Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Realst?
Realst is a malicious program that targets sensitive information. Two versions of this malware exist, targeting Apple and Windows devices, respectively. Of particular concern is that some of its most recent versions are designed to exploit macOS 14 Sonoma, the upcoming operating system that is still in the development phase.

Realst malware overview
Realst is distributed through deceptive means to target users of both Windows and macOS platforms, masquerading as counterfeit blockchain games such as Brawl Earth, Dawnland, Destruction, Evolion, Olymp of Reptiles, Pearl, SaintLegend, and WildWorld.
Once executed, the game installers unleash information-stealing malware on the victim's device. On Windows, this includes malicious software like RedLine stealer, Raccoon stealer, and AsyncRAT, while on macOS, the Realst malware itself is deployed to compromise user data. It is worth noting that there are at least 16 known variants of the Realst stealer.
Realst stealer targets browsers such as Brave, Firefox, Google Chrome, Opera, OperaGX, and Vivaldi. The majority of variants make an effort to acquire the user's password by employing osascript and AppleScript spoofing techniques. Also, Realst steals data from Keychain (password management system) and Telegram.
Additionally, cryptocurrency wallets using browser extensions are also at risk of data theft. Realst steals data from wallets like Binance Wallet, Martian Wallet, Metamask, Nami, Phantom, Petra Aptos Wallet, Pontem Aptos Wallet, Temple, TronLink, and Trust Wallet, potentially compromising valuable financial information and digital assets.
Victims of Realst may experience several distressing issues due to the malware's sophisticated capabilities. Firstly, the theft of sensitive data, such as passwords from browsers and the Keychain, can lead to compromised online accounts and potential identity theft.
Secondly, with the malware targeting cryptocurrency wallets, victims might face substantial financial losses if their digital assets are stolen. Thirdly, the invasive nature of Realst's information-stealing techniques can result in a significant breach of privacy, with personal information falling into the hands of malicious actors.
| Name | Realst information stealer |
| Threat Type | Information stealer |
| Detection Names | Avast (Python:Agent-MH [Trj]), Combo Cleaner (Trojan.GenericKD.68013976), ESET-NOD32 (Multiple Detections), Kaspersky (HEUR:Trojan-PSW.OSX.HashBreaker.e), Microsoft (Trojan:HTML/Phish.IKU!MTB), Full List (VirusTotal) |
| Symptoms | Information stealers are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Malicious installers for blockchain games, malicious online advertisements, social media platforms. |
| Damage | Stolen passwords, monetary loss, identity theft, privacy breaches, and more. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
In conclusion, Realst is a highly sophisticated and dangerous malware targeting both Windows and macOS users through deceptive means, disguising itself as fake blockchain games. Its information-stealing capabilities, including the extraction of passwords, compromising of cryptocurrency wallets, and invasion of sensitive data, pose serious threats to victims' privacy and financial security.
More examples of malware targeting macOS are NokNok, JokerSpy, and Geacon.
How did Realst infiltrate my computer?
Users inadvertently infect their computers with Realst when they unknowingly download and install the malware disguised as fake blockchain games. The threat actors behind Realst distribute it through deceptive means, promoting the counterfeit games via online advertisements, social media, or other platforms.
The downloaded game installers contain the Realst malware, which then gets executed upon installation, compromising the user's system and enabling the malware to carry out its information-stealing activities.
The known games used to distribute Realst, as mentioned earlier, are Brawl Earth, Dawnland, Destruction, Evolion, Olymp of Reptiles, Pearl, SaintLegend, and WildWorld.
How to avoid installation of malware?
Download files and software from reputable sources, such as official web pages and stores. Avoid downloading content from unknown websites or clicking on suspicious links received through emails or social media messages. Regularly update the operating system and antivirus software. Use a reputable security solution.
Be skeptical of links and attachments in unexpected emails from unknown senders. Refrain from opening any links or files unless you are certain of their safety. Never download pirated software or use cracking tools. Do not trust advertisements on questionable websites.
If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate all threats.
Appearance of games used as a disguise for Realst stealer:
Update December 12, 2024 – Realst (alongside its Windows version) has been observed proliferating through an elaborate scam. This campaign has been active for months. Its starting point is deceptive private/direct messages (PMs/DMs) sent from accounts bearing convincing disguises of legitimate-seeming companies or ones imitating individuals from the victim's contacts.
This spam mail uses lures themed on business proposals and Web3 job offers. The messages schedule video calls with the recipients via fake conferencing software. The scheme heavily relies on AI (Artificial Intelligence) to create convincing fronts for bogus companies with websites, blogs, social media presence, etc.
AI is also used to craft sites for the fraudulent communication program; known names include "Meeten", "Meetio", "Meetone", and "Cuesee". When users download/install what they think is the software for facilitating the video call, they actually allow Realst to infiltrate their device.
It must be mentioned that aside from promoting Realst, these websites host JavaScript designed to steal cryptocurrency from browser-based wallets.
Screenshot of a scam site distributing Realst as the fake "Meeten" conferencing software:

Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Realst?
- STEP 1. Remove Realst related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
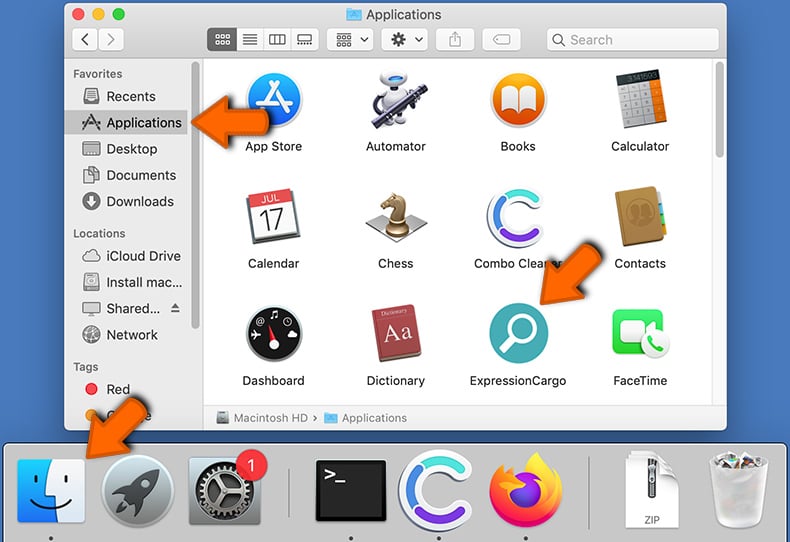
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
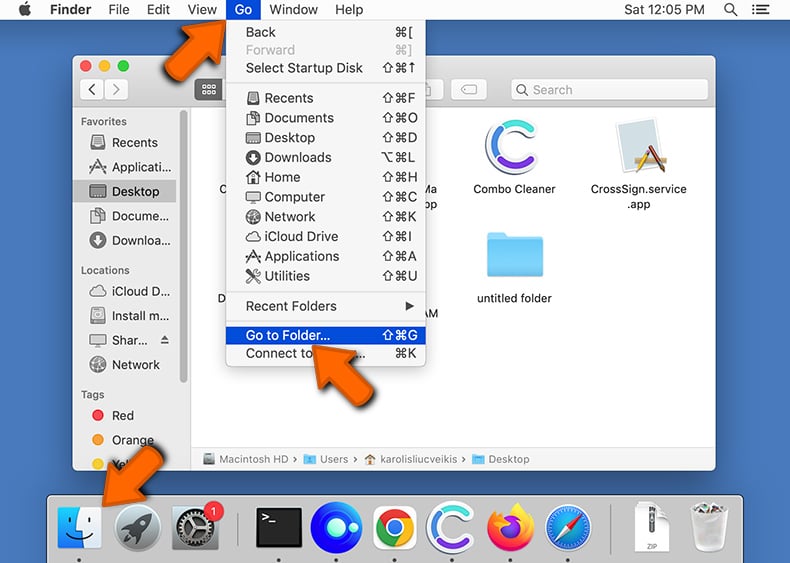
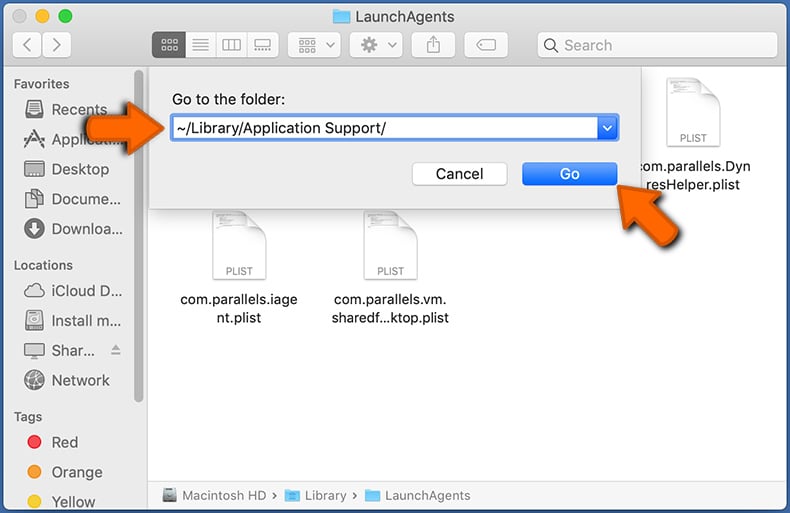
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
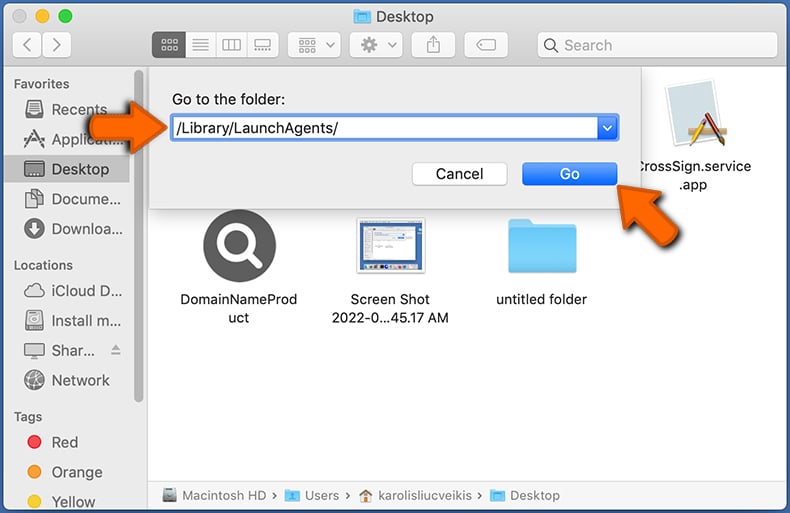
In the Go to Folder... bar, type: /Library/LaunchAgents/
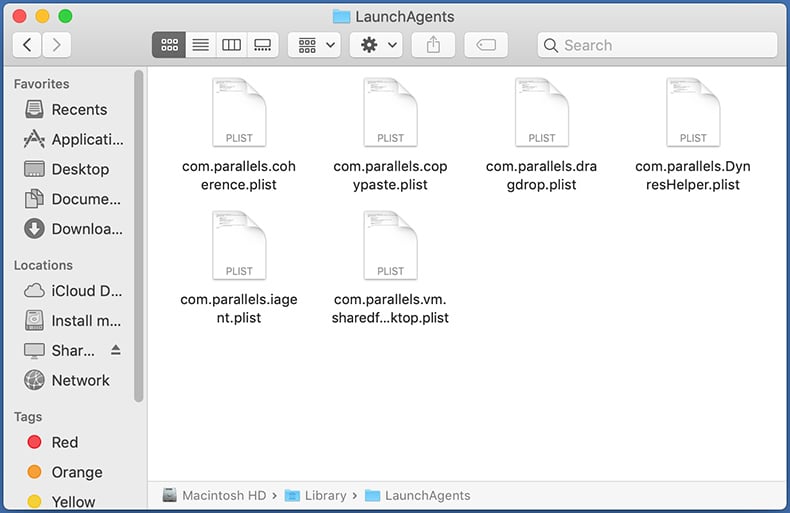
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
In the Go to Folder... bar, type: ~/Library/Application Support/
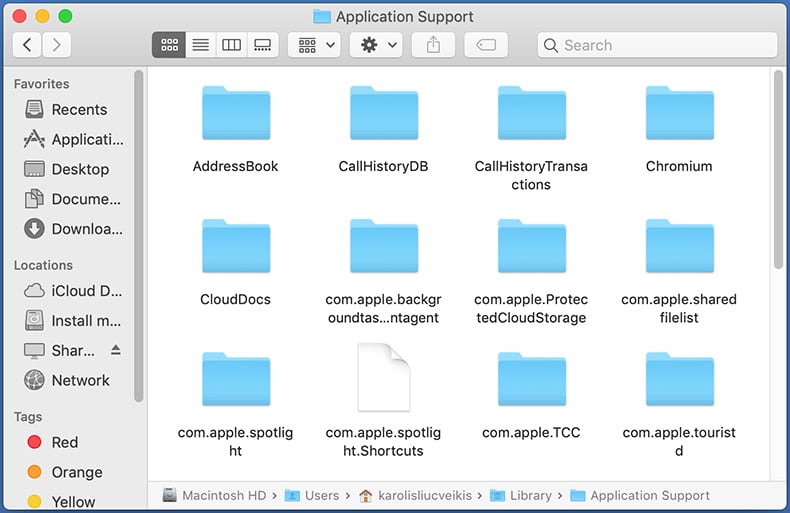
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
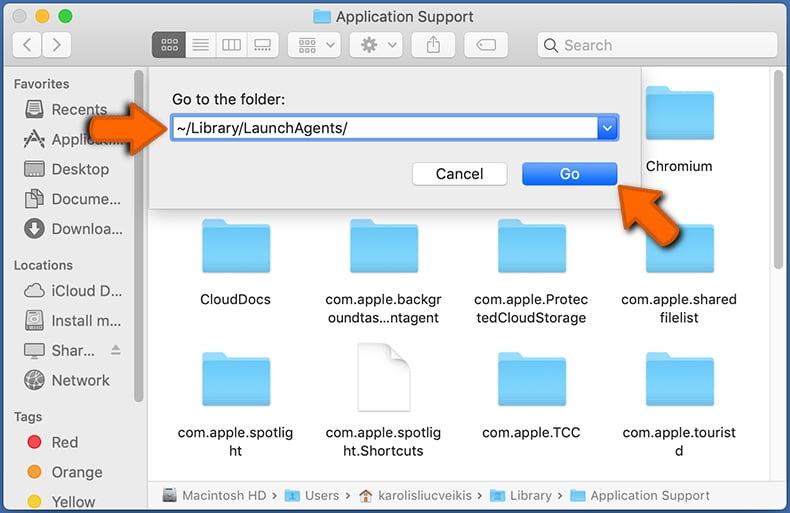
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
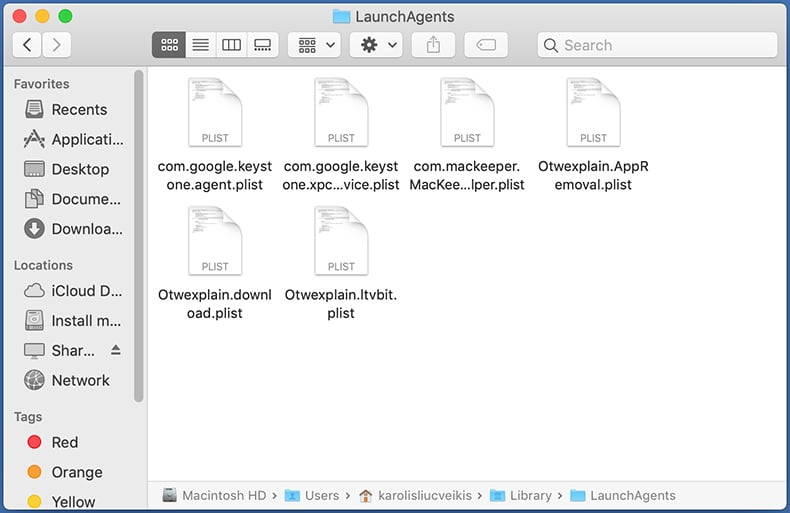
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
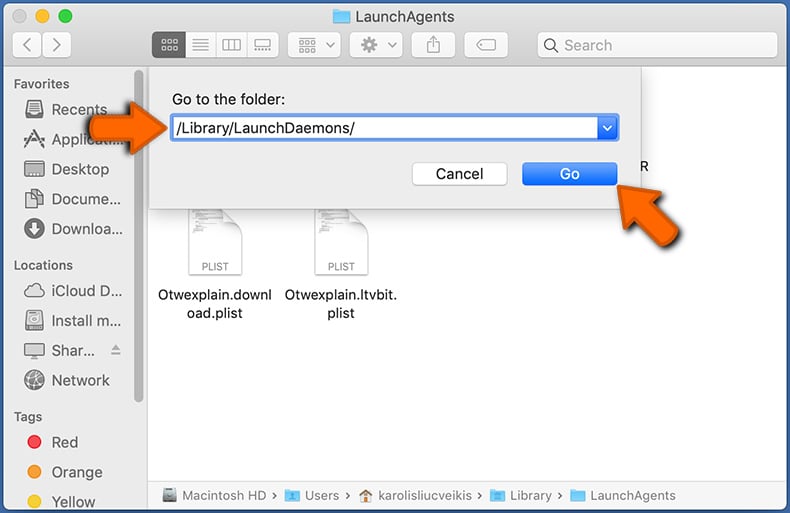
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
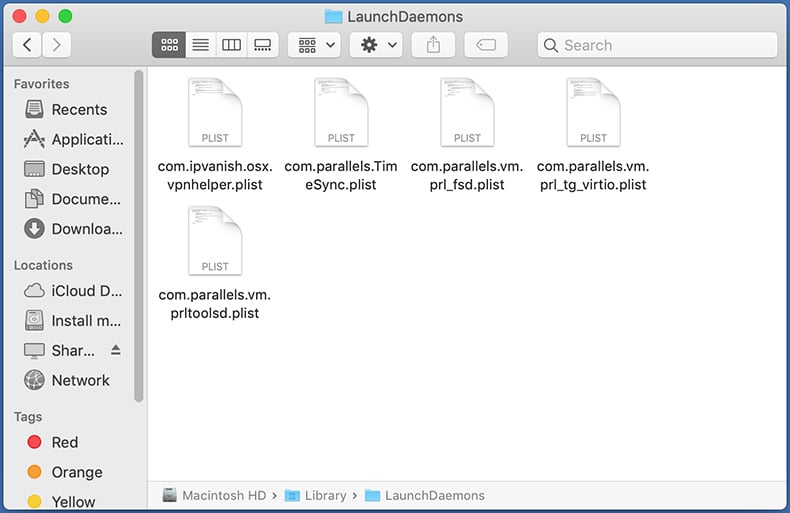
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
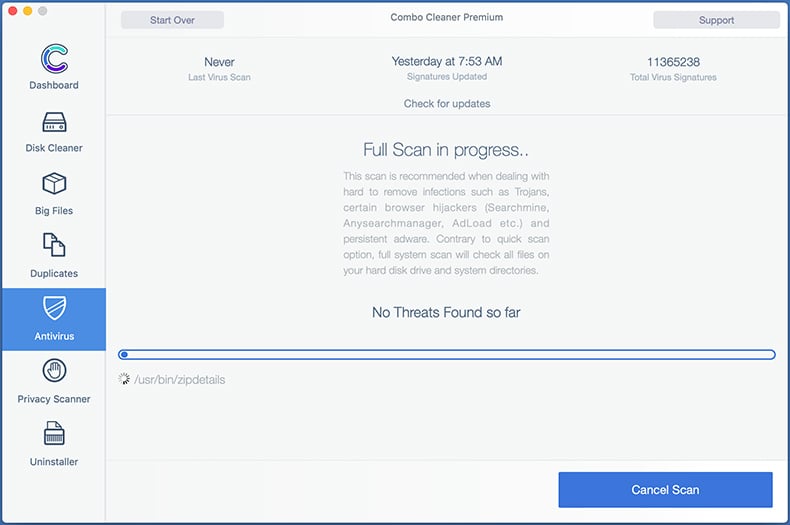
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
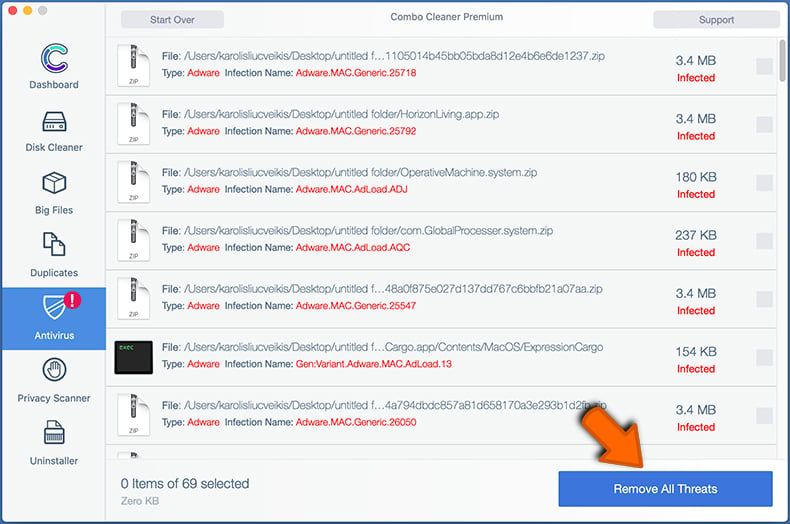
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
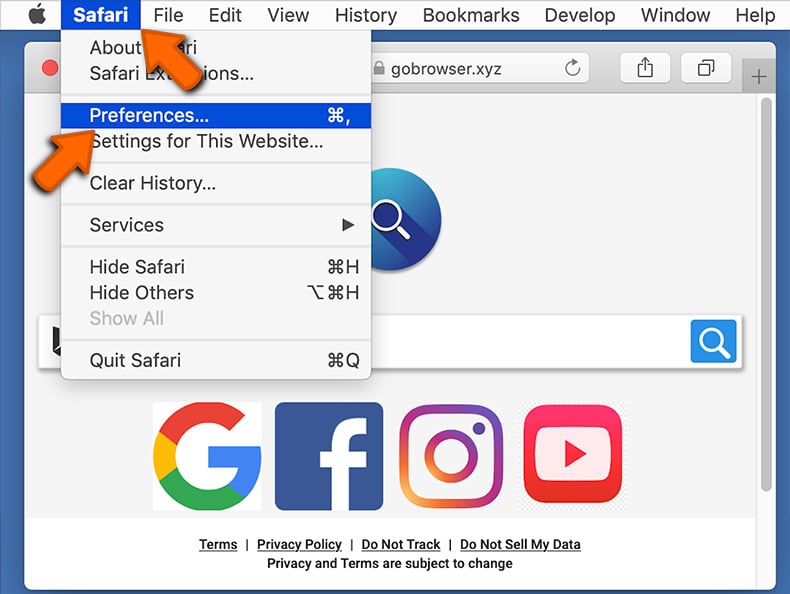
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
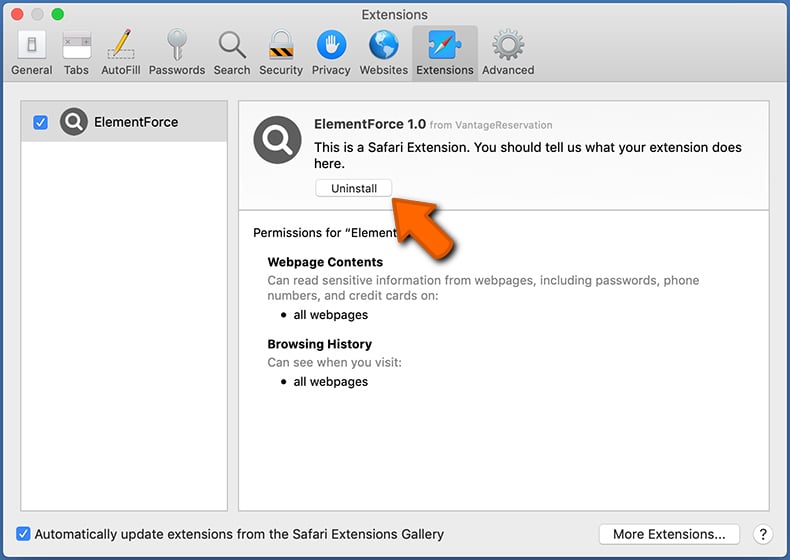
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
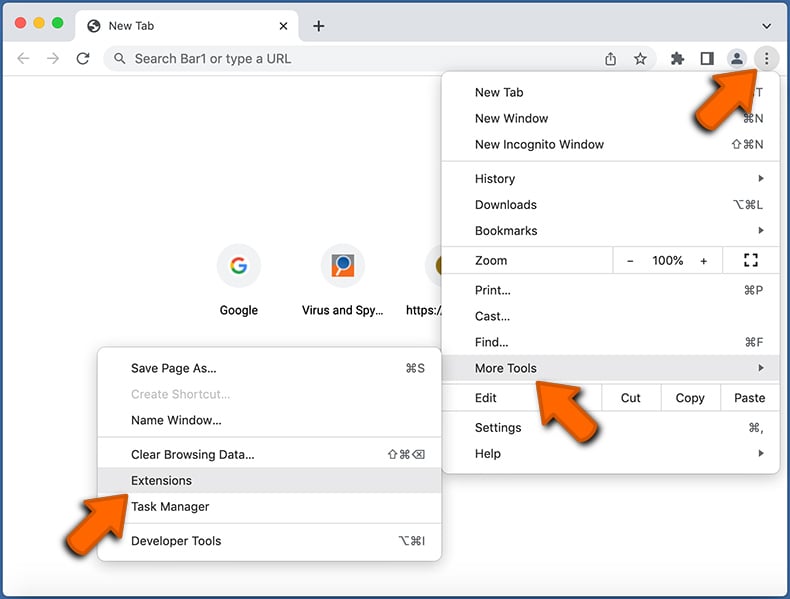
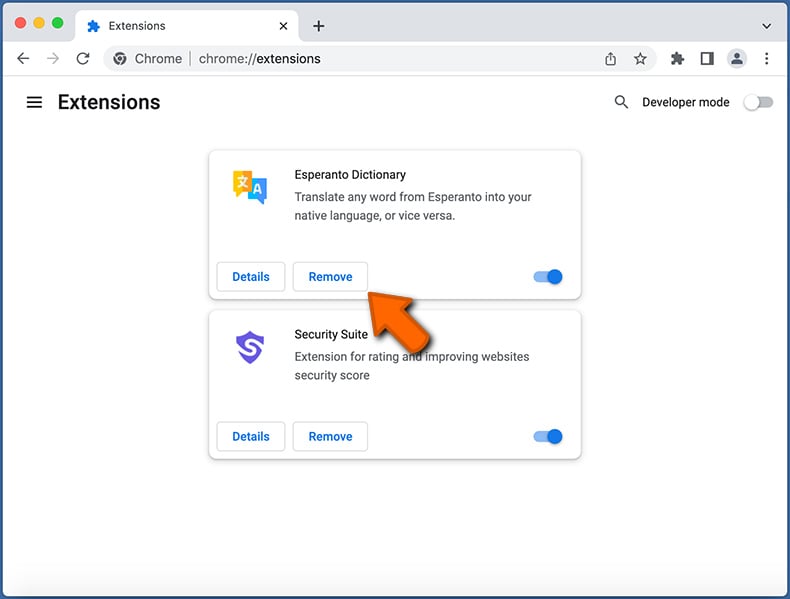
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
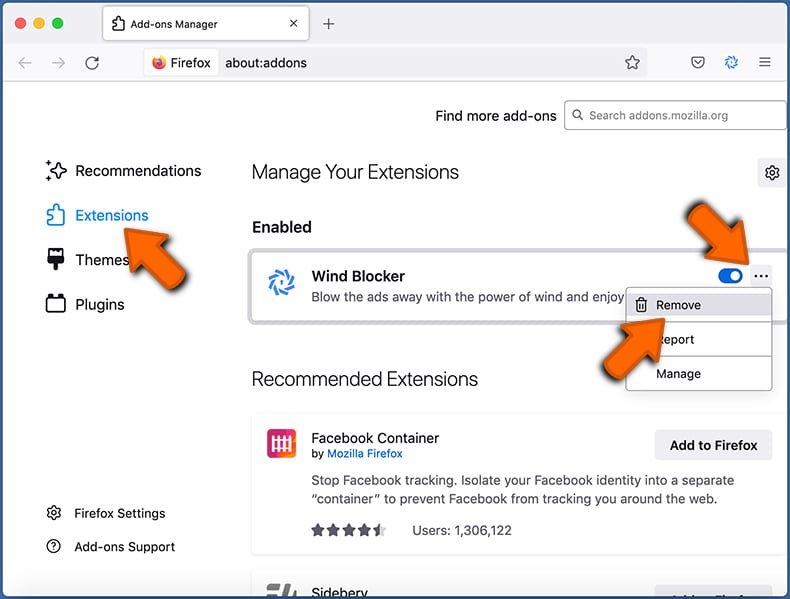
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
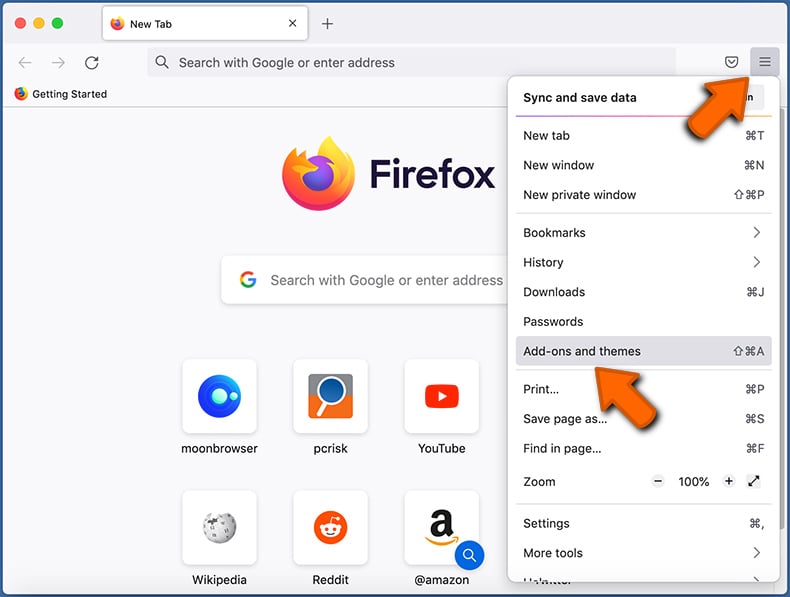
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Frequently Asked Questions (FAQ)
My computer is infected with Realst malware, should I format my storage device to get rid of it?
Malware such as Realst can be eliminated without formatting your system. You can use Combo Cleaner to achieve this.
What are the biggest issues that malware can cause?
The consequences of malware vary depending on its type/capabilities, and they can include identity theft, financial losses, data encryption, reduced computer performance, and potential further infections.
What is the purpose of Realst malware?
Realst steals information from multiple browsers, Telegram, Keychain, and crypto-related browser extensions.
How did Realst malware infiltrate my computer?
Users unintentionally infect their computers with Realst by unknowingly downloading and installing malware disguised as fake blockchain games. The known games used for Realst distribution include Brawl Earth, Dawnland, Destruction, Evolion, Olymp of Reptiles, Pearl, SaintLegend, and WildWorld. The threat actors distribute Realst deceptively through online advertisements, social media, or other platforms.
Will Combo Cleaner protect me from malware?
Combo Cleaner has the capability to detect and remove nearly all known malware infections. Sophisticated malware often conceals itself deep within the system. In order to address this, a full system scan is necessary.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate



▼ Show Discussion