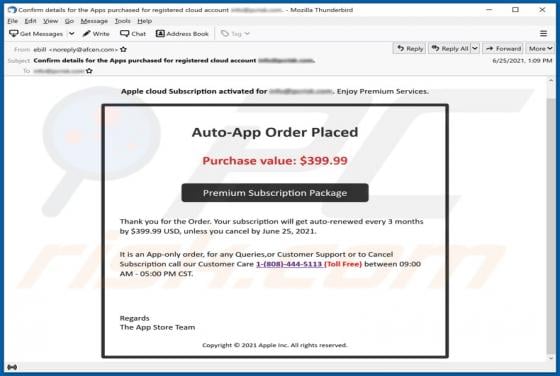
Apple Cloud Subscription Email Scam
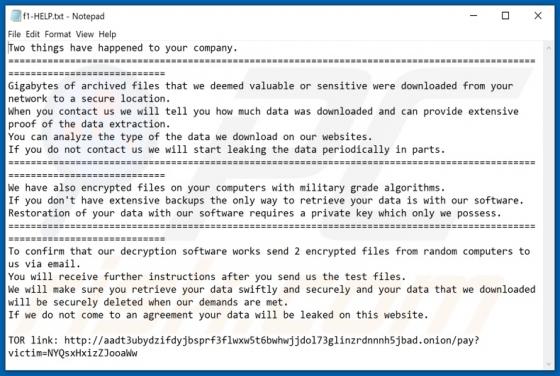
Typically, scammers behind phishing emails pretend to be legitimate companies, organizations to trick recipients into providing personal information (for example, login credentials, credit card details, social security numbers). This phishing email is disguised as a letter from Apple (App Store te