How to eliminate KEYSTEAL trojan-type malware from the operating system
Mac VirusAlso Known As: KEYSTEAL malware
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is KEYSTEAL?
KEYSTEAL is the name of a trojan targeting macOS Keychain data. This malware arrives onto systems as a trojanized app called ResignTool. Due to how sensitive the information stored on the Mac Keychain can be - this malware poses significant threats to user privacy.

KEYSTEAL malware overview
The variant of KEYSTEAL that we analyzed was installed by a malicious installer claiming to carry the ResignTool application. Following installation, the malware retained this disguise. However, it is more than just a combination of the same app icon and name; it is a modified ("trojanized") version of ResignTool.
ResignTool is designed to change the signing information on IPA format archive files used on iOS. This application is free but not available on Apple's App Store. Therefore, this program can only be obtained from open-source project hosting and file-sharing platforms - which opens up an avenue for cyber criminals to trojanize ResignTool and proliferate its malicious versions.
KEYSTEAL malware targets Keychain information. The password management system of macOS called Keychain can store a variety of vulnerable data, including usernames/passwords, private keys, digital certificates, secure notes, and other sensitive information.
This trojan also obtains the user account password by displaying a pop-up requesting this information after its installation is completed.
It is noteworthy that once KEYSTEAL concludes its malicious activities, it runs ResignTool's original routine - thus covering its tracks.
To summarize, KEYSTEAL infections can result in severe privacy issues, financial losses, and even identity theft.
| Name | KEYSTEAL malware |
| Threat Type | Mac malware, Mac virus, Trojan, password-stealing virus. |
| Detection Names (installer) | Avast (MacOS:KCSteal-A [Trj]), Kaspersky (UDS:Trojan-PSW.OSX.KCSteal), Lionic (Trojan.OSX.KCSteal.4!c), Symantec (OSX.Trojan.Gen), Full List Of Detections (VirusTotal) |
| Detection Names (app) | Kaspersky (HEUR:Trojan-PSW.OSX.KCSteal.gen), ZoneAlarm by Check Point (HEUR:Trojan-PSW.OSX.KCSteal.gen), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution Methods | Free software installers (bundling), infected email attachments, 'crack' software websites, social engineering, fake Flash Player installers, deceptive pop-up ads. |
| Additional Information | KEYSTEAL may infiltrate system as a trojanized ResignTool app. |
| Damage | Stolen passwords and banking information, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Mac malware examples
We have analyzed countless malware samples; GIMMICK, UpdateAgent, SysJoker, DazzleSpy, and NUKESPED are a few examples of those targeting mac Operating Systems.
Malicious software can have a wide variety of functionalities, and these functions can be in different combinations. However, regardless of whether a malicious program steals information, encrypts data, mines cryptocurrency, or performs other activities - its presence on a system endangers device integrity and user safety. Therefore, we strongly recommend eliminating all threats immediately upon detection.
How did KEYSTEAL infiltrate my computer?
Since KEYSTEAL infiltrates systems as a trojanized ResignTool application, it could be that its proliferation methods target users searching for this specific app to download. While ResignTool is free, it is unavailable on Apple's official store - hence, it can only be obtained from open-source project platforms, free file-hosting websites, freeware pages, and similar channels.
However, it is just as likely that using ResignTool is a handy way to lower user suspicion since their immediate searches for information on it would lead to a description of the legitimate software. Therefore, it could be that the KEYSTEAL trojan is spread using several techniques.
Generally, malware is proliferated by employing phishing and social engineering tactics. Virulent files can be in various formats (e.g., archives executables, documents, etc.) and infect devices when they are opened.
The most widely used malware distribution methods include: drive-by (stealthy/deceptive) downloads, dubious download sources (e.g., freeware and free file-hosting websites, Peer-to-Peer sharing networks, etc.), online scams, malicious attachments and links in spam emails/messages, malvertising, illegal software activation ("cracking") tools, and fake updates.
How to avoid installation of malware?
We highly recommend downloading only from official and verified sources. It is just as important to activate and update software with legitimate tools, as illegal activation tools ("cracks") and third-party updaters can contain malware.
We advise caution when browsing since fraudulent and dangerous online content usually appears legitimate and harmless. Another recommendation is to be vigilant with incoming emails, DMs/PMs, and other messages. The attachments and links found in suspect/irrelevant mail must not be opened, as they can be malicious and cause infections.
We must emphasize the importance of having a reputable anti-virus installed and kept updated. Security programs must be used to perform regular system scans and to remove threats and issues. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate threats.
KEYSTEAL trojan installation setup:

Pop-up (targeting user passwords) displayed after KEYSTEAL trojan's installation:

Appearance of KEYSTEAL trojan disguised as the ResignTool application:

Update 17 January 2024: The infostealers targeting macOS, namely KEYSTEAL, Atomic, and JaskaGo, underscore the persistent and adaptive nature of cybersecurity threats. Despite Apple's proactive measures, these malware variants exhibit continuous evolution, employing tactics such as code signature alterations, distribution method changes, and shifts in malicious behavior.
The threat landscape is characterized by the ability of these infostealers to evade static signature detection engines, emphasizing the importance of dynamic and advanced threat hunting techniques.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "KEYSTEAL"?
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove KEYSTEAL malware using Combo Cleaner:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
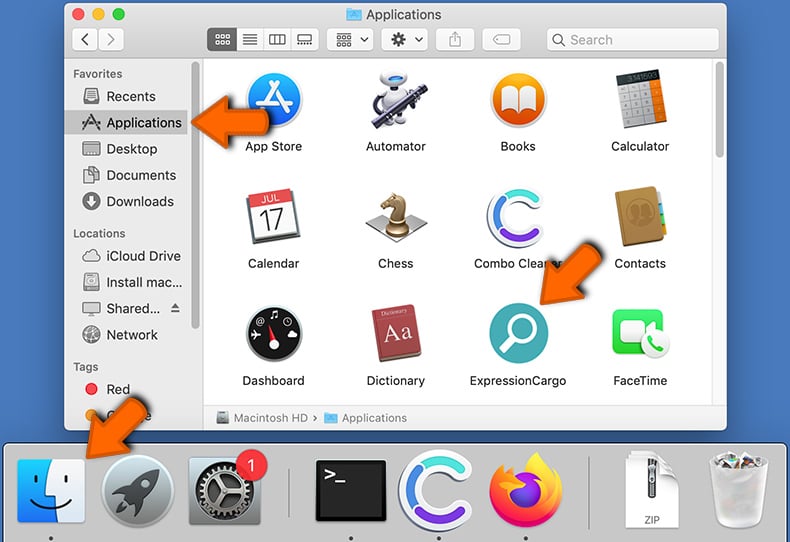
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
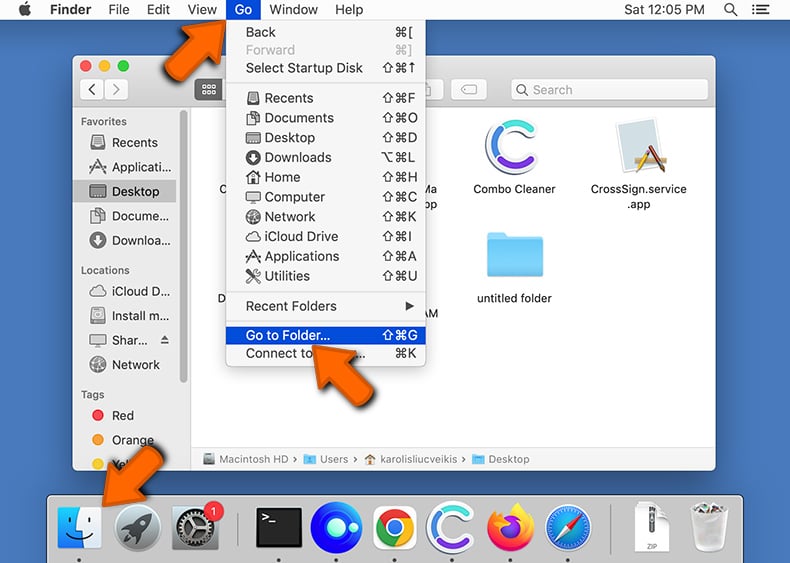
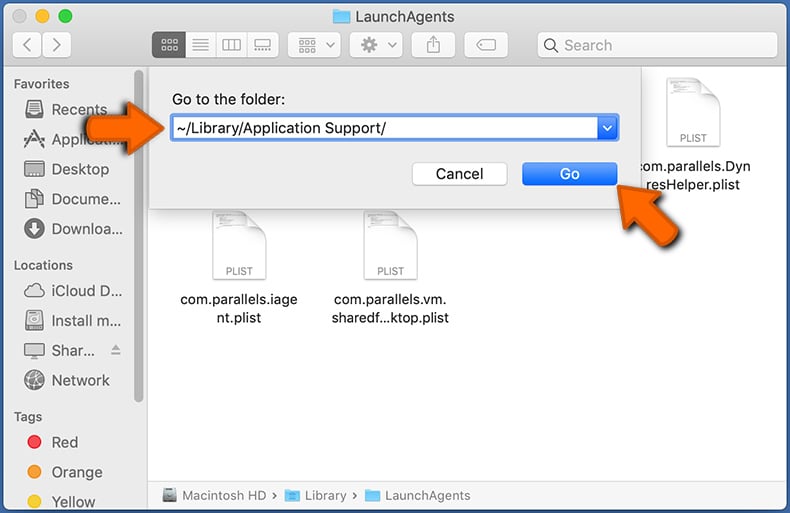
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
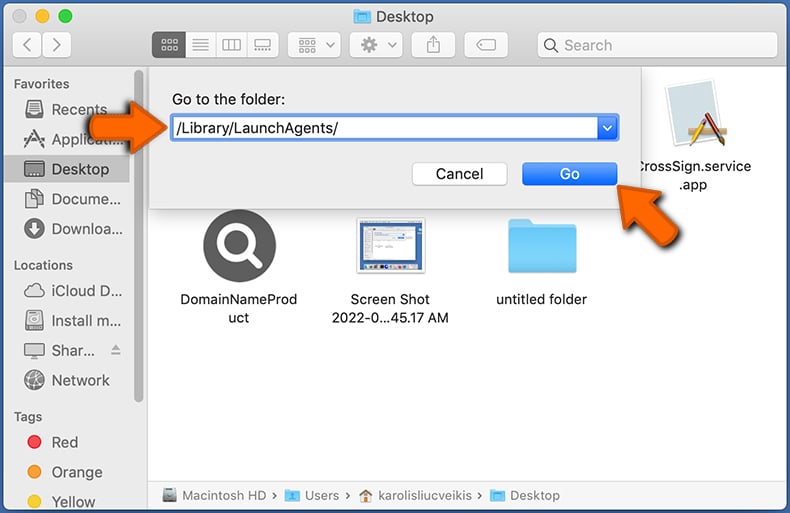
In the Go to Folder... bar, type: /Library/LaunchAgents/
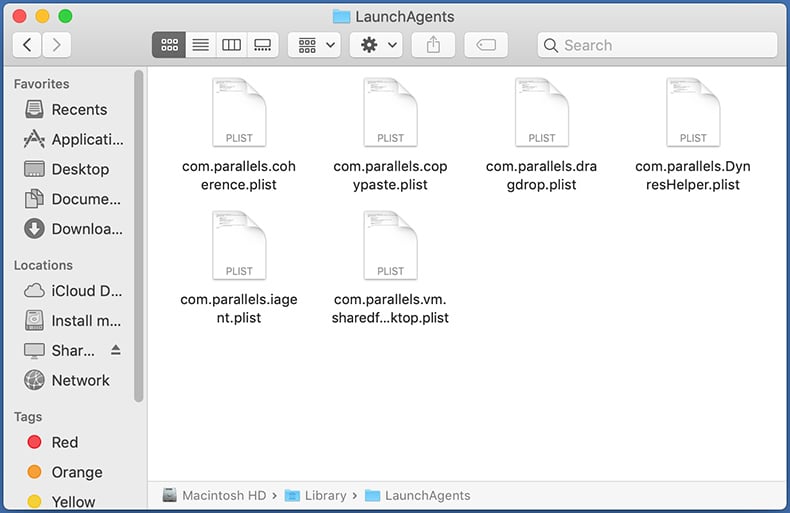
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
In the Go to Folder... bar, type: ~/Library/Application Support/
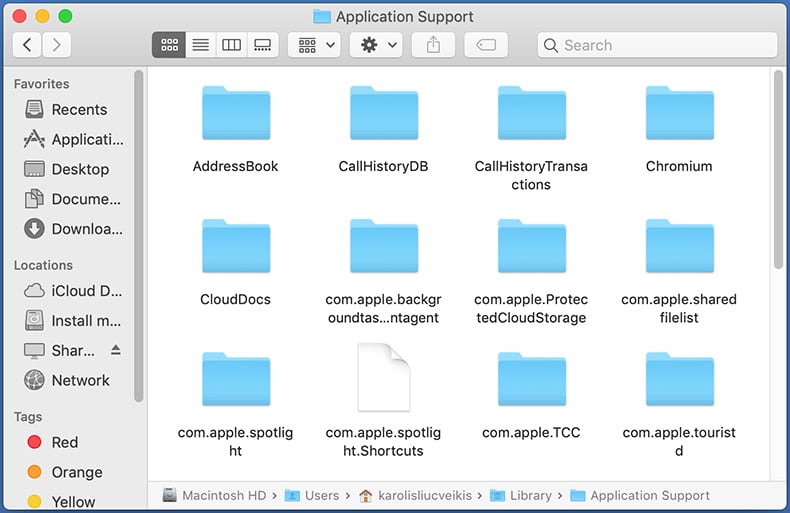
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
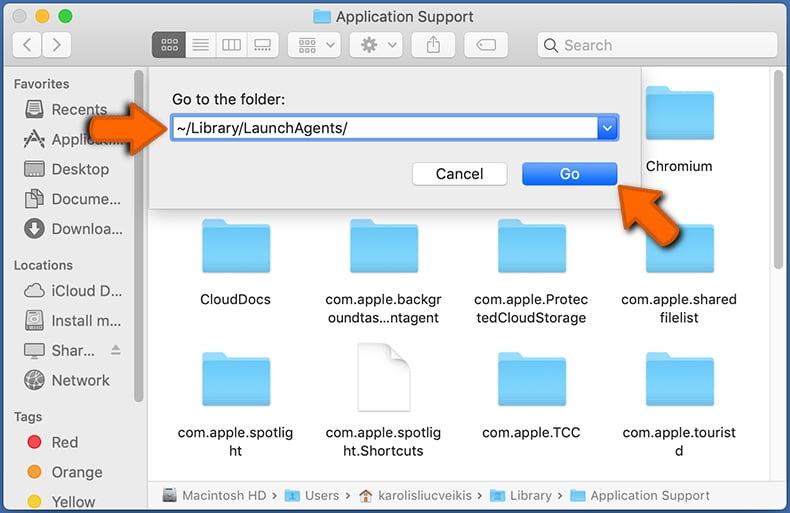
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
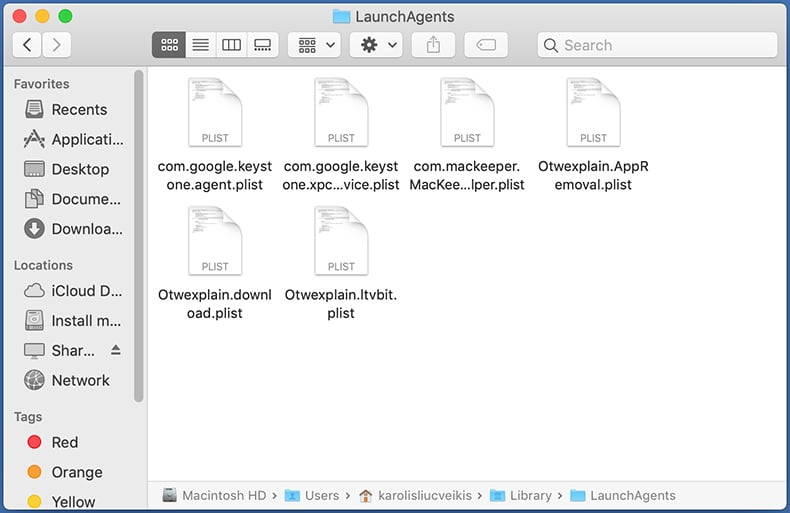
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
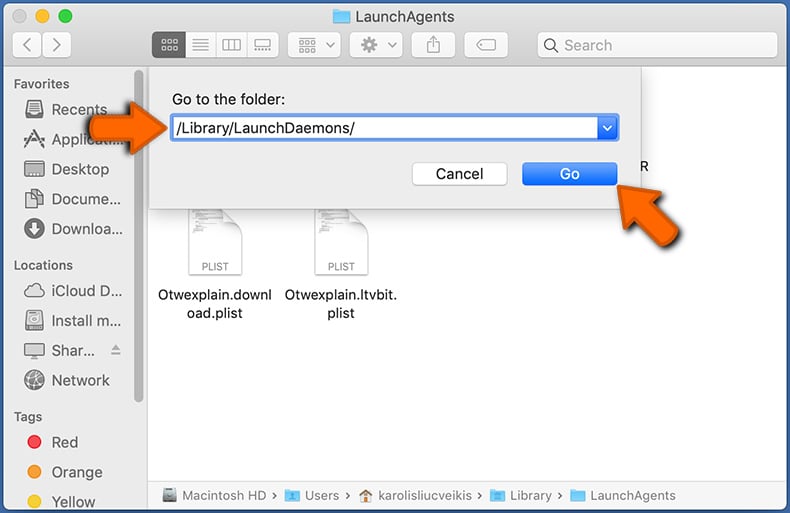
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
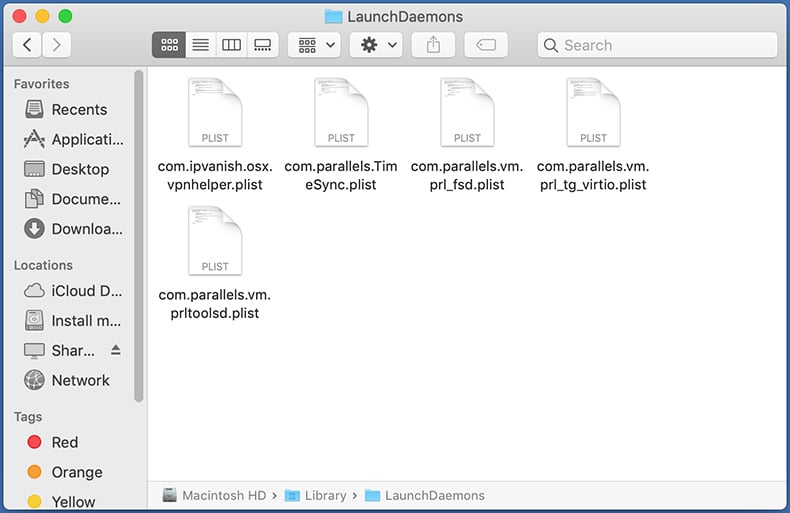
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
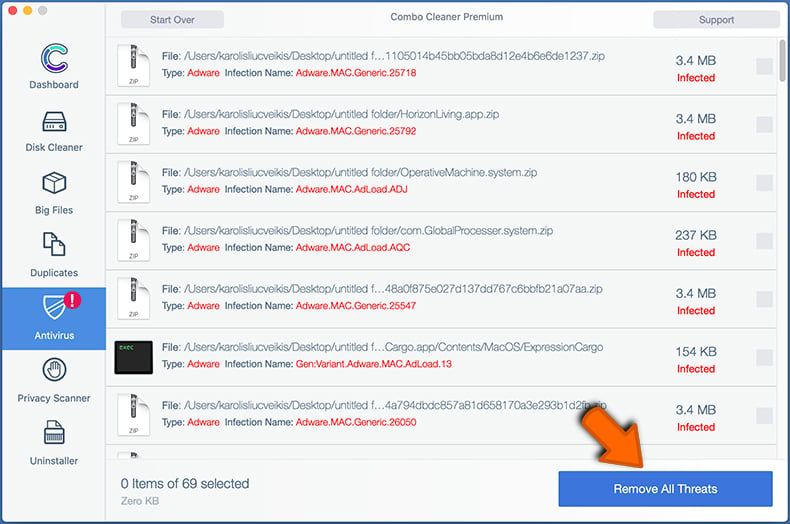
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
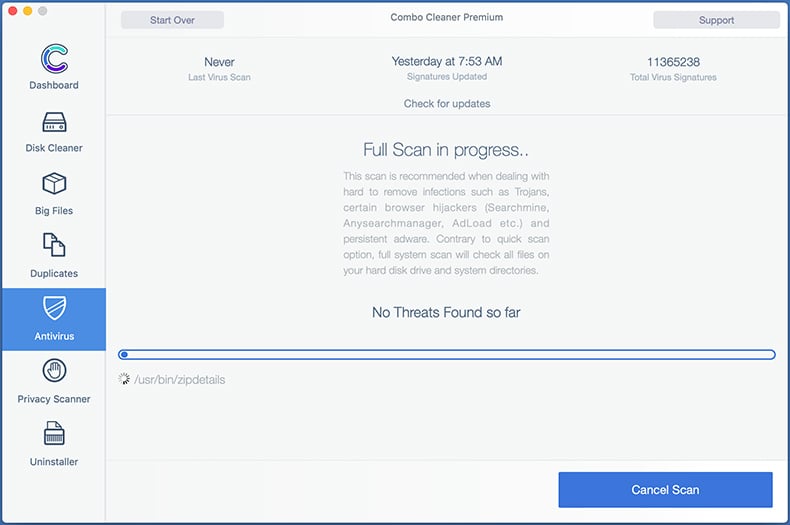
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
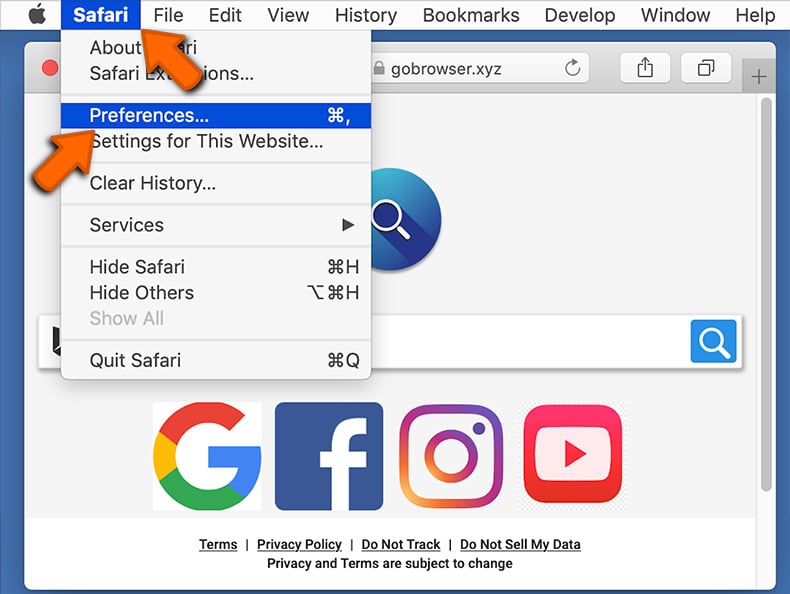
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
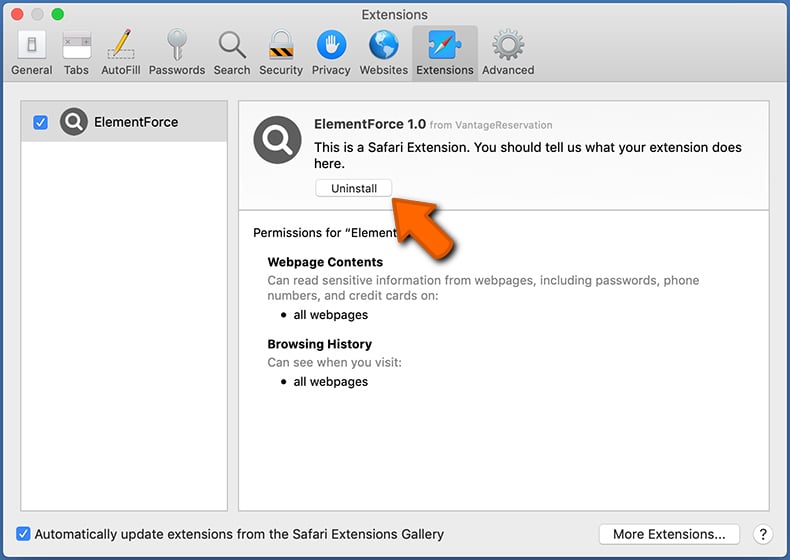
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
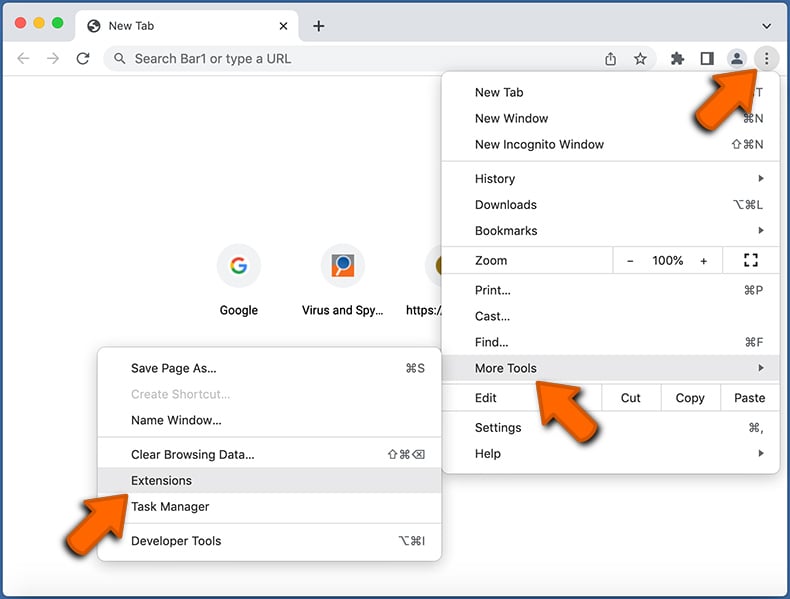
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
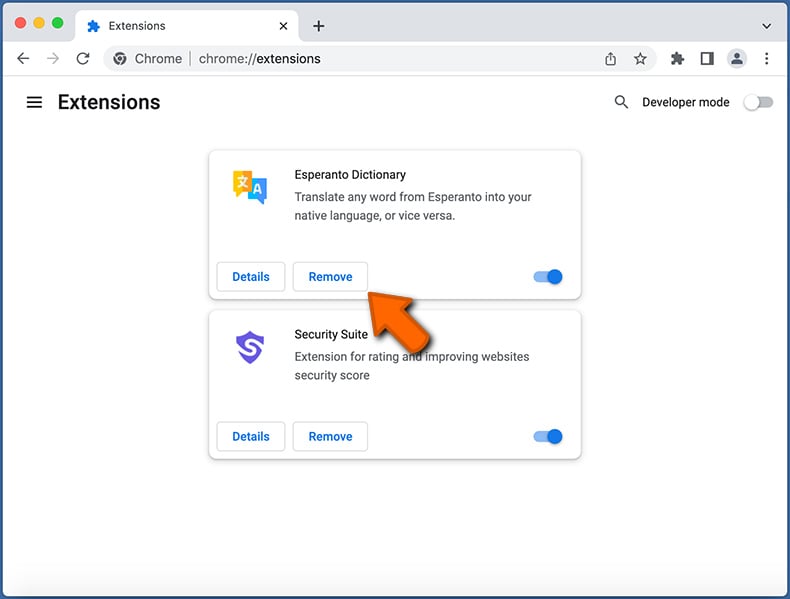
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
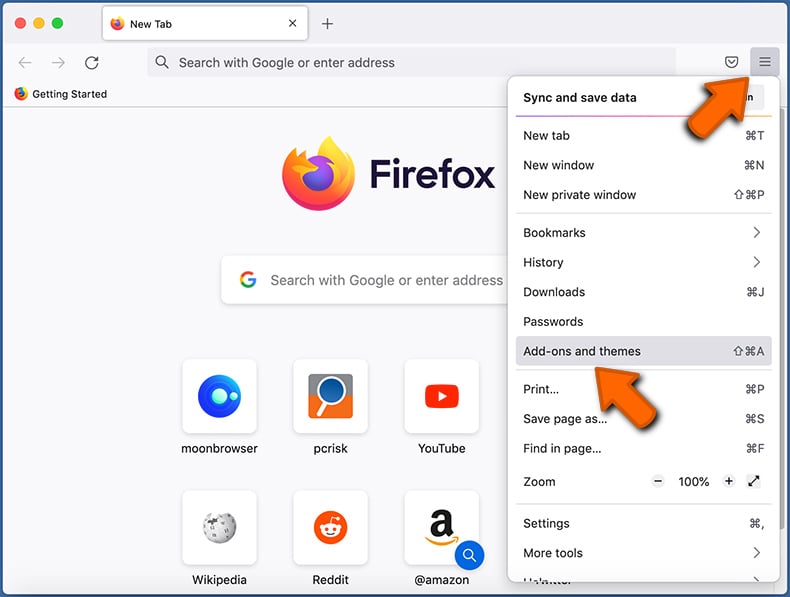
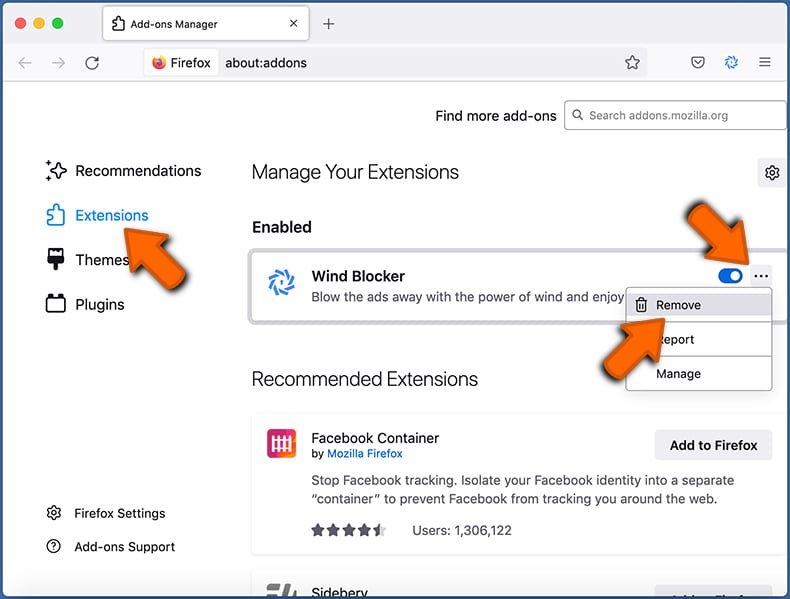
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Frequently Asked Questions (FAQ)
My computer is infected with KEYSTEAL malware, should I format my storage device to get rid of it?
No, KEYSTEAL's removal does not necessitate formatting.
What are the biggest issues that KEYSTEAL malware can cause?
The threats posed by an infection depend on the malicious program's functionalities and the cyber criminals' aims. KEYSTEAL targets macOS Keychain data (e.g., passwords, private keys, certificates, etc.) - hence, these infections may result in severe privacy issues, financial losses, and even identity theft.
What is the purpose of KEYSTEAL malware?
While malware operates differently, it is mainly used to generate revenue. However, cyber criminals might also use this software for their own amusement or to carry out personal vendettas, disrupt processes (e.g., websites, services, etc.), and even launch politically/geopolitically motivated attacks.
How did KEYSTEAL malware infiltrate my computer?
Malware is most commonly proliferated through drive-by downloads, spam emails and messages, online scams, untrustworthy download sources (e.g., freeware and free file-hosting websites, Peer-to-Peer sharing networks, etc.), illegal software activation tools ("cracks"), fake updates, and malvertising. Some malicious programs are even capable of self-spreading via local networks and removable storage devices (e.g., USB flash drives, external hard drives, etc.).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is designed to detect and remove threats. It is capable of eliminating practically all known malware infections. Keep in mind that sophisticated malicious software typically hides deep within systems - therefore, running a full system scan is paramount for its detection.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion