Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Zegost?
Zegost functions as information-stealing malware, and cybercriminals have been observed distributing it through targeted email attacks. This malicious software has been in existence since around 2011. The threat actors linked to Zegost are known for their persistence and ingenuity, employing various exploits to create and maintain connections with their targeted victims.

More about Zegost
Zegost employs various data collection processes to accomplish its objectives. It begins by identifying the targeted machine's operating system version, processor details, and running processes, sending this information to its command-and-control (C2) server.
The malware also checks network connections, RDP port numbers, and QQ messenger login details, relaying the collected data to the C2 servers. Moreover, it records keystrokes, which means it obtains data entered with the keyboard.
To evade detection, Zegost exhibits unique features such as actively clearing event logs (Application, Security, and System) and launching processes, distinguishing it from typical infostealers. It demonstrates a capability to operate with both visible and hidden windows, and it ensures persistence through dual methods: automatic service launch and registry key manipulation.
Zegost's evolution over the years includes the integration of COM programming, an uncommon strategy in malware. Its multifaceted spying capabilities extend to capturing video via the device's webcam, using the DirectShow capture filter for device enumeration. The malware also detects sandbox environments, enhancing its evasion tactics.
| Name | Zegost information stealer |
| Threat Type | Information Stealer |
| Detection Names | Avast (Win32:Trojan-gen), Combo Cleaner (Trojan.GenericKDZ.84947), ESET-NOD32 (A Variant Of Win32/Kryptik.FHSE), Kaspersky (HEUR:Trojan.Win32.Siscos.gen), Microsoft (Backdoor:Win32/Farfli!pz), Full List (VirusTotal) |
| Symptoms | Information stealers are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks', P2P networks, etc. |
| Possible Damage | Stolen sensitive information, identity theft, monetary loss, privacy issues, and more. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
Victims of a Zegost infection may face a myriad of serious issues. The malware's meticulous data collection, including keystrokes and sensitive system details, puts user privacy at significant risk. With the ability to capture video through webcams, Zegost further invades the personal space of users.
The malware's advanced evasion tactics, such as clearing event logs and persistent operation, not only make detection challenging but also contribute to potential long-term damage to the affected computer. Users may experience compromised security, increased susceptibility to identity theft, and an overall loss of control over their digital environment.
More examples of information stealers are Editbot, MrAnon, and Vare.
How did Zegost infiltrate my computer?
Zegost is disseminated via targeted email attacks, indicating a deliberate and focused strategy by threat actors. In these attacks, the malware is likely concealed within seemingly innocuous email attachments or links, exploiting the recipients' trust to gain access to their systems.
Also, malware is distributed via malvertising, where attackers inject malicious code into online advertisements, leading users to unwittingly download malware. Additionally, social engineering schemes, such as fake software updates or fraudulent alerts, are employed to trick users into executing malware.
Additional channels used to disseminate malware are pirated software, cracking tools, P2P networks, third-party downloaders, software vulnerabilities, etc.
How to avoid installation of malware?
Users can enhance their computer's protection against malware by maintaining updated and reputable antivirus software. Additionally, users should exercise caution when interacting with emails, avoiding clicking on suspicious links or downloading attachments from unknown sources.
Furthermore, users should only download software from official and trusted sources, avoiding third-party websites that may harbor malicious content. Keeping the operating system and all installed software up to date with the latest security patches is equally important. Additionally, it is recommended to avoid interacting with suspicious ads and pop-ups.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
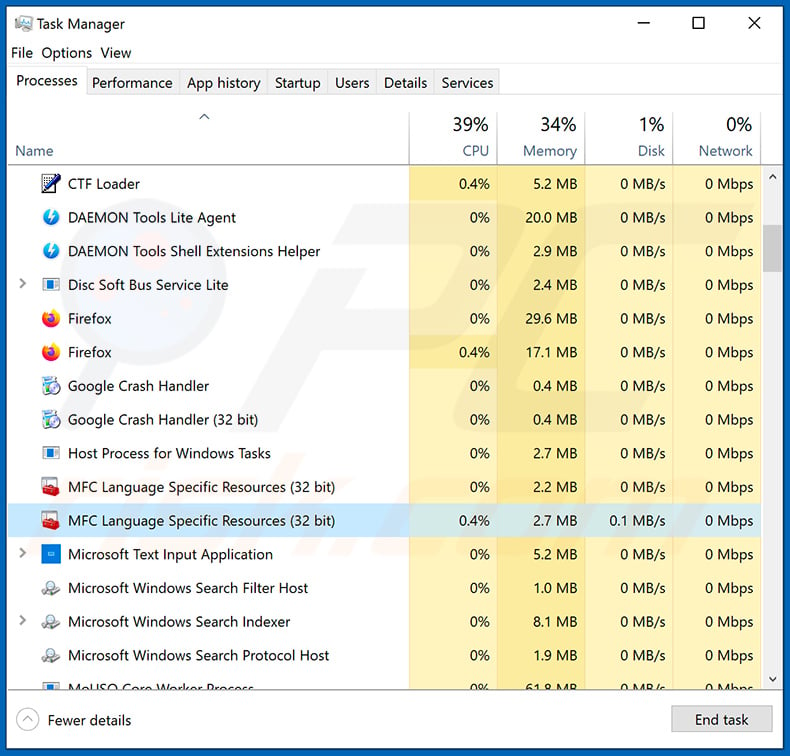
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
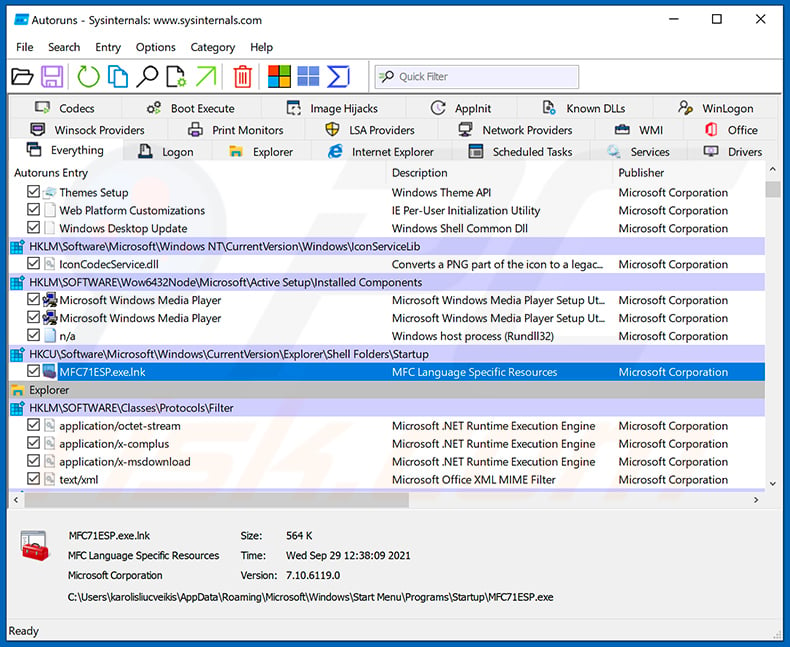
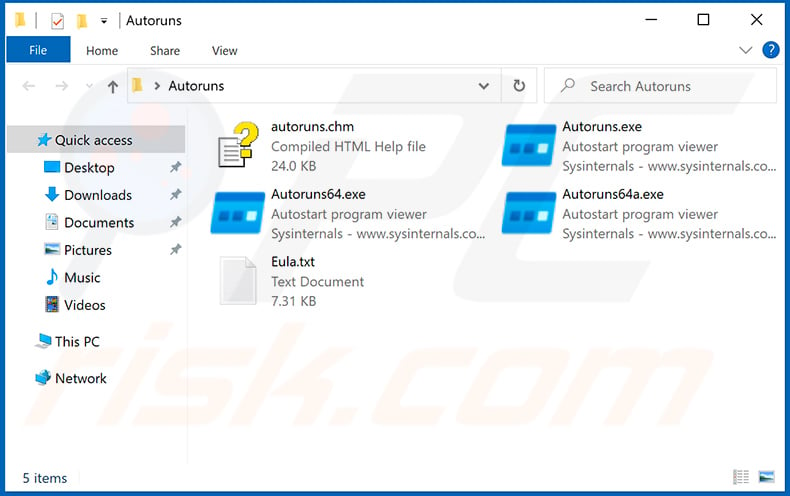
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
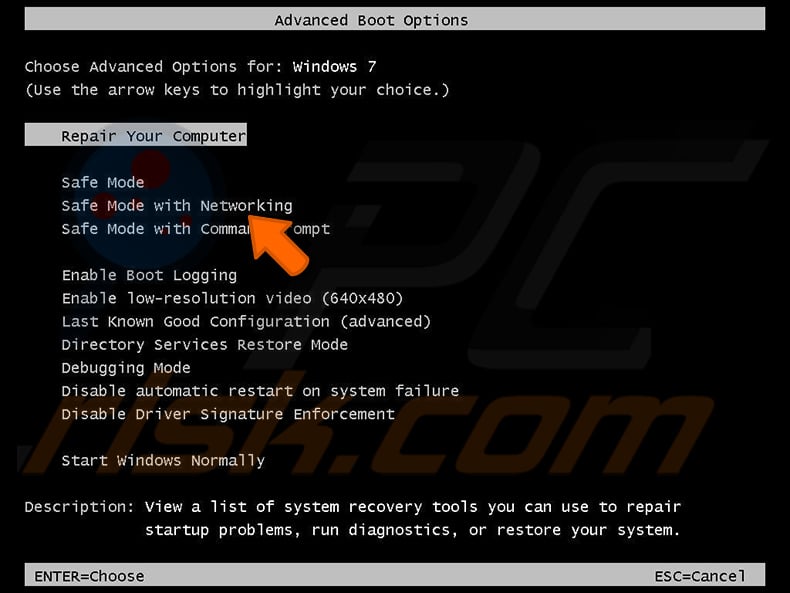
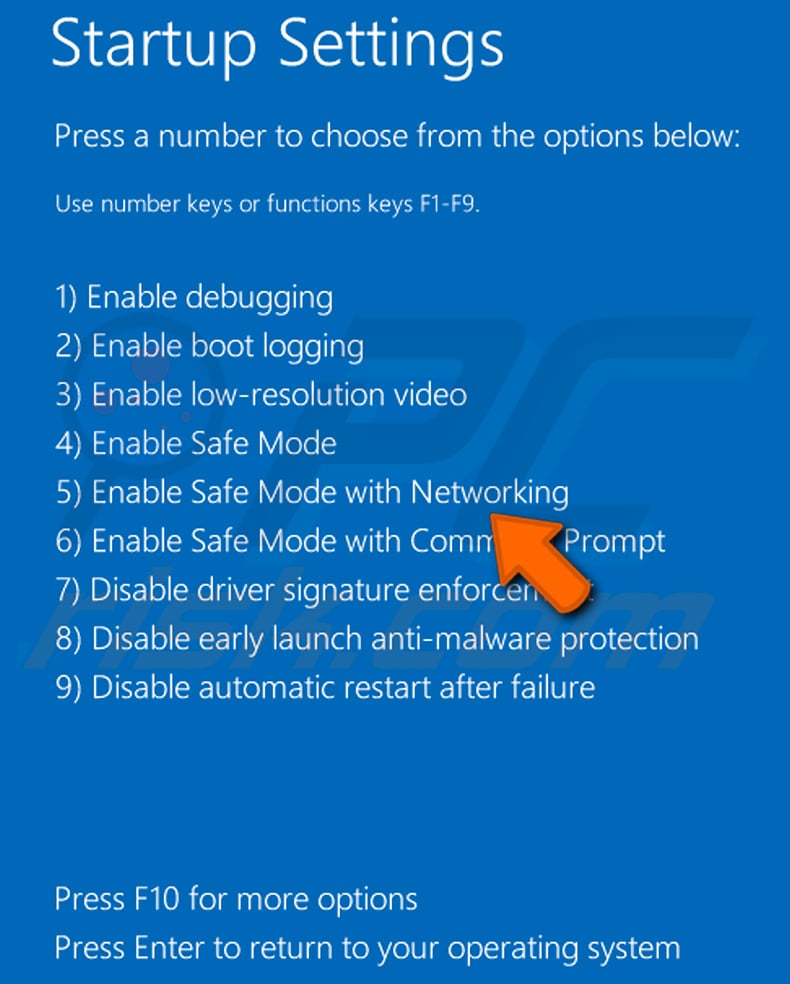
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
Video showing how to start Windows 7 in "Safe Mode with Networking":
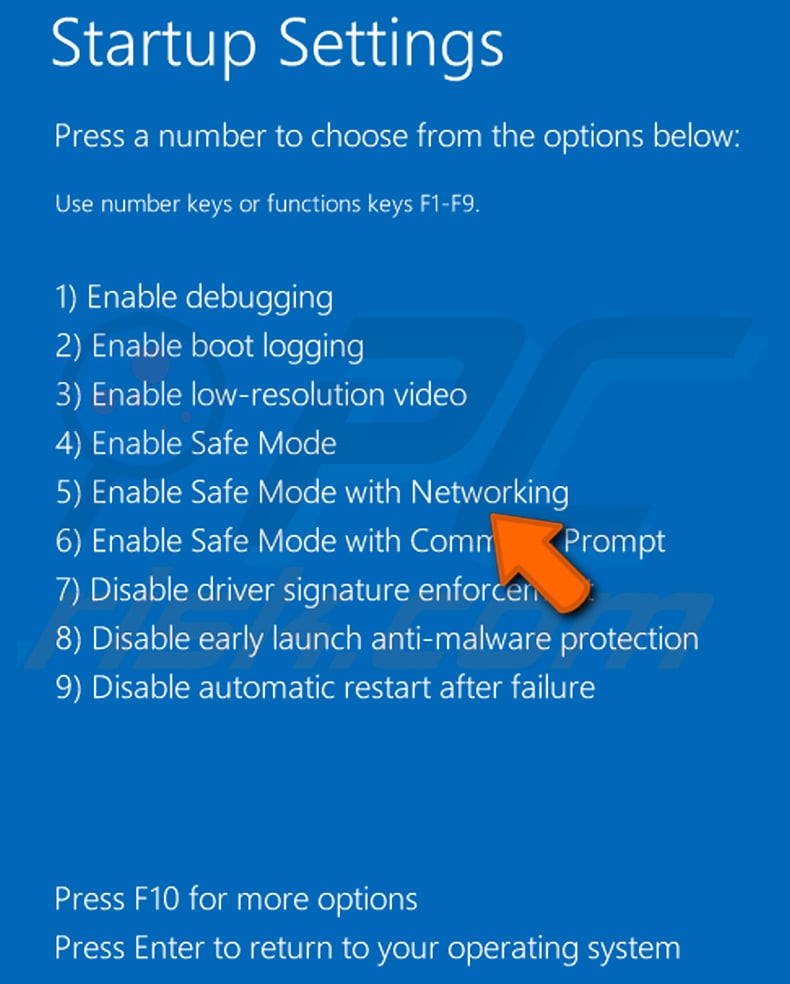
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
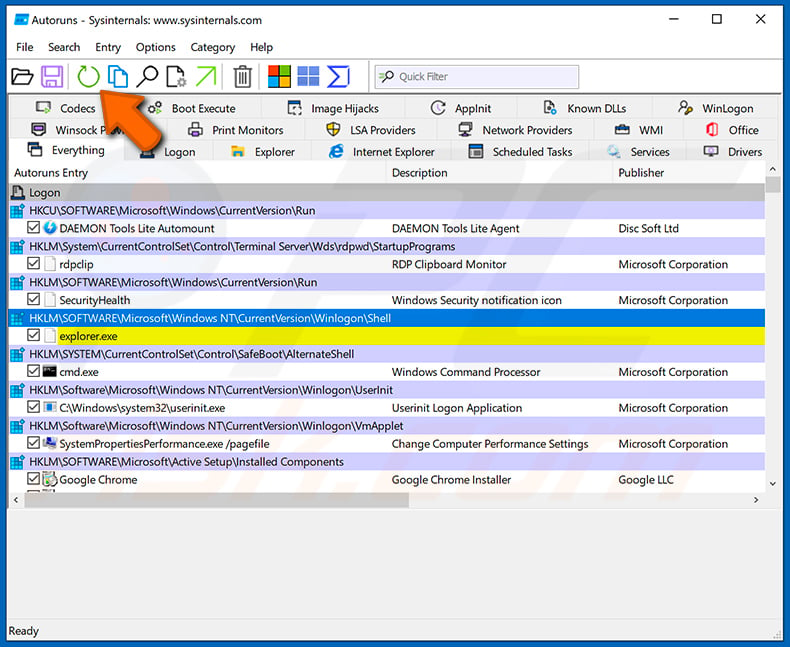
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
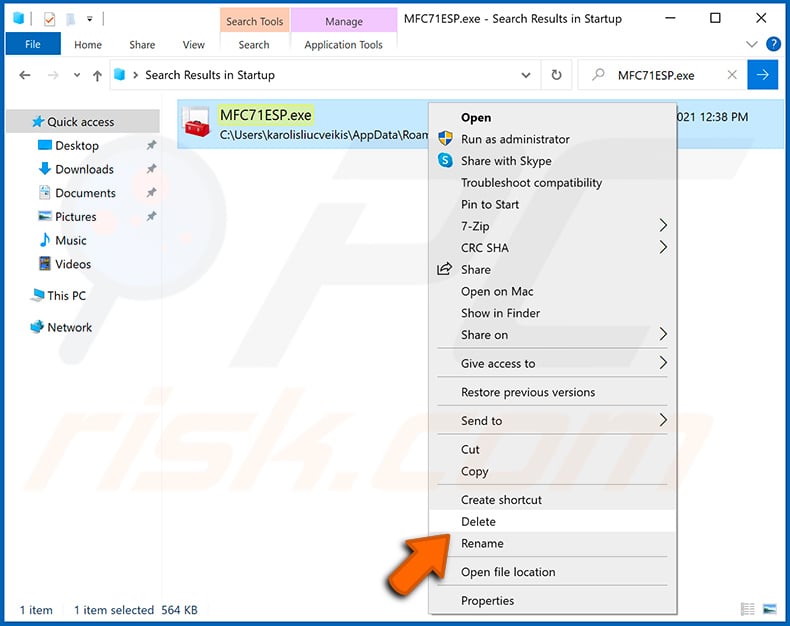
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
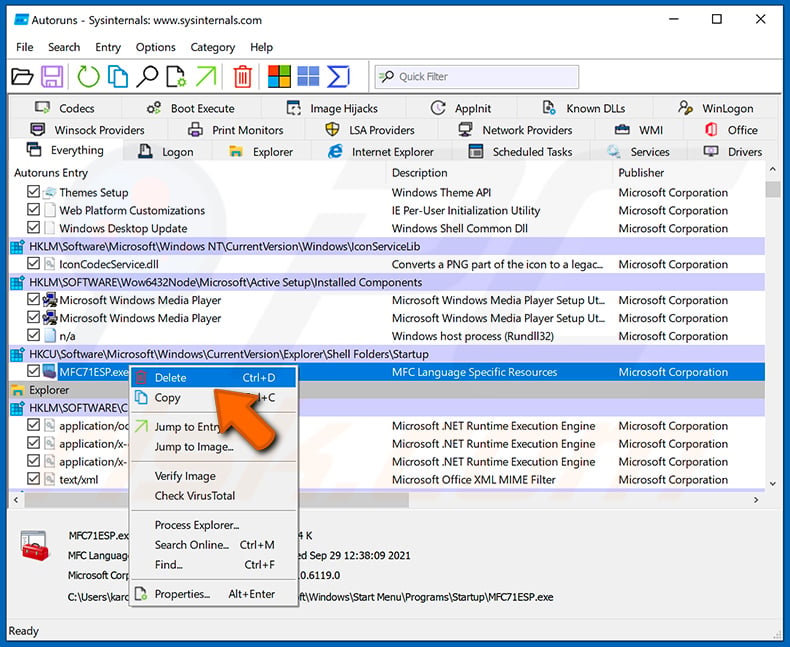
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Zegost malware, should I format my storage device to get rid of it?
Initiating a format on your storage device is an extreme step and should only be contemplated when alternative approaches, such as relying on trustworthy antivirus or anti-malware software, prove unsuccessful in eliminating the Zegost malware.
What are the biggest issues that malware can cause?
Having a computer infected with malicious software can result in substantial problems, such as data theft, system damage, file encryption, financial losses, and compromised privacy.
What is the purpose of Zegost malware?
The purpose of the Zegost malware is to steal information from infected systems, collecting data such as operating system details, processor information, network connections, RDP port numbers, QQ login details, and recorded keystrokes.
How did a malware infiltrate my computer?
Malware distribution commonly involves various methods, such as sending malicious attachments or links through emails, drive-by downloads, malicious ads, P2P networks, pirated software, and exploiting software vulnerabilities. Zegost, specifically, is recognized for being distributed through email channels.
Will Combo Cleaner protect me from malware?
Certainly, Combo Cleaner has the capability to identify and remove nearly all known malware infections. However, advanced malware has the ability to conceal itself deeply within the system. Therefore, it is crucial to perform a comprehensive system scan to eliminate hidden malware.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion