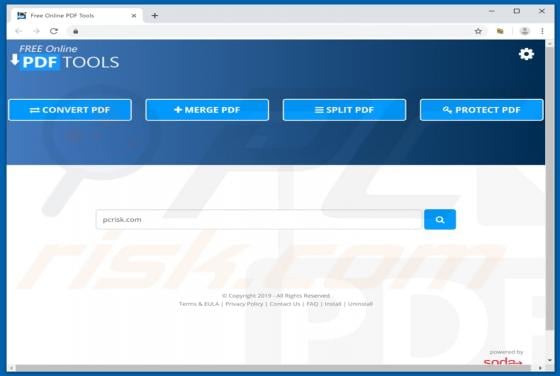
Freeonlinepdftools.com Redirect
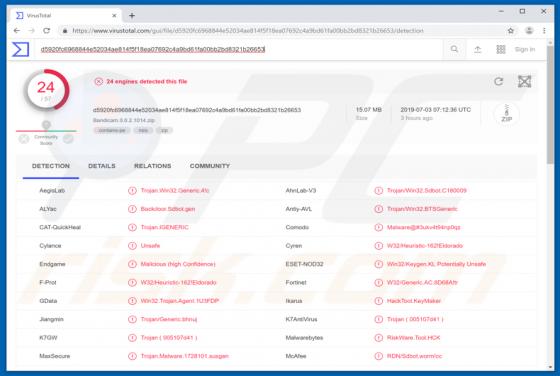
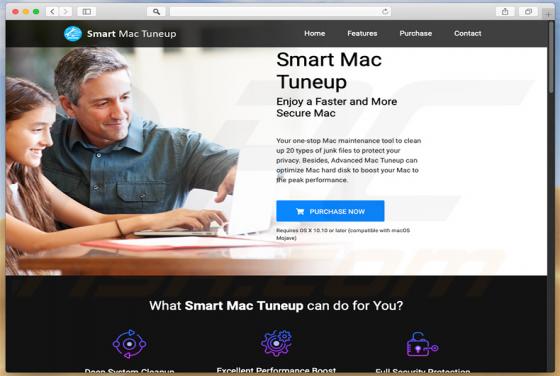
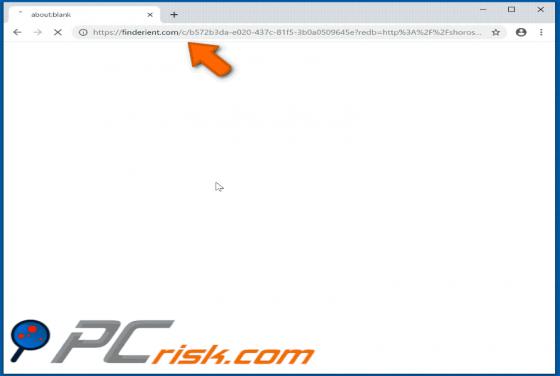
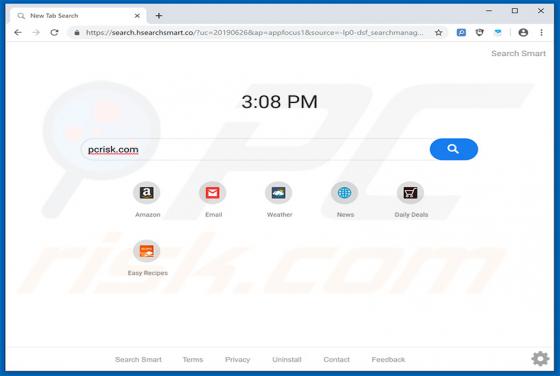
freeonlinepdftools.com is the address of a fake search engine. Typically, search engines of this type are advertised as tools that provide an enhanced browsing experience and various extra features. Typically, fake search engines are promoted via potentially unwanted apps (PUAs), browser hijackers