Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is XCSSET?
XCSSET is malicious software designed to steal various information and capable of operating as ransomware.
Some of the main functionality of this malware includes modification of displayed websites, stealing of log-in credentials (i.e. usernames and passwords) and other data relating to browsing activity, collection of information from certain messaging platforms, data encryption for the purpose of making ransom demands for decryption, and so on.
XCSSET is a high-risk malicious program, and its infections pose a significant threat to device and user safety. This malware has been observed being distributed inadvertently by various developers - sharing their Xcode projects, which have been stealthily compromised and injected with malicious code.

XCSSET overview
XCSSET malware can exfiltrate files from the infected system. It can also steal information of interest from Notes and Evernote (note-taking organizing and archiving applications). QQ, Skype, Telegram and WeChat messaging apps are similarly targeted by this malicious program. XCSSET can take screenshots of the current screen and visited websites.
As mentioned, this malware can also operate as ransomware. I.e., it can encrypt files and display ransom-demand messages, which promise data recovery if a certain sum is paid. Browsers are not exempt from XCSSET's list of targets. The potential abuse over the development version of the Safari browser is particularly varied (theoretically, limitless).
To elaborate, the malicious program can: alter the displayed web pages; extract browser cookies; prevent users from changing their passwords and, if that fails, record the newly-set passwords; steal credentials of amoCRM, Apple ID, Google, Paypal, SIPMarket and Yandex accounts; obtain credit card details (specifically, from the Apple Store); interfere with cryptocurrency transactions by switching addresses of cryptowallets, and so on.
To summarize, XCSSET infections can cause data and financial loss, lead to serious privacy issues and identity theft. If it is suspected or known that XCSSET (or other malware) has already infected the system, use anti-virus software to eliminate it immediately.
| Name | XCSSET virus |
| Threat Type | Phishing, Scam, Mac malware, Mac virus. |
| Detection Names | Avast (Other:Malware-gen [Trj]), BitDefender (Trojan.MAC.XCSSET.D), ESET-NOD32 (OSX/Spy.Xcsset.A), Kaspersky (HEUR:Trojan.OSX.Xtesc.gen), Full List (VirusTotal) |
| Symptoms | Your Mac becomes slower than normal, you see unwanted pop-up ads, you are redirected to dubious websites. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake Flash Player installers, torrent file downloads. |
| Damage | Internet browser tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites, loss of private information. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Examples of other malware targeting macOS
Gmera, Tarmac, NUKESPED and AppleJeus are some examples of other Mac-specific malware. These malicious programs have a wide variety of purposes and capabilities. All malware is classified as a threat to device and user safety, and thus necessitate immediate removal.
How did XCSSET infect my computer?
At the time of research, distribution of XCSSET malware was dependent on its victims, and specifically affected users who develop software.
The malicious code would insert itself into Xcode projects (Xcode being a software development file, resource and information repository) and when the projects shared (e.g. uploaded to GitHub), the malware was distributed to other systems. XCSSET is also spread using other techniques.
In general, malware is proliferated via Trojans, spam campaigns, illegal activation tools ("cracks"), fake updaters and untrusted download sources. Trojans are malicious programs, some of which can cause chain infections (i.e. download/install additional malware).
Scam emails are sent by the thousand, during large-scale operations called "spam campaigns". These messages contain download links of infectious files and/or the files are simply attached to the emails.
Infectious files can be in various formats, (e.g. archives, executables, Microsoft Office and PDF documents, JavaScript, etc.) and when they are opened, the infection process is initiated. Rather than activating licensed products, "cracking" tools can download/install malware.
Fake updaters infect systems by exploiting flaws of outdated products and/or by installing malicious software rather than the promised updates. Malware is often downloaded unintentionally from untrusted channels such as unofficial and free file-hosting websites, Peer-to-Peer sharing networks and other third party downloaders.
How to avoid malware infections
You are advised to use official and trustworthy download sources. It is also important to activate/update products with tools or functions provided by legitimate developers. Illegal activation tools ("cracks") and third party updaters are commonly employed to spread malware.
Do not open suspicious or irrelevant emails, especially those with any attachments or links found in them, as this can result in high-risk infection. To ensure device integrity and user safety, it is crucial to have a reputable anti-virus suite installed. This software must be kept up to date, used to run regular system scans and to remove detected/potential threats.
If your computer is already infected with malware, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate it.
Update 20 April 2021: It is known that XCSSET can now infect Mac computers with ARM64 (M1) and x86_x64 CPUs, and macOS Big Sur operating systems. Also, it uses malicious AppleScript files to create fake apps on macOS Big Sur and downloads icons (icon files) from a command and control server.
To make the fake icons look like the real ones, it modifies their "info.plist" files. It is important to mention that the latest XCSSET's modules modify icons so they would match the icons used in the version of the macOS installed on the infected machine.
Another important detail is that XCSSET loads its fake apps using its own "open" tool to avoid detection by macOS 11 security features.
It is also known that XCSSET now can steal sensitive information from websites such as 163[.]com, binance[.]com, Envato, Huobi, login.live[.]com, and nncall[.]net. Research shows that XCSSET can steal information from the Huobi page and replace cryptocurrency wallet addresses (change user's address to a specified address).
Update 18 February 2025: A new version of the XCSSET malware is now targeting users' personal information, such as data from digital wallets and the Notes app. The malware now uses better methods to hide its code, making it harder to analyze, and has added two ways to stay on the system: using zshrc (to run the payload every time a new shell session starts) and dock (downloading a signed tool to modify dock items).
It also adds itself to Xcode projects in new ways, placing the payload in different build settings so it can run later. XCSSET creates a fake Launchpad app to launch both the real app and the malware at the same time.
By targeting Xcode projects, XCSSET can reach more victims, stealing data like logins, chat app info, browser data, Notes app details, digital wallet information, and system files. It is advisable to check and verify Xcode projects, especially those from unofficial sources, to avoid being exposed to XCSSET.
Update 13 March 2025: XCSSET has been upgraded with more advanced obfuscation methods to bypass detection by security software. It also features improved persistence techniques, ensuring the malware stays on the infected system even after reboots or attempts to remove it. These updates make it more difficult to detect and eliminate.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "XCSSET"?
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:

Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
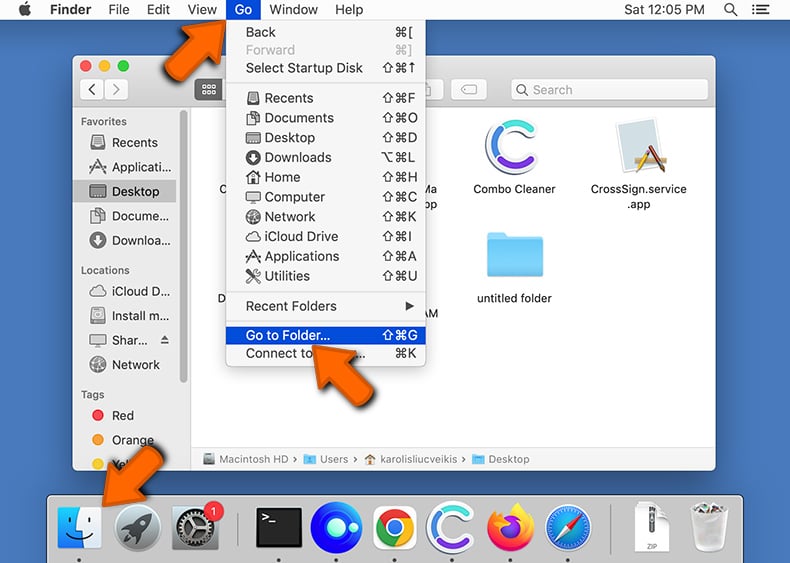
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
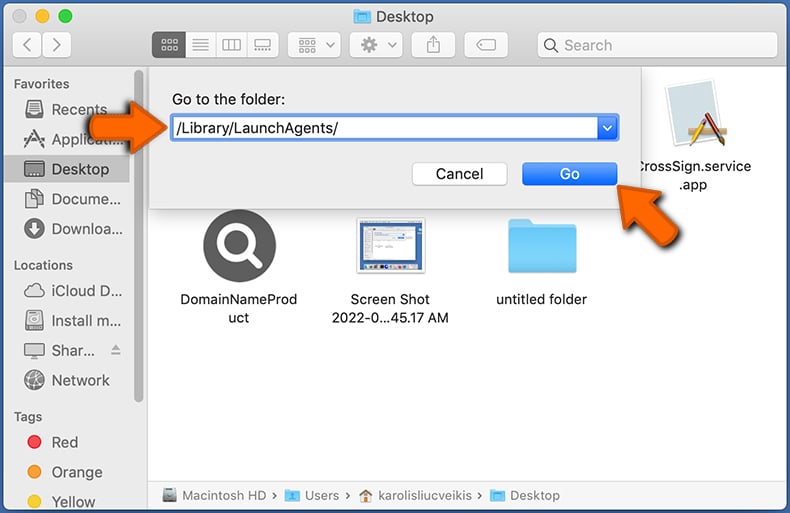
In the Go to Folder... bar, type: /Library/LaunchAgents/
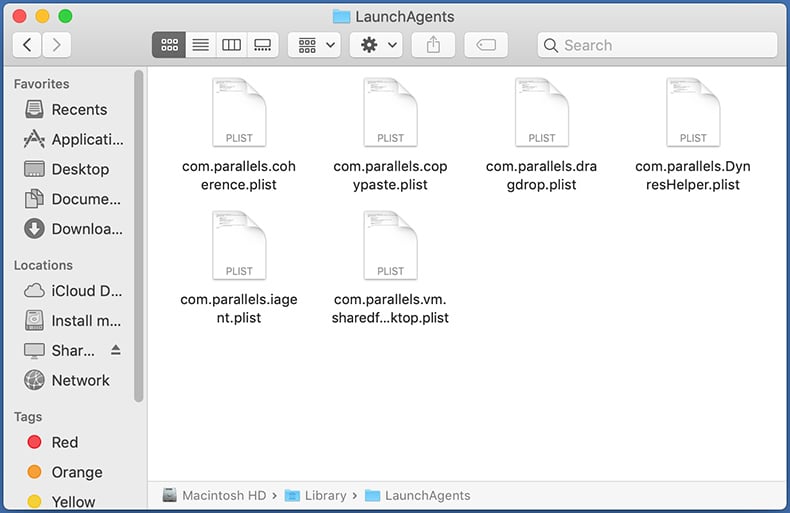
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
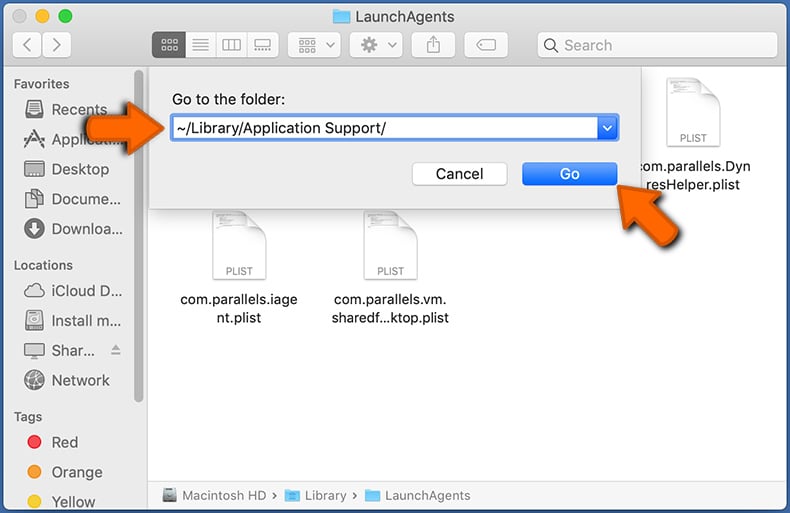
In the Go to Folder... bar, type: ~/Library/Application Support/
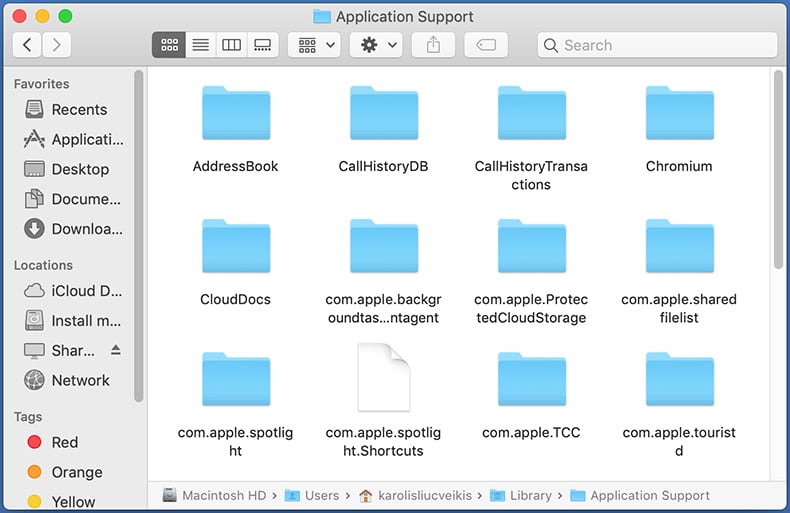
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
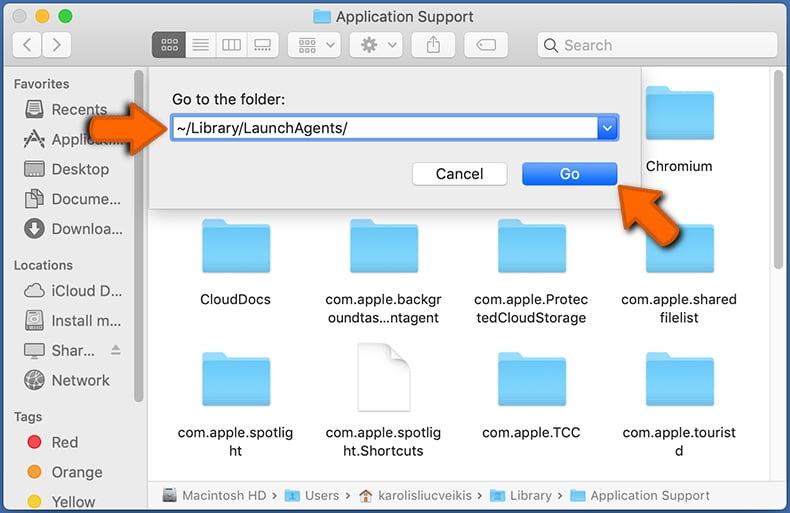
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
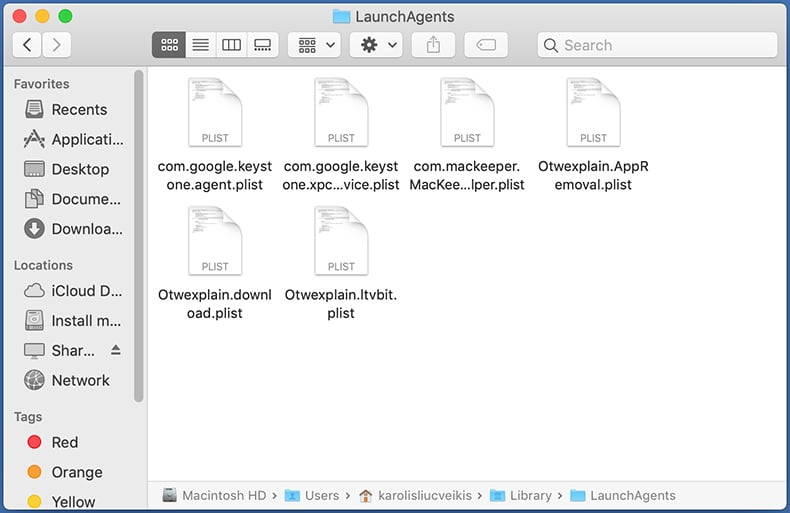
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
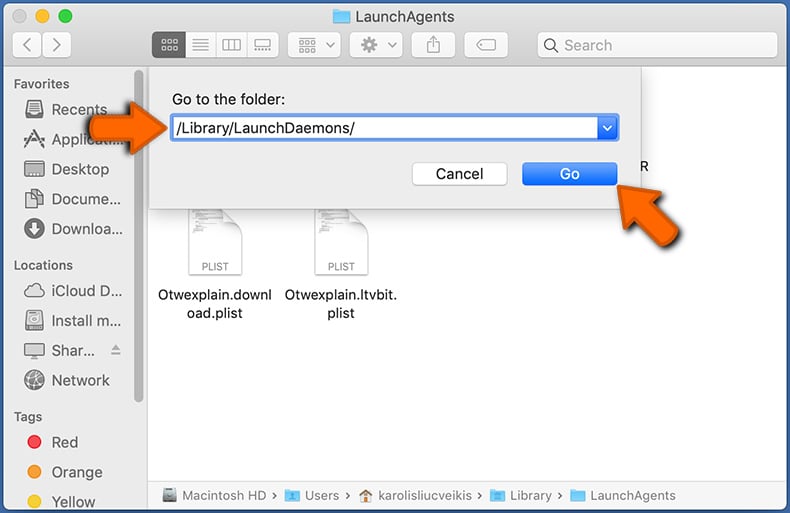
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
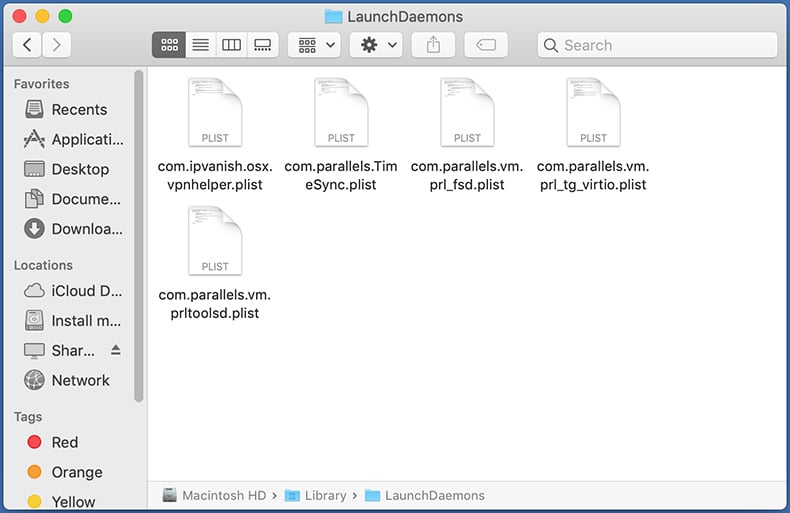
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
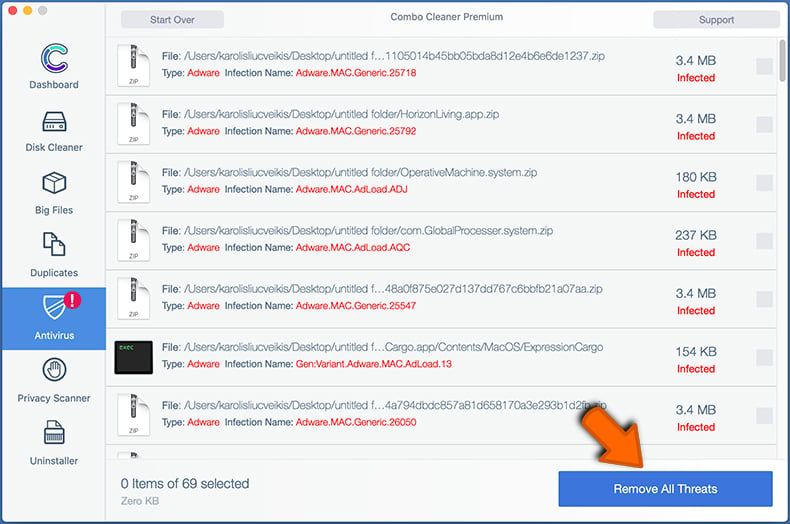
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
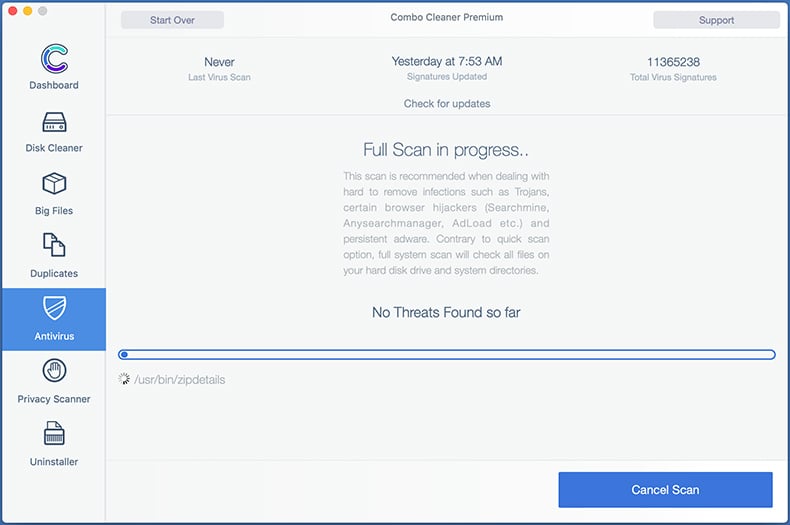
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
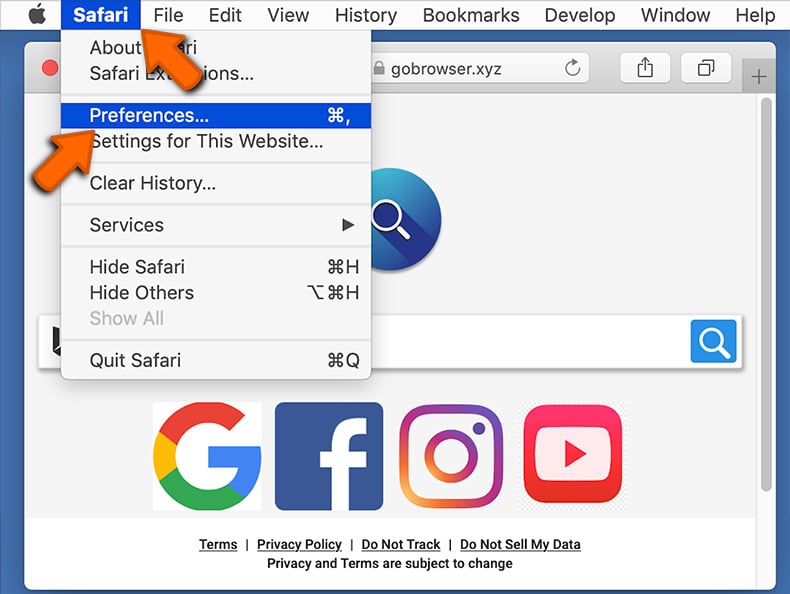
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
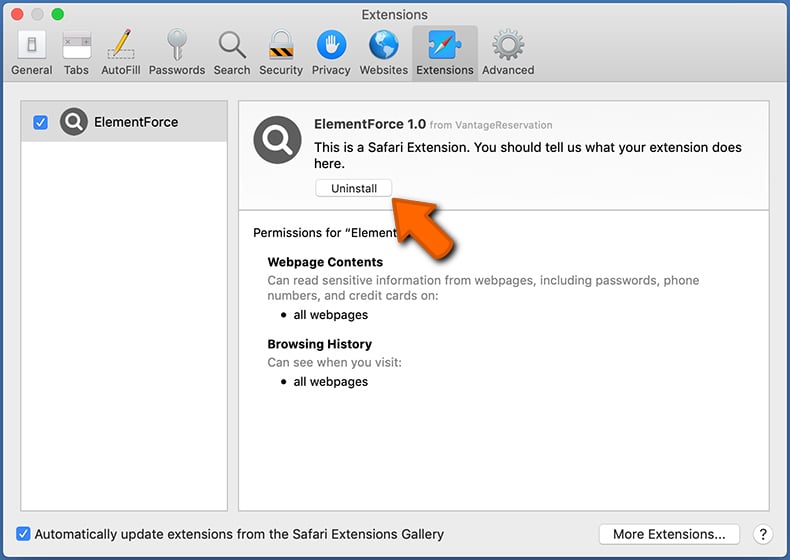
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
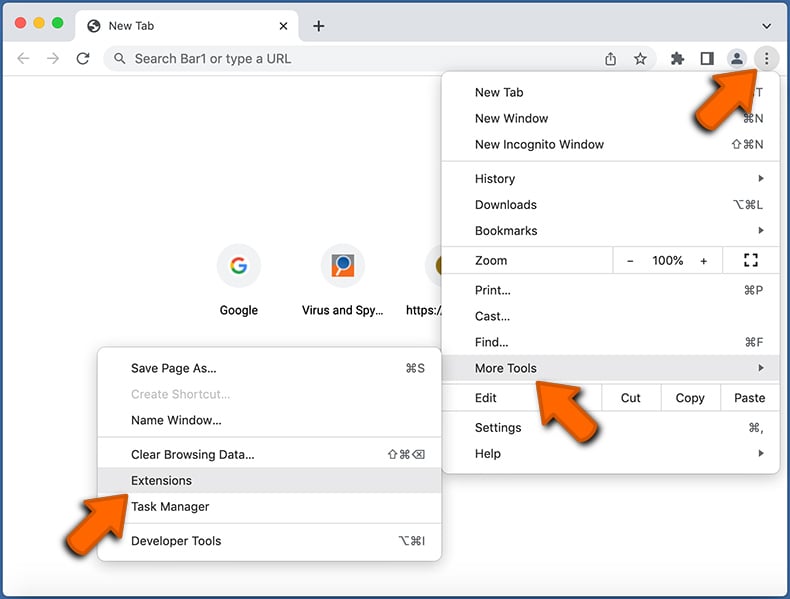
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
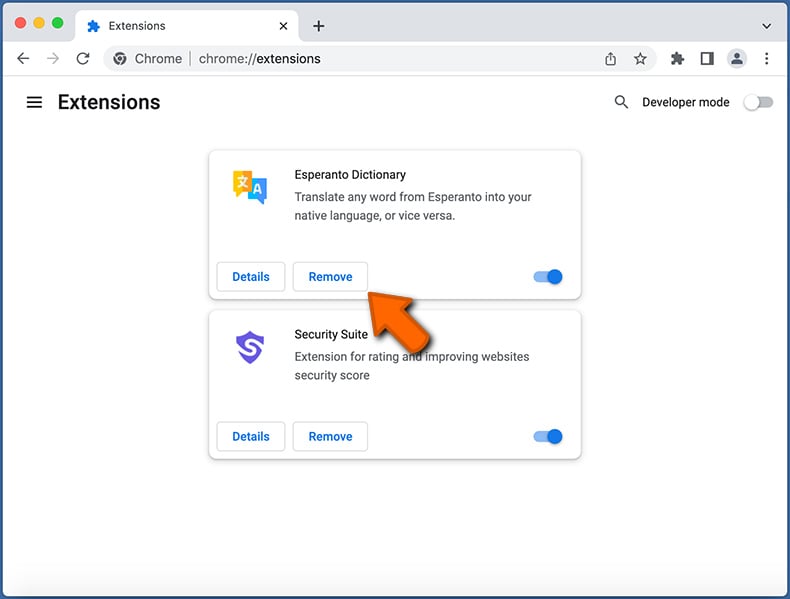
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
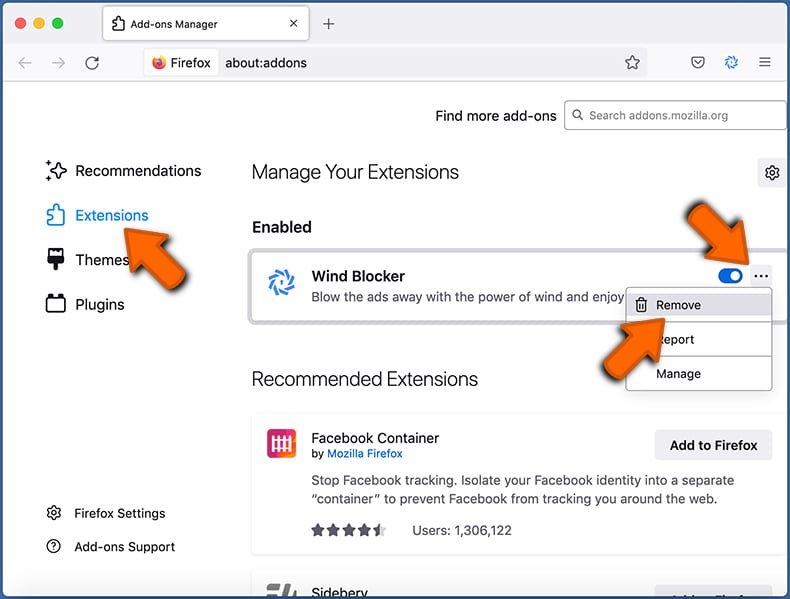
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
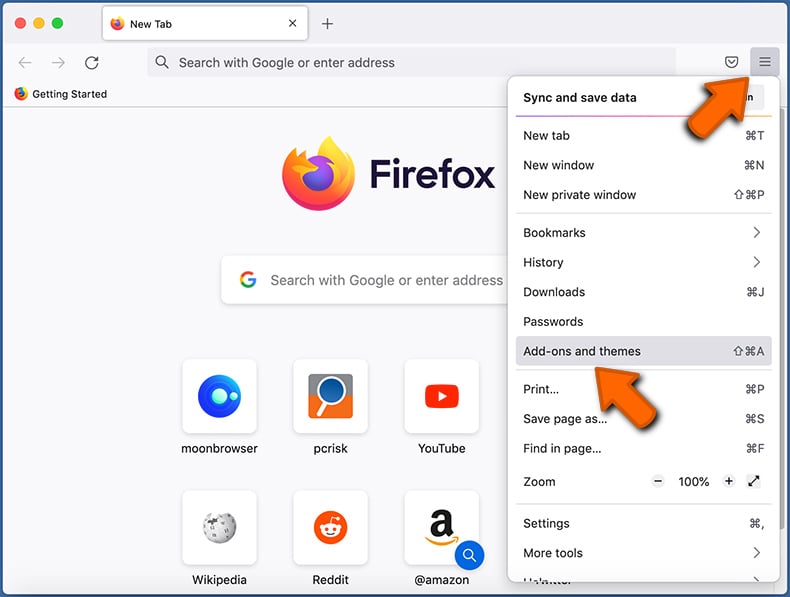
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Frequently Asked Questions (FAQ)
My computer is infected with XCSSET malware, should I format my storage device to get rid of it?
While formatting your storage device can remove XCSSET malware, it also risks permanent data loss if your files are not backed up. Therefore, it is better to scan and clean your system with a trusted malware removal tool like Combo Cleaner.
What are the biggest issues that malware can cause?
Malware infections can lead to serious consequences, including financial loss, identity theft, system performance problems, further infections, and data encryption. The extent of the damage depends on the type of malware and its abilities.
What is the purpose of XCSSET?
Once the system is infected with XCSSET, the malware can steal sensitive information from various applications, including digital wallets and the Notes app. It can also take screenshots, encrypt files as ransomware, and display ransom messages. Additionally, it targets browsers by altering pages, stealing cookies, logging passwords, and obtaining credentials from services like PayPal, Google, and Apple.
How did XCSSET infiltrate my computer?
XCSSET (at least newer versions) typically infiltrates a computer through infected Xcode projects. These malicious projects are often downloaded from unofficial repositories or third-party websites.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and remove nearly all known malware infections. However, advanced malware often resides deep within the system, so it is essential to perform a full system scan to ensure complete removal.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion