Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is NodeStealer?
NodeStealer is a type of malware written in JavaScript and executed through Node.js. It is used by threat actors to steal browser cookies and login credentials, enabling them to hijack Gmail, Facebook, Outlook, and possibly other accounts. The malware was initially discovered in late January of 2023.

More about NodeStealer
Upon execution, the malware ensures its continuous operation even after the victim restarts their machine by establishing persistence. In order to achieve this, the malware leverages the auto-launch module on Node.js.
The primary objective of NodeStealer malware is to obtain stored passwords and session information from Chromium-based browsers installed on the victim's machine. The malware is designed to target several browsers, including Chrome, Opera, Microsoft Edge, and Brave.
If NodeStealer malware detects cookies or credentials related to Facebook accounts, it utilizes the Facebook API to extract information about the compromised account (to gather information related to advertising accounts). This information is then used by threat actors to run unauthorized ads using the victim's advertising accounts.
Once the NodeStealer malware successfully acquires the stored browser information and completes the Facebook account surveillance, it proceeds to extract all the stolen data to a command-and-control (C2) server operated by the attacker.
| Name | NodeStealer data stealer |
| Threat Type | Information stealer |
| Detection Names | Avast (Win64:Evo-gen [Trj]), Combo Cleaner (Trojan.Spy.YWG), Emsisoft (Trojan.Spy.YWG (B)), Kaspersky (Trojan-PSW.Win64.Fobo.gf), Sophos (Mal/Generic-S), Full List (VirusTotal) |
| Symptoms | Inability to access various accounts, including Facebook, Gmail, and Outlook |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, monetary loss, and more |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Possible damage
Victims of NodeStealer can experience various problems, including unauthorized access to their Facebook, Gmail, and Outlook accounts, hijacked advertising accounts, and the theft of their stored browser information. These can lead to financial losses, identity theft, and damage to personal and professional reputations.
How did NodeStealer infiltrate my computer?
Cybercriminals can distribute NodeStealer malware through various tactics, such as phishing emails, social engineering techniques, malvertising, or by bundling it with legitimate software. One known tactic is to disguise NodeStealer as a harmless document, such as a PDF or XLSX file, with an appropriate corresponding icon and filename that can trick users into opening it.
Threat actors may also use social engineering techniques to persuade users to click links or download attachments that contain the malware. Additionally, they may create fake websites or social media profiles that offer fake software updates or free downloads, which, when clicked, lead to the download and installation of the NodeStealer malware.
How to avoid installation of malware?
Be cautious when dealing with email attachments or links received from unfamiliar or suspicious email addresses, especially if the email is unexpected or irrelevant. Keep your operating system, software, and plugins up-to-date. Use antivirus software and make sure it is always updated.
Avoid downloading applications from untrustworthy sources such as Peer-to-Peer networks, suspicious websites, or third-party downloaders. Download software from official websites and app stores. Do not trust ads, pop-ups, or links on questionable websites.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Update 3 August 2023 - Recently, a new campaign has surfaced, distributing two Python-written NodeStealer variants with additional functionalities. Cybercriminals have enhanced these variants with the ability to steal cryptocurrency, act as downloaders, and perform other malicious activities besides stealing Facebook accounts.
The NodeStealer variant, designed to download more malware, is set up to fetch two .zip files. Once these files are downloaded and extracted, NodeStealer establishes persistence for BitRAT, hVNC RAT, and XWorm.
This variant is also capable of stealing MetaMask credentials from Chrome, Cốc Cốc, and Brave browsers. MetaMask is an extension that helps users access Ethereum Wallets through their browsers. By stealing these credentials, the attackers can take cryptocurrency from hijacked wallets without permission.
Another variant also focuses on attacking Facebook business accounts and MetaMask wallets. However, this version has additional abilities, including stealing emails and using anti-analysis measures. It possesses the capability to analyze and read the victim's emails. This function may have been added to interfere with Facebook notifications that could alert the victim about the modifications made by the NodeStealer.
Also, the malware's creator included a basic function to look for specific malware analysis tools and virtual machine processes on the victim's system. If any of these tools are found running, the malware automatically shuts itself down to avoid being detected and analyzed.
Update January 9, 2025 – an updated variant of NodeStealer has been discovered being distributed through phishing campaigns. Sophisticated techniques have been introduced into the program, including DLL side-loading. This version was found in a campaign targeting Malaysia's education sector.
The infection originated from spam emails written in Bahasa Melayu. One of the letter themes was a copyright infringement notice that lured recipients into following a link to download a PDF document.
However, the malicious file installed NodeStealer instead. Part of the chain was a seemingly legitimate PDF reader, which was exploited to load the malware onto the system (DLL side-loading). There is evidence linking this campaign to a Vietnamese threat actor.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is NodeStealer?
- STEP 1. Manual removal of NodeStealer malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
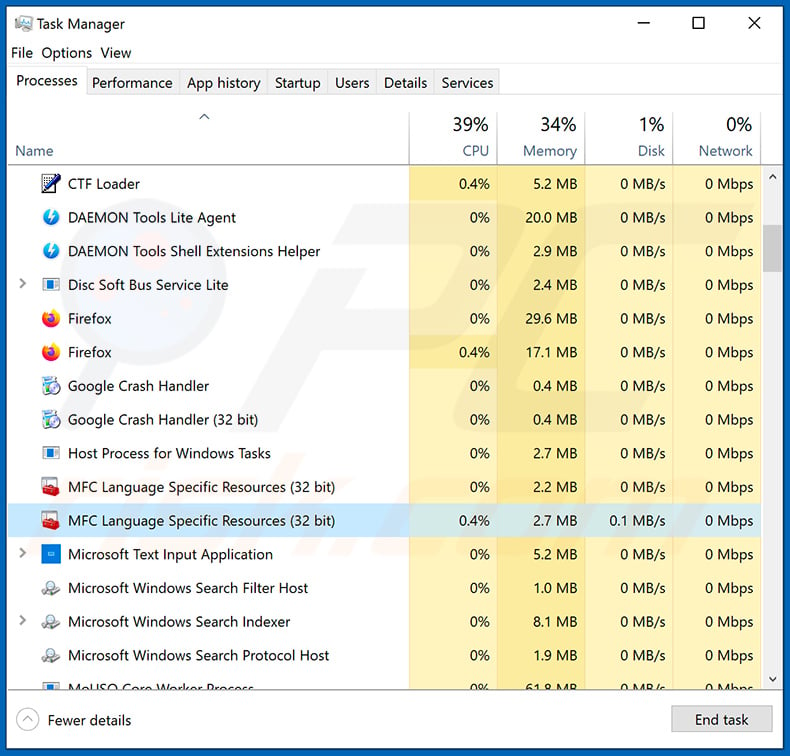
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
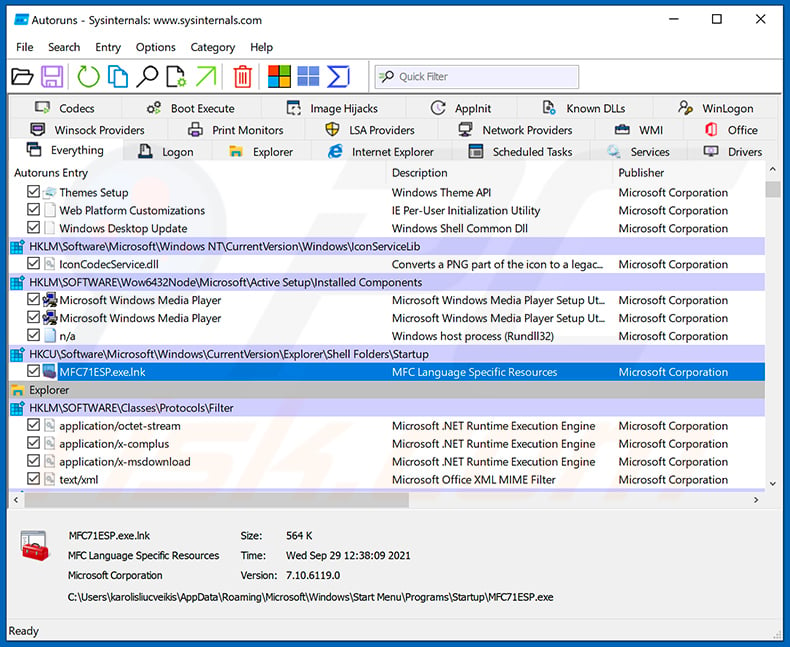
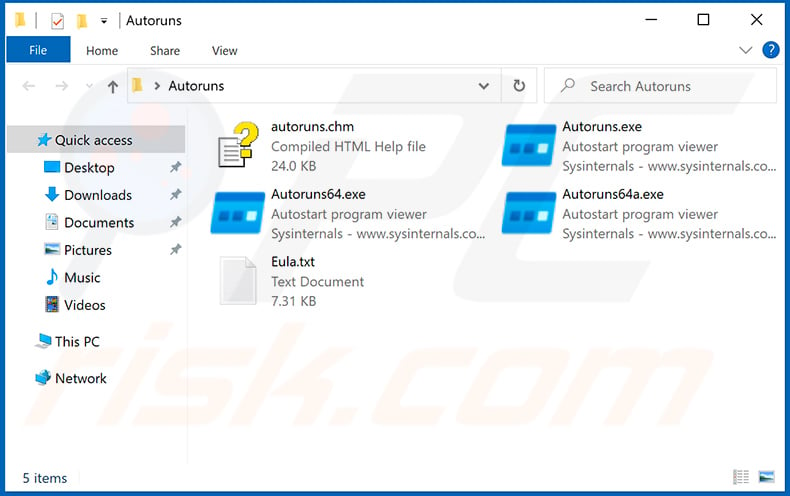
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
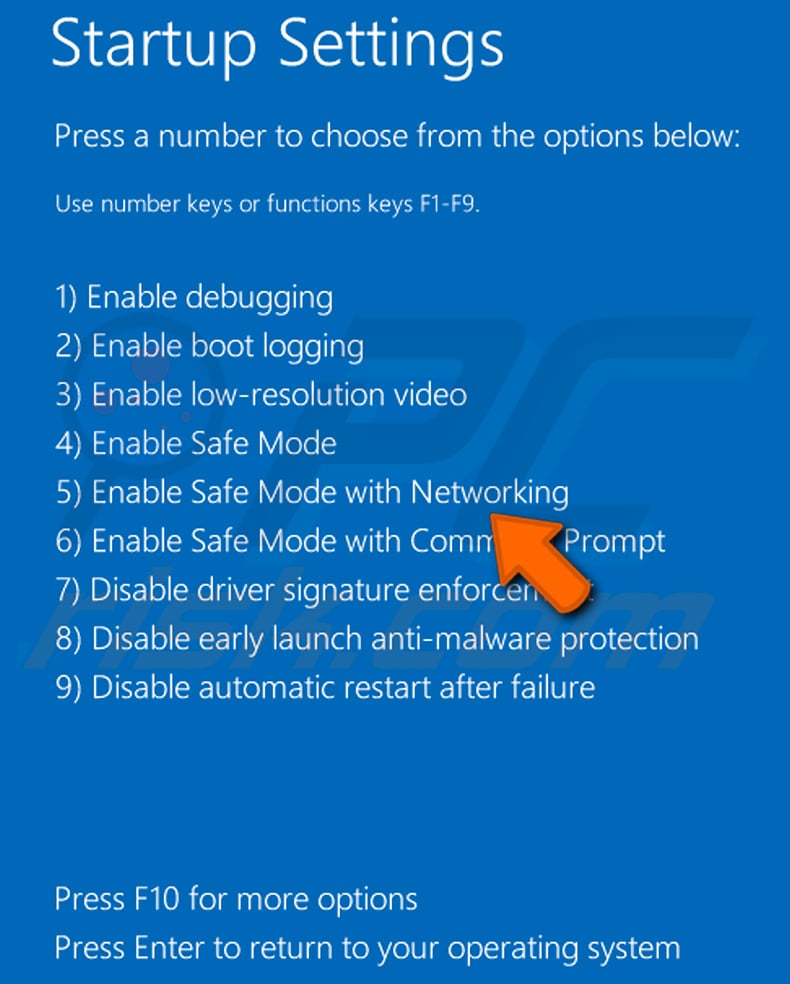
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
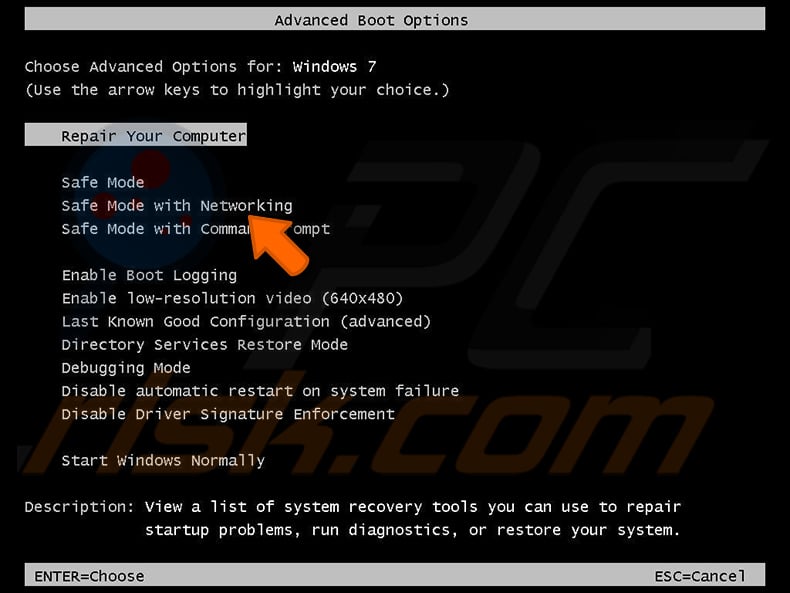
Video showing how to start Windows 7 in "Safe Mode with Networking":
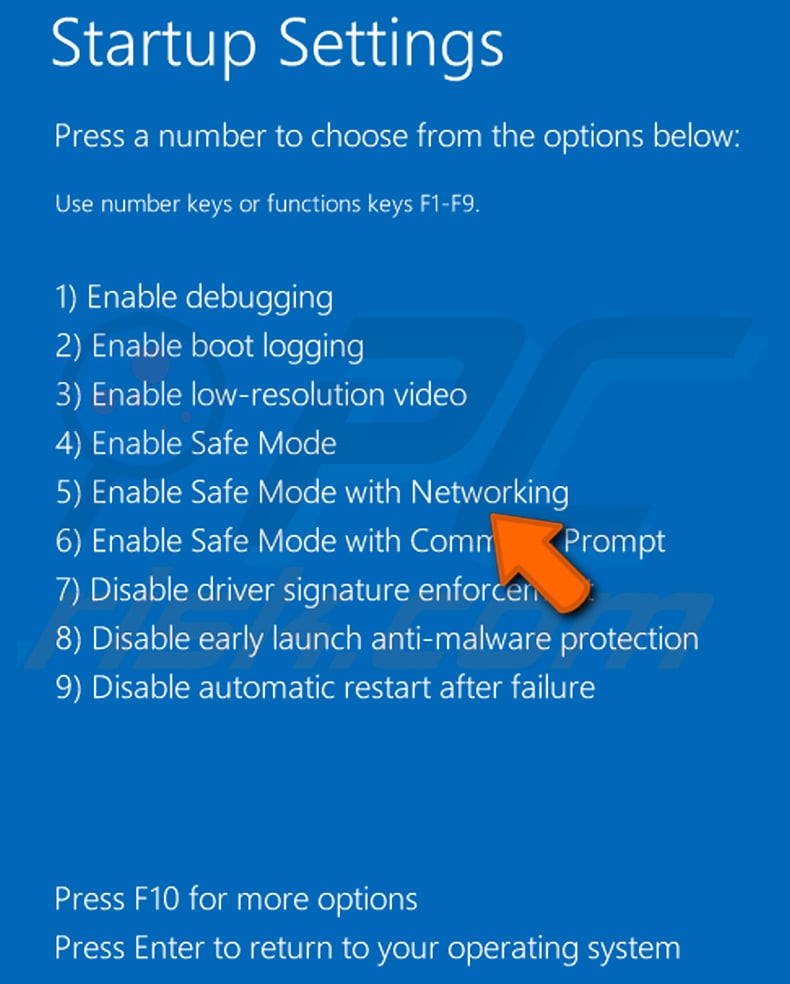
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
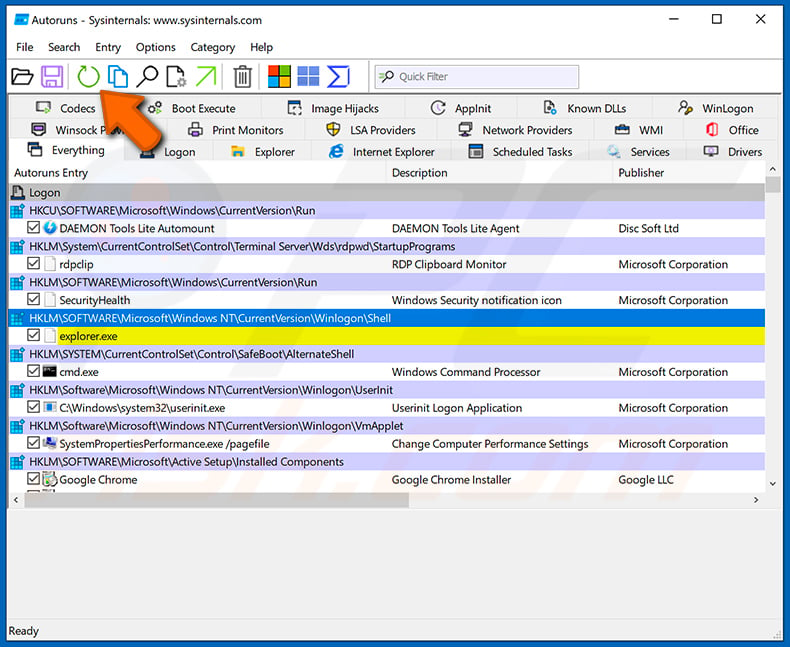
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
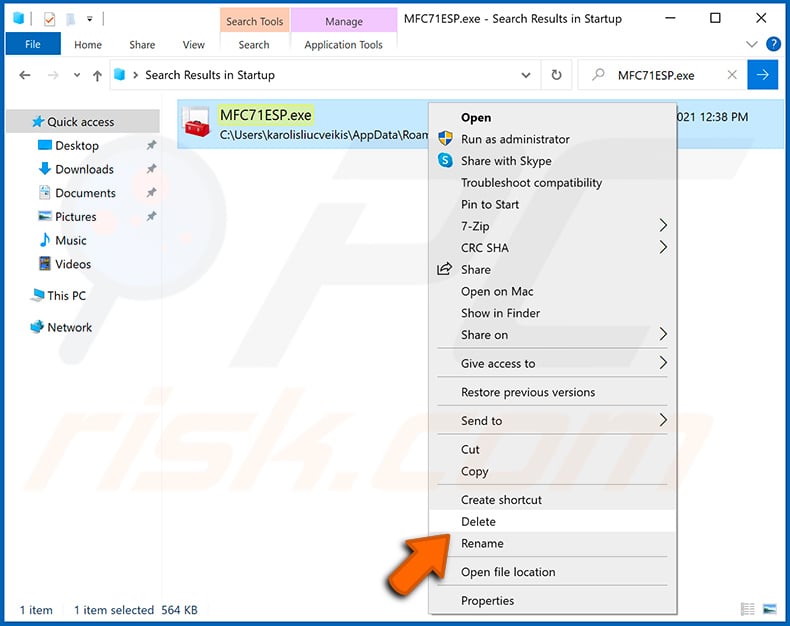
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
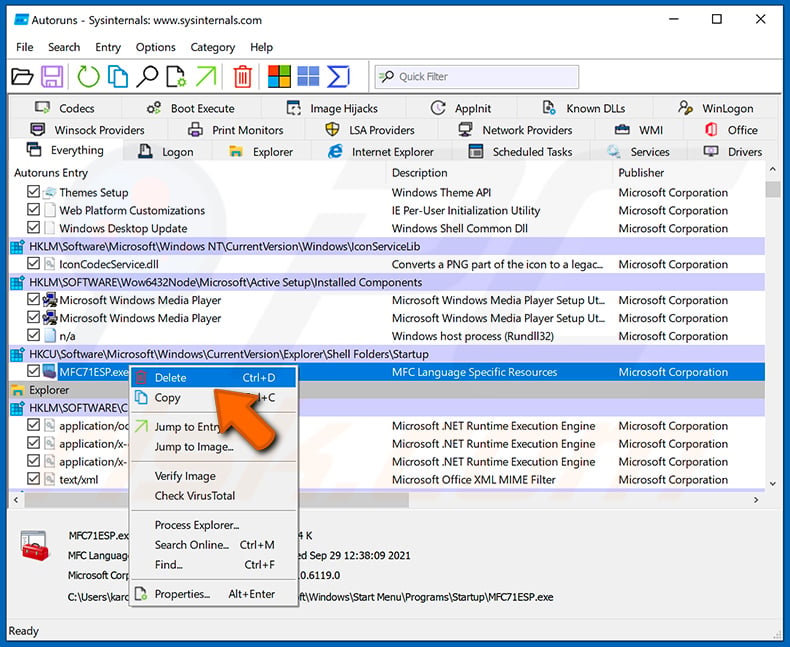
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with NodeStealer malware, should I format my storage device to get rid of it?
Formatting your storage device may remove the NodeStealer malware but also delete all your data. Instead of formatting, you can try to use an anti-malware program to remove the NodeStealer malware.
What are the biggest issues that malware can cause?
The impact of malware can vary depending on its type and capabilities. It may result in identity theft, financial losses, reduced computer performance, increased susceptibility to additional infections, and other issues.
What is the purpose of NodeStealer malware?
The purpose of NodeStealer malware is to steal stored password and cookie session information from Chromium-based browsers on the target's computer, including Chrome, Opera, Microsoft Edge, and Brave browsers. The stolen information is then used by threat actors to hijack social media, email, and advertising accounts and run unauthorized ads.
How did NodeStealer malware infiltrate my computer?
NodeStealer malware can be distributed through various tactics by cybercriminals, including phishing emails, social engineering techniques, malvertising, or bundling it with legitimate software. One common tactic is to disguise the malware as a harmless document, such as a PDF or XLSX file, with an appropriate icon and filename that can deceive users into opening it.
Will Combo Cleaner protect me from malware?
Combo Cleaner has the ability to detect and remove almost all known malware infections. However, it is important to note that some high-end malware may hide deep in the system, making it difficult to detect and remove. It is recommended to run a full system scan to ensure thorough detection and removal of any malicious software.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion