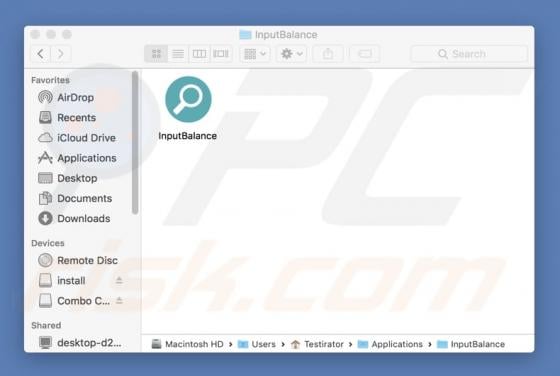
InputBalance Adware (Mac)
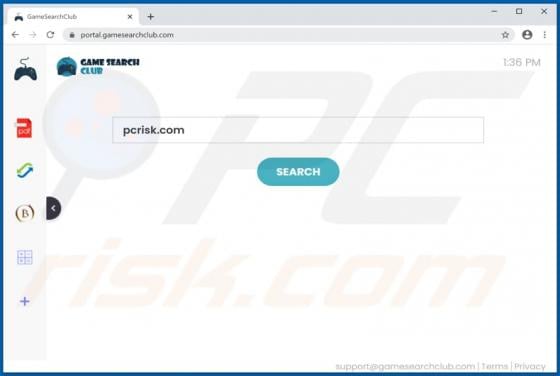
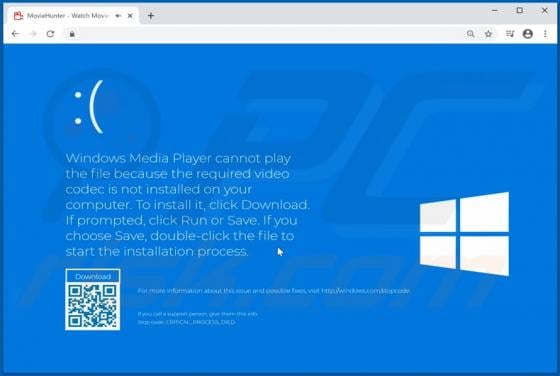
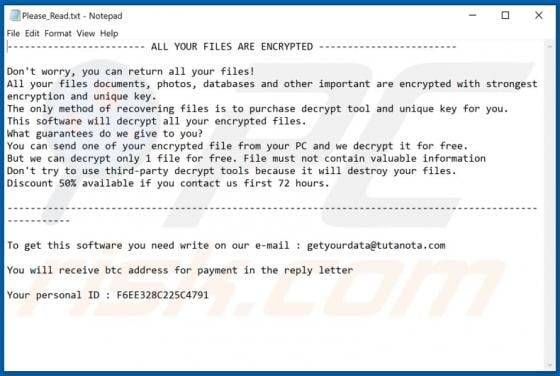
InputBalance functions as adware, browser hijacker and a data collector - it serves advertisements, promotes a fake search engine, and gathers private, sensitive information. Commonly, users download and install these apps inadvertently. InputBalance is distributed by using a fake installer disg