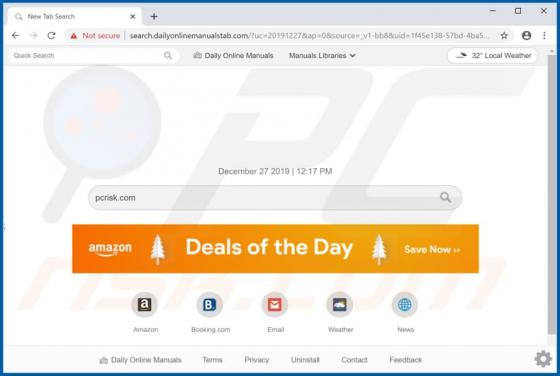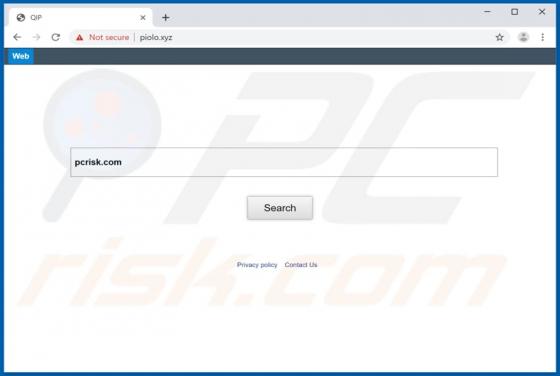
Piolo.xyz Redirect
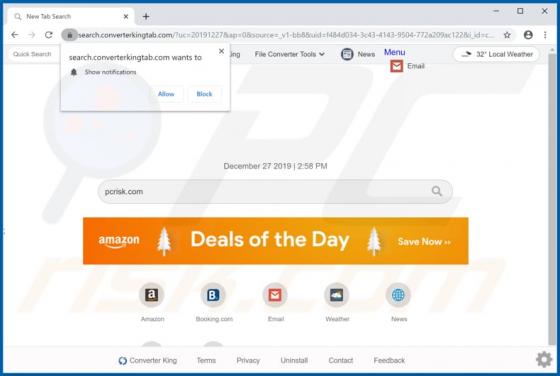
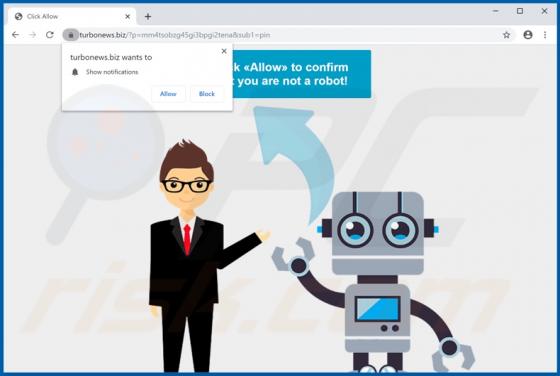
piolo.xyz is the address of a fake search engine that is promoted through potentially unwanted applications (PUAs): browser hijackers called CERX and Dorss APP. It is also very likely that there are other apps of this type that promote this fake search engine. CERX is related to QIP (another brow