How to remove Vespy malware from the operating system
![]() Written by Tomas Meskauskas on
Written by Tomas Meskauskas on
What kind of malware is Vespy Grabber?
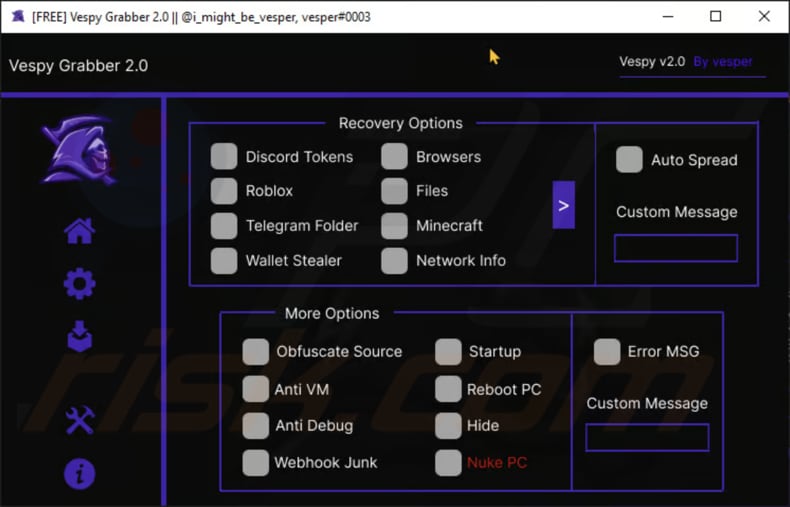
Vespy Grabber is a sophisticated and multifaceted malware that poses a grave risk to both individual users and organizations. Vespy Grabber is a highly invasive malware strain known for its extensive capabilities, ranging from capturing desktop and webcam screenshots to exfiltrating sensitive data from various sources.
More about Vespy Grabber
Vespy Grabber's range of functionalities is alarming and includes the ability to capture desktop and webcam screenshots, extract comprehensive computer information, hardware identification (HWID), and even pilfer Windows Product Keys.
One of the most concerning aspects of Vespy Grabber is its proficiency in infiltrating popular web browsers, such as Edge, Chrome, Brave, Opera, and Opera GX. Once inside, it can exfiltrate a vast array of sensitive data, including passwords, credit card details, browsing history, autofill information, and downloaded files.
It can also hijack browser profiles and import cookies using the Cookiebro Extension, giving the attackers access to a treasure trove of personal information. The malware's capabilities further extend to popular communication and gaming platforms. Vespy Grabber can compromise Discord accounts, acquiring Discord Tokens to facilitate infiltration and spreading through Discord DMs.
The malware can steal passwords and extract account information. It also targets the gaming community, infiltrating Roblox by capturing all Roblox Cookies across various browsers, infiltrating the Windows Registry for Roblox Cookies, and even targeting Roblox gambling sites. This poses significant threats to the security of gamers' accounts and assets.
Vespy Grabber's reach extends to cryptocurrency enthusiasts and investors, compromising wallets such as Exodus, Metamask, Coinbase Wallet, Electrum, Bitcoin Wallet, Guarda, Atomic, Bitpay, Coinomi, and Armory. It goes beyond mere theft, targeting cryptocurrency gambling sites and pilfering vital data. The malware even infiltrates Telegram, gaining access to the tdata folder.
Additionally, Vespy Grabber can capture Minecraft session files, delve into network information, including IP addresses and WiFi details, and conduct clipboard manipulation through BTC and ETH clippers. The malware also operates as a keylogger, recording keystrokes and capturing current window screenshots.
To compound the threat, Vespy Grabber is equipped with anti-detection features like obfuscation, anti-debugging, and anti-virtual machine capabilities. It can inject code, create webhooks to send stolen data, display fake error messages, force system reboots, and even hide its executable files, making it exceptionally challenging to detect and remove.
| Name | Vespy information stealer |
| Threat Type | Grabber, Information Stealer, Keylogger |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords, monetary (including cryptocurrency) loss, identity theft, loss of access to personal (including gaming) accounts, and more. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Conclusion
In summary, Vespy Grabber is a formidable and highly sophisticated malware strain capable of infiltrating, stealing, and compromising a vast array of personal, financial, and digital assets, highlighting the critical importance of robust cybersecurity practices to protect against such an insidious threat.
More examples of information-stealing malware are EasyStealer, Exela, and Fewer.
How did Vespy infiltrate my computer?
Malware attacks can ensnare users through a multitude of vectors. For instance, phishing emails employ cunning tactics to deceive users into clicking on malicious links or downloading infected attachments. Visiting compromised or fraudulent websites can similarly expose users to drive-by downloads, surreptitiously infecting their systems without their awareness.
Moreover, the allure of downloading unverified software, especially from unofficial sources, provides yet another gateway for malware to infiltrate a user's device. Social engineering techniques are also leveraged to orchestrate these attacks. The absence of robust cybersecurity awareness and preventative measures further compounds these vulnerabilities.
How to avoid installation of malware?
Exercise caution when handling unsolicited emails, particularly those containing dubious attachments or links. Prioritize the acquisition of software and applications exclusively from established and trustworthy sources, such as the Apple App Store, Google Play Store, or the official website of the software developer.
Consistently keep your operating system, antivirus software, and applications up to date to fortify your system against potential security vulnerabilities. Avoid interacting with advertisements on questionable websites, and firmly resist the temptation to download pirated software, cracking tools, or key generators.
Rely on reputable antivirus software to bolster your defense against potential threats. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
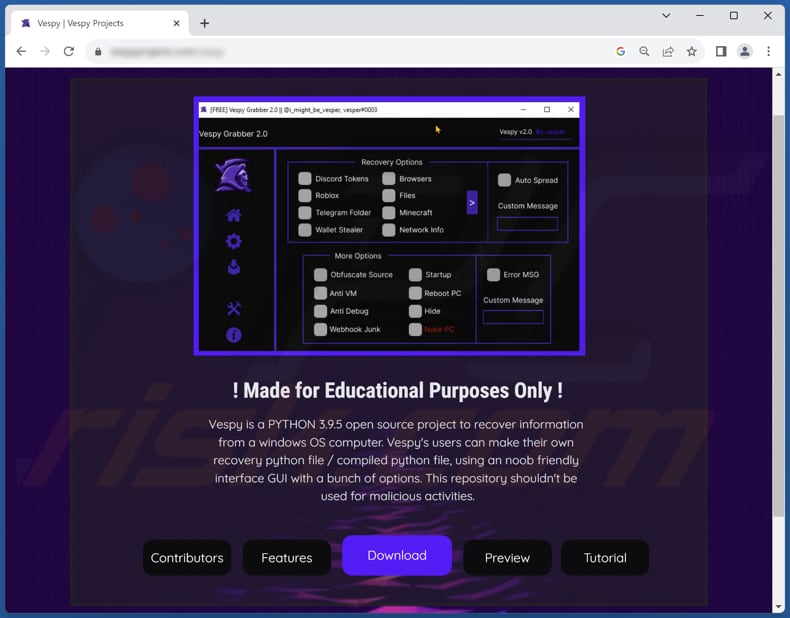
Website promoting Vespy Grabber:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
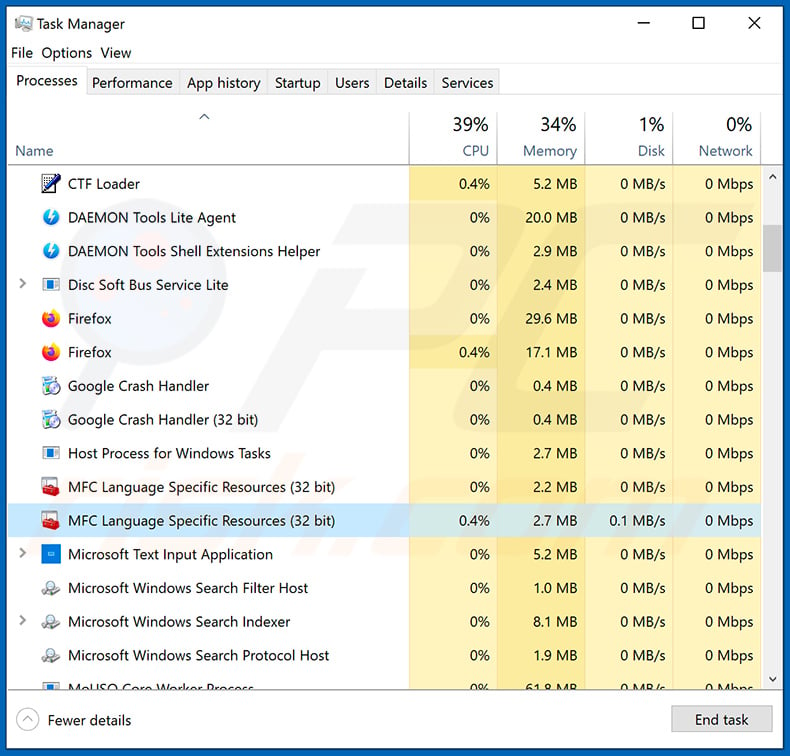
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
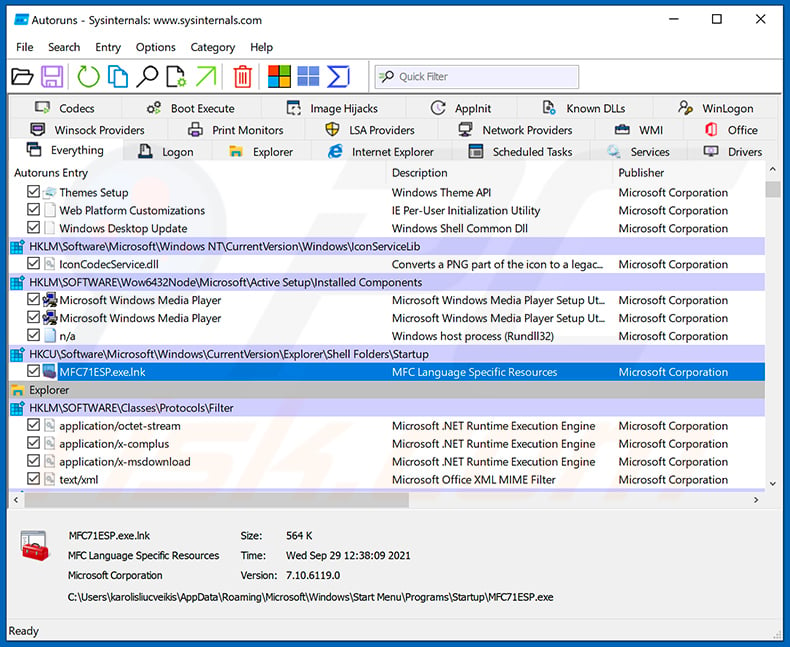
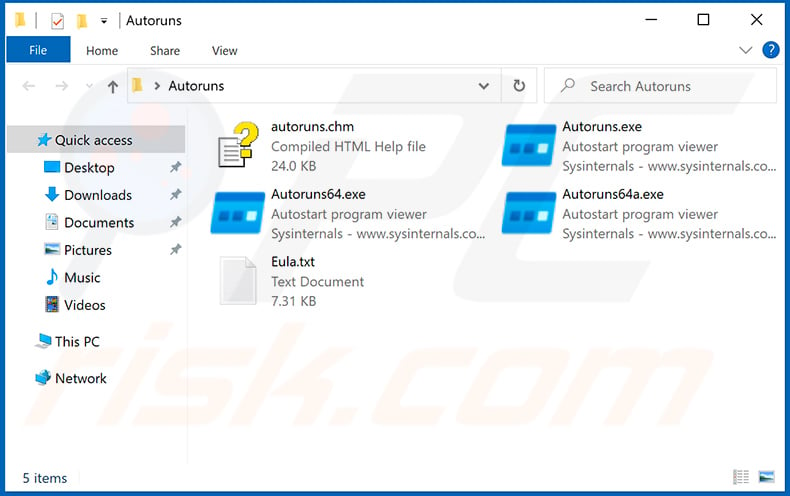
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
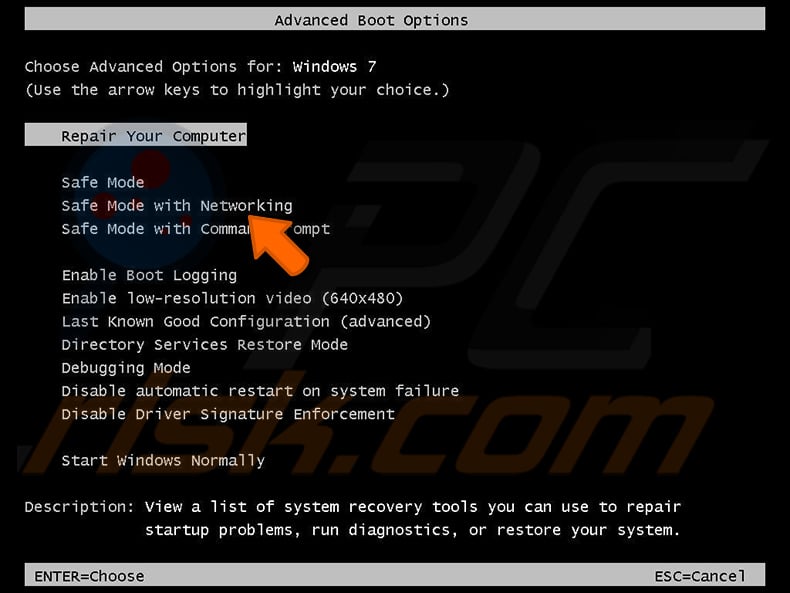
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
Video showing how to start Windows 7 in "Safe Mode with Networking":
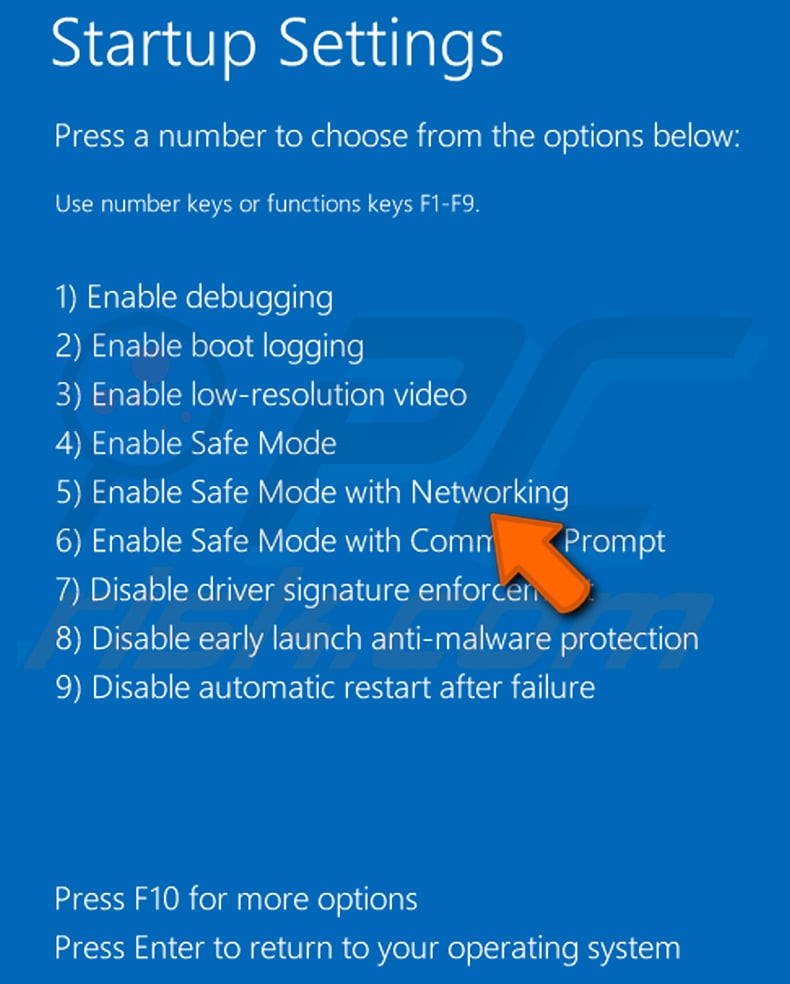
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
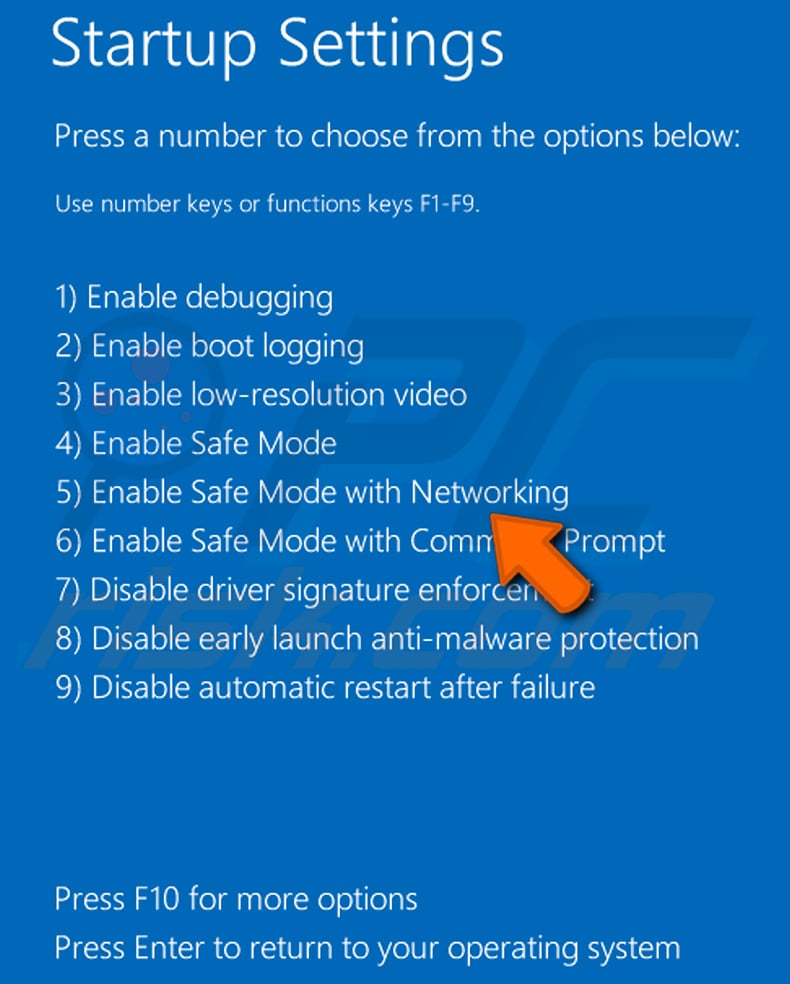
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
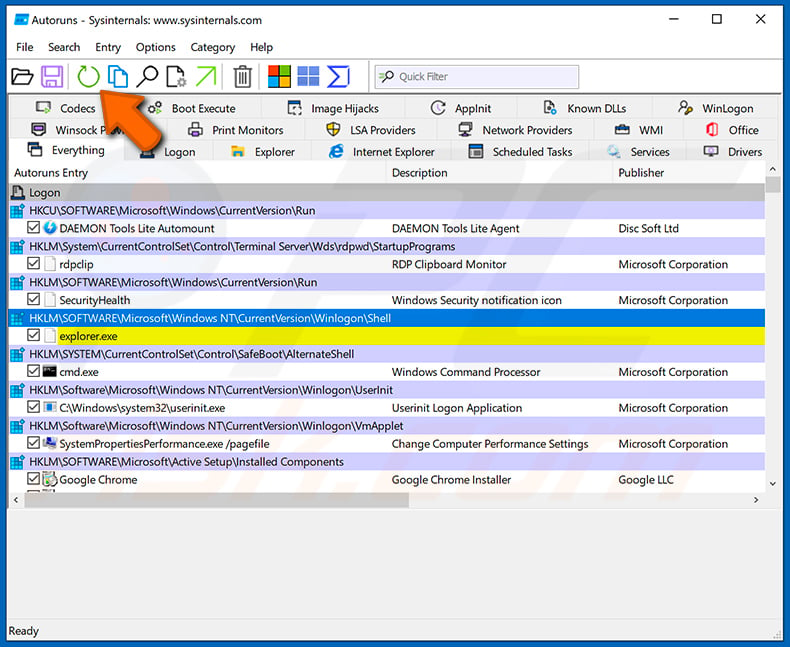
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
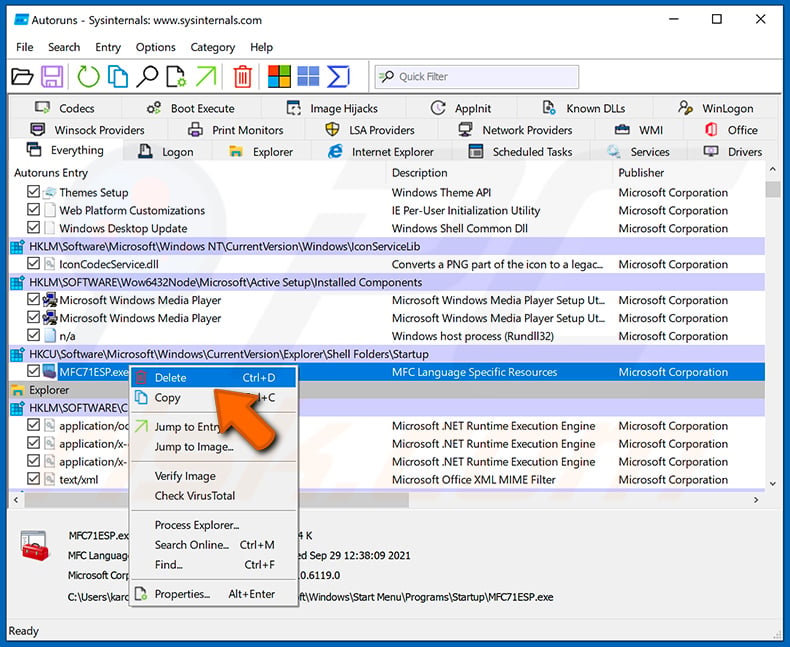
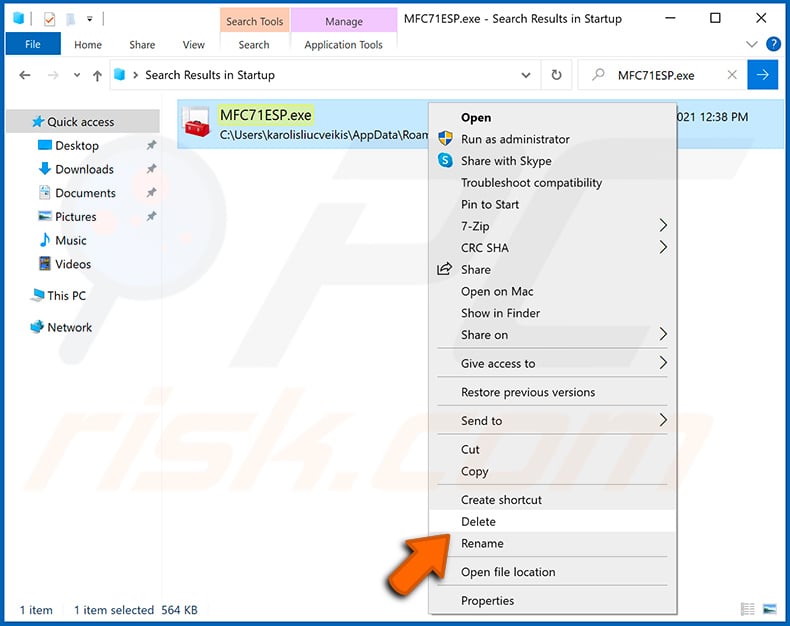
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Vespy malware, should I format my storage device to get rid of it?
When confronted with a Vespy malware infection on your computer, you may consider formatting your storage device as a potential means of malware elimination. Nevertheless, it is important to recognize that formatting should be viewed as a final recourse due to its inherent consequence of erasing all data on the storage device. As a precaution, it is advisable to explore alternative remedies before resorting to formatting, such as employing antivirus software like Combo Cleaner to facilitate the removal of Vespy Grabber.
What are the biggest issues that malware can cause?
Malware poses extensive challenges, the foremost being data breaches and invasions of privacy, where valuable information may be maliciously exfiltrated, resulting in identity theft and financial harm. Moreover, malware can disrupt computer systems and cause substantial harm, exemplified by ransomware incidents that trigger downtime, productivity setbacks, and financial repercussions.
What is the purpose of Vespy Grabber?
Vespy Grabber is designed to steal a wide range of sensitive information and data from infected devices, including but not limited to login credentials, financial details, personal information, and more.
How did a malware infiltrate my computer?
Avenues of infection encompass practices like opening malicious email attachments, downloading content from untrustworthy websites, using compromised software or apps, and running outdated software or operating systems lacking the latest security updates. Malware may also proliferate through security vulnerabilities and social engineering tactics.
Will Combo Cleaner protect me from malware?
Combo Cleaner is proficient in identifying and eliminating the majority of malware infections. Since sophisticated malware often hides deep within the system, performing a comprehensive system scan is advisable to eradicate such threats effectively.
▼ Show Discussion