Removal instructions for malicious programs from the Duke malware family
TrojanAlso Known As: Duke malware toolset
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Duke?
Duke is the general name for malware toolsets used by the APT29 APT (Advanced Persistent Threat) actor, also known as The Dukes, Cloaked Ursa, CozyBear, Nobelium, and UNC2452. APT29 is a Russian state-sponsored group associated with the Foreign Intelligence Service of the Russian Federation (SVR RF). The group is politically and geopolitically motivated; it deals with intelligence gathering and cyber-espionage.
The Duke malware family encompasses a broad range of malicious programs, including system backdoors, loaders, data stealers, process disruptors, and others.
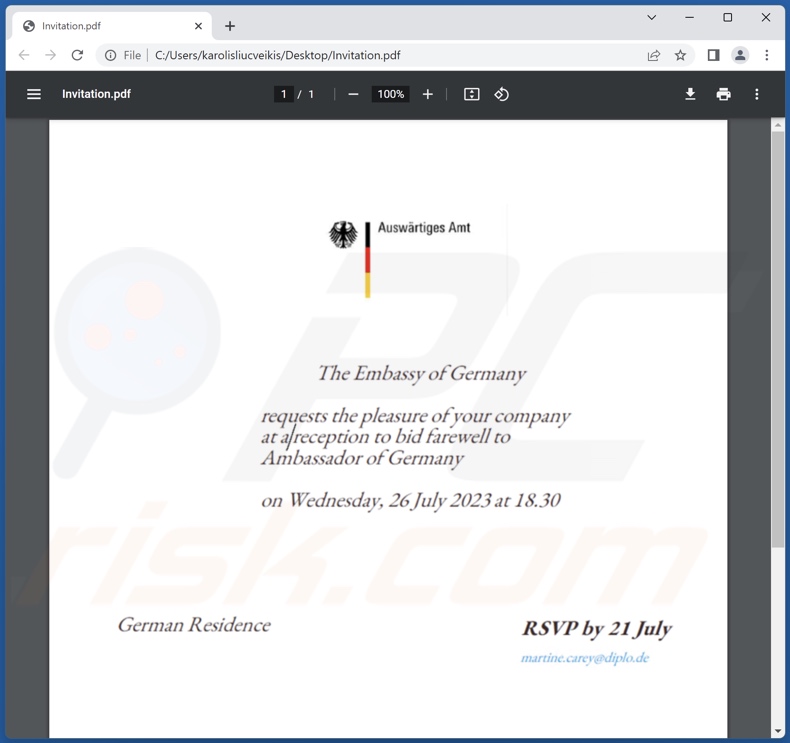
The latest spam campaign linked to The Dukes group occurred in 2023 and implemented malicious PDF documents disguised as diplomatic invitations from the German embassy. This email campaign targeted Foreign Affairs ministries of countries aligned with NATO.
Duke malware toolset overview
The Dukes APT actor has been in operation since at least 2008, and throughout the years, the group has implemented a wide variety of tools. The following is a chronological listing of some of the better-known toolsets utilized by this threat actor.
PinchDuke – consists of several loaders intended to infiltrate additional malicious components or programs into compromised systems.
It also encompasses a grabber for file exfiltration and a credential stealer. The latter targets data associated with the Microsoft Authenticator (passport.net), email clients (Mail.ru, Mozilla Thunderbird, Outlook, The Bat!, Yahoo Mail), browsers (Internet Explorer, Mozilla Firefox, Netscape Navigator), messaging services (Google Talk), etc.
GeminiDuke – includes loader capabilities and multiple persistence-ensuring mechanisms. It likewise boasts stealer functionalities predominantly used for device configuration data collection.
Information of interest includes: user accounts, installed drivers and software, running processes, programs/services launched at startup, network settings, folders/files present in specific locations, recently executed programs and opened folders/files, etc.
CosmicDuke (aka BotgenStudios, NemesisGemina, Tinybaron) – comprises several loaders, multiple persistence-ensuring components, and a module for privilege escalation.
The largest part of this malware is an information-stealer with abilities to: exfiltrate files with specific extensions, export cryptographic certificates (including private keys), take screenshots, record keystrokes (keylogging), extract log-in credentials (browsers, email clients, messengers), and acquire clipboard (copy-paste buffer) contents.
MiniDuke – is a malware with several variants, including a loader, downloader, and backdoor. Chiefly, MiniDuke is used to prepare a system for further infection and/or facilitate it.
CozyDuke (aka Cozer, CozyBear, CozyCar, EuroAPT) – is primarily a backdoor that opens a "backdoor" for further infections, particularly its own modules. To this effect, it employs a dropper and multiple modules for persistence.
Other components include ones for extracting system data, executing basic Cmd.exe commands, taking screenshots, and stealing log-in credentials. However, CozyDuke can also infiltrate/execute other files – hence, it could be used to (theoretically) cause just about any type of malware infection.
OnionDuke – is a modular malware with a variety of potential configurations. It has loader and dropper capabilities. The program implements several different information-stealing modules, e.g., for passwords and other data.
It also has a component for launching DDoS (Distributed Denial-of-Service) attacks. Another module is designed to use hijacked social networking accounts for launching spam campaigns (potentially to spread the infection further).
SeaDuke (aka SeaDaddy, SeaDask) – is a cross-platform (Windows and Linux) backdoor. It is a relatively basic toolset with the main objective of executing infiltrated files, thus furthering the infection.
HammerDuke (aka HAMMERTOSS, Netduke) – is a simple backdoor. Its known use has been exclusively as a secondary backdoor that follows a CozyDuke infection.
CloudDuke (aka CloudLook, MiniDionis) – has two backdoor versions. This malware also includes downloader and loader capabilities. Typically, it downloads/installs payloads from predetermined locations, either from the Web or a Microsoft OneDrive account.
It is pertinent to mention that unless The Dukes APT actor ceases operations, the likelihood of new malware toolset implementation is high.
Generally, sophisticated malware can cause multiple system infections, decreased system performance or failure, data loss, severe privacy issues, financial losses, and identity theft. However, malicious software leveraged against highly sensitive targets can pose threats of even greater significance.
| Name | Duke malware toolset |
| Threat Type | Trojan, backdoor, loader, password-stealing virus, banking malware, spyware. |
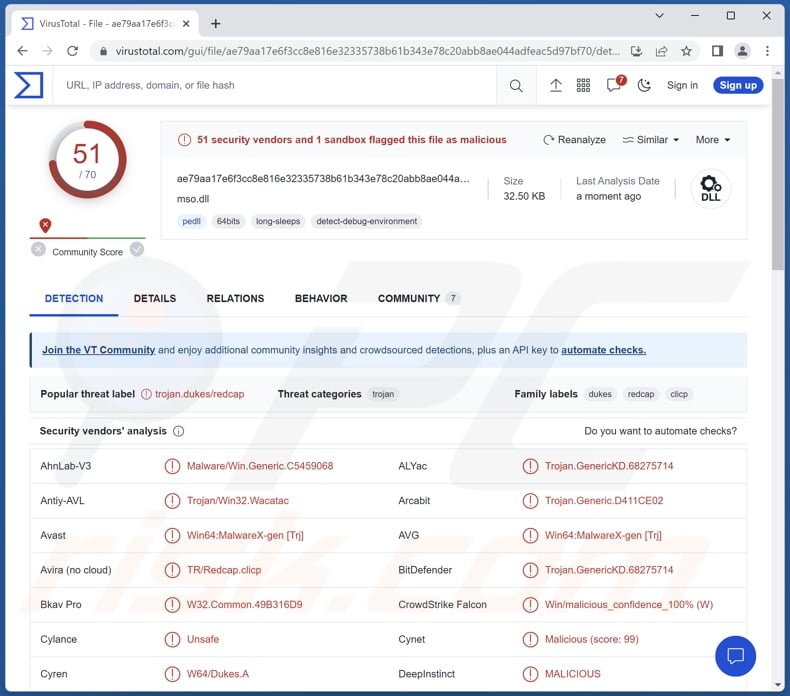
| Detection Names (PDF attachment) | Avast (Other:Malware-gen [Trj]), Combo Cleaner (Trojan.GenericKD.68283668), ESET-NOD32 (PDF/TrojanDropper.Agent.CJ), Kaspersky (Trojan-Dropper.HTML.Agent.cn), Microsoft (Trojan:Win32/Leonem), Full List Of Detections (VirusTotal) |
| Detection Names (PDF payload) | Avast (Win64:MalwareX-gen [Trj]), Combo Cleaner (Trojan.GenericKD.68275714), ESET-NOD32 (A Variant Of Win64/Dukes.N), Kaspersky (Trojan.Win64.Agent.qwikue), Microsoft (Trojan:Win32/Casdet!rfn), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Malware in general
Malware can be narrowly tailored for a specific purpose or be incredibly versatile. While malicious software is most commonly used to generate revenue, its application can vary. Attacks can be motivated by attackers' personal relationships and grudges or political/geopolitical reasons and circumstances.
However, regardless of how malware operates – its presence on a system endangers device integrity and user safety. Therefore, all threats must be eliminated immediately upon detection.
We have analyzed thousands of malware samples; JanelaRAT, Agniane stealer, NightClub, Jorik, XWorm RAT, and WikiLoader are just a few of our newest articles on malicious programs.
How did Duke infiltrate my computer?
The latest 2023 campaign undertaken by APT29 (The Dukes) utilized spam emails in targeted attacks. The spam was sent to Foreign Affairs ministries of interest to the Russian Federation (i.e., NATO-aligned bodies). The emails contained malicious PDF attachments masquerading as diplomatic invites from a German embassy.
One of the spam operations did not include a payload; the document titled "Day of German Unity" sent a notification to the attackers once the email attachment was opened. This suggests that it could have been an operation for reconnaissance or a test to survey the lure's success rates.
The other campaign distributed a PDF with the "Farewell to Ambassador of Germany" filename containing a Duke malware variant. This document had JavaScript code embedded into it, which was implemented to deliver a multi-staged payload in an HTML format.
If the PDF was opened in Adobe Acrobat (or a similar reader), the user gets queried about the embedded code and its execution. If the victim permitted it, a malicious HTML document titled "Invitation_Farewell_DE_EMB" was launched.
The chain then progressed to the retrieval of a ZIP archive containing a virulent HTA (HTML Application). The chain moved through several more stages until Duke malware was successfully infiltrated.
The Dukes group has been around for well over a decade and has used a variety of techniques to proliferate their malicious programs. Therefore, the malware toolsets described in this article can arrive in different infection chains, as well as in various files and lures.
This APT actor has been linked to a similar spam campaign, wherein the bait was disguised as diplomatic invitations from a Norwegian embassy, and this operation likewise targeted entities associated with Foreign Affairs. An entirely different campaign connected to APT29 used Torrent files to spread OnionDuke back in 2013-2015.
To expand upon the most widely used malware distribution techniques in general: malicious software is primarily proliferated via malicious attachments/links in spam mail (e.g., emails, DMs/PMs, SMSes, etc.), drive-by (stealthy/deceptive) downloads, untrustworthy download channels (e.g., freeware and third-party sites, P2P sharing networks, etc.), online scams, malvertising, illegal software activation tools ("cracks"), and fake updates.
Some malicious programs can even self-spread through local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
How to avoid installation of malware?
We highly recommend treating incoming emails and other messages with caution. Attachments or links found in suspect/irrelevant mail must not be opened, as they can be infectious. We advise using post-2010 Microsoft Office versions since they have the "Protected View" mode that prevents automatic macro command execution.
Another recommendation is to be careful while browsing since fake and malicious online content usually appears genuine and harmless.
Additionally, all downloads must be performed from official and verified channels. It is just as important to activate and update programs by using functions/tools provided by legitimate developers, as those acquired from third-parties may contain malware.
We must emphasize that having a reputable anti-virus installed and kept up-to-date is essential to device and user safety. This software must be used to run regular system scans and to remove threats and issues. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Known toolset components and modules:
PinchDuke toolset:
- Data stealer
- Loader (multiple)
GeminiDuke toolset:
- Data stealer
- Loader
- Persistence-ensuring component (multiple)
CosmicDuke toolset:
- Data stealer
- Loader (multiple)
- Persistence-ensuring component (multiple)
- Privilege escalation component
MiniDuke toolset:
- Backdoor
- Downloader
- Loader
CozyDuke toolset:
- Backdoor
- Data stealers (screenshots, passwords, password hashes)
- Dropper
- Persistence-ensuring component (multiple)
OnionDuke toolset:
- Data stealers (passwords, etc.)
- DDoS
- Dropper
- Loader
- Social networking spam
SeaDuke toolset:
- Backdoor
HammerDuke toolset:
- Backdoor
CloudDuke toolset:
- Backdoor (two variants)
- Downloader
- Loader
Malicious PDF attachment distributing Duke malware variant:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
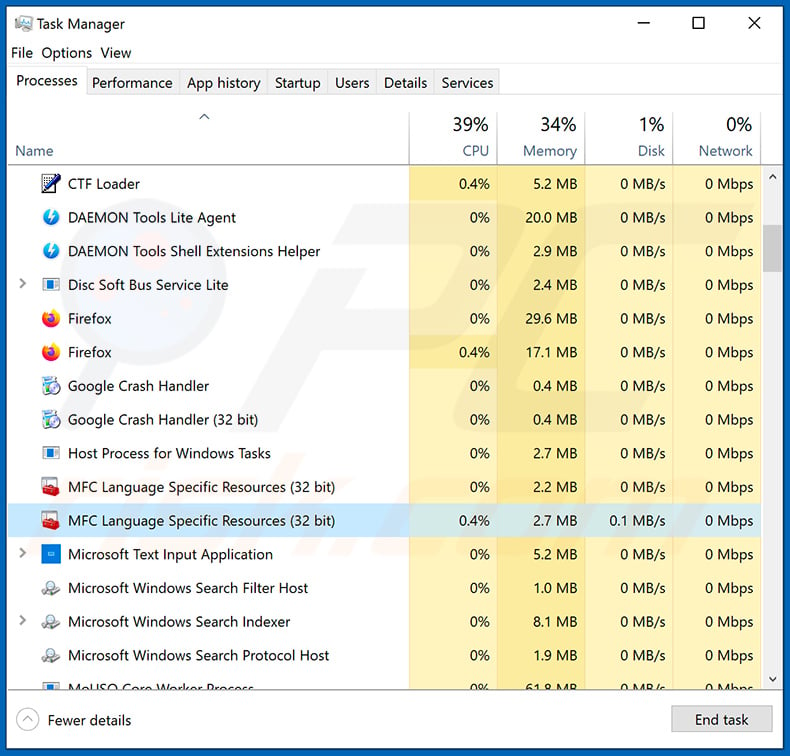
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
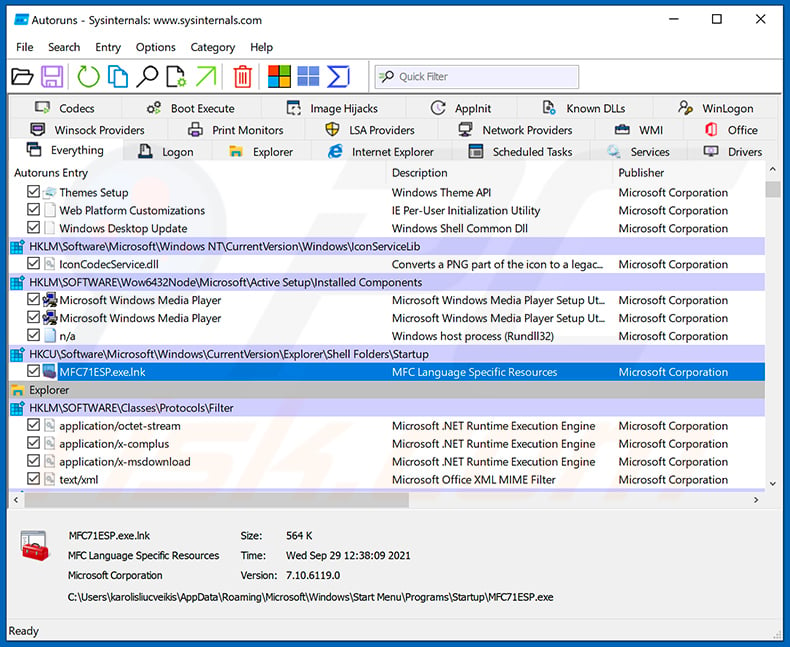
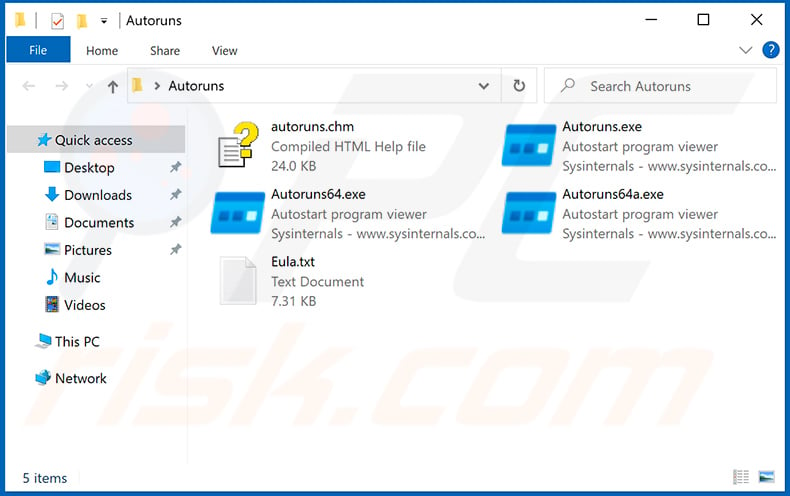
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
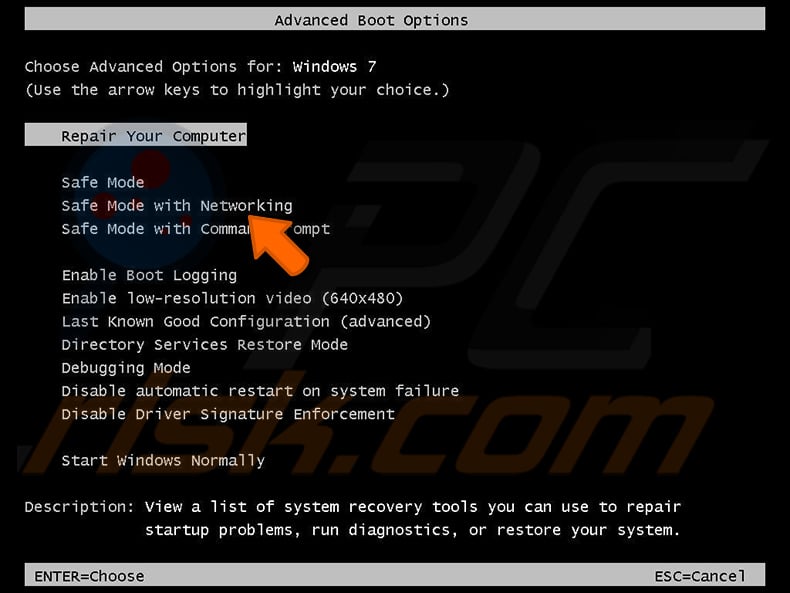
Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
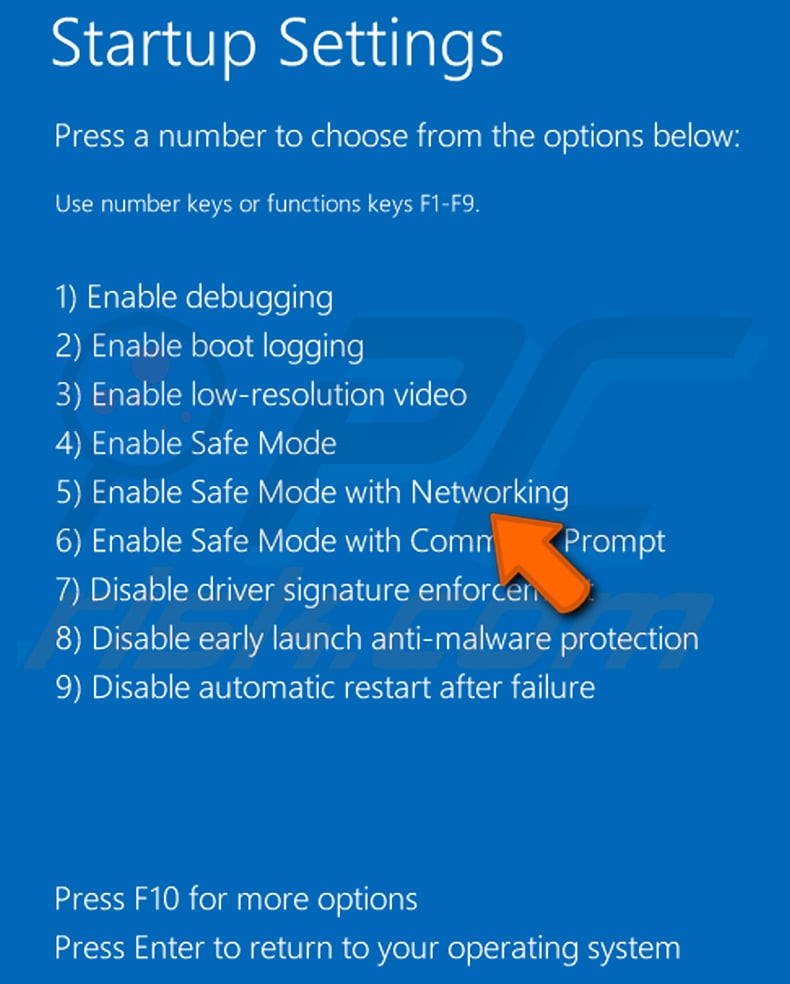
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
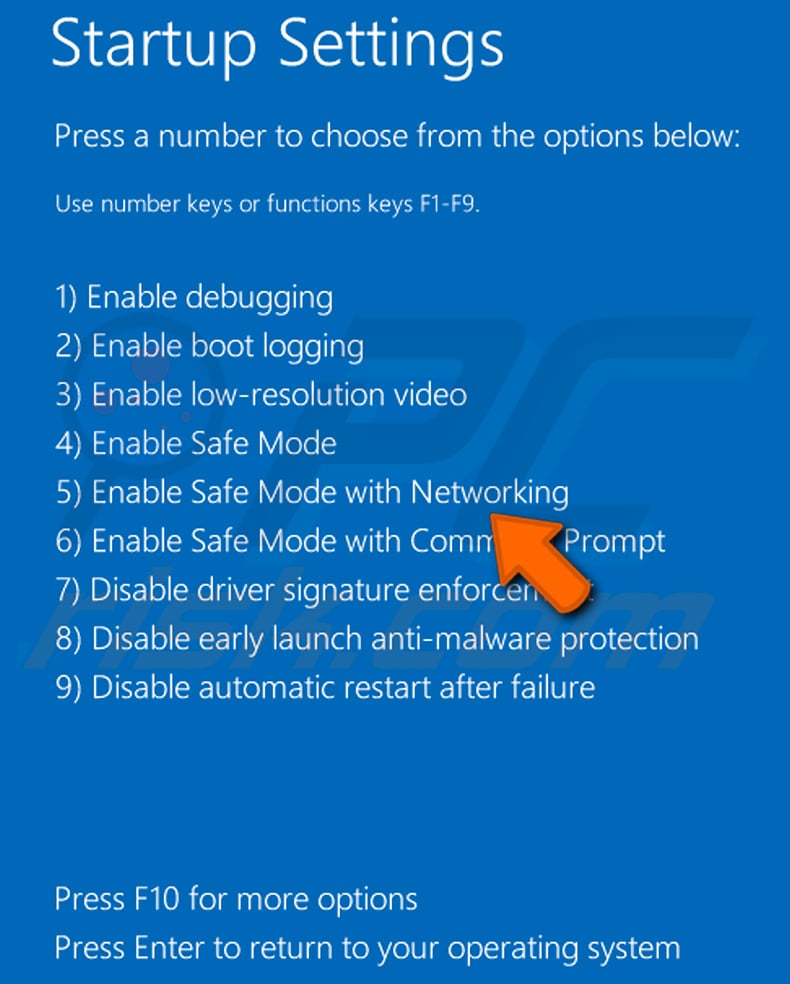
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
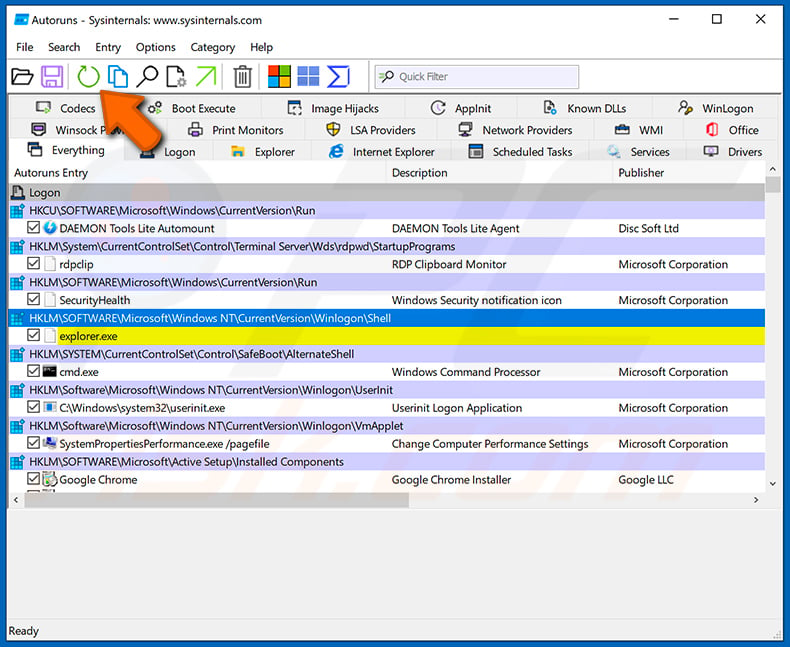
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
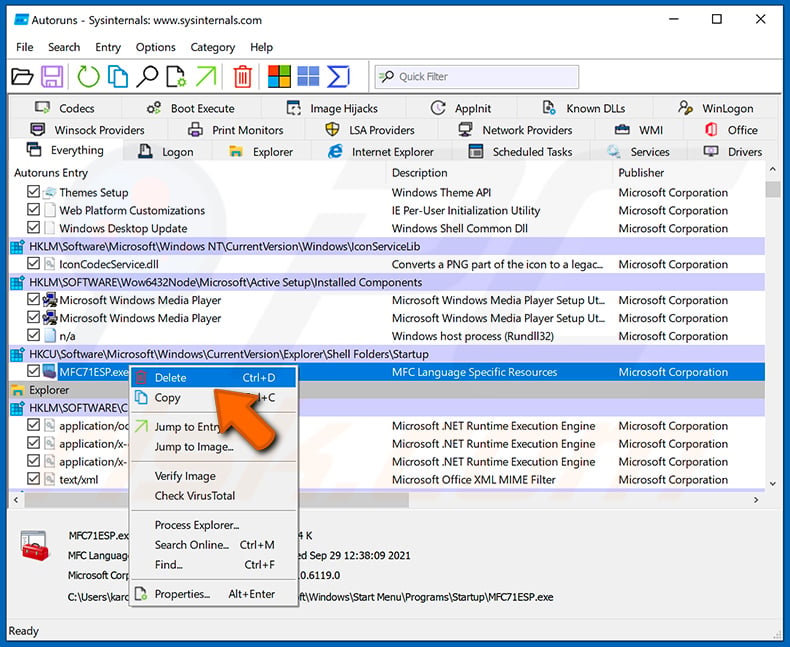
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
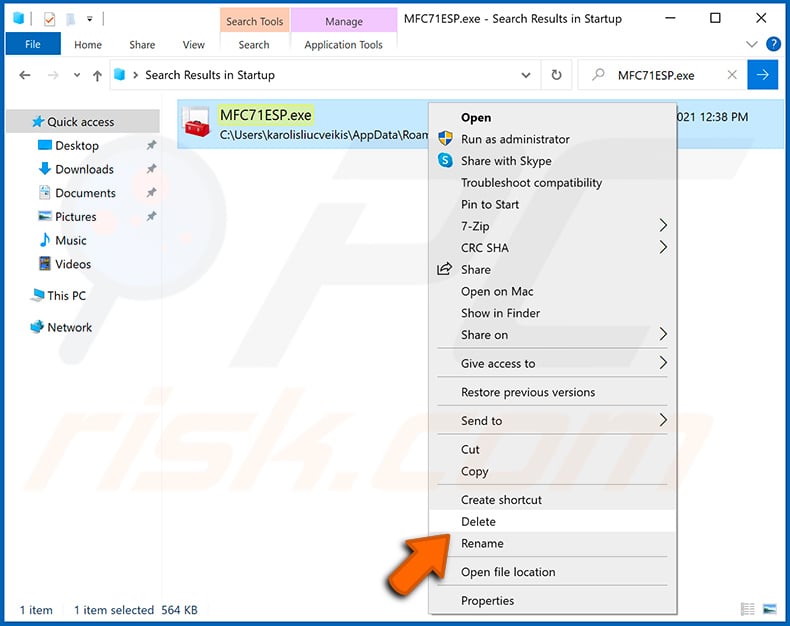
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Duke malware, should I format my storage device to get rid of it?
Generally, malware removal does not necessitate formatting.
What are the biggest issues that Duke malware can cause?
The threats posed by an infection depend on the malware's capabilities and the cyber criminals' modus operandi. Duke malware family consists of toolsets that are designed for varied purposes, ranging from additional malicious content download/installation to data extraction.
Typically, high-risk infections carry the following threats: multiple system infections, decreased system performance or failure, data loss, serious privacy issues, significant financial losses, and identity theft. Duke toolsets are used by the APT29 group, which is backed by the Russian state. Attacks motivated by political/geopolitical reasons may pose even greater threats.
What is the purpose of Duke malware?
As mentioned in the previous answer, Duke malicious programs are used by a Russian state-sponsored group that has connections to the Foreign Intelligence Service of the Russian Federation (SVR RF). Hence, these malware toolsets are used in attacks centered on intelligence gathering and cyber-espionage with a significant political/geopolitical element to them.
In general, malware is primarily used for profit; other reasons include the cyber criminals' amusement, personal vendettas, process disruption (e.g., websites, services, companies, etc.), and hacktivism.
How did Duke malware infiltrate my computer?
Duke malware toolsets have been proliferated using various techniques. The latest 2023 campaign entailed spam emails carrying malicious PDFs disguised as diplomatic invites from a German embassy. This campaign targeted Foreign Affairs ministries aligned with NATO.
However, other lures and distribution methods are likely. The most commonly used techniques include: spam mail, online scams, malvertising, dubious download channels (e.g., freeware and free file-hosting sites, P2P sharing networks, etc.), illegal software activation tools ("cracks"), and fake updates. Furthermore, some malicious programs can self-proliferate via local networks and removable storage devices.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is capable of detecting and eliminating most of the known malware infections. Note that since high-end malicious programs tend to hide deep within systems – running a full system scan is paramount.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion