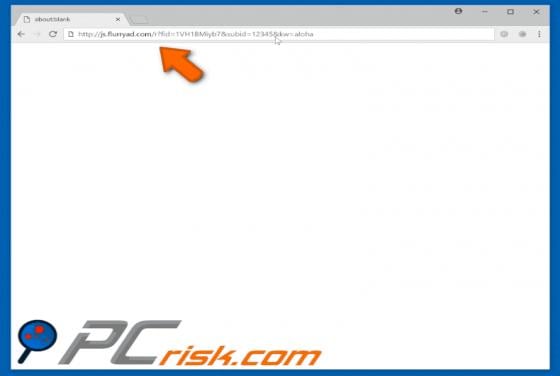
Flurryad.com POP-UP Redirect
flurryad.com is a rogue website virtually identical (or very similar) to click.new-posts.support, adxfactory.com click-now-on-this.online, and many more. This website redirects visitors to other untrustworthy and potentially malicious sites. In most cases, users visit flurryad.com inadvertently -