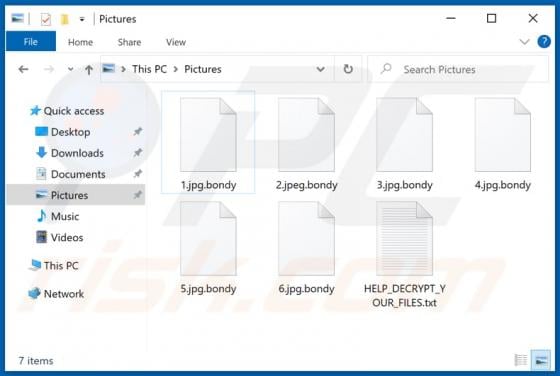
Bondy Ransomware
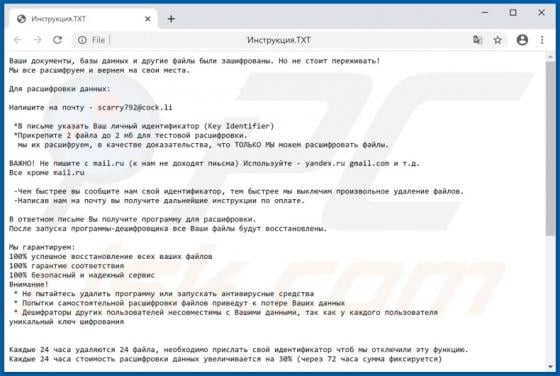
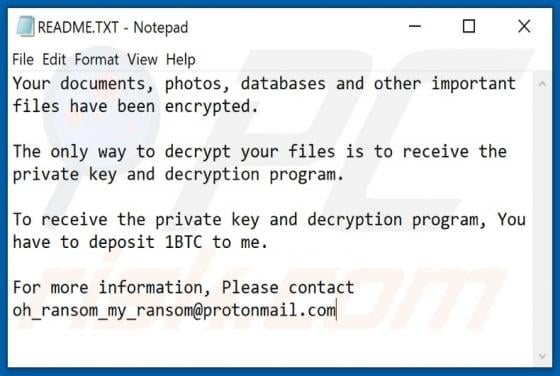
Discovered by S!Ri, Bondy is ransomware designed to encrypt files, append its extension to the filenames of all affected files, and create a ransom message (within the "HELP_DECRYPT_YOUR_FILES.txt" text file) in all folders that contain encrypted files. It renames files by appending the ".bondy"