Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is RustBucket?
RustBucket is a type of macOS malware that has the ability to retrieve further payloads from a Command-and-Control (C&C) server. The malware has the capability to collect system data and whether it is operating in a virtual environment. RustBucket allows the attacker to carry out malicious actions on compromised devices.

More about RustBucket
RustBucket is a type of malware that enables an attacker to perform various actions on infected machines. Some of the possible actions that can be taken with RustBucket include stealing sensitive information, deleting or modifying files, installing additional malware, and taking remote control of the compromised system.
Once the malware infects a device, it can gather system information, such as the list of running processes, the current time, and whether it is running in a virtual machine. The attacker can use this information to determine how to proceed with the attack.
The malware may also enable the attacker to steal sensitive information from the infected device, such as login credentials, banking information, and personal data. This information can be used for identity theft, financial fraud, and other malicious purposes.
In addition to stealing information, RustBucket may be used to delete or modify files on the infected device. This can cause damage to the system, disrupt operations, and cause data loss. The malware may also be used to install additional malware on the device, such as ransomware, which can encrypt files and demand payment in exchange for the decryption key.
Overall, RustBucket is a dangerous malware that may cause significant harm to an infected device and its users.
| Name | RustBucket macOS malware |
| Threat Type | Mac malware, Mac virus |
| Detection Names (RustBucket) | Avast (Other:Malware-gen [Trj]), Combo Cleaner (Trojan.MAC.Generic.111990), ESET-NOD32 (OSX/NukeSped.R), Kaspersky (Trojan-Downloader.OSX.Lazarus.c), Full List Of Detections (VirusTotal) |
| Detection Names (Fake PDF) | TrendMicro (HEUR_PDFEXP.E), Full List Of Detections (VirusTotal) |
| Symptoms | Malicious programs are usually designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution Methods | Social engineering, trojanized application, fake PDF document |
| Damage | Monetary loss, identity theft, data loss, additional infections, and more |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Threat actors behind RustBucket
It is believed that RustBucket can be attributed to a state-sponsored threat actor from North Korea. The Advanced Persistent Threat (APT) group known as BlueNoroff, which is thought to operate as a sub-group of the notorious Lazarus Group, is believed to be responsible for the creation and distribution of RustBucket.
How did RustBucket install on my computer?
The distribution of RustBucket by cybercriminals is a multi-stage process that involves social engineering tactics to trick victims into initiating the infection chain. The malware is contained within an unsigned application called "Internal PDF Viewer.app", which is programmed to fetch and execute the second-stage payload on the system.
To execute the first-stage malware, the user must manually override Gatekeeper. Once the first stage is executed, the second stage, which is a signed application masquerading as a legitimate Apple bundle identifier, is launched. It displays a fake PDF to the victim, featuring information from a legitimate venture capital firm.
Following the launch of the second stage, the malware contacts the command-and-control (C&C) server to obtain the third-stage payload. The third-stage payload is a signed trojan written in Rust programming language and capable of running on ARM and x86 architectures.
The distribution method used by cybercriminals for RustBucket involves the use of various decoys to deceive victims into executing the malware.
How to avoid installation of malware
To avoid malware, keep your software and operating system up to date with the latest security patches. Avoid clicking on suspicious links or downloading files from unknown sources (including attachments in suspicious emails), and use reputable antivirus software to scan your system regularly.
Additionally, avoid clicking advertisements and pop-ups on dubious websites. Download software solely from official pages and verified stores. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate all threats.
Unsigned application ("Internal PDF Viewer.app") used to distribute RustBucket:

Fake PDF document used to distribute RustBucket:

Update July 3, 2023 – new version of RustBucket malware has been discovered. The variant sports sophisticated anti-detection and persistence-ensuring capabilities. Recent research strongly suggests that RustBucket is used by the Lazarus Group, a North Korean state-sponsored threat actor. This malware has been used in a cryptocurrency-targeting attack against a company headquartered in the European Union, which provides crypto-payment services. More information on these developments can be found in an article on the Elastic Security Labs website.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "RustBucket"?
- STEP 1. Remove RustBucket related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
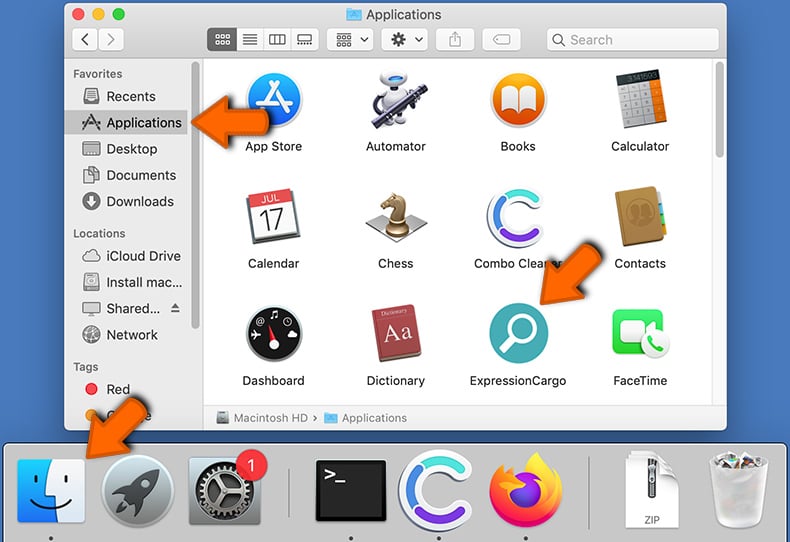
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
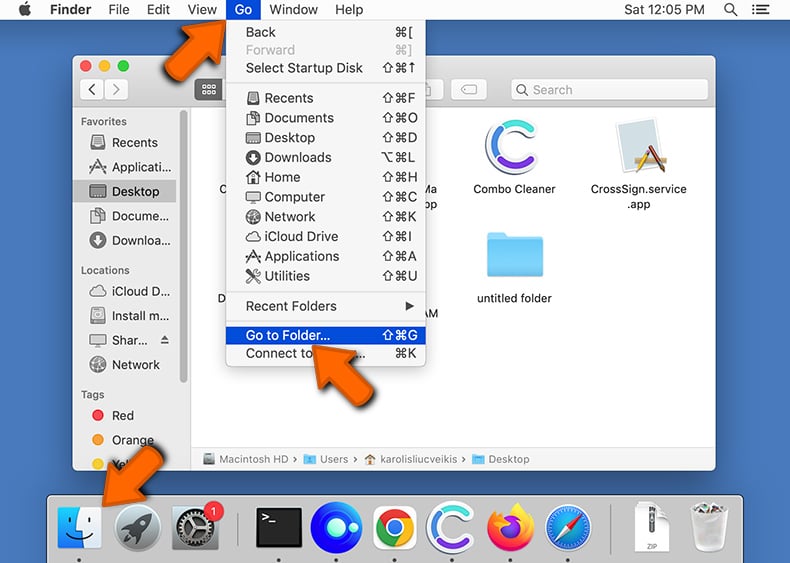
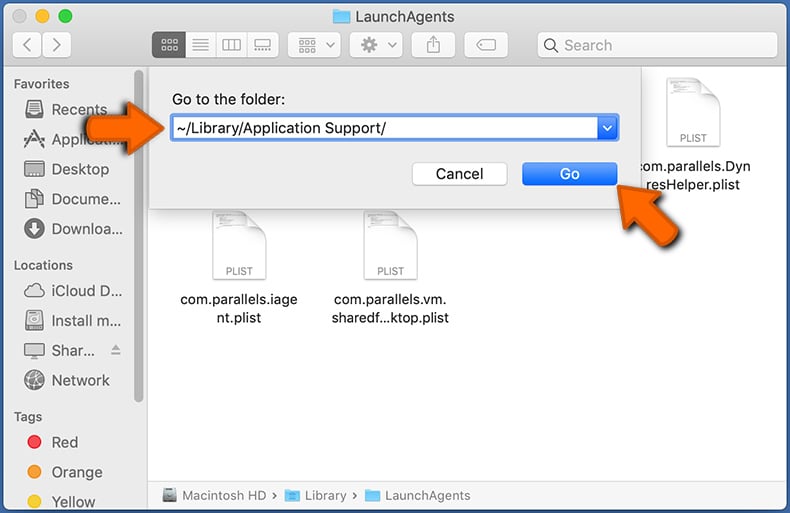
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
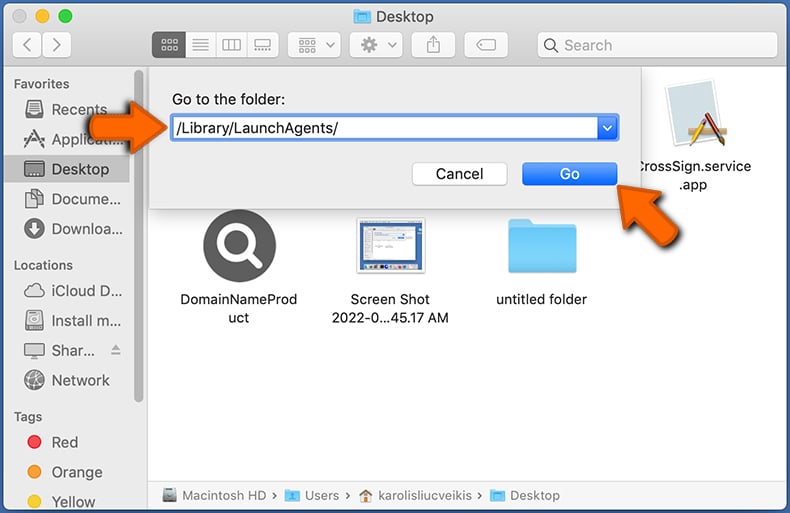
In the Go to Folder... bar, type: /Library/LaunchAgents/
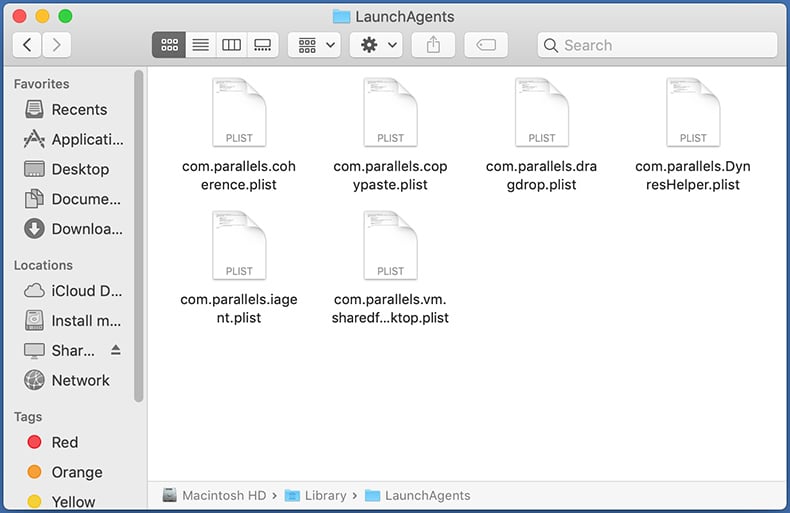
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
In the Go to Folder... bar, type: ~/Library/Application Support/
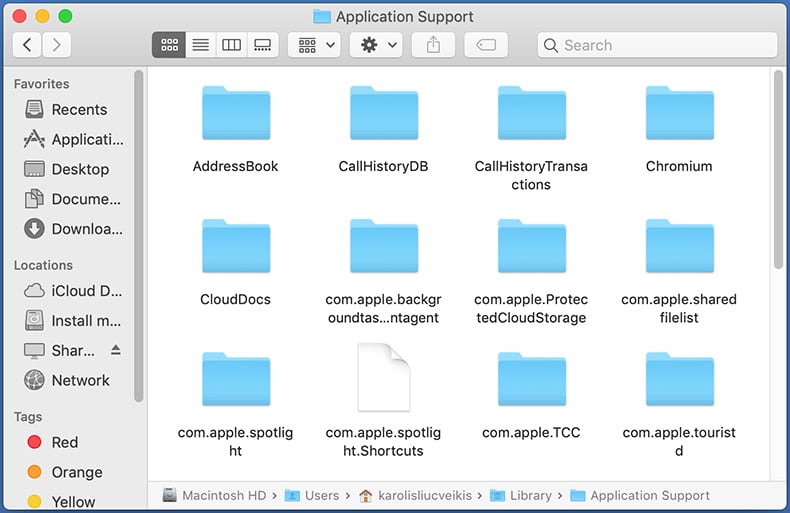
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
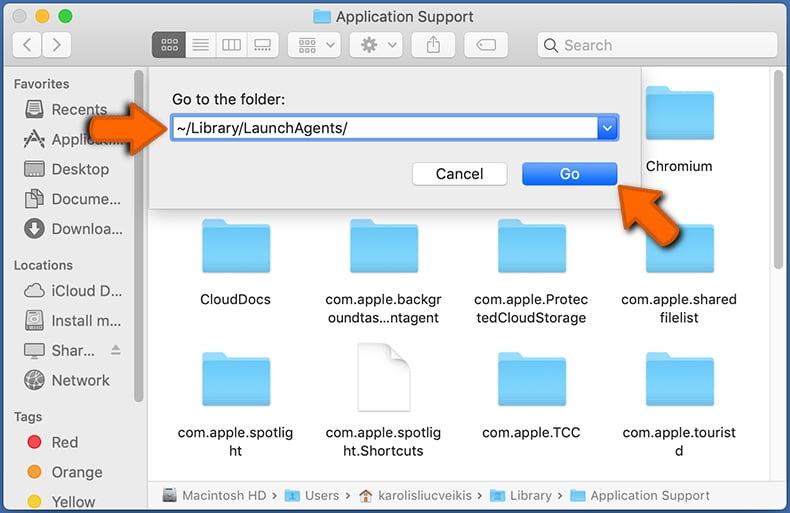
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
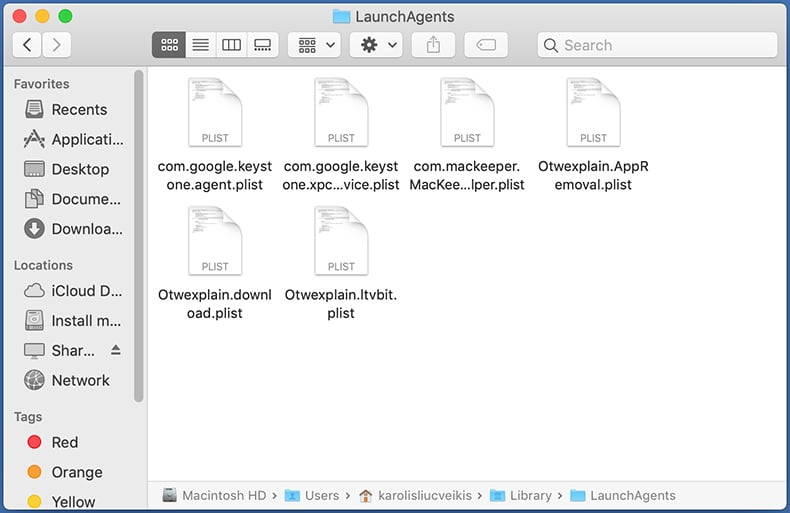
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
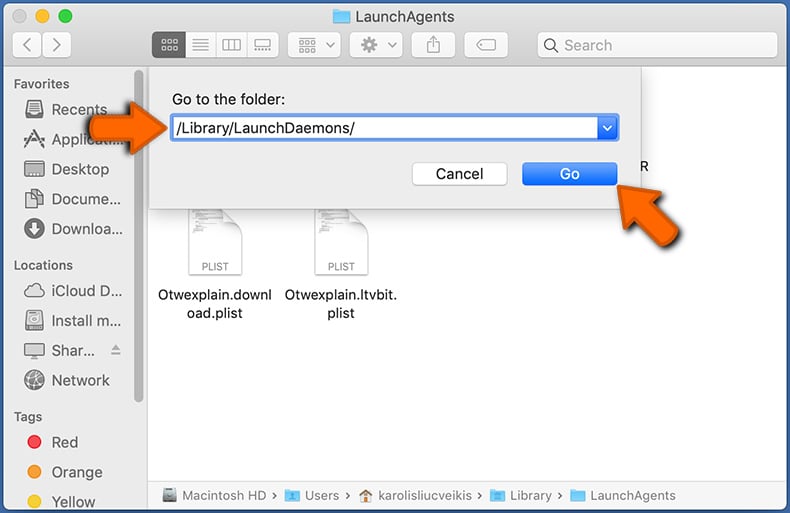
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
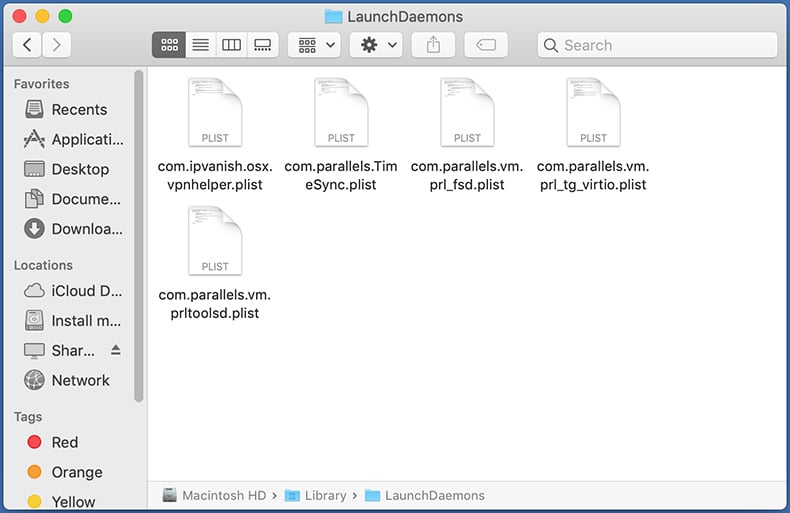
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
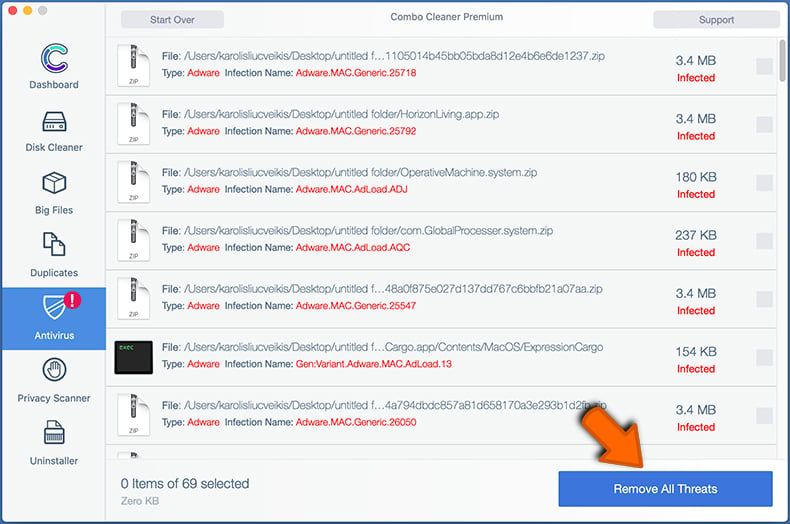
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
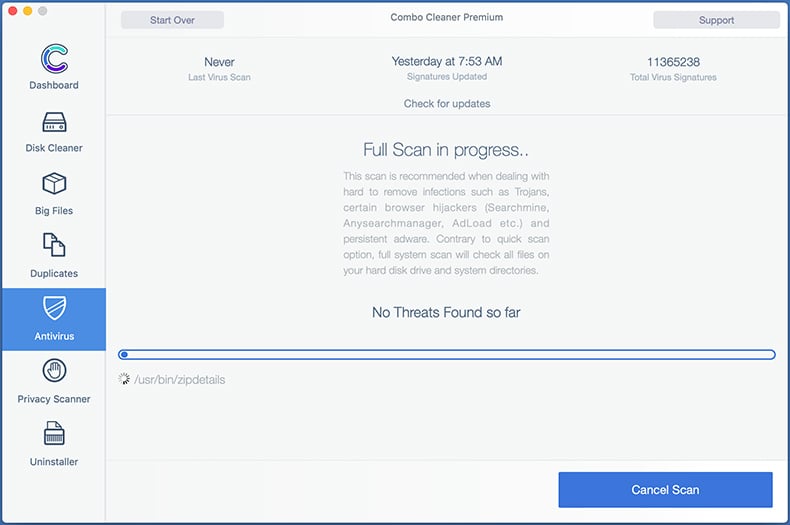
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
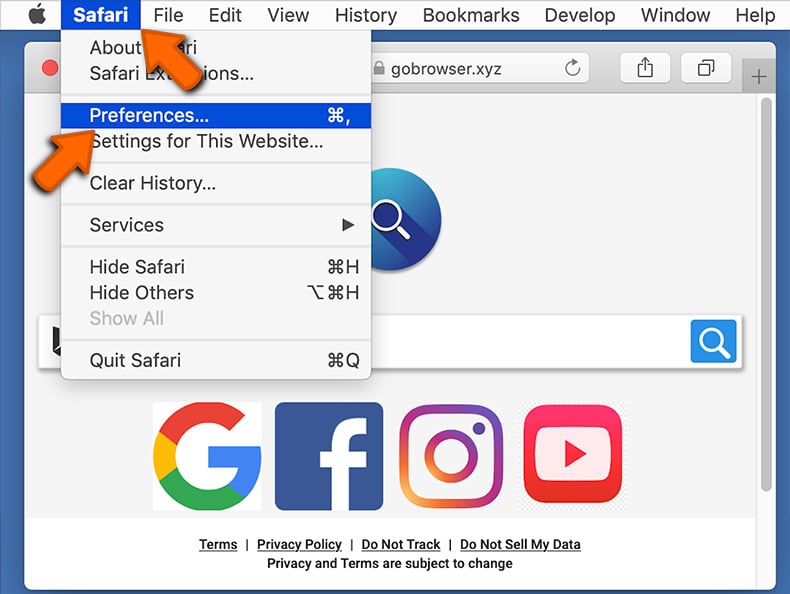
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
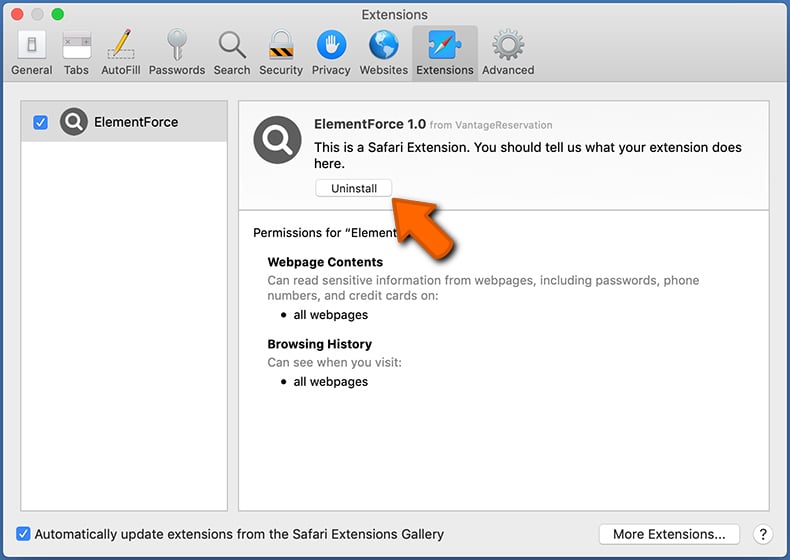
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
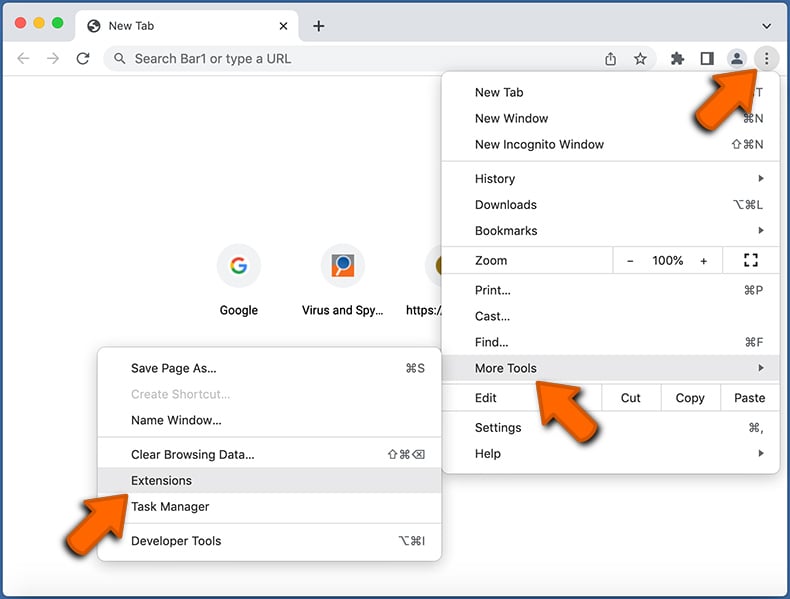
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
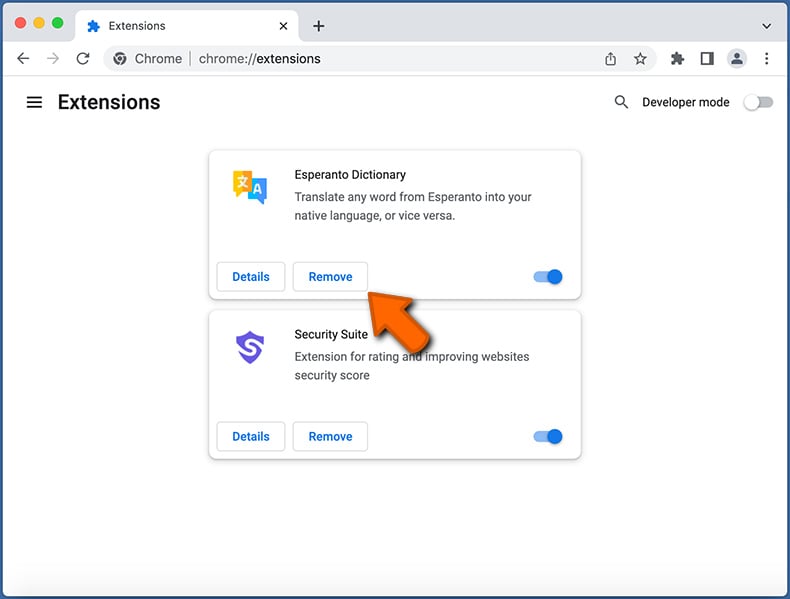
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
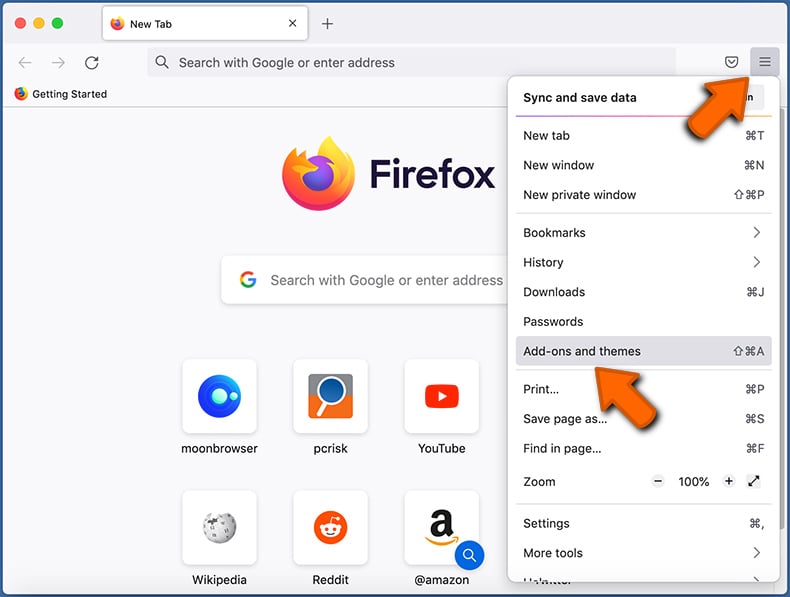
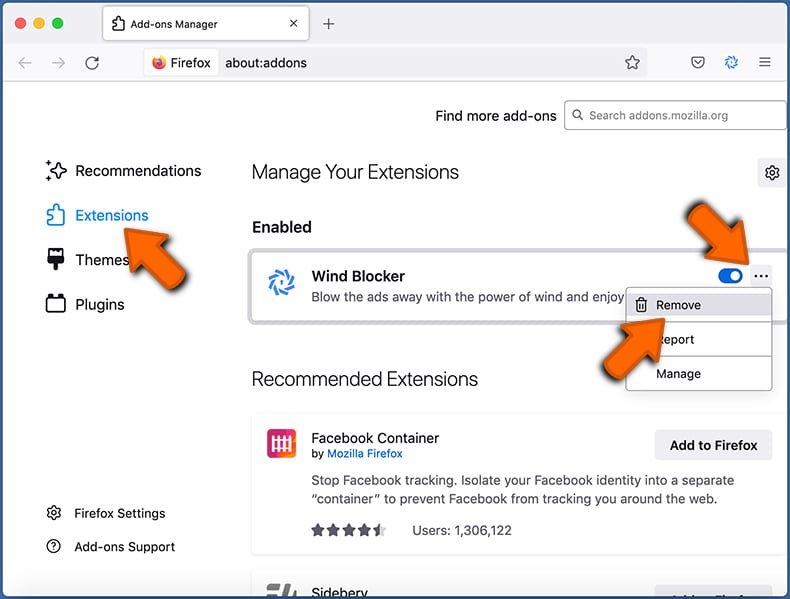
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Frequently Asked Questions (FAQ)
My computer is infected with RustBucket malware, should I format my storage device to get rid of it?
If your computer is infected with RustBucket malware, formatting may be an effective solution for removing the malware. However, it is recommended to try using antivirus software for the removal first.
What are the biggest issues that malware can cause?
The negative effects of malware can vary depending on its type. Some types of malware can lead to serious issues such as identity theft, financial losses, and decreased computer performance. Additionally, malware can sometimes lead to further infections.
What is the purpose of RustBucket malware?
The purpose of RustBucket malware is to gain unauthorized access to a victim's computer system and allow the attacker to carry out various actions on the infected machines. This includes collecting various information and downloading additional malware payloads from the Command-and-Control server.
How did RustBucket malware infiltrate my computer?
RustBucket malware infiltrates computers through a multi-stage process that involves social engineering tactics to trick victims into initiating the infection chain. It is contained within an unsigned application called "Internal PDF Viewer.app" and requires a manual override of Gatekeeper to execute. The malware communicates with a C2 server to obtain a third-stage payload, a Trojan written in Rust programming language.
Will Combo Cleaner protect me from malware?
Combo Cleaner has the ability to detect and eliminate nearly all known malware infections, although it is important to note that sophisticated malware may be deeply hidden within the system. Therefore, it is crucial to perform a complete system scan to ensure effective detection and removal.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion