SkilledRecord Adware (Mac)
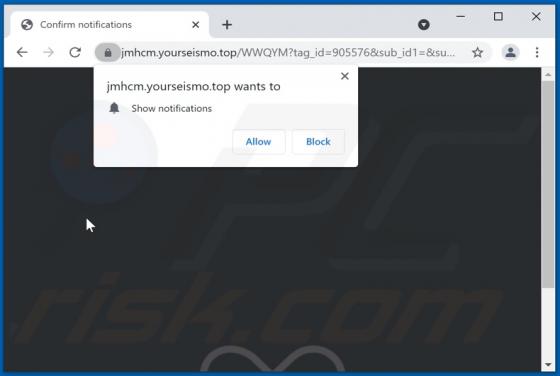
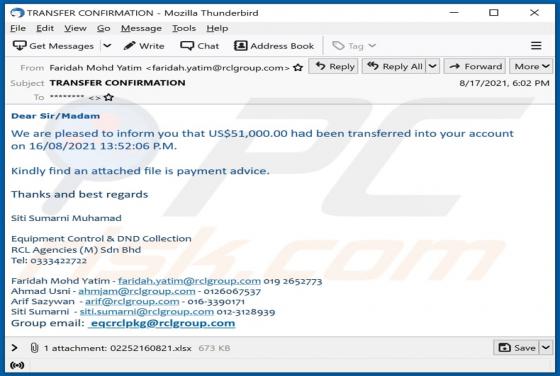
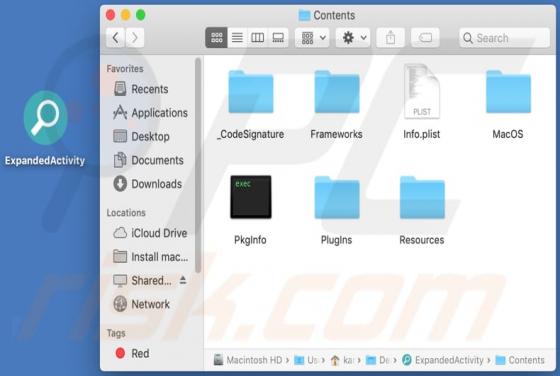
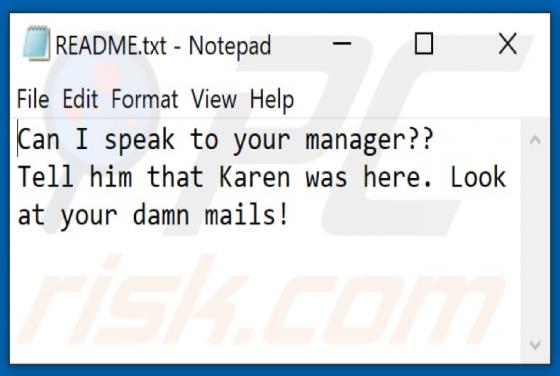
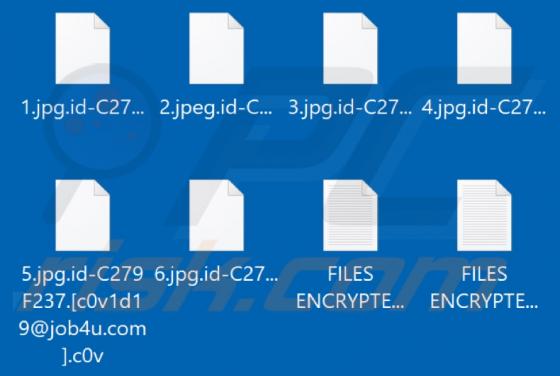
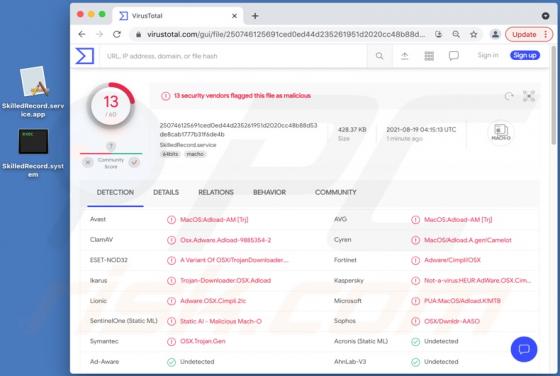
SkilledRecord is a rogue application classified as adware. It has browser hijacker qualities as well. This app operates by delivering intrusive advertisement campaigns and promoting fake search engines through modifications to browser settings. Additionally, SkilledRecord likely has data trackin