How to remove VShell malware from the Mac operating system (macOS)
Mac VirusAlso Known As: VShell virus
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is VShell?
VShell is a piece of malicious software with backdoor, RAT (Remote Access Trojan), and injector abilities. This program can cause chain infections and execute commands on infected machines. VShell is highly compatible, as it can infiltrate payloads for Mac (macOS), Windows, and Linux operating systems. This malware has been used in campaigns carried out by a Chinese state-sponsored threat actor tracked as "UNC5174".
VShell malware overview
VShell is a fileless malware that operates exclusively in-memory, which eliminates the possibility of file-based detection by security software. The malicious program disguises itself as a system process and is executed via "fexecve" syscall (system call).
VShell functions as a backdoor – it can open a "backdoor" into targeted systems and cause further infections. This program has base RAT (Remote Access Trojan) capabilities, i.e., it can establish remote access/control over systems and execute arbitrary commands.
VShell manipulates system operations and maps the memory (through syscalls). It prevents the sizable memory mappings (ranging from 64-512 MB) from being accessed/changed and allocates them for subsequent payloads. This malware can infect the system by downloading and executing virulent files or by acting as an injector (i.e., injecting shellcode and malicious binaries).
VShell can introduce payloads intended for macOS, Windows, or Linux. In theory, programs of this kind can cause just about any infection (e.g., trojan, ransomware, cryptocurrency miner, etc.), but in practice – they typically operate within certain specifications or limitations. Additionally, this malware can steal victim's files.
The latest campaign involving VShell was one undertaken by the UNC5174 threat actor. To expand upon this infection chain, in its initial stage, a malicious bash script introduced two payloads: "dnsloger" and "system_worker". The former is associated with the SNOWLIGHT malware, while the latter – with the Sliver and Cobalt Strike malware. In this stage, actions were undertaken to ensure persistence, implant Silver malware, and for SNOWLIGHT to download VShell and execute it in-memory.
It must be mentioned that oftentimes malware developers and attackers improve upon their software and methodologies. The UNC5174 group is known to customize the tools they use in their campaigns. Therefore, possible future iterations of VShell could have additional/different abilities and features.
To summarize, software like VShell can cause multiple system infections that may lead to severe privacy issues, financial losses, and identity theft.
| Name | VShell virus |
| Threat Type | Mac malware, Mac virus, Remote Access Trojan (RAT), backdoor, injector. |
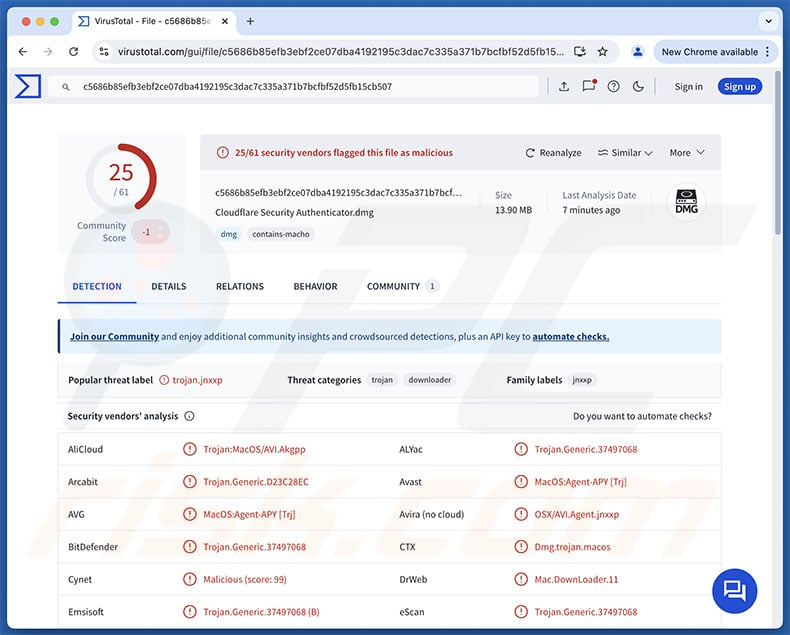
| Detection Names | Avast (MacOS:Agent-APY [Trj]), Combo Cleaner (Trojan.Generic.37497068), ESET-NOD32 (OSX/Agent.EC), Kaspersky (UDS:Trojan-Downloader.OSX.Agent.gen), Full List Of Detections (VirusTotal) |
| Symptoms | Malware is designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution Methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Fileless malware examples
We have written about countless malicious programs; SeroXen, DarkWatchman, XCSSET, and AZORult are merely a few of our articles on malware capable of operating in-memory.
Malicious software can be highly versatile or be designed for an incredibly specific purpose. However, it does not matter how malware functions – its presence on a system threatens device and user safety. Hence, all threats must be removed immediately upon detection.
How did VShell install on my computer?
While VShell developers have made it unavailable for legal reasons, it can still be found on the Web. The malware's license expiration should prevent its use, but there is information online on how to bypass this. There are GitHub repositories hosting this program, and it is available as a downloadable ZIP archive on Chinese third-party file-sharing sites. Therefore, this malware can be used by various cyber criminals, who prefer different distribution techniques.
As previously mentioned, VShell was used in attacks carried out by a threat actor referred to as UNC5174. However, the methods that were utilized in this campaign are currently unknown. Evidence suggests that UNC5174 is a contractor for the Chinese government.
This group has targeted entities operating in the governmental, energy, defense, medical, research, and technical sectors – based in Canada, the United States, the United Kingdom, and the Asian-Pacific region. Some older tactics used by UNC5174 include phishing campaigns in 2019 and exploiting the Ivanti Cloud Service Appliance (CSA) products in 2024 (during the Summer Olympics).
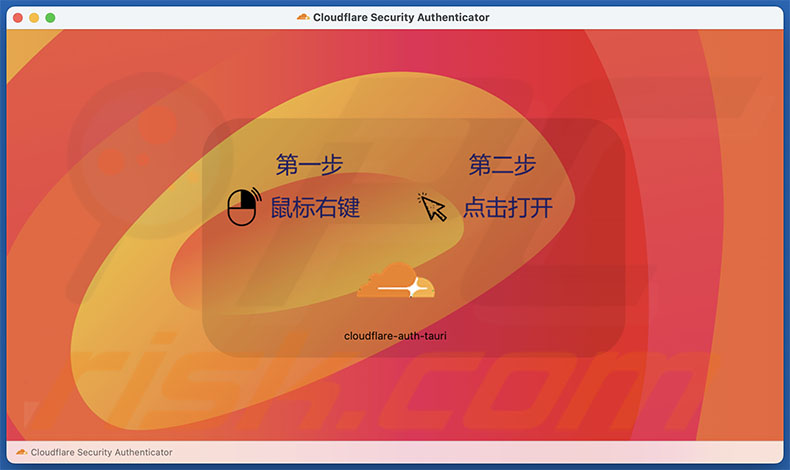
Phishing and social engineering are standard in malware distribution. Malicious programs are typically presented as or bundled with ordinary software/media files. VShell has been disguised as Cloudflare Security Authenticator.
Virulent files can be archives (ZIP, RAR, etc.), executables (.exe, .run, etc.), documents (Microsoft Office, Microsoft OneNote, PDF, etc.), JavaScript, and so on. Merely opening an infectious file can be enough to trigger malware download/installation processes.
Malicious software is primarily distributed via virulent attachments/links in spam mail (e.g., emails, PMs/DMs, etc.), trojans (backdoors/loaders/droppers/injectors), drive-by (stealthy/deceptive) downloads, untrustworthy download sources (e.g., freeware and third-party websites, P2P sharing networks, etc.), online scams, illegal software activation tools ("cracks"), and fake updates.
What is more, some malware is capable of self-proliferating through local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
How to avoid installation of malware?
We recommend downloading only from official and verified channels. Another recommendation is to activate and update software using functions/tools provided by legitimate developers, as illegal product activation ("cracking") tools and third-party updates can contain malware.
Additionally, it is essential to be vigilant while browsing since fraudulent and malicious online content usually appears genuine and harmless. Incoming emails and other messages must be approached with care. Attachments or links found in dubious mail must not be opened, as they can be infectious.
It is paramount for device integrity and user safety to have a reputable antivirus installed and kept updated. Security programs must be used to perform regular system scans and to remove threats/issues. If your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate the infiltrated malware.
VShell malware disguised as "Cloudflare Security Authenticator":
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "VShell"?
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
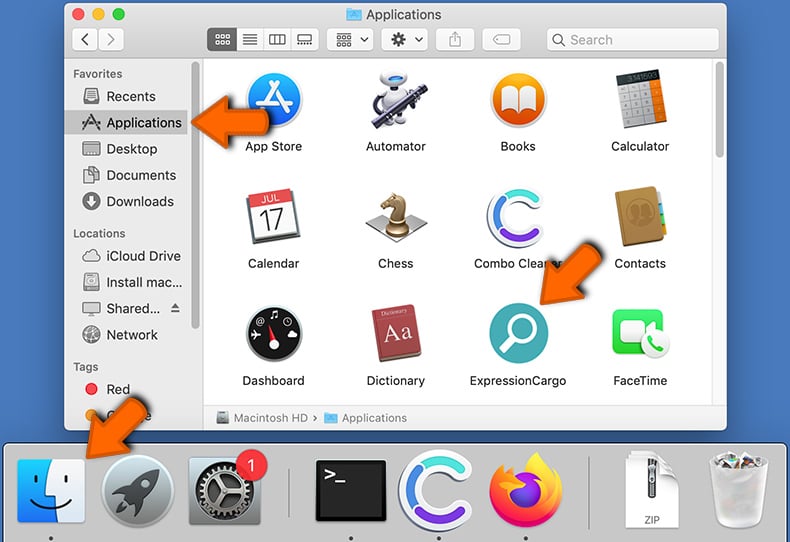
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
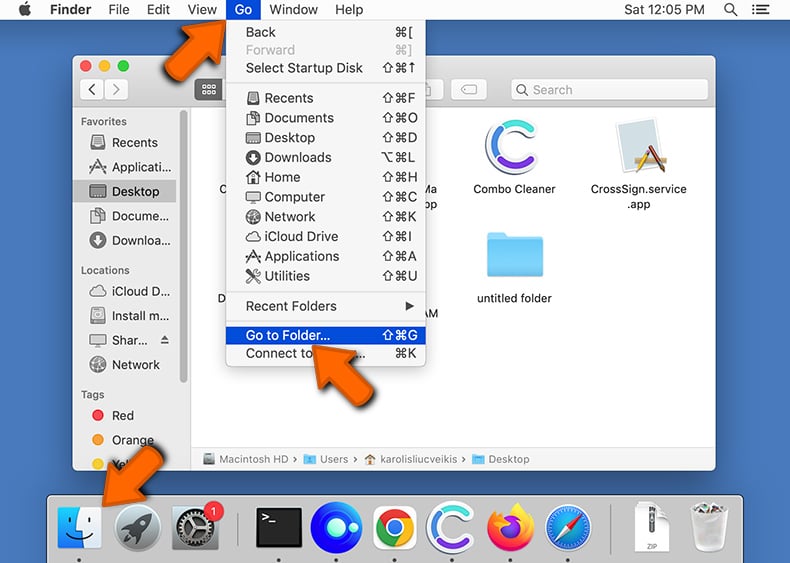
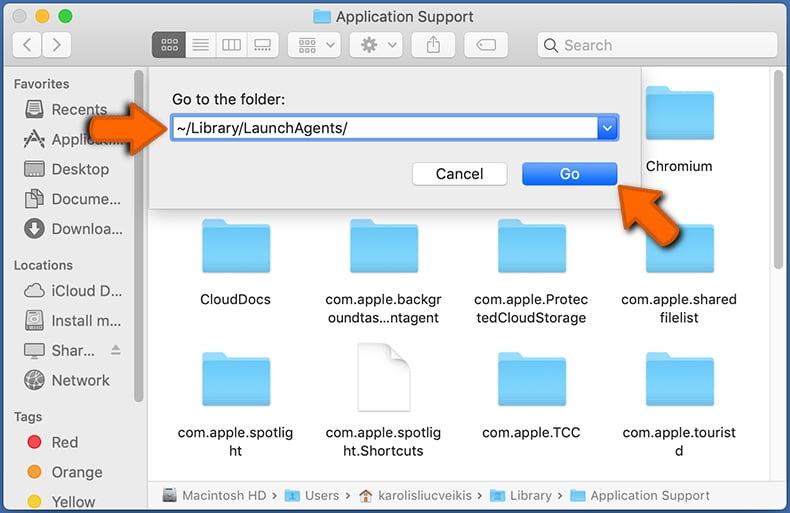
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
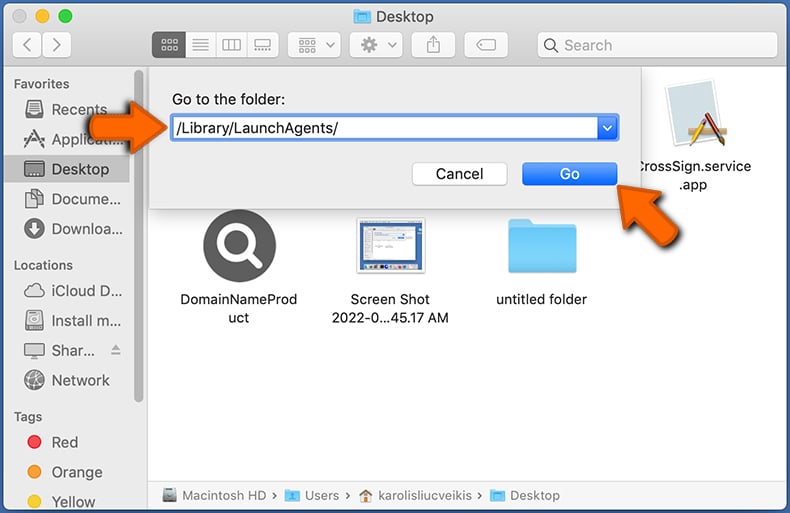
In the Go to Folder... bar, type: /Library/LaunchAgents/
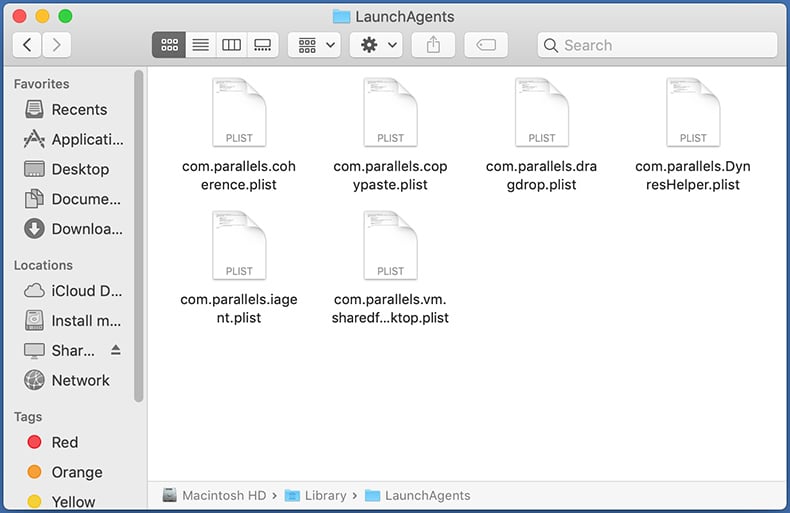
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
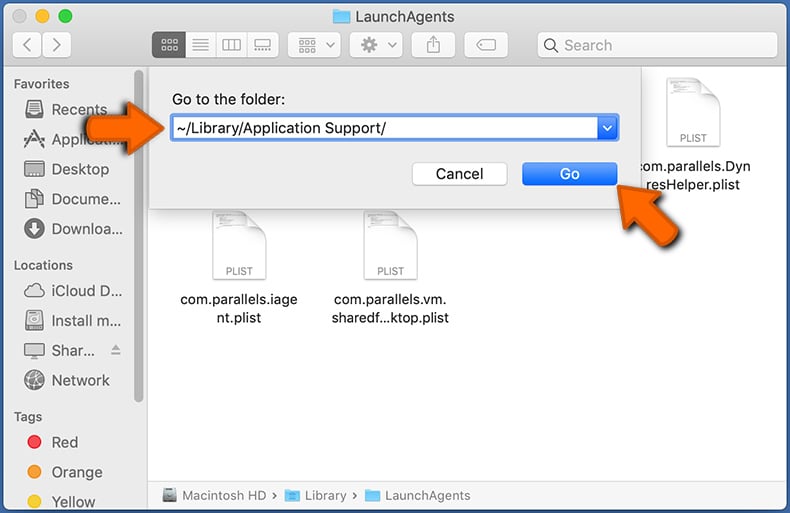
In the Go to Folder... bar, type: ~/Library/Application Support/
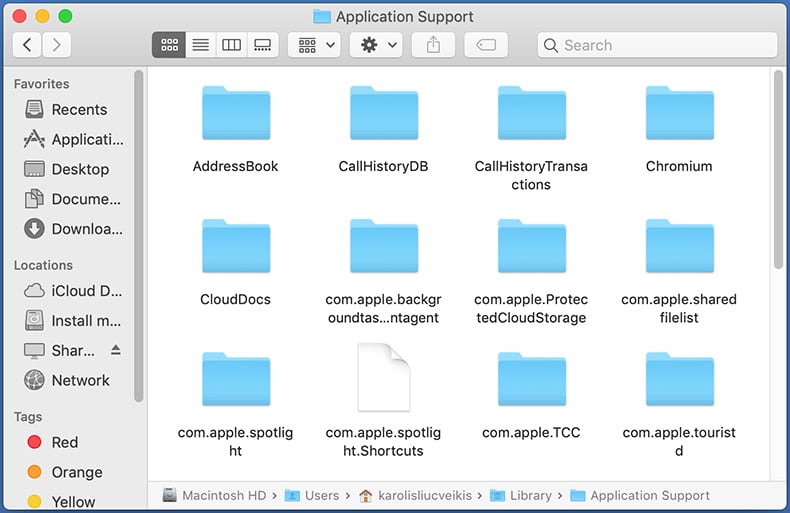
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
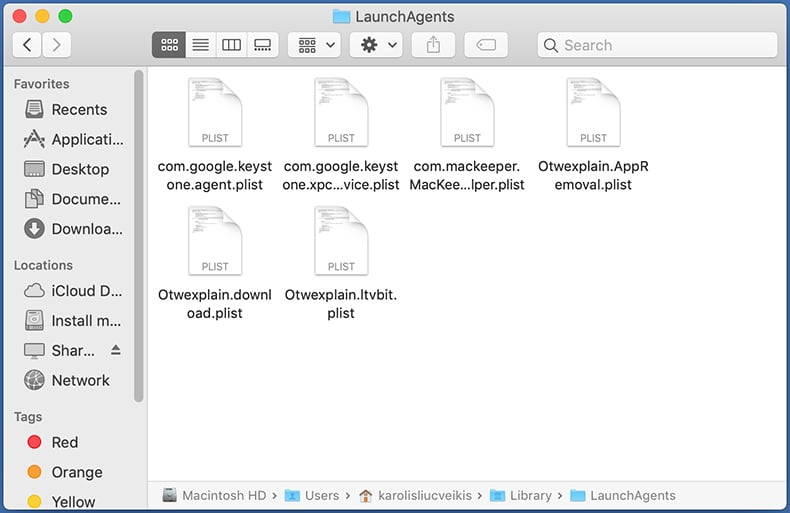
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
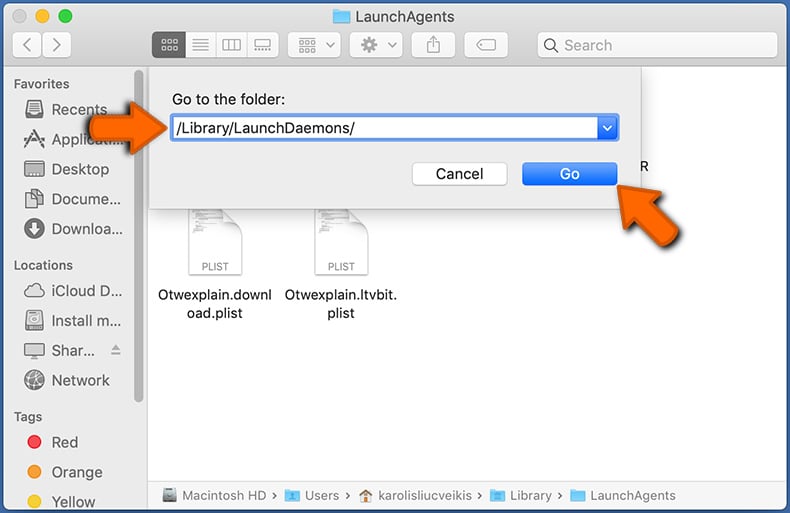
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
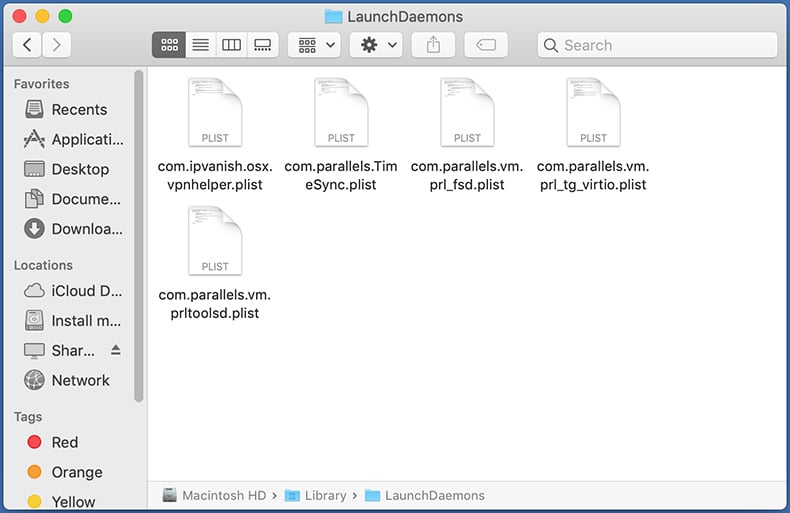
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
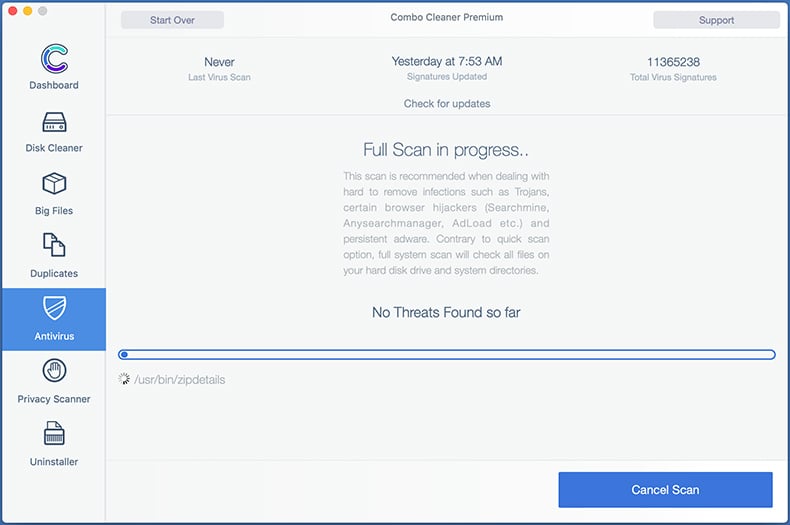
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
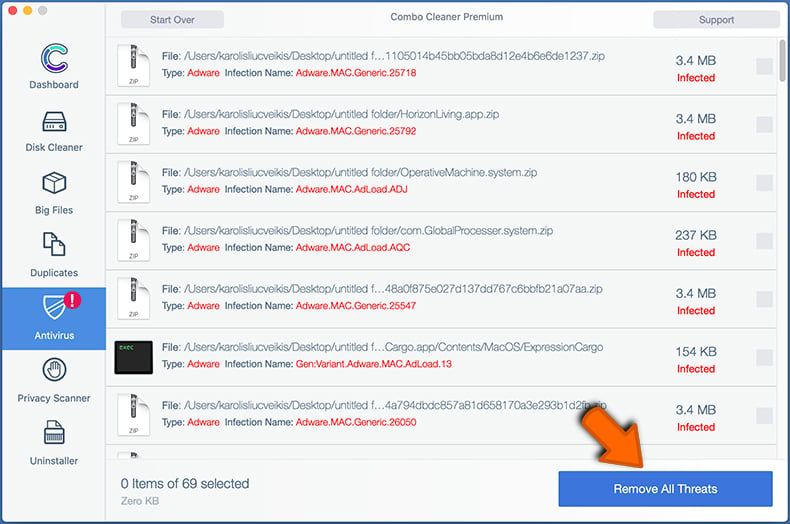
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
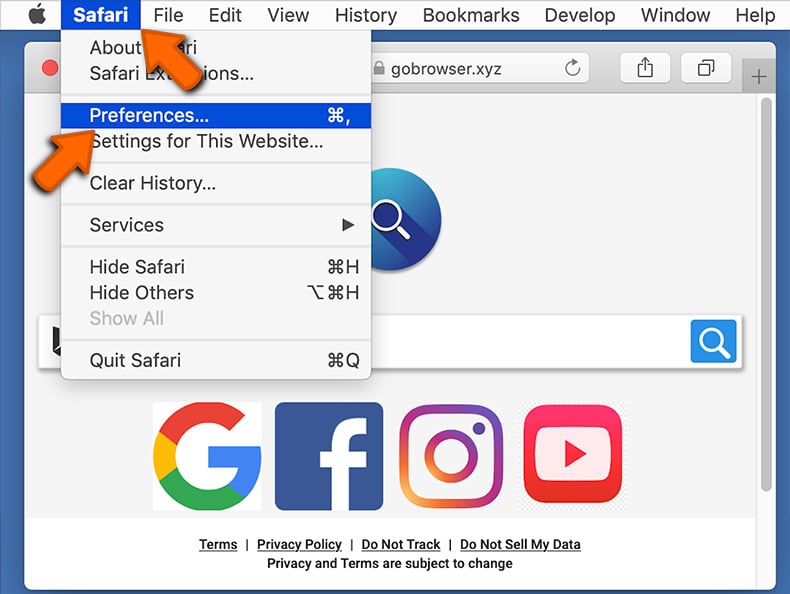
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
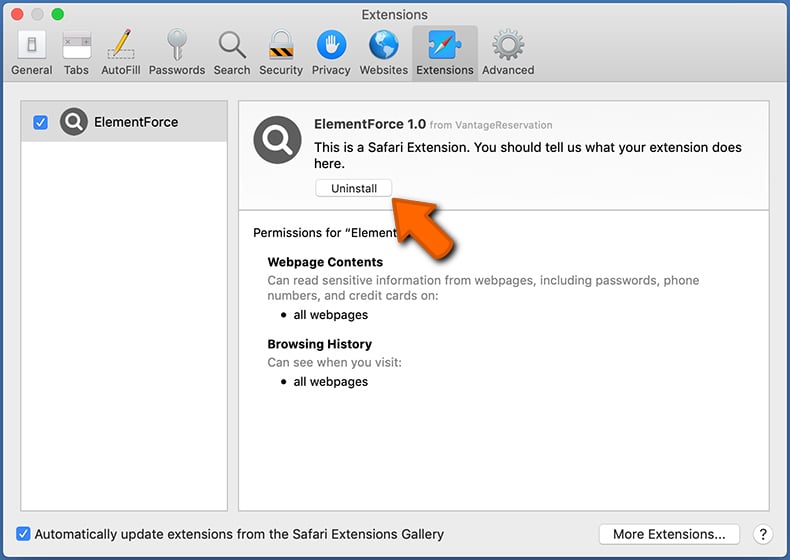
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
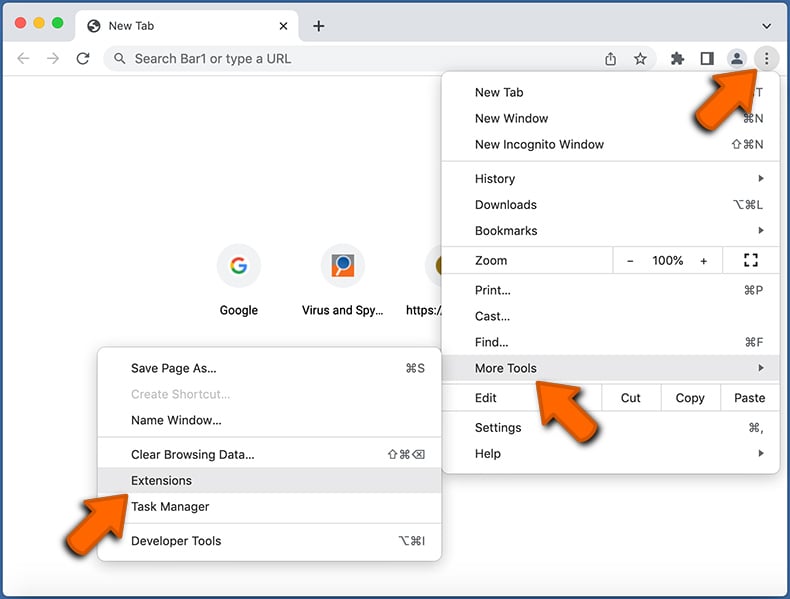
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
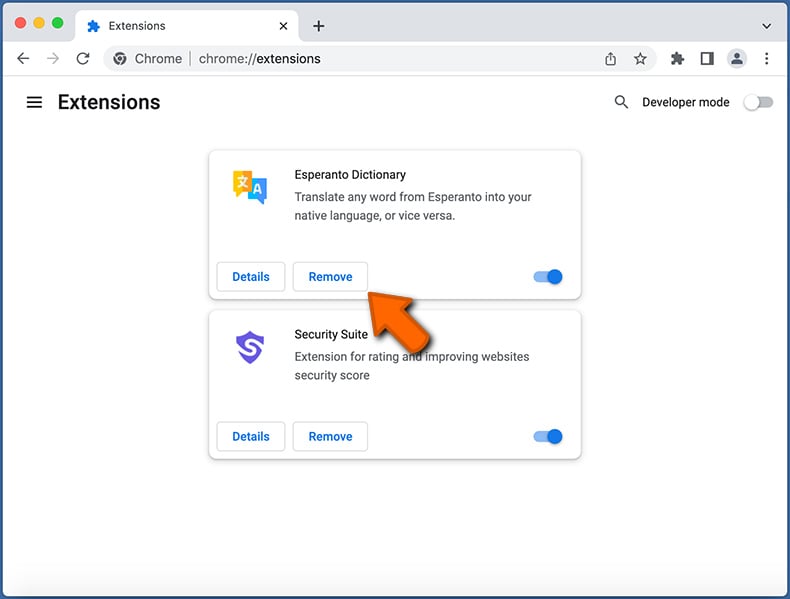
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
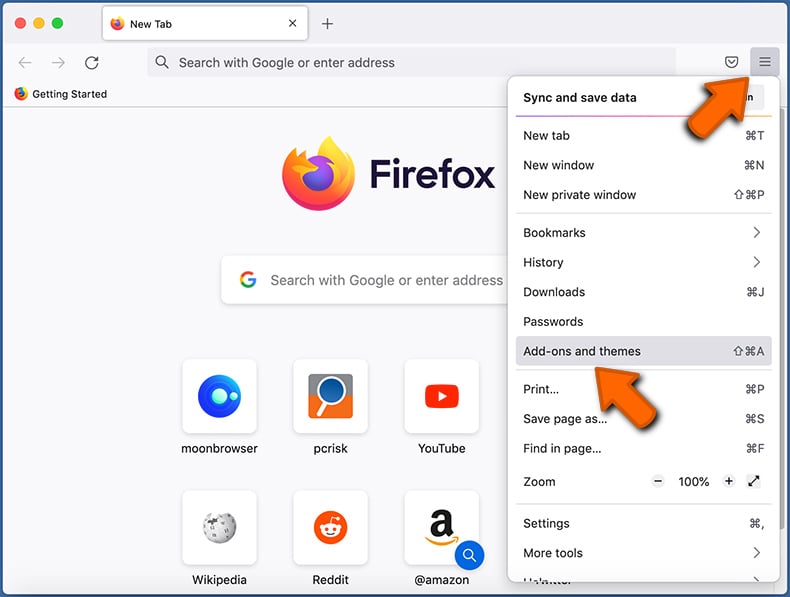
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
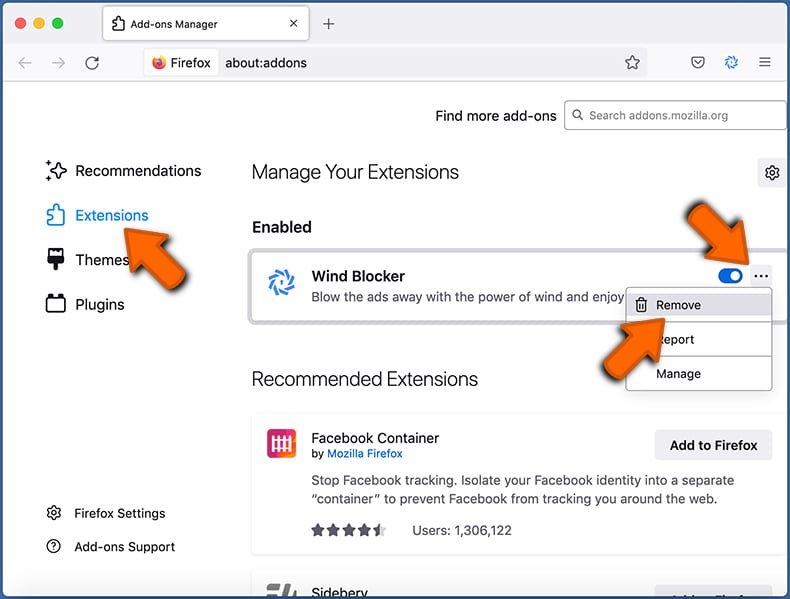
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Frequently Asked Questions (FAQ)
My computer is infected with VShell malware, should I format my storage device to get rid of it?
Malware removal rarely requires formatting.
What are the biggest issues that VShell malware can cause?
The dangers posed by an infection depend on the malicious program's functionalities and the attackers' modus operandi. VShell can cause chain infections and steal victims' files. As such, the presence of this malware on devices can result in multiple system infections, severe privacy issues, financial losses, and identity theft.
What is the purpose of VShell malware?
Profit is the most common motivation behind malware attacks. However, cyber criminals can also use malicious software to amuse themselves, realize personal vendettas, disrupt processes (e.g., websites, services, companies, organizations, etc.), engage in hacktivism, and launch politically/geopolitically motivated attacks. VShell has been used by UNC5174 – a threat actor backed by the Chinese government; hence, these attacks are likely to have had geopolitical reasons.
How did VShell malware infiltrate my computer?
The most widespread malware proliferation methods include: trojans, drive-by downloads, spam mail, online scams, suspect download channels (e.g., unofficial and free file-hosting sites, Peer-to-Peer sharing networks, etc.), illegal software activation ("cracking") tools, and fake updates. Furthermore, some malicious programs can self-spread via local networks and removable storage devices.
Will Combo Cleaner protect me from malware?
Combo Cleaner is designed to scan computers and eliminate all kinds of threats. It can detect and remove most of the known malware infections. Remember that performing a full system scan is crucial since sophisticated malicious software usually hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion