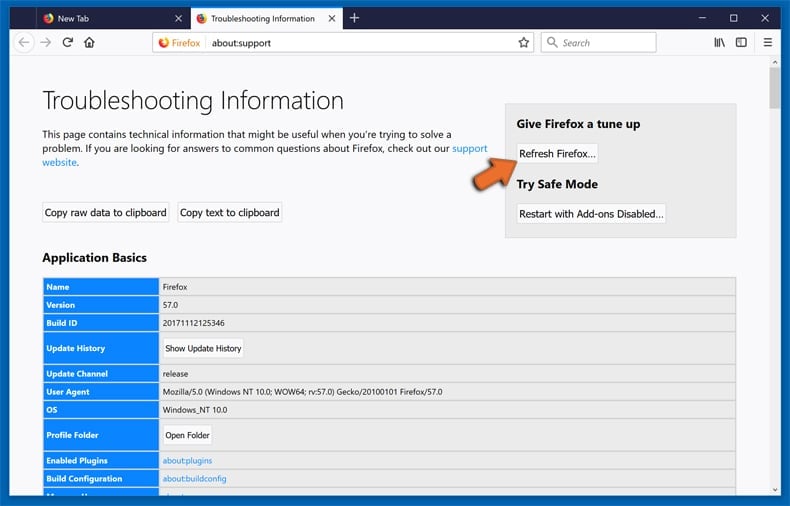
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
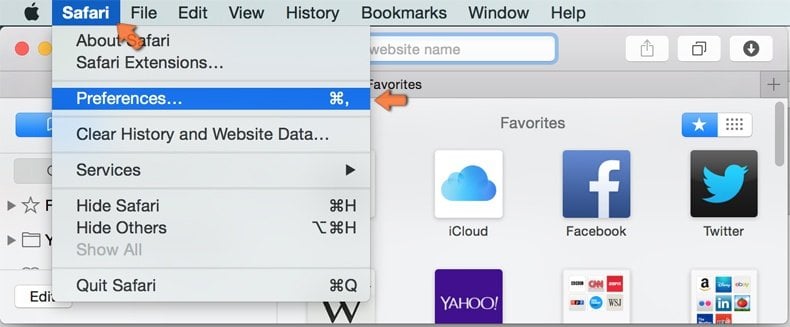
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
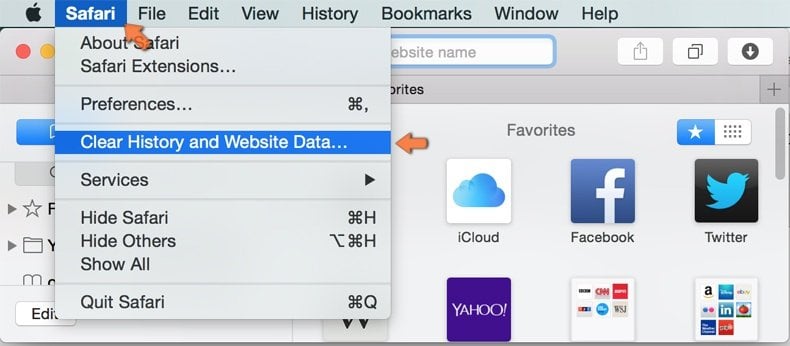
In the opened window select all history and click the Clear History button.

 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
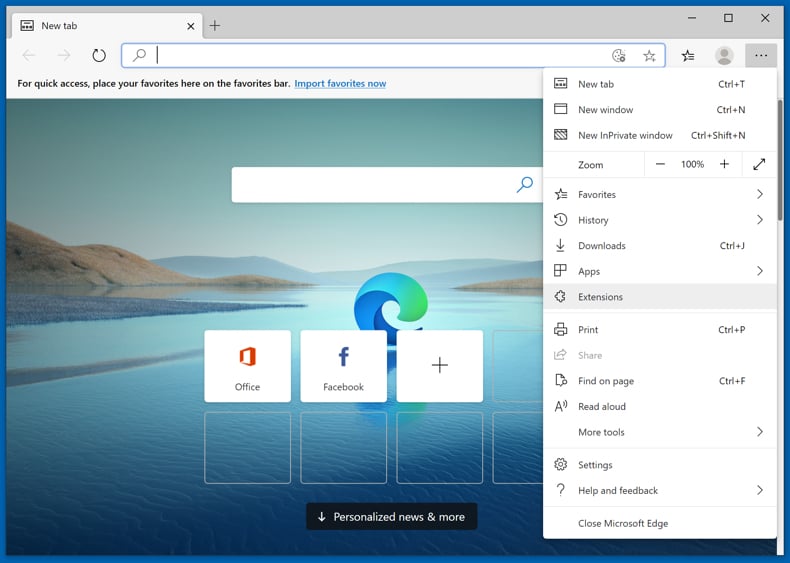
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
Optional method:
If you continue to have problems with removal of the euphractussexcinctus unwanted browser extension, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
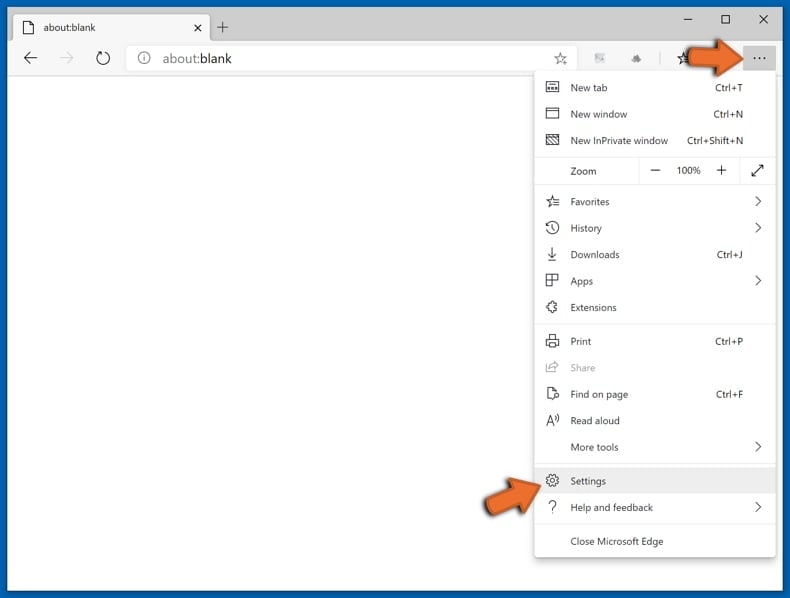
In the opened settings menu select Reset settings.
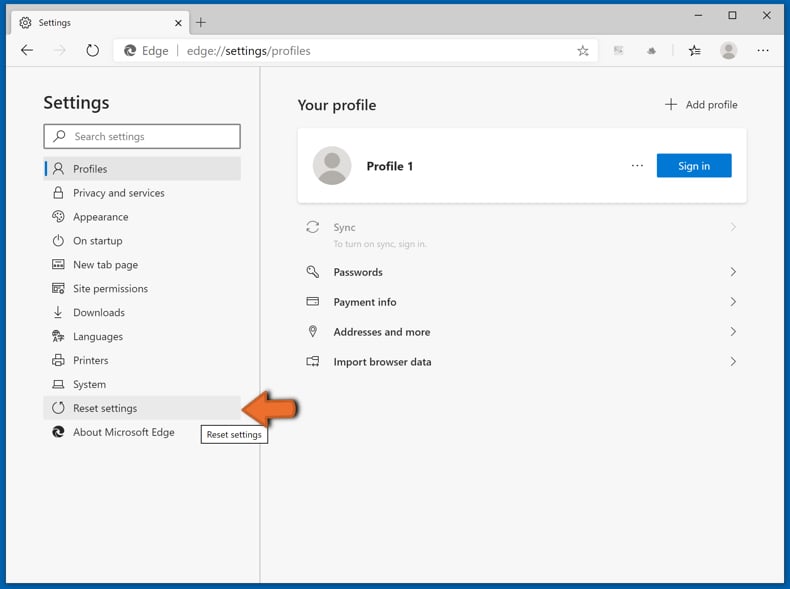
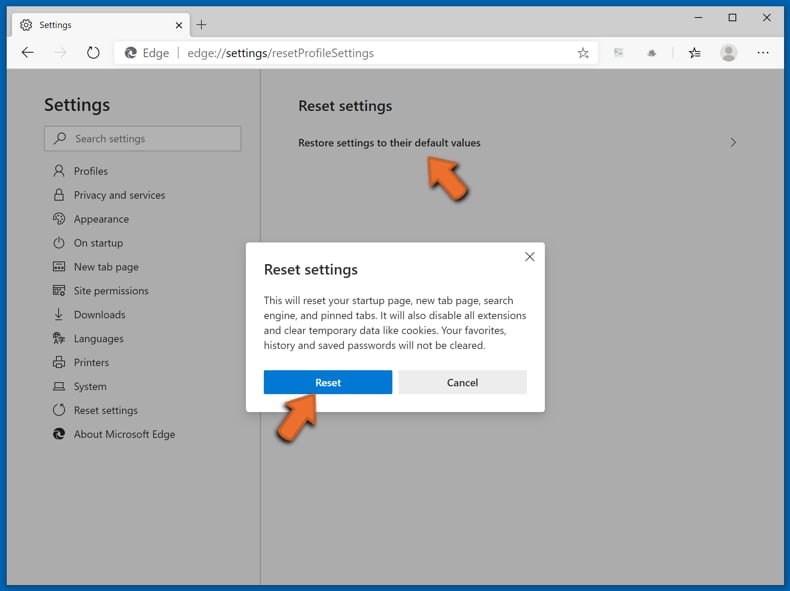
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
 Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Post a comment:
If you have additional information on euphractussexcinctus unwanted browser extension or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
What harm can EuphractusSexcinctus cause?
EuphractusSexcinctus can change browsers' appearance and behavior for nefarious purposes. This extension might be capable of exploiting browser vulnerabilities to further the infection. Additionally, EuphractusSexcinctus can read browsing histories and collect vulnerable information. Hence, the primary threats include system infections, serious privacy issues, financial losses, and even identity theft.
What does EuphractusSexcinctus do?
EuphractusSexcinctus can manage browsers' apps, extensions, themes, and other settings. It also utilizes the "Managed by your organization" feature (Chrome, Edge) for additional control and to ensure persistence. This extension also spies on users' browsing activity and collects sensitive data.
How do EuphractusSexcinctus developers generate revenue?
Profit could be made by selling or abusing the collected information. It is also common for rogue browser extensions to generate revenue through content promotion, e.g., by displaying advertisements, force-opening webpages, etc.
Will Combo Cleaner remove malicious software?
Yes, Combo Cleaner is capable of detecting and removing all manner of threats. It must be mentioned that manual removal (performed without security programs) might not be a perfect solution. In some instances, various file remnants stay hidden within the system after the software has been manually removed. Furthermore, the remaining components might continue to run and cause issues. Therefore, thorough software removal is paramount.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion