Removal instructions for the Chromium Extension-Loading Shortcut Virus
Browser HijackerAlso Known As: Chromium extension-loading shortcut malware
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Chromium extension-loading shortcut virus?
"Chromium extension-loading shortcut virus" refers to a type of infection affecting Chromium-based browsers like Google Chrome, Microsoft Edge, Brave, and countless others. In these infections, modified LNK (Windows Shortcut) files are used to launch the legitimate browser alongside malicious extensions.
Recent browser-targeting viruses combine LNK and CRX (Chromium Extension) files, which results in stealthy infections leaving the victim unbeknownst to their presence.
This infection technique can be used to introduce a variety of malicious software to compromised browsers. The extensions could be used to steal browsing data, personally identifiable details, log-in credentials, cause chain infections, manipulate website contents, or possess other harmful abilities.

Chromium extension-loading shortcut virus overview
In Chromium extension-loading shortcut viruses when a user opens their Chromium-based browser using its shortcut, the altered LNK file which contains an additional command (e.g., "--load extension") added to its target.
Once executed, shortcut opens the genuine browser that has malicious extensions already loaded onto it. The extensions are stored in a folder created by the malware that drops these shortcuts. Path to the extension folder is also specified in the modified shortcut's target.
These viruses include either CRX files or unpacked extensions (i.e., directories comprising extension files). Some browsers allow for manual installation of extensions using these files, while others limit users to the extensions available on Web stores for security reasons.
At the time of writing, several notable extension-loading shortcut virus chains have been observed; these infections largely targeted the financial sector. One of these virus chains features BRAINSTORM – a dropper written in Rust, which replaces LNK files with ones intended to open the legitimate browser running the RILIDE malicious extension.
RILIDE has multiple functionalities; it collects relevant information, such as the victims' IP address (geolocation) and browsing history (visited websites), and it takes screenshots of browser tab views. When the victim visits a targeted site, RILIDE employs JavaScript injection to facilitate account credential theft and other malicious activities.
To elaborate, stolen finance-related accounts (e.g., online banking, e-commerce, cryptocurrency wallets, etc.) can be used to perform fraudulent transactions or make online purchases.
Cyber criminals can also steal the identities of social account owners (e.g., emails, social networking/media, messengers, etc.) and ask their contacts/friends/followers for loans or donations, promote scams, and spread malware by sharing malicious files/links.
Another chain culminating in RILIDE began with a set of files presented as the desktop version of TradingView – a trading and investing centered charting platform and social network. This infection chain progressed to the BRAINFOG – a Node.js packaged binary dropper, which drops Visual Basic scripts (used for LNK replacement) and RILIDE.
An Advanced Installer compiled dropper dubbed BRAINLINK was also used to drop a CAB file containing LNK-modifying PowerShell scripts and RILIDE.
Yet another virus variant implemented the PUFFPASTRY backdoor malware, which is capable of manipulating executable files and even infiltrating malicious ones.
In summary, Chromium extension-loading shortcut viruses can result in multiple infections, severe privacy issues, financial losses, and identity theft.
| Name | Chromium extension-loading shortcut malware |
| Threat Type | Malicious browser extension, Malware, Backdoor, Password-Stealing Malware |
| Detection Names (modified shortcut) | Malwarebytes (RiskWare.ShortcutHijack), Full List Of Detections (VirusTotal) |
| Detection Names (BRAINSTORM) | Avast (Script:SNH-gen [Trj]), Combo Cleaner (Gen:Variant.Zusy.445836), ESET-NOD32 (A Variant Of Generik.BVQAQAJ), Kaspersky (Not-a-virus:HEUR:AdWare.Win32.Agent), Microsoft (Trojan:Win32/Malgent!MSR), Full List Of Detections (VirusTotal) |
| Detection Names (RILIDE) | Combo Cleaner (Trojan.GenericKD.66298139), ESET-NOD32 (JS/Spy.Agent.GC), Sophos (JS/Agent-BJVI), TrendMicro (Trojan.Win32.FRS.VSNW05D23), Full List Of Detections (VirusTotal) |
| Symptoms | Manipulated Internet browser settings. Extension(s) that you do not recall installing suddenly appeared on your browser. Decreased web browsing speed, unwanted ads and redirects. |
| Distribution Methods | Deceptive pop-up ads, free software installers (bundling), malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, browser tracking - privacy issues, possible additional malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Browser-targeting software examples
There is a variety of malicious content that targets browsers; it ranges from sophisticated data-stealing software to extensions that display unwanted advertisements. ChromeLoader is a notable example of malware designed to install malicious extensions onto browsers.
Adware-type browser extensions are quite popular; they operate by displaying ads on visited webpages and may also generate redirects and collect private data. Convert Page to PDF, One Click Refresh, and Image Viewer are just a few examples of this advertising-supported software.
Browser hijackers are likewise prevalent; these extensions make changes to browser settings in order to cause redirects to fake search engines. Browser-hijacking software typically targets sensitive information as well. Amazon Rain Forest - New Tab Search, Sticky Note Board Extension, and Drinking Well are a couple of our newest finds within this software category.
Keep in mind that regardless of how an unwanted/malicious extension or application operates – its presence on a system may endanger device integrity and user safety.
How did Chromium extension-loading shortcut virus install on my computer?
Malicious software is proliferated using phishing and social engineering techniques. It can be disguised as or bundled with ordinary content, likewise it could be promoted through fake advertising of various "useful" and "advantageous" functionalities. For example, Chromium extension-loading shortcut viruses have been noted being spread under the guise of TradingView Desktop.
The most widely used distribution methods include: drive-by (stealthy/deceptive) downloads, online scans, bundled installers, fake updaters, pirated software and illegal program activation ("cracking") tools, dubious download channels (e.g., freeware and third-party websites, Peer-to-Peer sharing networks, etc.), malicious attachments and links in spam emails/messages, and malvertising.
How to avoid installation of malicious software?
We highly recommend being vigilant while browsing since fraudulent and dangerous online content usually appears harmless. Incoming emails and other messages must be treated with caution, as they can contain virulent attachments/links.
Another recommendation is to download only from official and verified sources. We also advise activating and updating software by using legitimate functions/tools, as those obtained from third-parties may include malicious content.
We must emphasize the importance of having a reputable anti-virus installed and kept updated. Security programs must be used to run regular system scans and to remove detected threats/issues.
If your computer is already infected with Chromium extension-loading shortcut virus, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate this threat.
Screenshot of a Google Chrome shortcut modified by this virus:

Update 17 November 2023 - A sophisticated version of the Rilide Stealer extension, targeting Chromium-based browsers like Google Chrome, Microsoft Edge, Brave, and Opera, has emerged. This malware surpasses its predecessor with advanced features, including sending stolen data to a Telegram channel and interval-based screenshot captures.
Rilide's functionalities cover enabling/disabling extensions, retrieving browsing data, stealing login credentials, taking screenshots, and injecting malicious scripts. A notable update in this version involves adapting to the Chrome Extension Manifest V3, requiring a complete refactor, as initially identified by Trellix under the name 'CookieGenesis.'
The Commands & Control server issues diverse commands, encompassing extension management, system information retrieval, notifications creation, browser cookies and screenshots capture, URL information retrieval, browsing history acquisition, and proxy settings management.
Notably, the new 'screenshot_rules' command enables attackers to capture active tab screenshots at specified intervals based on predefined URL rules.
While the transition to Chrome Extension Manifest V3 poses challenges by restricting the loading of remote JavaScript code, Rilide's developers employ publicly disclosed techniques, leveraging inline events to execute malicious JavaScript code.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Chromium extension-loading shortcut virus?
- STEP 1. Uninstall unwanted applications using Control Panel.
- STEP 2. Remove malicious extensions from Google Chrome.
- STEP 3. Remove malicious plug-ins from Microsoft Edge.
Malicious software removal:
Windows 11 users:
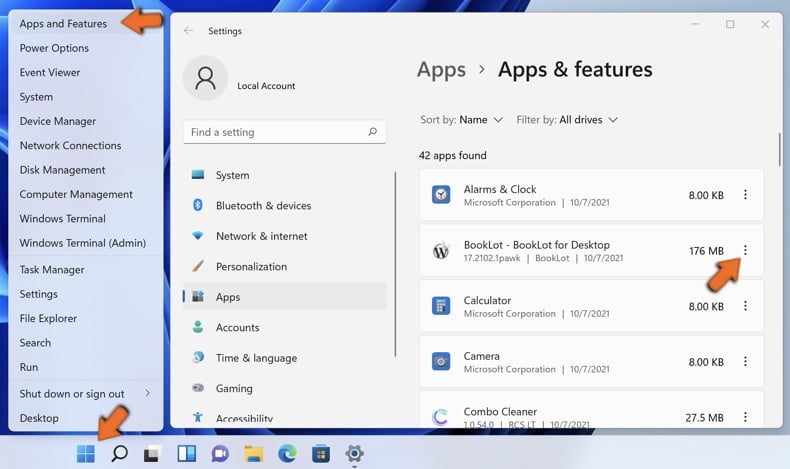
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
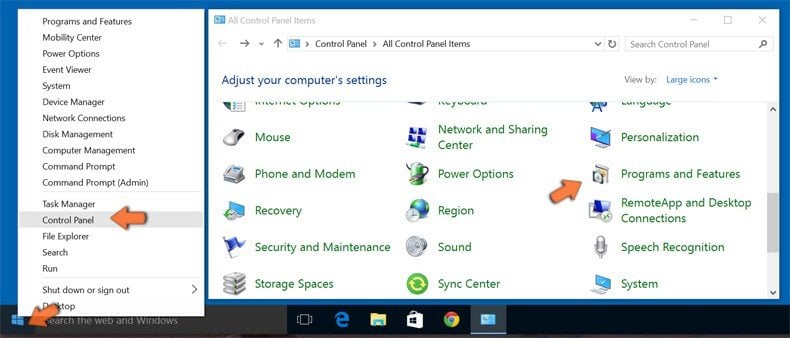
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.

In the uninstall programs window, look for any unwanted applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the unwanted applications, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove malicious extensions from Internet browsers:
Video showing how to remove potentially unwanted browser add-ons:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:

Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate any recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate any recently-installed suspicious extensions, select these entries and click "Remove".

Optional method:
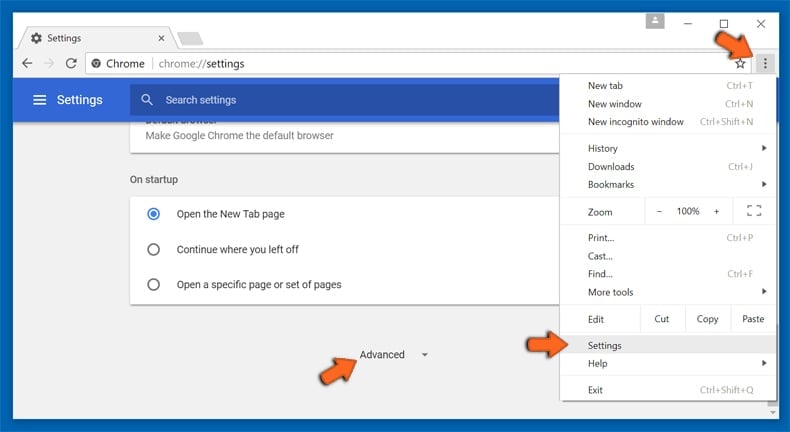
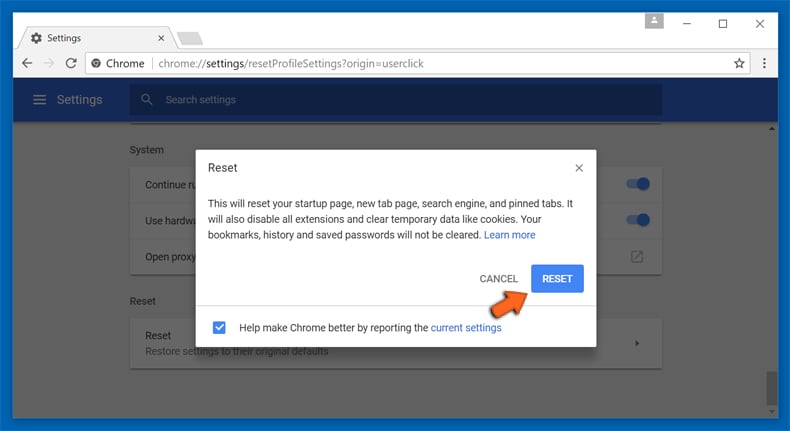
If you continue to have problems with removal of the chromium extension-loading shortcut malware, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
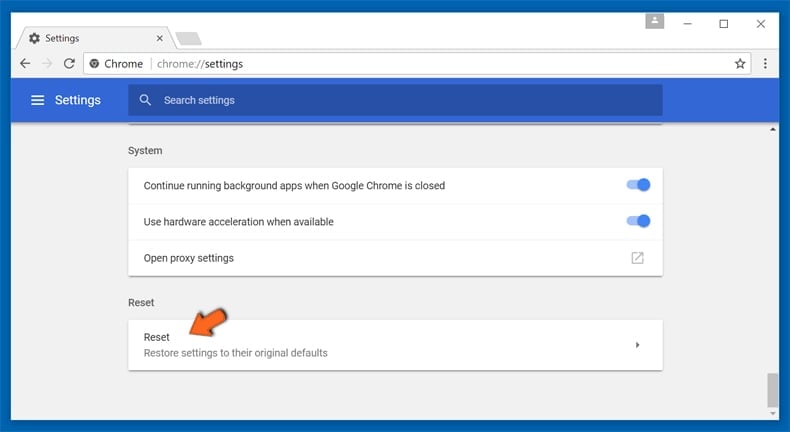
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
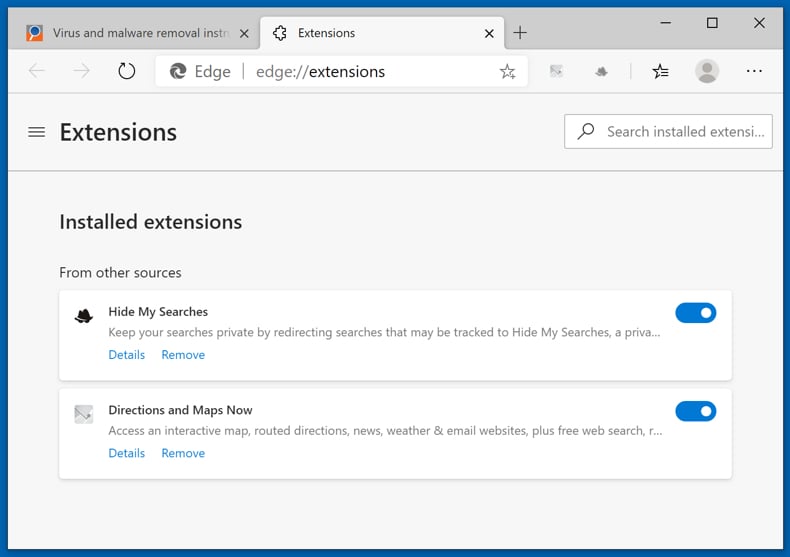
Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Extensions". Locate any recently-installed suspicious browser add-ons, and remove them.
(at the top right corner of Microsoft Edge), select "Extensions". Locate any recently-installed suspicious browser add-ons, and remove them.
Change your homepage and new tab settings:
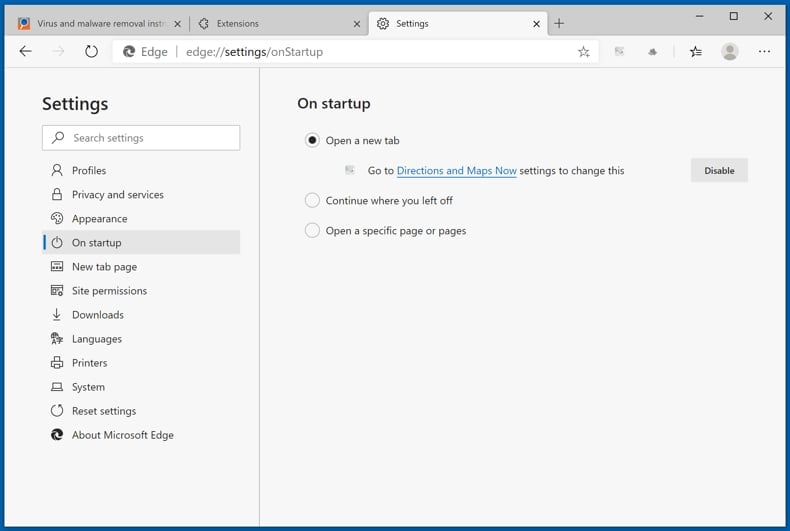
Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Settings". In the "On startup" section look for the name of the browser hijacker and click "Disable".
(at the top right corner of Microsoft Edge), select "Settings". In the "On startup" section look for the name of the browser hijacker and click "Disable".
Change your default Internet search engine:
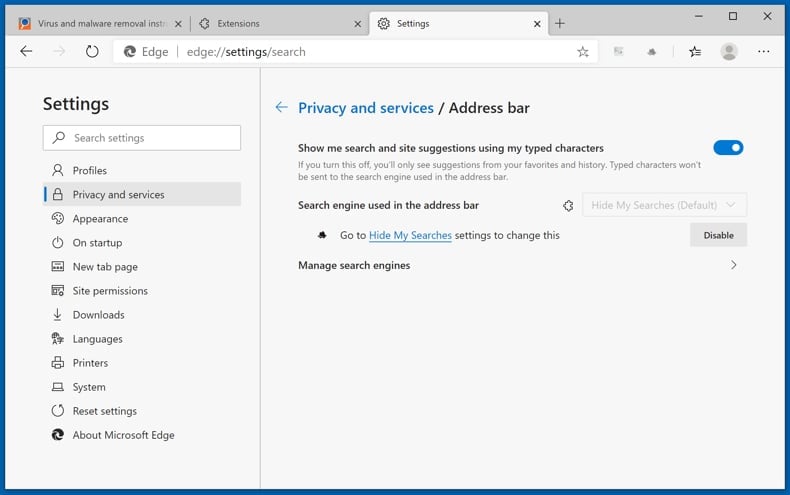
To change your default search engine in Microsoft Edge: Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge), select "Privacy and services", scroll to bottom of the page and select "Address bar". In the "Search engines used in address bar" section look for the name of the unwanted Internet search engine, when located click the "Disable" button near it. Alternatively you can click on "Manage search engines", in the opened menu look for unwanted Internet search engine. Click on the puzzle icon
(at the top right corner of Microsoft Edge), select "Privacy and services", scroll to bottom of the page and select "Address bar". In the "Search engines used in address bar" section look for the name of the unwanted Internet search engine, when located click the "Disable" button near it. Alternatively you can click on "Manage search engines", in the opened menu look for unwanted Internet search engine. Click on the puzzle icon ![]() near it and select "Disable".
near it and select "Disable".
Optional method:
If you continue to have problems with removal of the chromium extension-loading shortcut malware, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
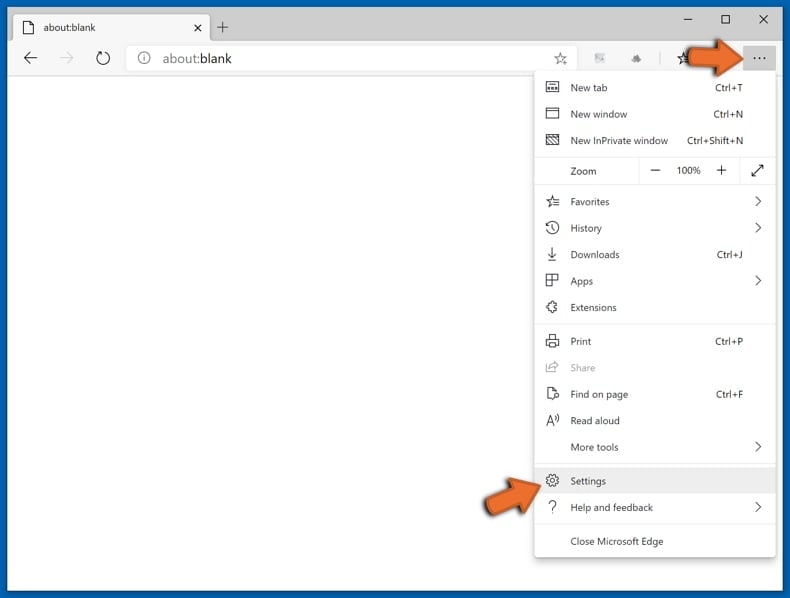
In the opened settings menu select Reset settings.
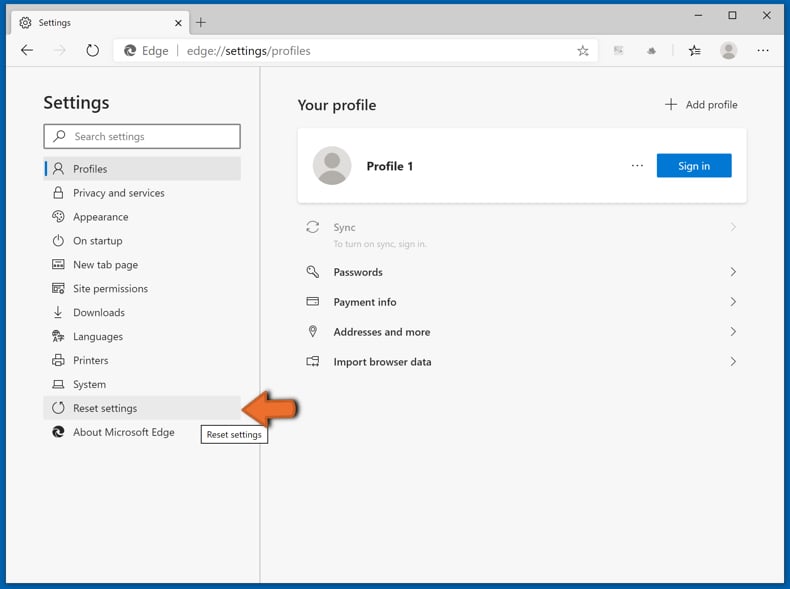
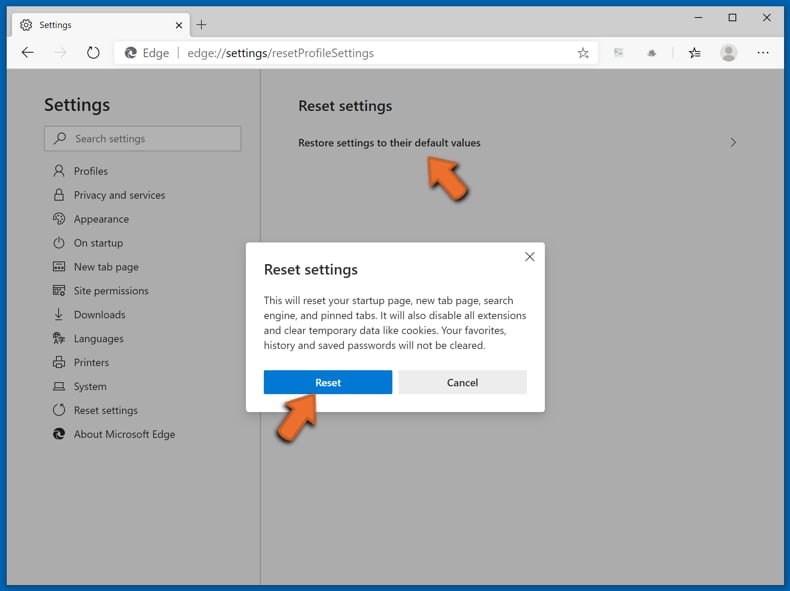
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
 A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
A browser hijacker is a type of adware infection that modifies Internet browser settings by assigning the homepage and default Internet search engine settings to some other (unwanted) website URL. Commonly, this type of adware infiltrates operating systems through free software downloads. If your download is managed by a download client, ensure that you decline offers to install advertised toolbars or applications that seek to change your homepage and default Internet search engine settings.
Post a comment:
If you have additional information on chromium extension-loading shortcut malware or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
What is Chromium extension-loading shortcut virus?
Chromium extension-loading shortcut virus is an infection targeting Chromium-based browsers. The virus replaces the browser's shortcut (LNK) files with ones modified to open the legitimate browser that is already loaded with malicious extensions. The extensions can have a broad range of functionalities ranging from data theft to the display of malicious ads.
What are the biggest issues that Chromium extension-loading shortcut virus can cause?
The threats posed by a piece of malicious software depend on its abilities and the cyber criminals' goals. As mentioned in the previous answer, the Chromium extension-loading shortcut virus can infect browsers with various malicious extensions. This type of infection has been observed being used to proliferate extensions that steal finance-related account log-in credentials (i.e., usernames/passwords). Generally, high-risk infections can lead to serious privacy issues, financial losses, and identity theft.
How did Chromium extension-loading shortcut virus infiltrate my computer?
Malicious software is primarily spread through drive-by downloads, online scams, spam emails/messages, untrustworthy download sources (e.g., freeware and free file-hosting sites, P2P sharing networks, etc.), pirated software and illegal activation tools ("cracks"), bundled installers, fake updaters, and malvertising.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is designed to detect and remove various threats. It is capable of eliminating malicious browser extensions and practically all known malware infections. It must be stressed that since highly sophisticated malware usually hides deep within systems – performing a full system scan is paramount.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion