Myweathercenter.co Redirect
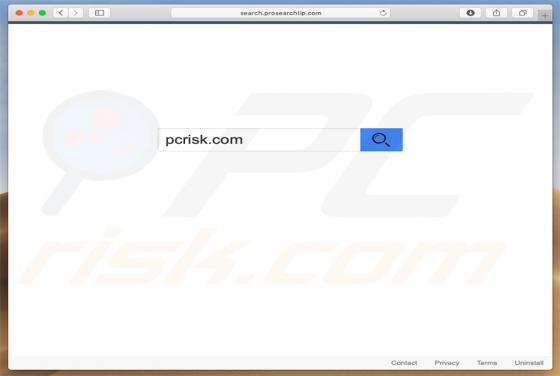
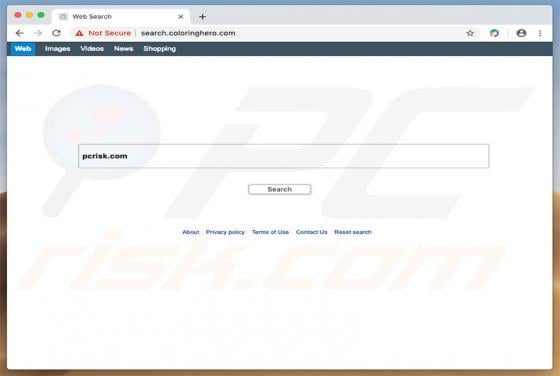
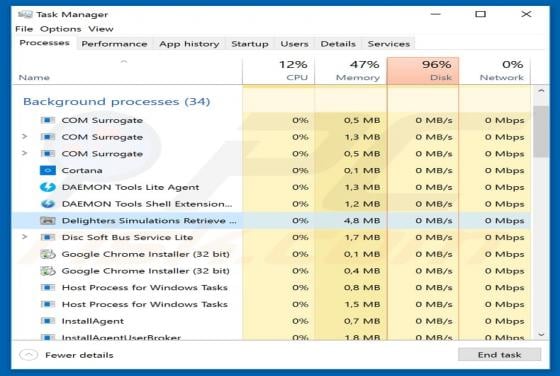
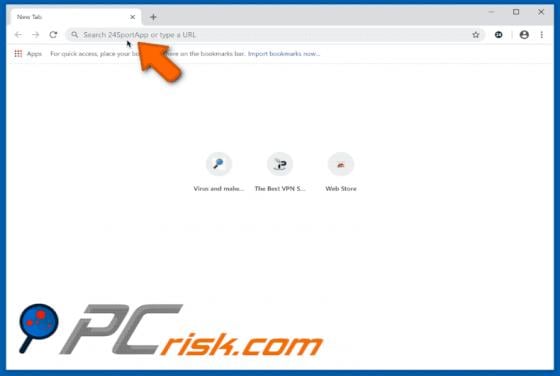
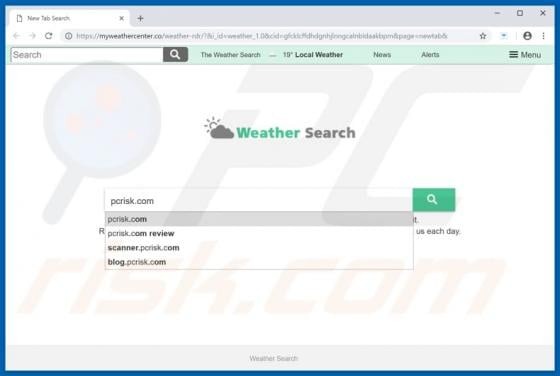
myweathercenter.co (also known as feed.hmyweathercenter.co) is a fake search engine that is presented as legitimate. Developers promote the site as useful, offering various features, enhancing the browsing experience, and so on. Unfortunately, it is promoted using two browser hijackers: My Weather