How to remove LuaDream from infected computers
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What kind of malware is LuaDream?
In the dynamic field of cybersecurity, an interesting new development has surfaced. Sandman, a known advanced threat actor, has introduced an unusual and complex modular backdoor. What sets this apart is its use of the LuaJIT platform, which is not commonly seen in cyber threats. This innovative malware, named LuaDream, marks a noteworthy advancement in cybersecurity.
More about LuaDream
LuaDream is a multifaceted and versatile backdoor with various components and protocols. Its primary functions include overseeing attacker-supplied plugins and extracting both system and user data. The structure and design of LuaDream suggest that it is a well-maintained, actively developed project of significant complexity and scale.
The main purpose of LuaDream is to secretly connect the victim's computer to another one controlled by cybercriminals. It sends over information about victim's computer, like what type it is, who is using it, and even some private data. Moreover, LuaDream can communicate with the other computer in various ways, like through the internet or secret channels.
Additionally, LuaDream can change its disguise to avoid being detected by security programs. LuaDream can cause significant issues for its victims. Firstly, it can lead to data theft, as it gathers sensitive information about the victim's computer and sends it to the cybercriminals. This stolen data may include personal information, login credentials, and even financial details.
LuaDream's ability to communicate with remote servers and execute various commands means it can be used for a range of malicious activities, such as downloading and executing additional malware or carrying out further attacks on the victim's network or other targets.
LuaDream's complexity and adaptability make it a persistent threat, and its ability to disguise its activities can make detection and removal challenging, leaving victims vulnerable to ongoing attacks and data breaches.
| Name | LuaDream backdoor |
| Threat Type | Backdoor Malware |
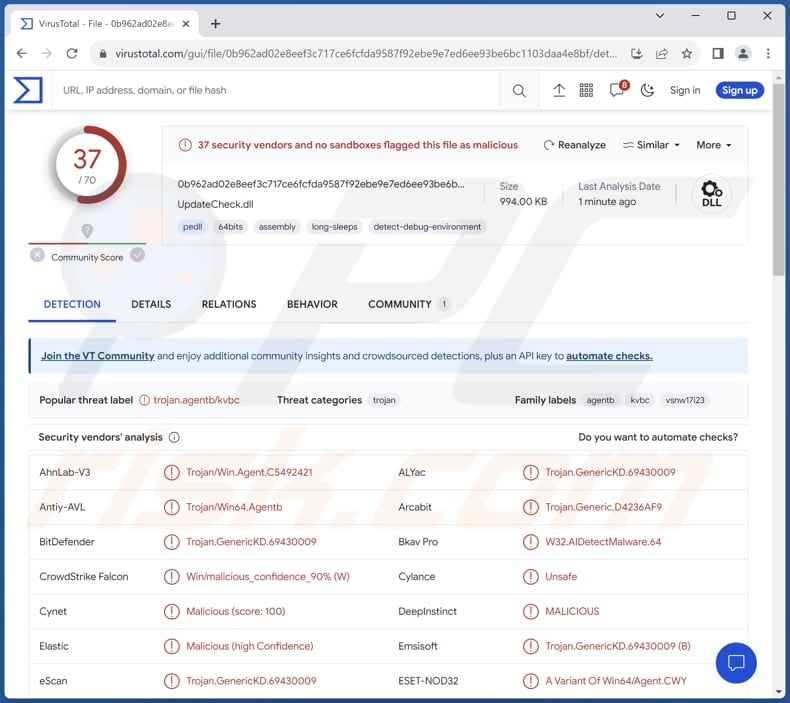
| Detection Names | Arcabit (Trojan.Generic.D4236AF9), Combo Cleaner (Trojan.GenericKD.69430009), ESET-NOD32 (A Variant Of Win64/Agent.CWY), Kaspersky (Trojan.Win64.Agentb.kvbc), Microsoft (Trojan:Win32/Wacatac.B!ml), Full List (VirusTotal) |
| Symptoms | Backdoor malware is designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Conclusion
LuaDream is a highly sophisticated and adaptable malware threat known for its multi-component structure and use of the LuaJIT platform. It poses significant risks to victims, including data theft and the potential for further malicious activities. Its complex design and ability to disguise its activities make it a persistent and challenging threat to address in the cybersecurity landscape.
How did LuaDream infiltrate my computer?
Users can unknowingly introduce malware into their computers in multiple ways. One common method involves downloading software or files from dubious sources, especially those that offer pirated software, key generators, or counterfeit websites promising access to copyrighted material or software cracks.
Malware can also infiltrate a system when users interact with questionable pop-up ads or download attachments from unsolicited emails. Furthermore, visiting compromised or malicious websites, connecting infected external storage devices, or neglecting to update software and security measures can create vulnerabilities that cybercriminals exploit to infect computers.
How to avoid installation of malware?
Firstly, ensure that you only download software and files from reputable sources, avoiding unverified or pirated content. Secondly, be cautious when clicking links in emails, especially if the sender is unknown, and avoid downloading attachments from suspicious emails. Regularly update your operating system and all software to patch potential vulnerabilities that malware can exploit.
Do not interact with shady ads or notifications from questionable websites. Additionally, install and maintain reputable antivirus or anti-malware software. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Update October 10, 2024: Recently, cybercriminals behind LuaDream have been spotted targeting the educational sector. These attacks take advantage of the popularity of Lua gaming engine add-ons among the student gaming community.
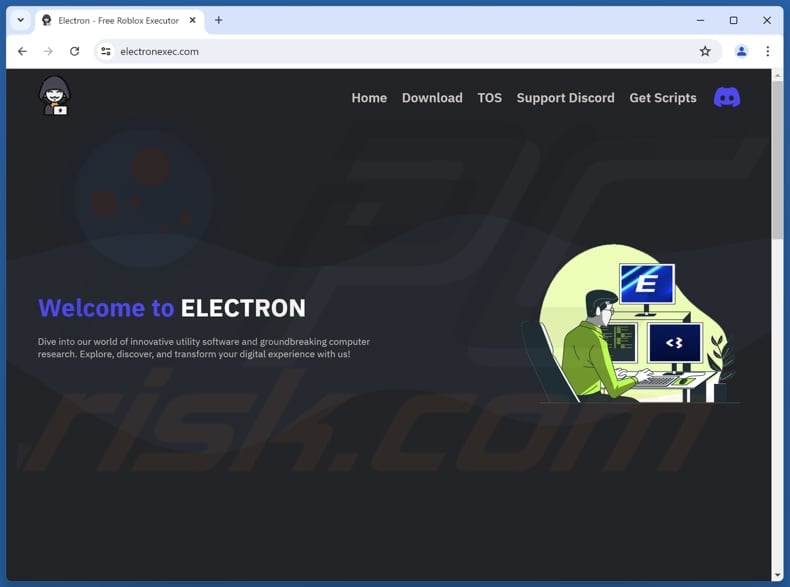
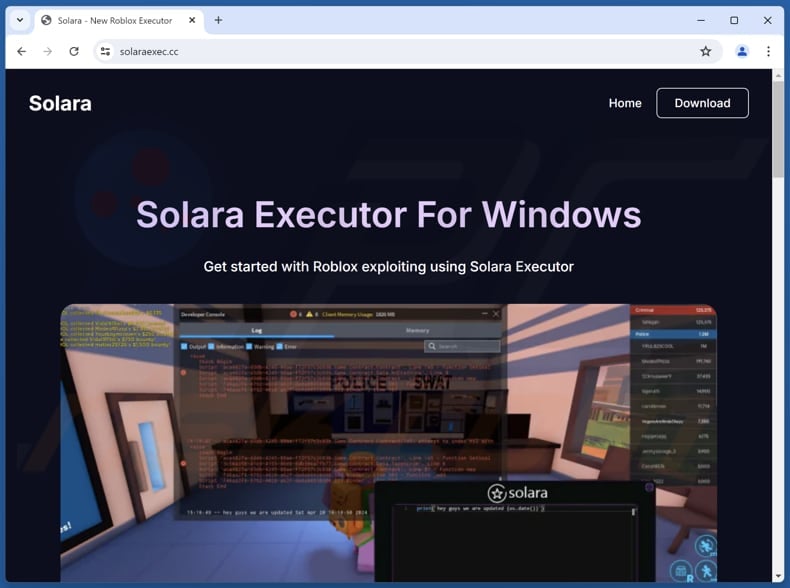
LuaDream is delivered via advertisements for the Solara and Electron executors, popular cheating script engines often linked to Roblox, which directed users to various Lua malware variants hosted on several GitHub repositories.
In recent campaigns, LuaDream is typically packaged as an installer or a ZIP archive, which usually includes four components: a Lua compiler, a Lua DLL file, an obfuscated Lua script, and a batch file. Once the batch file is executed, the loader connects to a C2 server and sends information about the infected machine.
The server then assigns two types of tasks: Lua loader tasks, which help the malware stay hidden and active, and task payloads, which download and set up additional malware.
Screenshot of the Electron site hosting LuaDream:
Screenshot of the Solara site hosting LuaDream:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is LuaDream?
- STEP 1. Manual removal of LuaDream malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
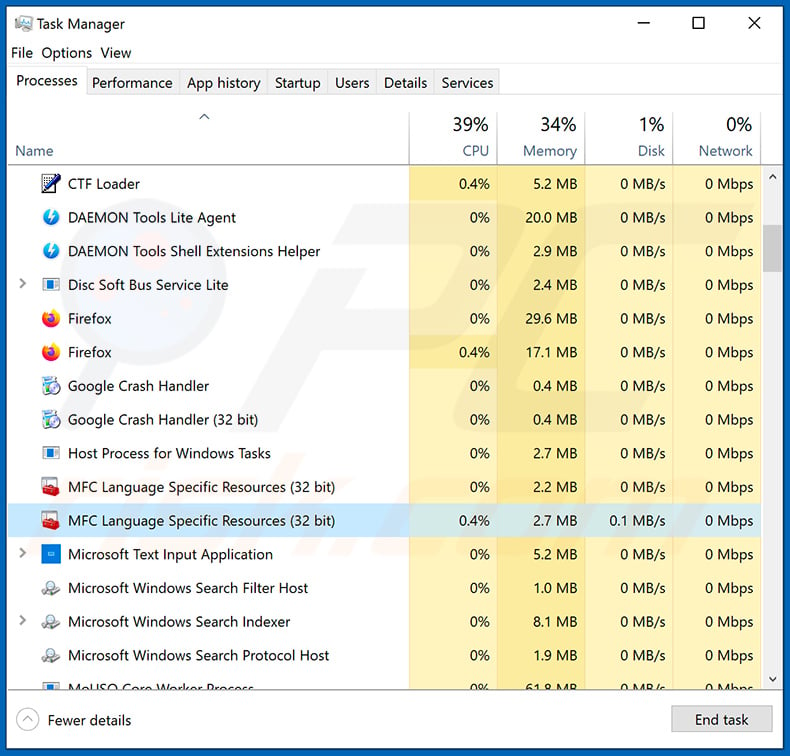
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
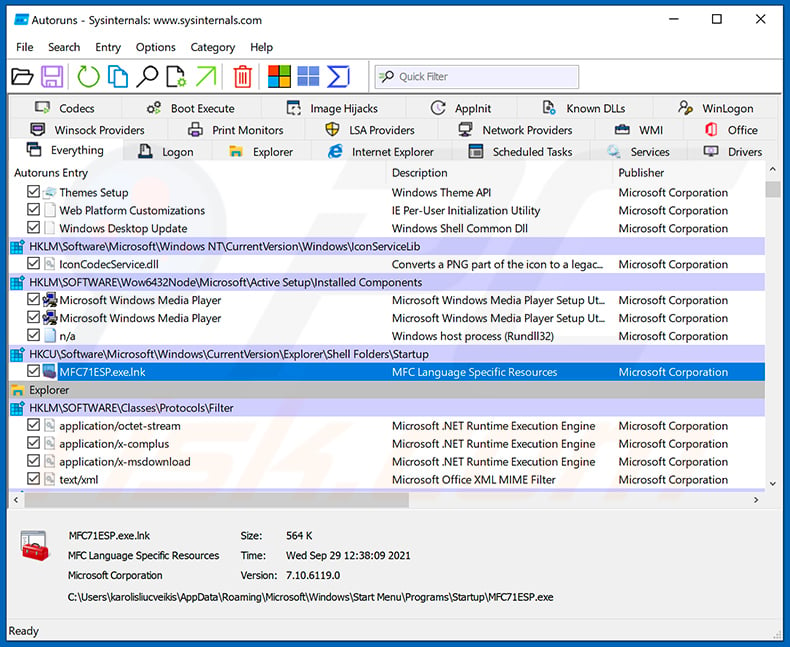
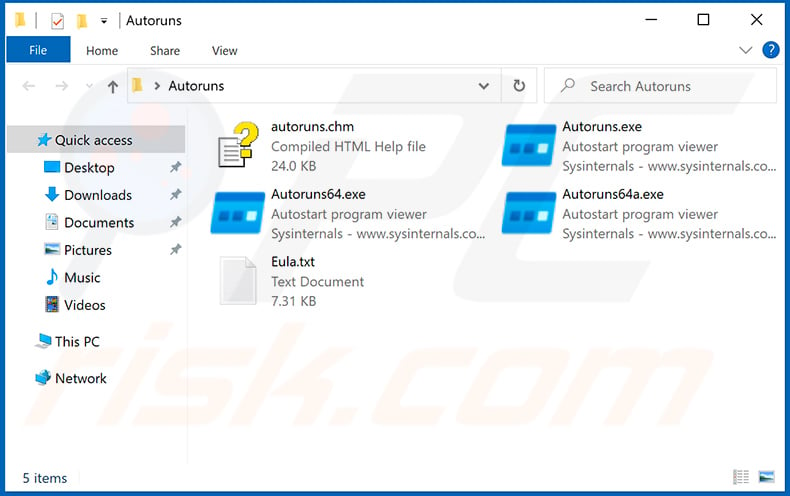
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
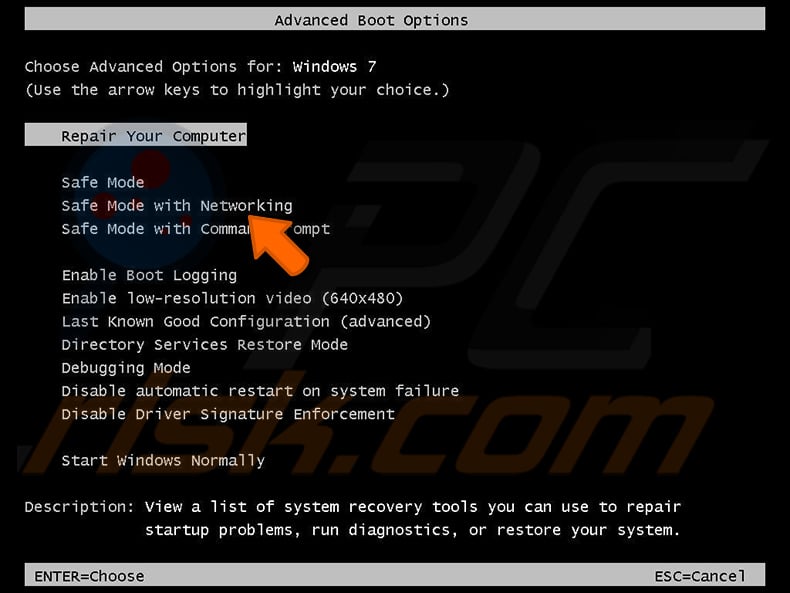
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
Video showing how to start Windows 7 in "Safe Mode with Networking":
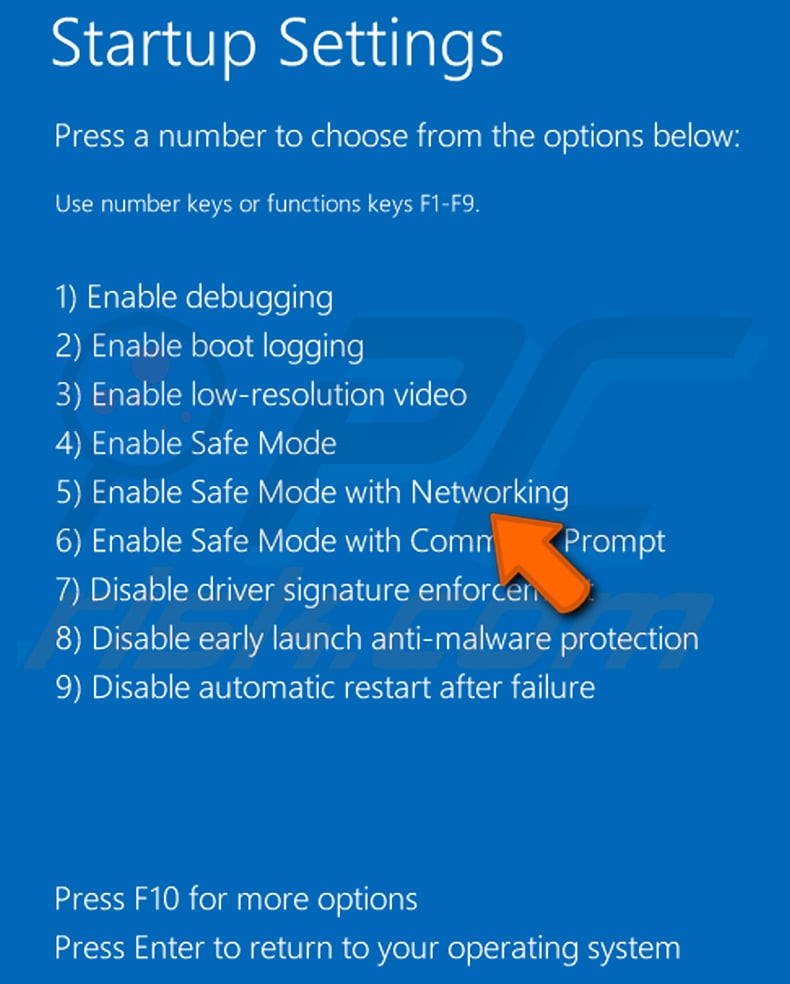
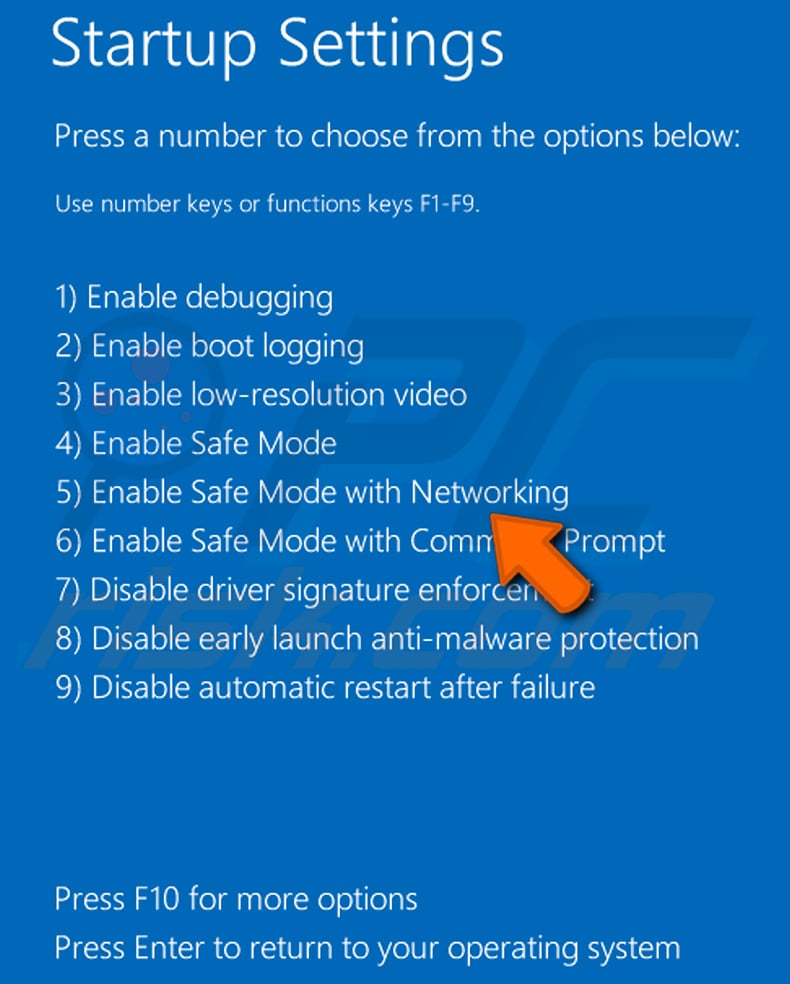
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
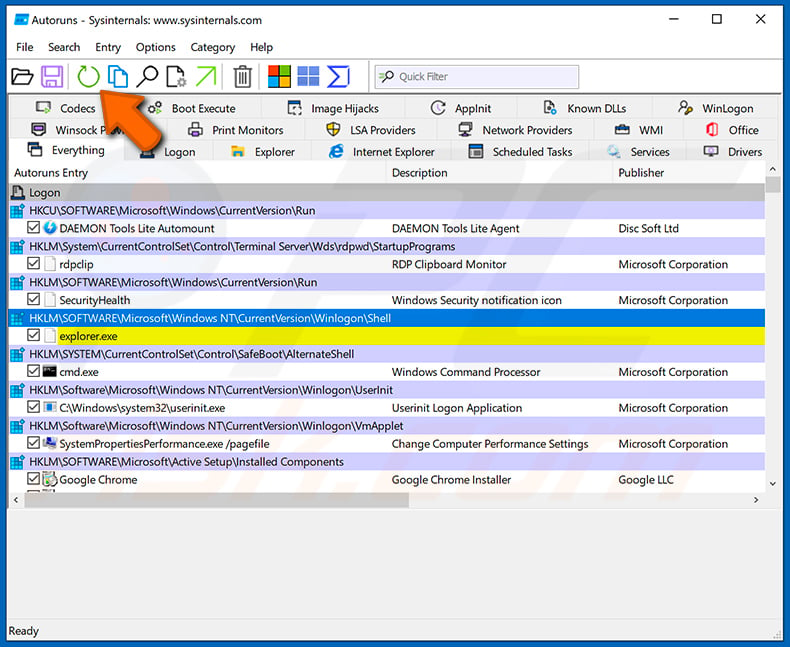
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
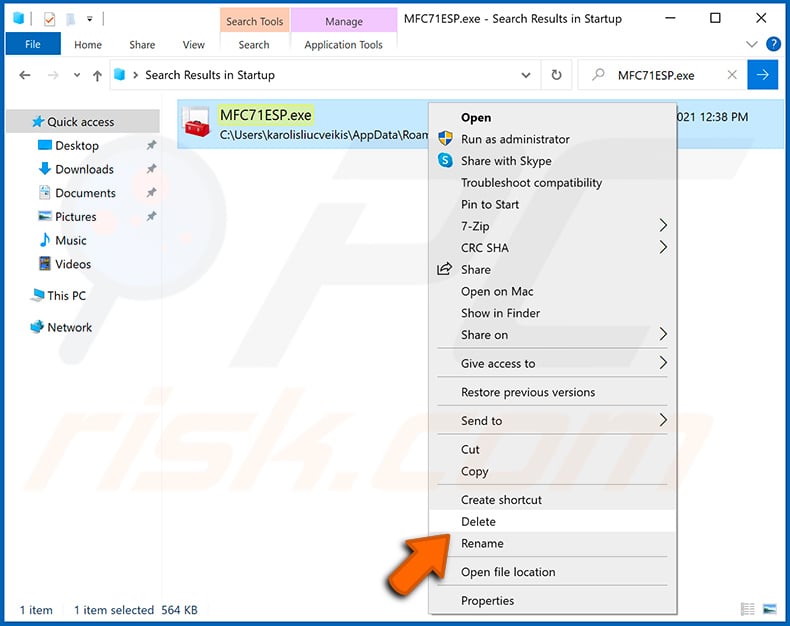
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
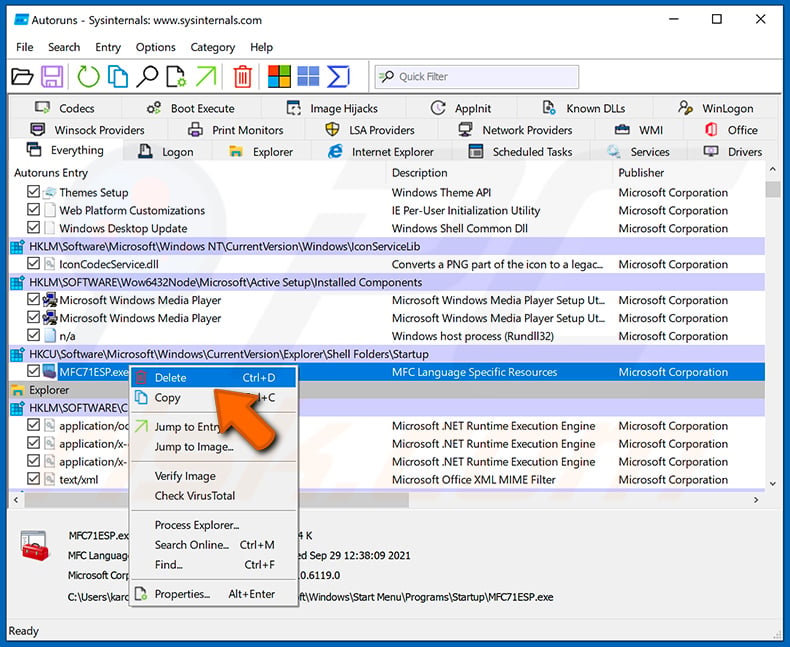
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with LuaDream malware, should I format my storage device to get rid of it?
Rather than resorting to the extreme step of immediately formatting your storage device, which should be considered a last resort, it is advisable to explore alternative solutions. It is recommended to investigate alternatives, such as using trusted antivirus and anti-malware tools like Combo Cleaner to conduct scans and remove the LuaDream malware.
What are the biggest issues that malware can cause?
Malware can result in various negative consequences, including data breaches, financial losses, privacy infringements, and disruptions to system functionality. Additionally, it can put personal and sensitive information at risk.
What is the purpose of LuaDream malware?
LuaDream primarily functions to establish a covert connection between the victim's computer and one under the control of cybercriminals. It transmits details about the victim's computer, including its type, user identity, and even certain confidential information.
How did a malware infiltrate my computer?
Computers can become infected through various means, often due to user actions or vulnerabilities in the system. One common avenue is downloading files or software from unverified or malicious websites, which may contain malware. Clicking on suspicious email attachments or links in phishing emails can also introduce malware. Additionally, not keeping the operating system and software up to date can leave the computer vulnerable to exploitation by cybercriminals.
Will Combo Cleaner protect me from malware?
Combo Cleaner has the capability to detect and eliminate the majority of malware infections. However, it is essential to understand that advanced malware can hide deeply within the system. Therefore, conducting a thorough system scan is crucial to uncover and remove any hidden threats effectively.

▼ Show Discussion