How to remove the AMOS (Atomic) stealer-type malware from your operating system
Mac VirusAlso Known As: AMOS (Atomic) malware
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware AMOS (Atomic)?
AMOS (Atomic) stealer, is a malicious program targeting Mac OSes (Operating Systems). It is classified as a stealer – a type of malware that extracts and exfiltrates information from infected devices. At the time of writing, AMOS is actively sold on Telegram.

AMOS (Atomic) malware overview
Once we executed a sample of the AMOS stealer on our test machine, it displayed a fake pop-up window requesting access to System Preferences and prompting the user to enter their password. With this social engineering technique, the malware acquires its first bit of information (i.e., system password).
Afterwards, this stealer begins collecting relevant device data, e.g., Mac model name, UUID, CPU, RAM, OS version, and so on. AMOS can obtain a wide variety of information from compromised devices. This malware requests permission to access the Desktop and Documents, from which it can then download victims' files.
The stealer can also extract data from Keychain – the Mac password management system. Keychain can be used to store Wi-Fi credentials, website and FTP usernames/passwords, credit card details, etc.
AMOS steals information from browsers as well, including Google Chrome, Mozilla Firefox, Microsoft Edge, and others (full list). From browsers, this malware can acquire browsing data, Internet cookies, autofills, log-in credentials (i.e., IDs, usernames, email addresses, passwords, passphrases, etc.), credit card numbers, and so forth.
This stealer also targets cryptowallets and cryptocurrency-related browser extensions (full list). For example, AMOS can brute-force MetaMask seeds and private keys.
To summarize, the presence of software like AMOS on devices can result in severe privacy issues, significant financial losses, and even identity theft.
If you suspect that your Mac is infected with the AMOS stealer (or other malware) – immediately use an anti-virus to eliminate it without delay.
| Name | AMOS (Atomic) malware |
| Threat Type | Mac malware, Mac virus, Stealer |
| Detection Names | Avast (MacOS:Agent-YR [Trj]), Combo Cleaner (Gen:Variant.Trojan.MAC.Stealer.3), ESET-NOD32 (OSX/PSW.Agent.J), Kaspersky (UDS:DangerousObject.Multi.Generic), Full List Of Detections (VirusTotal) |
| Symptoms | Malicious programs are usually designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution Methods | Free software installers (bundling), infected email attachments, 'crack' software websites, social engineering, deceptive pop-up ads. |
| Damage | Stolen passwords and cryptocurrency wallets, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Malware in general
We have analyzed numerous malicious programs; RustBucket, MacStealer, KEYSTEAL, and GIMMICK are merely a few examples of malware that targets Mac OSes.
In most cases, malicious software is used to generate revenue – however, how it achieves the goal can vary drastically. Malware can have a wide range of functionalities, which can be in different combinations.
Regardless of how this software operates – its presence on a system endangers device integrity and user safety. Therefore, we strongly advise removing all threats immediately upon detection.
How did AMOS malware infiltrate my computer?
The AMOS stealer is sold on Telegram; hence, how it is distributed depends on the cyber criminals using it at the time. Generally, malware is proliferated using phishing and social engineering techniques.
Malicious software is usually disguised as or bundled with regular programs/media. When an infectious file is executed, run, or otherwise open – the infection chain (i.e., malware download/installation) is triggered.
The most commonly used distribution methods include: drive-by (stealthy/deceptive) downloads, malicious attachments and links in spam mail (e.g., emails, PMs/DMs, SMSes, etc.), online scams, dubious download sources (e.g., freeware and third-party websites, Peer-to-Peer sharing networks, etc.), malvertising, illegal software activation ("cracking") tools, and fake updates.
How to avoid installation of malware?
We highly recommend downloading only from official and verified channels. Additionally, all programs must be activated and updated using legitimate functions/tools, as illegal activation tools ("cracks") and third-party updaters can contain malware.
Another recommendation is to treat incoming emails and other messages with caution. The attachments or links found in suspect/irrelevant mail must not be opened, as they can be virulent. We advise being vigilant while browsing since fake and malicious online content usually appears ordinary and innocuous.
It is paramount to have a reputable anti-virus installed and kept up-to-date. Security software must be used to run regular system scans and to remove detected threats. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate threats.
Screenshot of a deceptive website spreading AMOS stealer:

Screenshots of various applications used as a disguise for AMOS stealer:
CardGame:

Adobe Photoshop CC 2023:

AMOS stealer malware sold on Telegram:

List of browsers targeted by AMOS stealer:
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Opera
- OperaGX
- Brave
- Vivaldi
- Yandex
List of cryptocurrency wallets and extensions targeted by AMOS stealer:
Atomic, Binance, Coinomi, Electrum, Exodus, Auro, BinanceChain, Byone, CLW, Coin98 Wallet, Coinbase, CWallet, Cyano, Crypto Airdrops & Bounties, DAppPlay, EVER Wallet, Exodus Web3 Wallet, Finnie, Flint Wallet, Freaks Axie, Guarda, Harmony Wallet, Hycon Lite Client, ICONex, iWallet, Jaxx Liberty, KardiaChain, Keplr, KHC, LeafWallet, Liquality, Martian Wallet for Sui & Aptos, Math Wallet, MetaMask, MewCx, Nabox, NeoLine, Oasis, Oxygen, Phantom, Polymesh, Rabby Wallet, Ronin, Slope, Starcoin, Station Wallet, Swash, Temple Wallet, TezBox, TON, Trezor Password Manager, TronLink, Tron Explorer, Trust Wallet, Wombat, XDCPay, XDEFI, Yoroi, ZilPay.
Update November 22, 2023 - Cyber criminals have recently started spreading AMOS stealer via malicious websites disguising as various browser updates (such as Safari, Google Chrome, or other).
Screenshot of a fake Google Chrome update page spreading AMOS stealer:

Screenshot of a fake Safari update page spreading AMOS stealer:

Screenshot of a fake Grand Theft Auto (GTA) 6 download website (alphagta6[.]com) spreading AMOS stealer:
![Fake Grand Theft Auto (GTA) 6 download website (alphagta6[.]com) spreading AMOS stealer](/images/stories/screenshots202312/lumma-amos-update-2023-12-20-deceptive-website.jpg)
Screenshot of a Twitter (X) post promoting this site:
![Twitter post promoting a fake Grand Theft Auto (GTA) 6 download website (alphagta6[.]com) spreading AMOS stealer](/images/stories/screenshots202312/lumma-amos-update-2023-12-20-twitter-post.jpg)
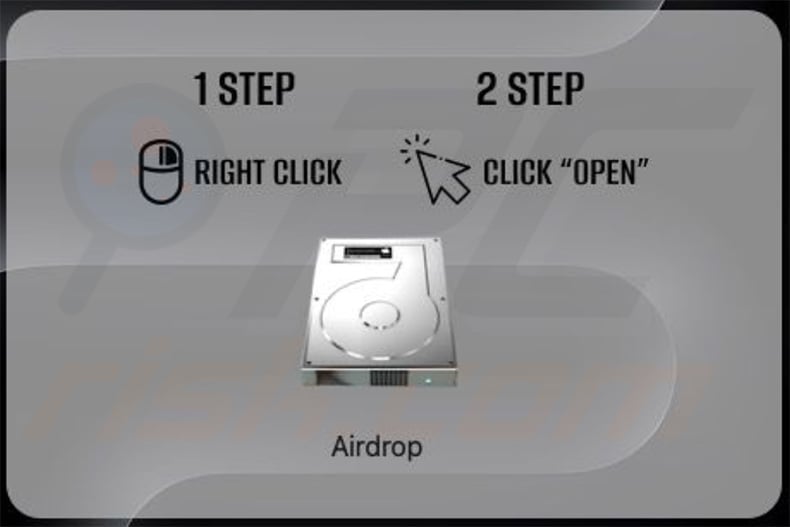
Screenshot of a fake Airdrop installer setup spreading AMOS stealer (source: MalwareHunterTeam):
Update January 17, 2024: The infostealers targeting macOS, namely KEYSTEAL, AMOS, and JaskaGo, underscore the persistent and adaptive nature of cybersecurity threats. Despite Apple's proactive measures, these malware variants exhibit continuous evolution, employing tactics such as code signature alterations, distribution method changes, and shifts in malicious behavior.
The threat landscape is characterized by the ability of these infostealers to evade static signature detection engines, emphasizing the importance of dynamic and advanced threat hunting techniques.
Update March 4, 2024: Recently, a new variant of the AMOS stealer has been uncovered. This updated version utilizes a Python script to maintain stealth and avoid detection. This variant has remained largely unnoticed, prompting the release of Indicators of Compromise to aid detection and mitigation efforts.
Notably, this variant has similarities in code with the RustDoor backdoor. The primary function of this malware is to extract sensitive data stored within browsers and specific system files, along with attempting to steal local user account passwords.
It achieves its objectives through a combination of Python and Apple Script code. Additionally, the malware appears to employ tactics to identify sandbox or emulator environments, further complicating detection measures.
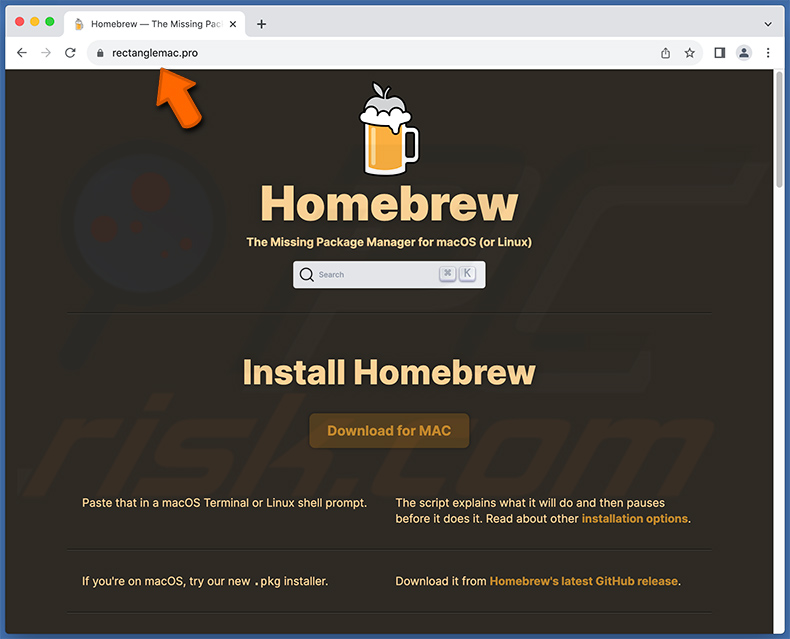
Update May 16, 2024 - AMOS Stealer has been recently observed being distributed via fake Homebrew download websites. The genuine Homebrew website is brew.sh, meaning that all other domains promoting this app should not be trusted. The same distribution method is also used to spread Cuckoo stealer.
Screenshot of a fake Homebrew download website (rectanglemac[.]pro) used to spread AMOS Stealer:
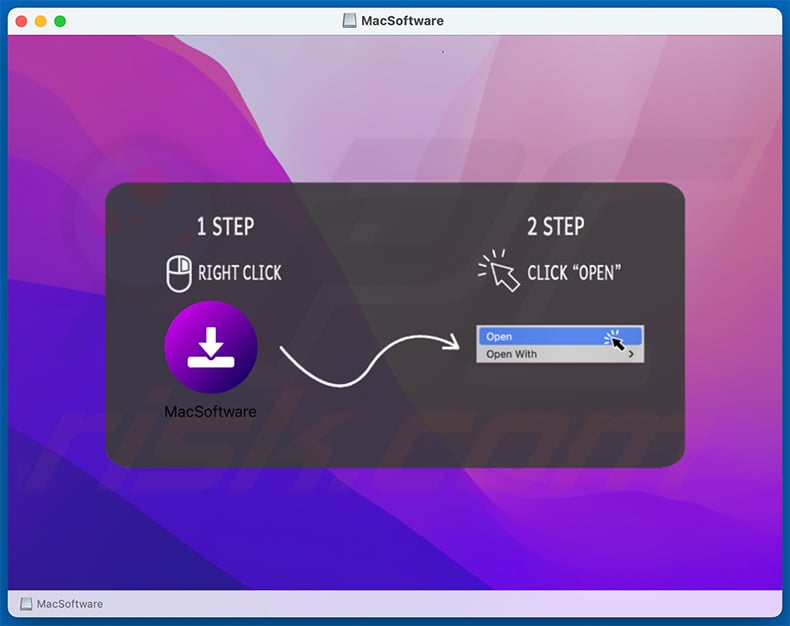
Update July 18, 2024 – new distribution method for AMOS has been discovered. This stealer is proliferated via a malvertising campaign under the guise of a Microsoft Teams app for Mac. The promotion is held by abusing the Google Ads service; when users enter a query related to "Microsoft Teams", they are presented with a malicious advertisement as one of the topmost Google search results.
Clicking on the ad causes a multi-stage redirect that lands on a malicious page, which continues the charade of offering Microsoft Teams for Mac. Through a filtering system, only genuine users (excluding bots, etc.) are allowed to access the site. The downloaded installer (containing AMOS) is generated with a different filename and size each time.
The setup requests installation via right-click, thus evading protection measures against unsigned installers. Following successful installation, AMOS stealer proceeds to ask permissions and the system password, as described in the article above.
Update November 18, 2024 - Cybercriminals have created fake websites impersonating the AI editor EditPro to distribute malware. These sites are promoted through ads and fake deepfake videos on X. Clicking "Get Now" downloads malware disguised as the EditProAI app, targeting macOS users and Windows users.
Screenshot of a malicious installer using Shell Script to inject AMOS Stealer:
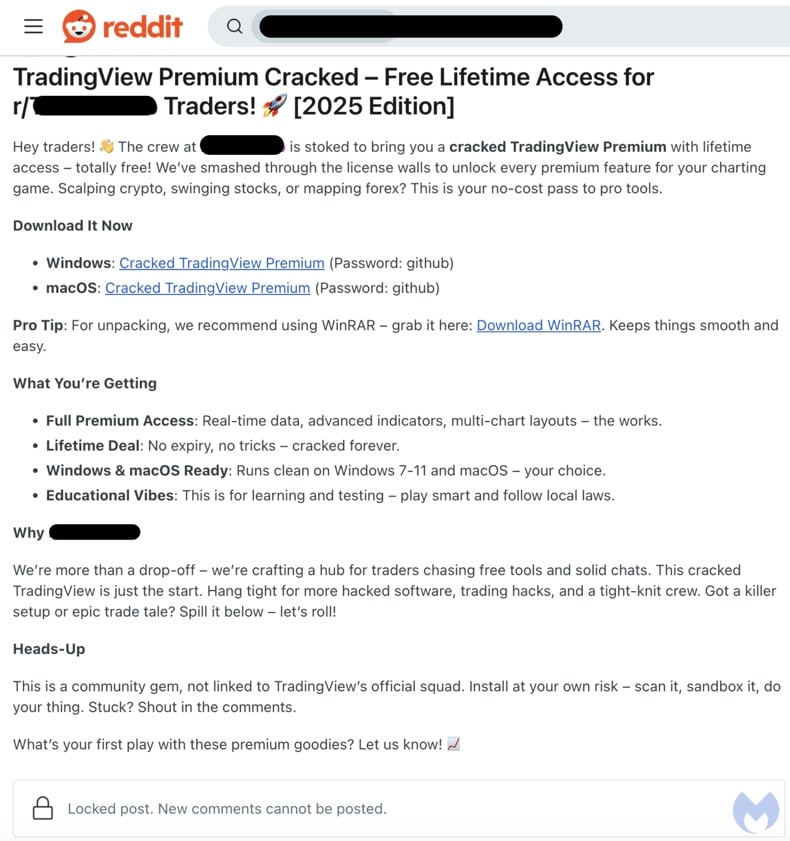
Update March 20, 2025 – new campaign spreading the AMOS (Atomic) stealer has been discovered. The malware is promoted through Reddit posts presenting it as "cracked" software versions. The campaign also targets Windows users with the Lumma stealer.
Known deceptive posts centered on cryptocurrency trading by pushing pirated tools, like TradingView. This is an active and involved campaign wherein the threat actor participates in the comments and provides aid to interested Redditors.
Reddit post spreading AMOS stealer as a "cracked" version of TradingView (image source – Malwarebytes):
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is AMOS (Atomic) stealer?
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
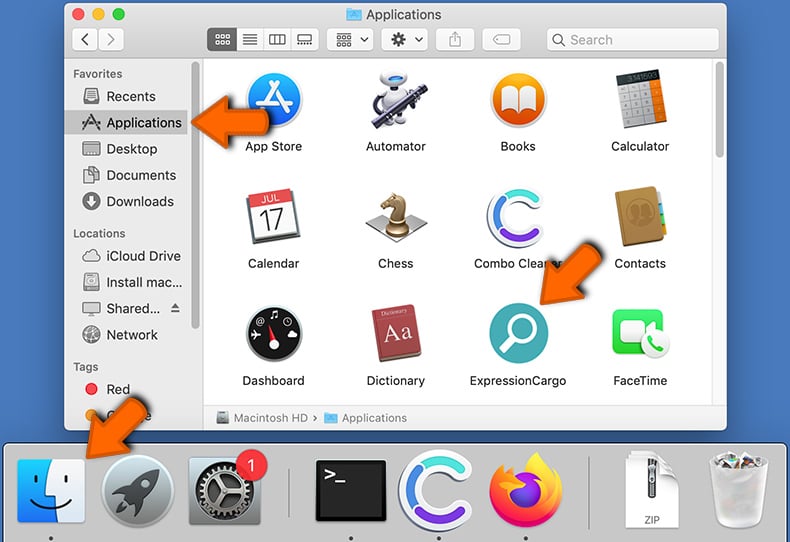
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
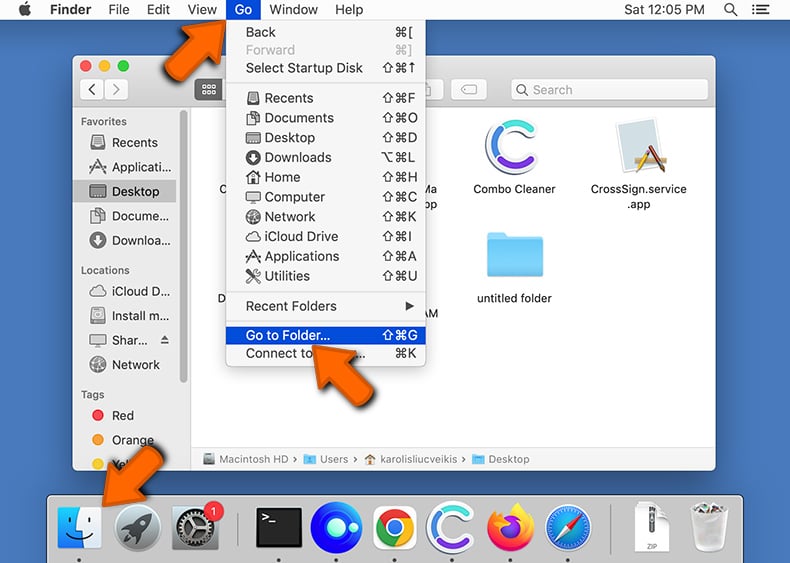
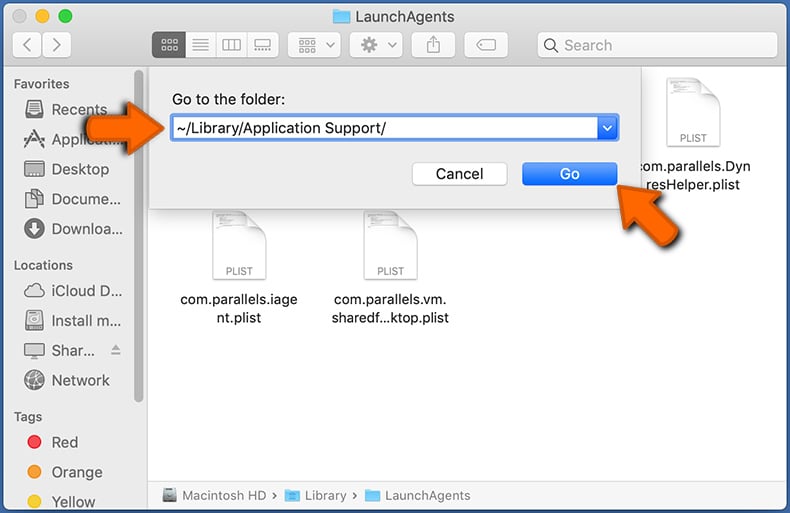
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
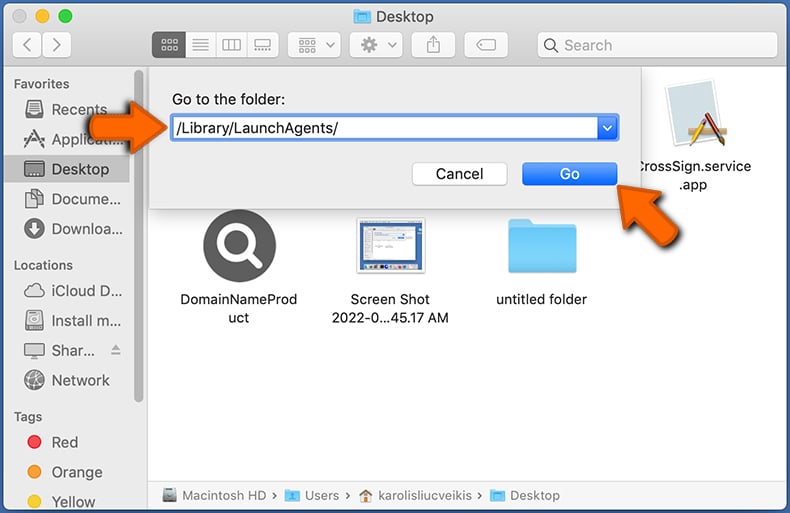
In the Go to Folder... bar, type: /Library/LaunchAgents/
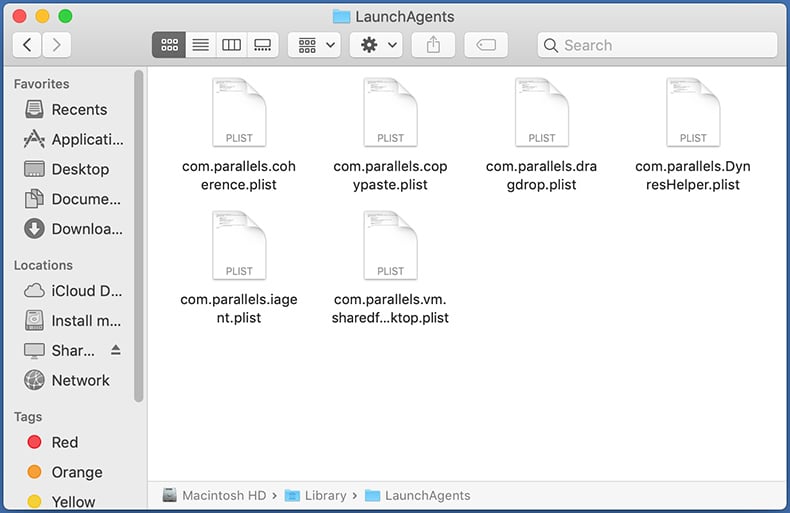
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
In the Go to Folder... bar, type: ~/Library/Application Support/
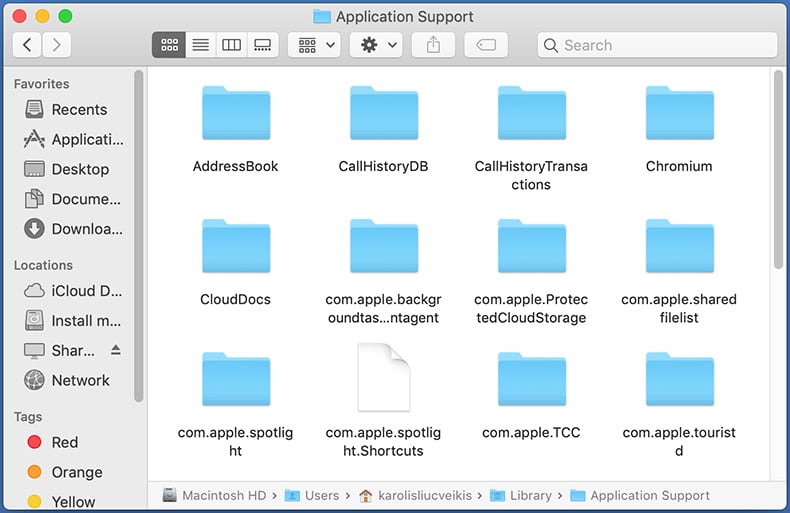
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
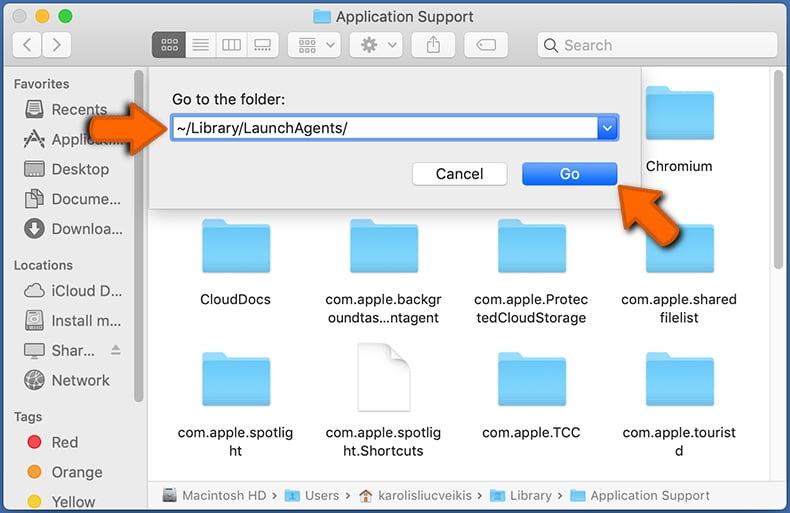
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
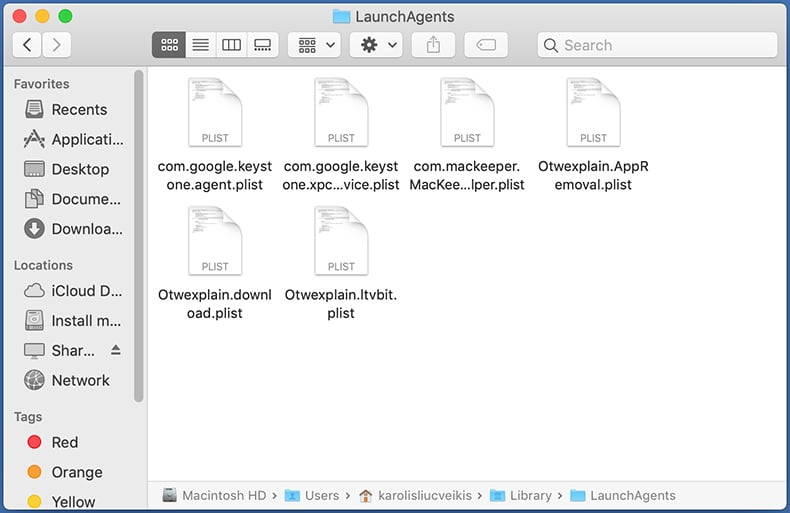
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
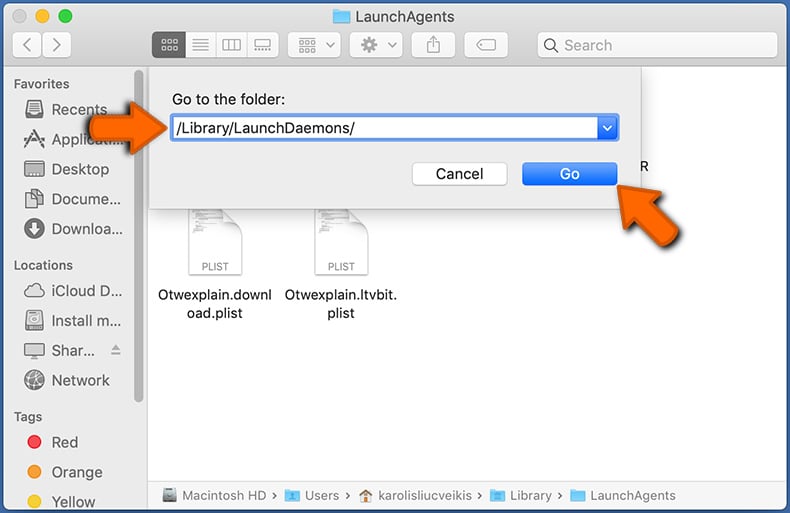
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
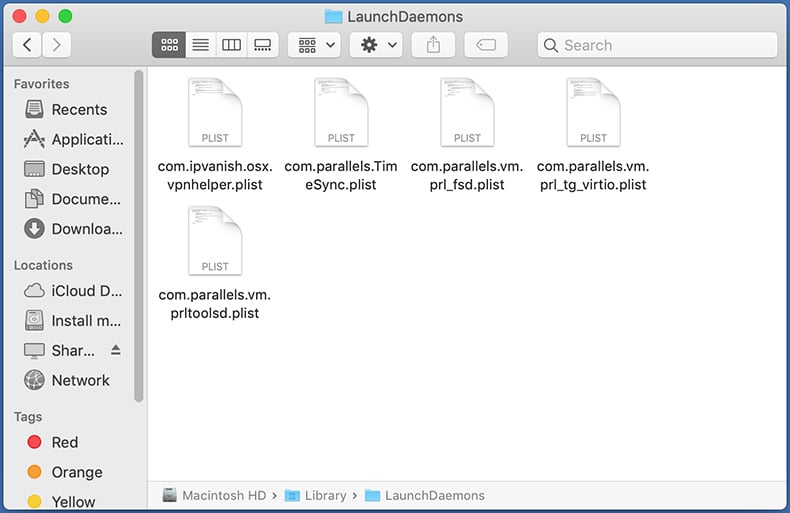
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
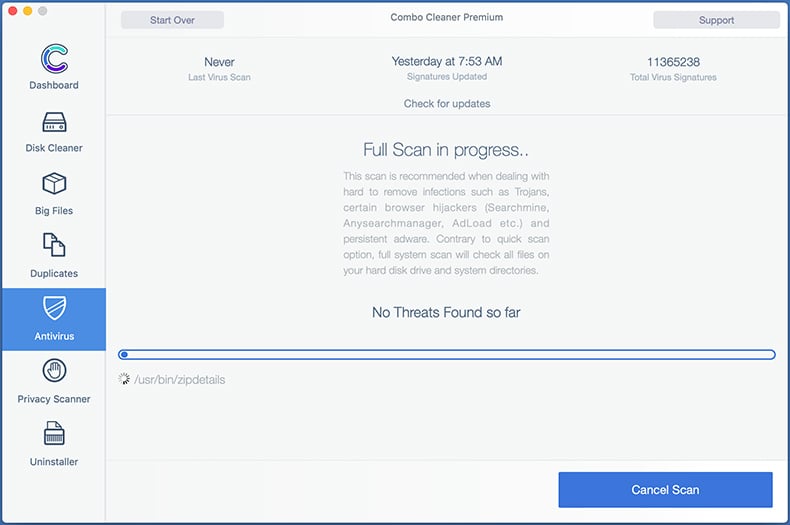
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
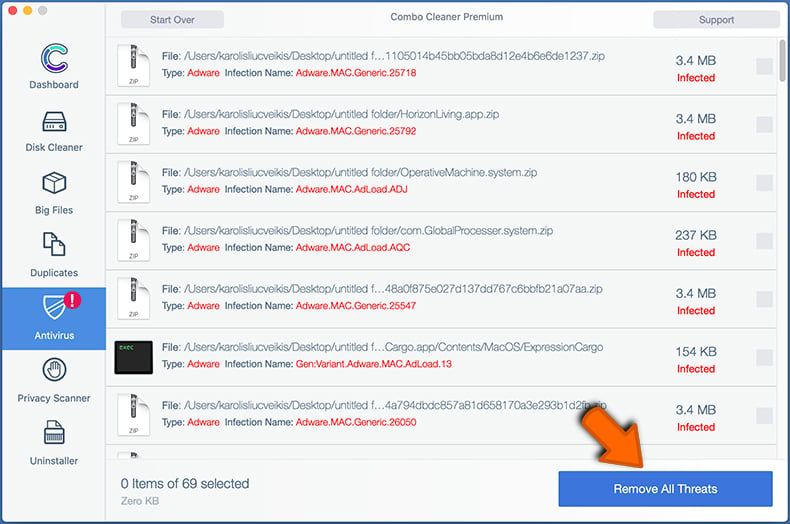
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
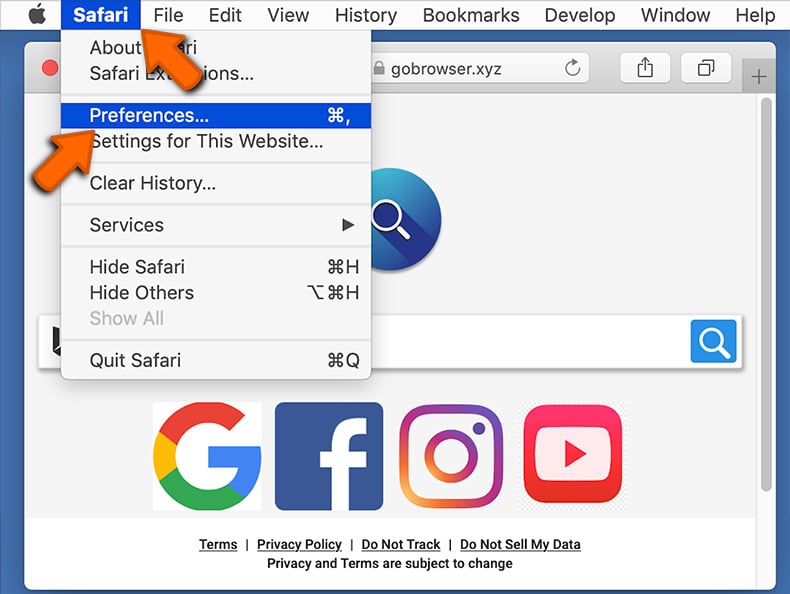
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
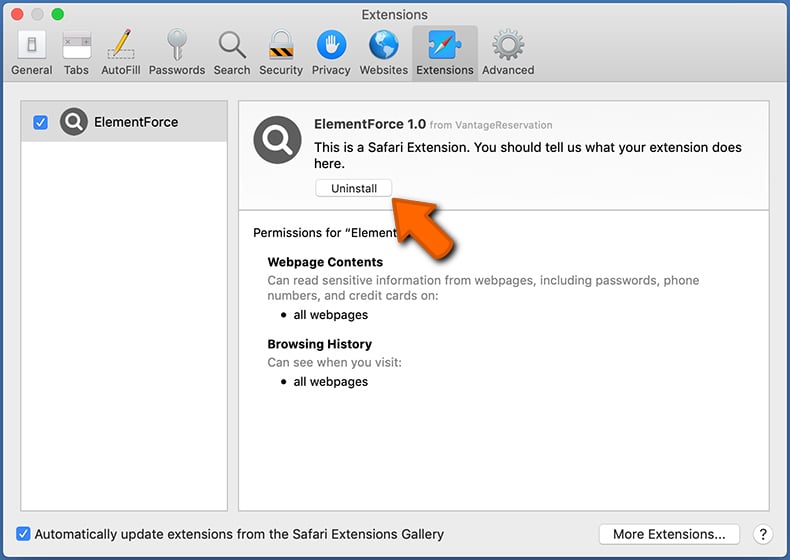
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
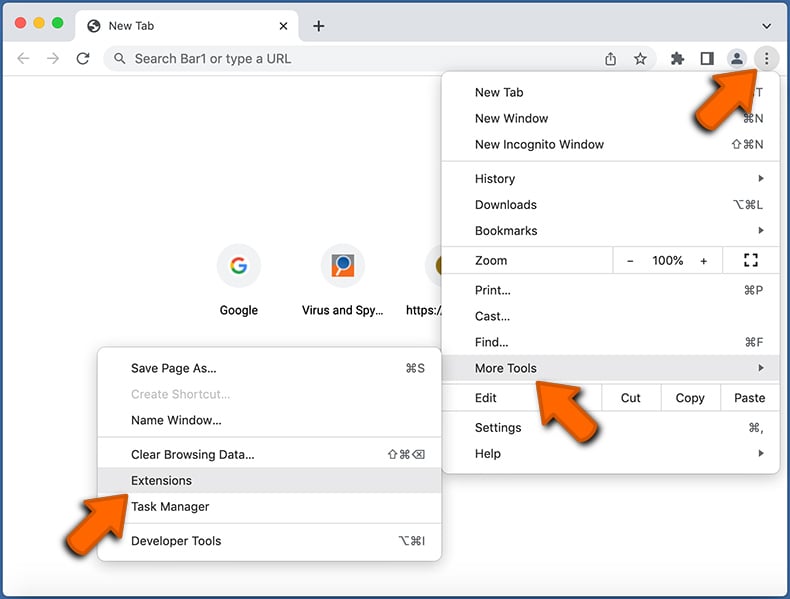
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
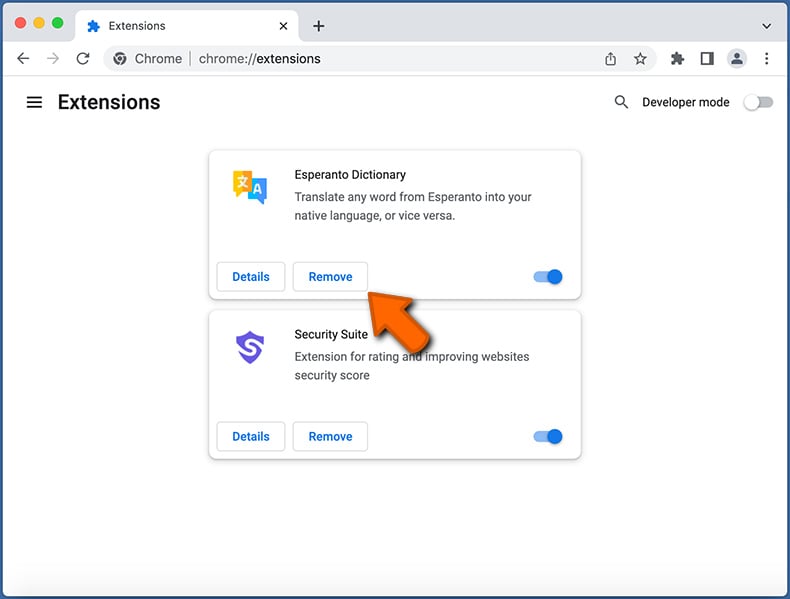
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
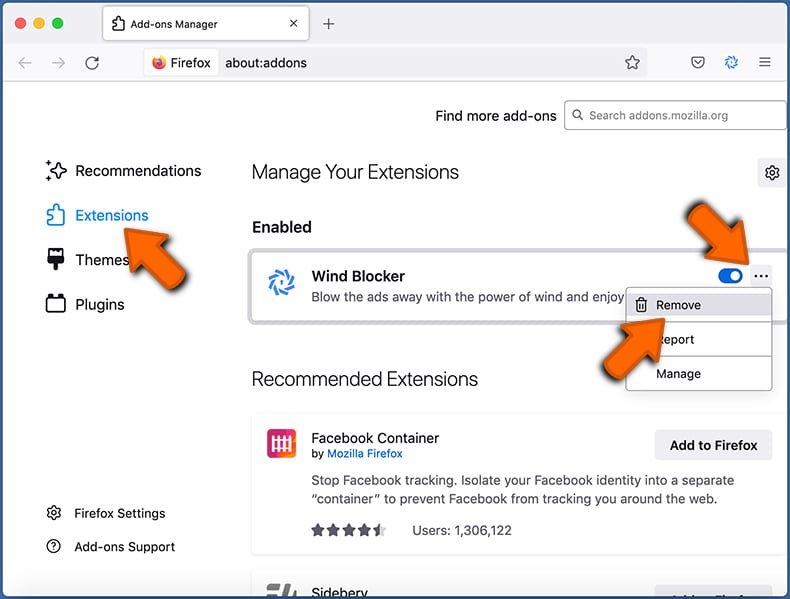
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
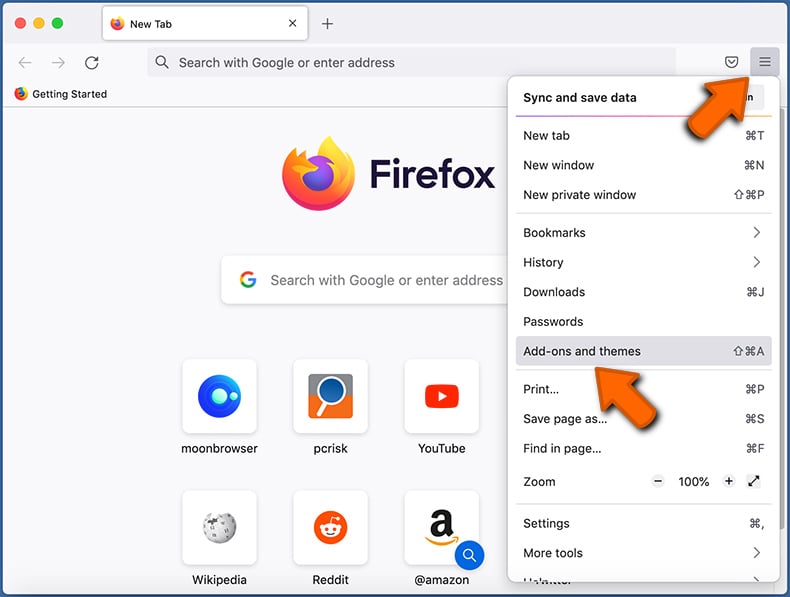
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Frequently Asked Questions (FAQ)
My computer is infected with AMOS malware, should I format my storage device to get rid of it?
No, most malicious programs can be removed without formatting.
What are the biggest issues that AMOS malware can cause?
The threats posed by malware depend on its capabilities and the cyber criminals' aims. AMOS is a stealer – a type of program designed to extract and exfiltrate information from infected systems. Typically, infections of this kind can lead to severe privacy issues, financial losses, and identity theft.
What is the purpose of AMOS malware?
In most cases, malware is used for profit. However, this software can also be used for the cyber criminals' amusement or to disrupt processes (e.g., websites, services, companies, etc.). Furthermore, malware attacks may be motivated by personal vendettas or political/geopolitical reasons.
How did AMOS malware infiltrate my computer?
Malware is primarily spread through drive-by downloads, dubious download channels (e.g., freeware and free file-hosting sites, P2P sharing networks, etc.), spam emails and messages, online scams, malvertising, illegal program activation tools ("cracks"), and fake updates. What is more, some malicious programs can self-proliferate via local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is designed to detect and eliminate threats. It is capable of removing practically all known malware infections. Note that performing a complete system scan is essential since sophisticated malicious software typically hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion