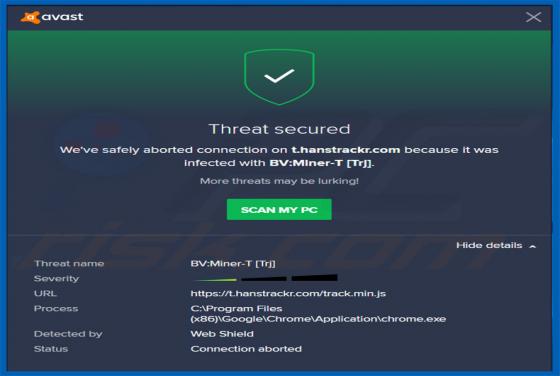
Hanstrack.com Browser Hijacker
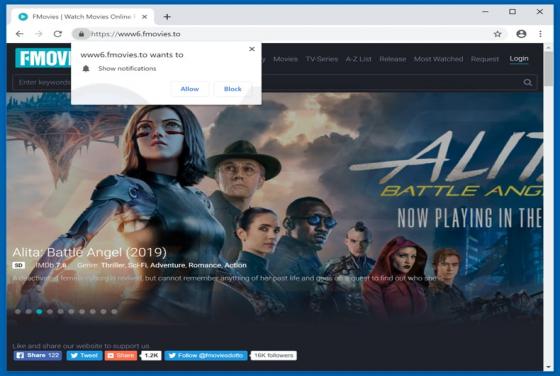
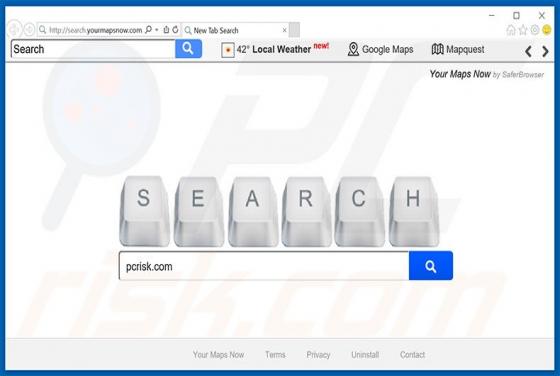
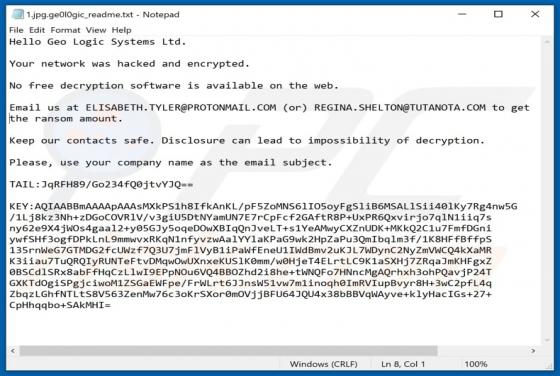
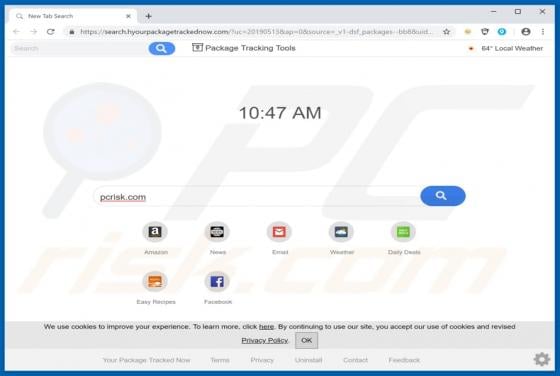
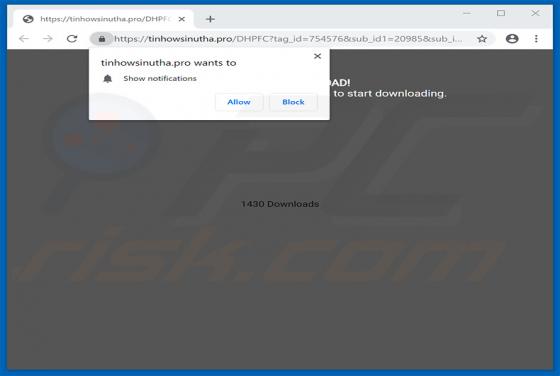
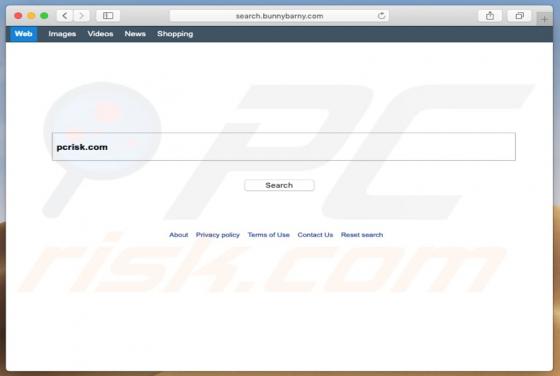
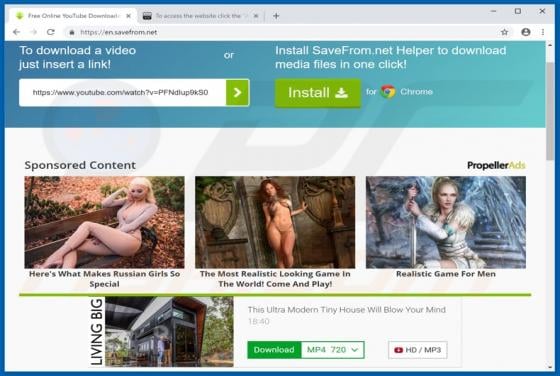
hanstrackr[.]com is a rogue website promoted via various rogue plug-ins. In fact, criminals also promote this site by hijacking legitimate plug-ins and injecting them with malicious code. Therefore, developers continually encounter redirects to hanstrackr[.]com whenever a malicious/compromised pl