How to eliminate the Rose grabber from the system
![]() Written by Tomas Meskauskas on
Written by Tomas Meskauskas on
What kind of malware is Rose?
Rose is a grabber, a type of malicious software designed to steal sensitive information from a targeted system. Rose is an updated variant of the Phorcy stealer. It is capable of stealing data from browsers and other apps, cryptocurrency wallets, and performing other malicious activities. Victims should eliminate Rose from systems immediately.
More about Rose
Rose can bypass User Account Control, granting it elevated privileges on the targeted system. This elevation of privileges enhances the malware's ability to carry out various malicious actions without encountering typical security barriers. Additionally, the attackers can set a unique icon for the malware, contributing to its camouflage and making it less conspicuous to victims.
To ensure persistence on the infected system, the Rose grabber remains active and continues its malicious operations each time the system restarts. Simultaneously, the malware employs tactics to undermine the system's security measures. It turns off the built-in antivirus protection (Windows Defender) and firewalls, aiming to evade detection and removal.
The Rose grabber evades virtual machine environments. This makes it more challenging for security researchers to analyze the malware in a controlled environment. Furthermore, the malware takes preventative measures by blocking access to antivirus-related websites, hindering the victim's ability to seek assistance or updates for their security software.
In its efforts to remain undetected, the malware includes a self-destruct mechanism designed to erase traces of the malware. In order to deceive users and create confusion, the malware can display false error messages, potentially leading the user to overlook the malicious activities.
The Rose grabber extends its reach to various communication platforms, such as Discord, through features like Discord injection. This feature allows the injection of code into Discord processes. Combined with the ability to steal Discord tokens, the malware gains unauthorized access to Discord accounts.
It goes further by initiating mass direct messages to all friends on the victim's Discord account, illustrating its potential for widespread impact. Beyond social platforms, the malware targets gaming sessions on Steam, Epic Games, and Uplay, stealing active sessions for potential exploitation.
Additionally, the Rose grabber focuses on extracting sensitive information from various web browsers, including passwords, cookies, browsing history, and autofill data. It extends its reach to gaming platforms like Minecraft and messaging applications such as Telegram, highlighting its versatility in compromising a wide range of user data.
Moreover, the Rose grabber can extract cryptocurrency wallet information. This poses a significant threat to users involved in digital currency transactions. It also targets platform-specific data, such as Roblox cookies, showcasing its adaptability to different online environments.
The malware goes beyond personal data theft by collecting system information, IP addresses, and even saved Wi-Fi passwords. This comprehensive approach allows the attackers to gather a vast amount of information about the victim, potentially facilitating further exploitation or unauthorized access.
Also, the malware can cause a Blue Screen of Death, disrupting the user's experience. Additionally, the malware has the capability to capture screenshots and webcam images, providing attackers with visual insights into the victim's activities.
To facilitate data exfiltration, the Rose grabber utilizes Discord webhooks, sending stolen data to specified destinations via Discord. This method of communication offers a convenient and covert means for the attackers to receive and control the stolen information.
Finally, the Rose grabber concludes its arsenal with the deployment of a crypto miner to utilize the victim's computer in cryptocurrency mining operations. Additionally, it introduces a ransomware feature, coercing victims into paying a specific amount in Monero by threatening data loss.
In the future, the Rose grabber may incorporate additional capabilities. These expected improvements might involve implementing an EXE Binder to merge various files into a single executable, a feature to freeze the screen, allowing manipulation of the user's display, and a characteristic for distributing malware intended for spreading malicious messages across social media platforms.
| Name | Rose stealer |
| Threat Type | Grabber, Stealer, Crypto miner, Ransomware |
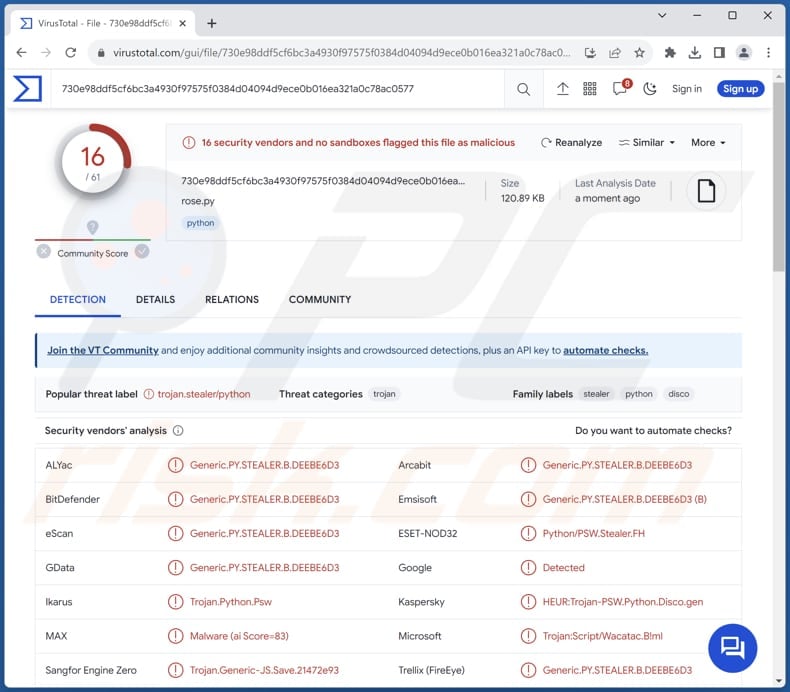
| Detection Names | Combo Cleaner (Generic.PY.STEALER.B.DEEBE6D3), ESET-NOD32 (Python/PSW.Stealer.FH), Kaspersky (HEUR:Trojan-PSW.Python.Disco.gen), Microsoft (Trojan:Python/Multiverze), Symantec (Trojan.Gen.NPE), Full List (VirusTotal) |
| Payload | Cryptocurrency miner, Ransomware |
| Symptoms | Grabbers are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet, additional infections, monetary loss, and more. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Conclusion
In conclusion, the Rose grabber represents a highly sophisticated and multifaceted malware with a diverse range of capabilities geared towards information theft, system manipulation, and potential financial exploitation. Rose's multifarious nature underscores the importance of robust cybersecurity measures to safeguard against evolving and increasingly sophisticated threats.
More examples of grabbers are Vespy, Nagogy, and Luna.
How did Rose infiltrate my computer?
Opening email attachments from unknown or untrusted sources can lead to the execution of malware. Clicking links in phishing emails, social media messages, or suspicious websites can also lead users to websites hosting malware or initiate malicious downloads.
Furthermore, cybercriminals may use social engineering tactics, such as posing as tech support, to manipulate users into downloading malicious software. Also, visiting compromised or malicious websites can trigger automatic downloads and installations of malware without the user's knowledge.
In other cases, users infect computers by failing to update operating systems and software, clicking on malicious advertisements, downloading files from peer-to-peer networks and similar sources, or running pirated software, cracking tools, or key generators.
How to avoid installation of malware?
To prevent unintentional infections, users should practice good cybersecurity hygiene, including using reputable security software, keeping software up to date, being cautious with email attachments and links, and avoiding downloads from untrusted sources.
Being careful when interacting with websites, especially those that display suspicious pop-ups or ads, is also recommended. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
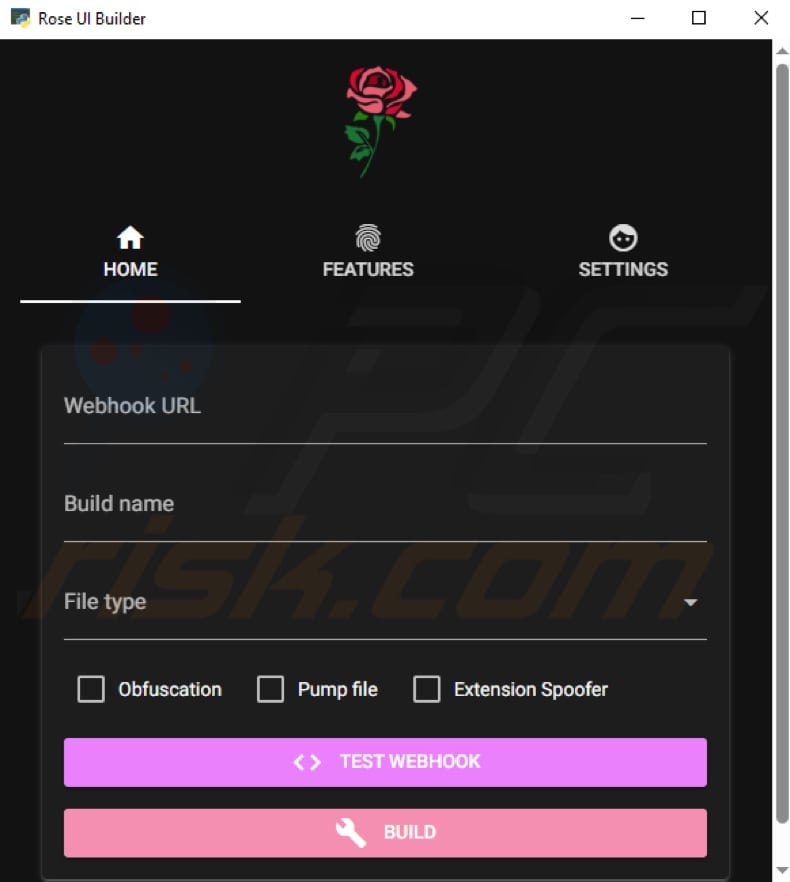
Rose's builder:
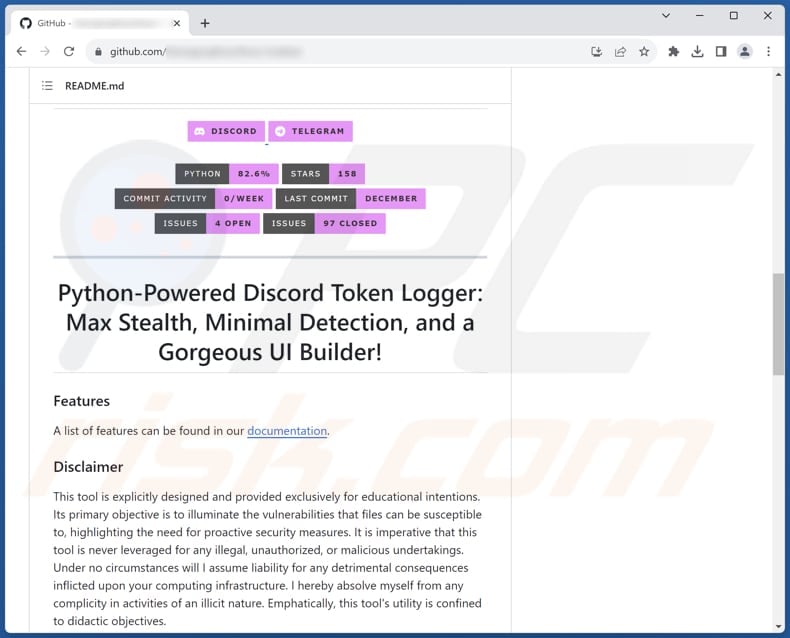
Rose grabber promoted in GitHub:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
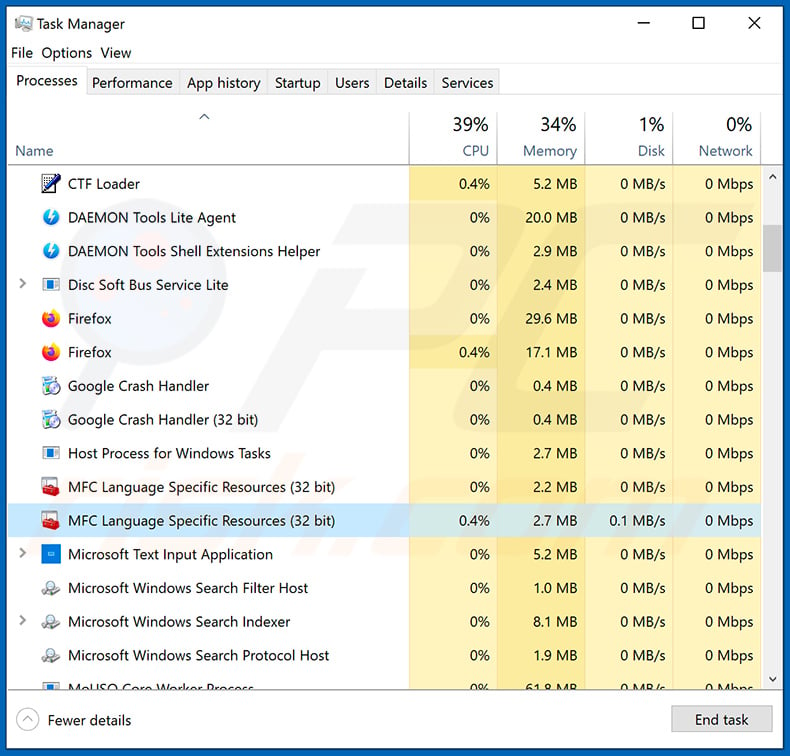
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
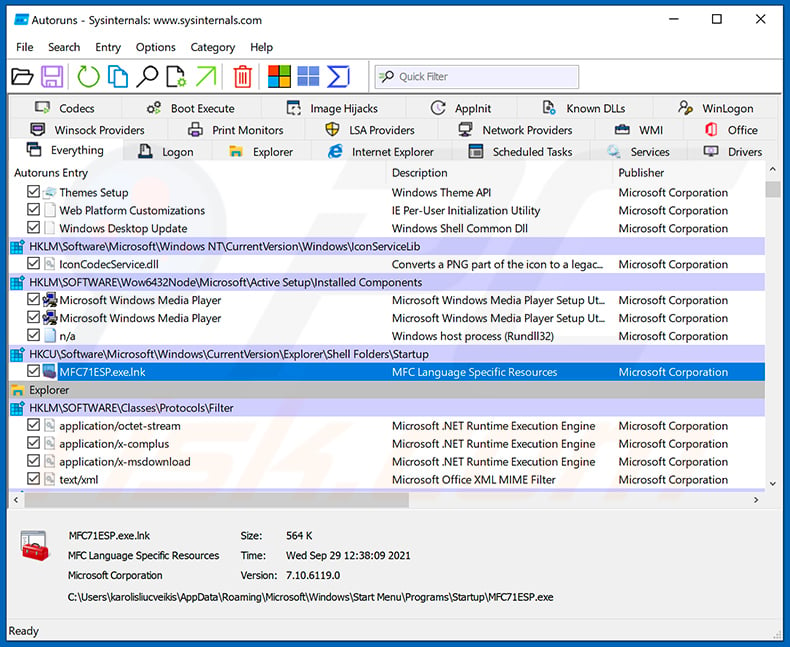
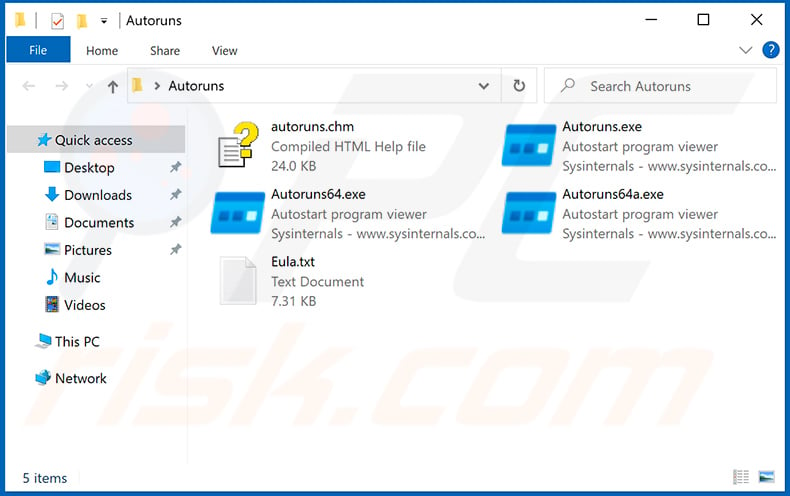
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
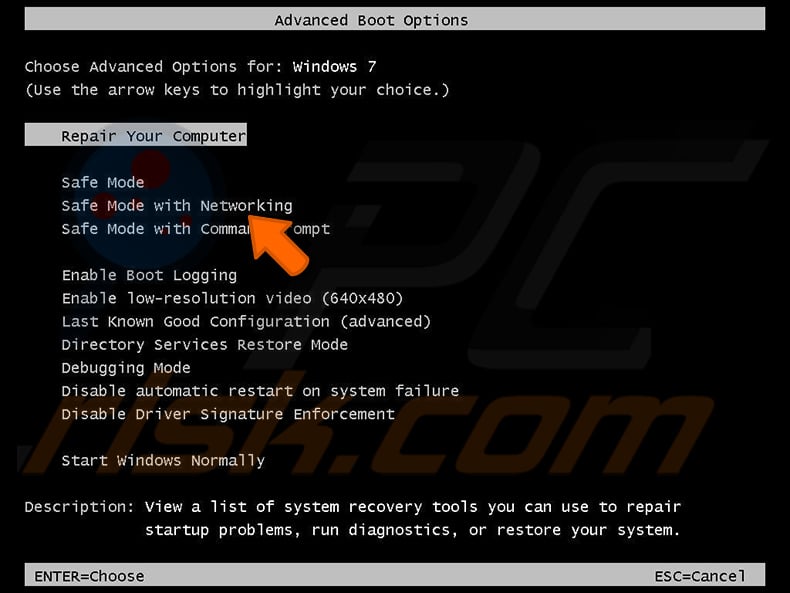
Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
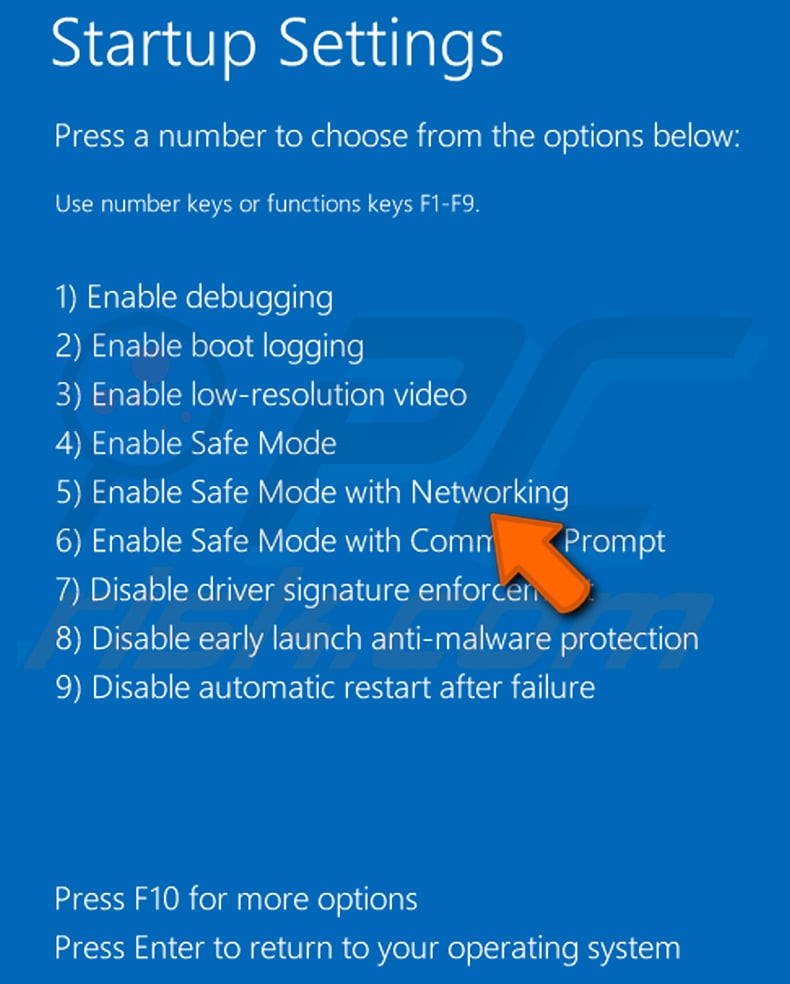
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
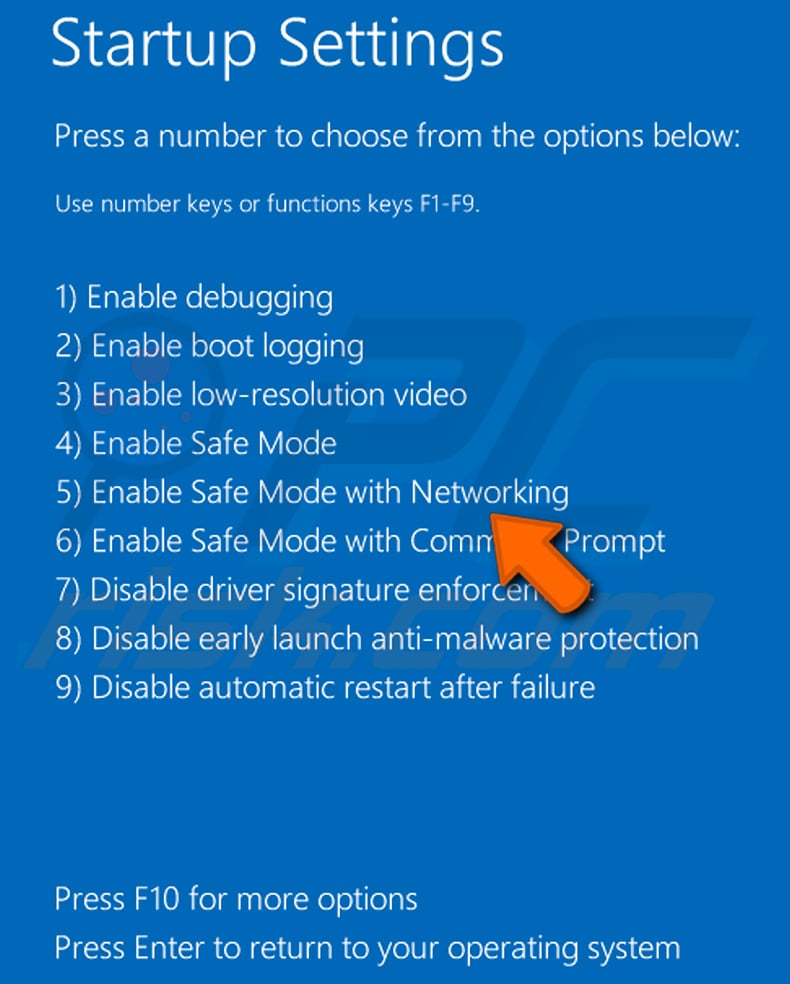
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
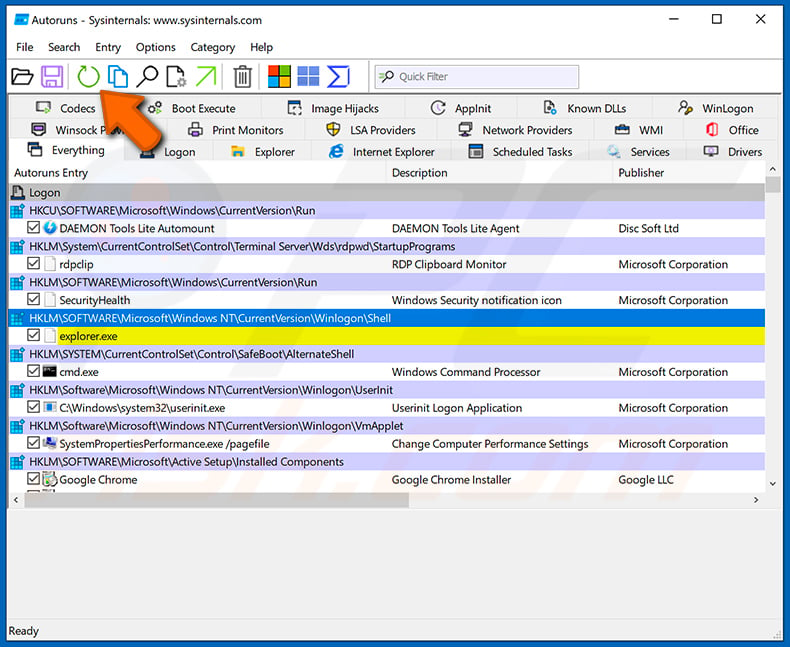
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
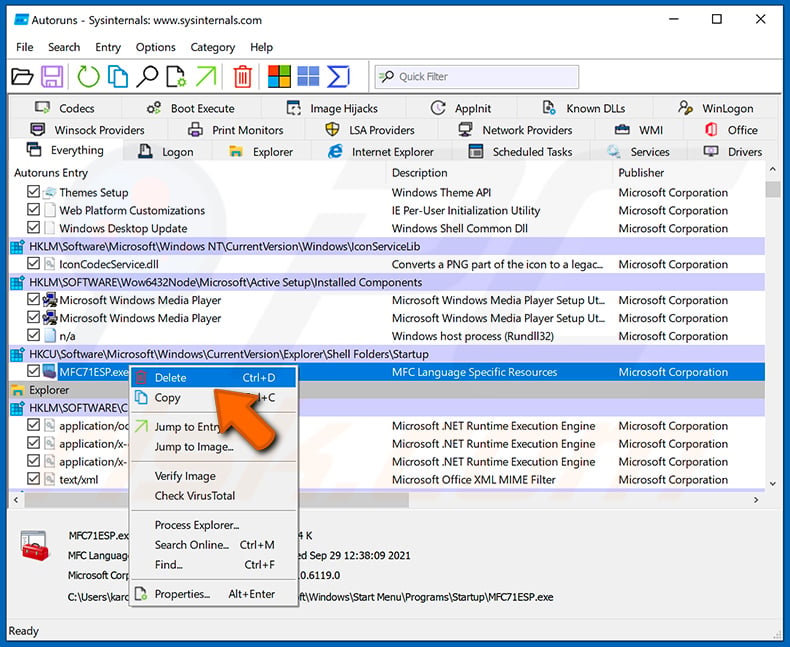
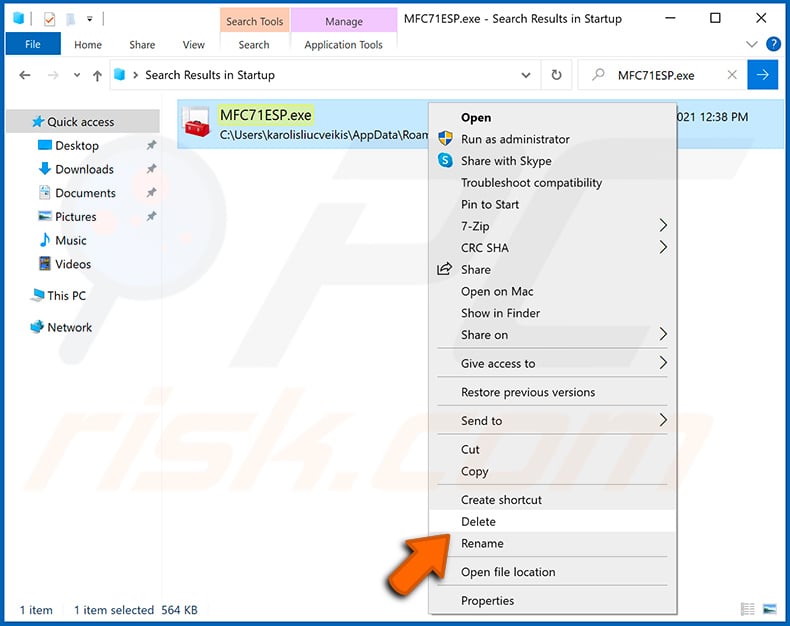
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Rose malware, should I format my storage device to get rid of it?
If you suspect that your computer is infected with the Rose malware, formatting your storage device might be a drastic step and should be considered carefully. Before taking such a measure, consider running a reputable security tool like Combo Cleaner to detect and remove malware.
What are the biggest issues that malware can cause?
Malware can lead to severe consequences, such as unauthorized access to sensitive data, financial harm, damage to system functionality, compromised privacy, additional infections, and disruption of normal computer operations.
What is the purpose of Rose grabber?
The primary purpose of the Rose grabber is to compromise systems for information theft, including sensitive data, login credentials, and personal information, while also facilitating unauthorized access and potential financial exploitation.
How did a malware infiltrate my computer?
Common entry points for malware include malicious email attachments, infected websites, malicious ads, pirated software, cracking tools, software vulnerabilities, infected USB drives, and downloads from untrusted sources.
Will Combo Cleaner protect me from malware?
Combo Cleaner can identify and remove nearly all recognized malware infections. It is important to note that sophisticated malware often conceals itself deeply within the system, emphasizing the necessity of conducting a comprehensive system scan.
▼ Show Discussion