Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is LookupConsole?
The LookupConsole app is part of the AdLoad adware family. Typically, adware-type applications feed users with various advertisements and often gather information. As well as operating as adware, LookupConsole is a browser hijacker - this app promotes the address of a fake search engine by changing browser settings.
In most cases, users download and install adware unintentionally. For these reasons these apps are classified as potentially unwanted applications (PUAs). Research shows that apps from the AdLoad family are distributed through fake Adobe Flash Player installers.

Adware displays ads in the form of banners, coupons, pop-ups, surveys, and so on. These often conceal underlying content of visited websites and, if clicked, open untrusted web pages or cause download/installation of unwanted applications by executing certain scripts.
In addition, LookupConsole changes browser settings. Typically, apps that promote fake search engines change settings such as the address of the default search engine, homepage, and new tab - they prevent users from changing them as long as the rogue programs are installed.
Note that fake search engines generate misleading results. Furthermore, it is likely that LookupConsole will collect data such as, for example, addresses of visited pages, entered search queries, geolocations, IP addresses and other details of this kind.
Some adware-type apps can access confidential information that the developers misuse in various ways, or simply sell it to third parties. In most cases, people download and install these apps inadvertently. This particular app is distributed through a fake Adobe Flash Player installer which installs LookupConsole, rather than the official Adobe Flash Player.
Commonly, these installers are used to distribute various PUAs, however, in some cases, they infect systems with malware including ransomware, Trojan-type programs, etc.
| Name | Ads by LookupConsole |
| Threat Type | Adware, Mac malware, Mac virus. |
| Detection Names | Avast (MacOS:Adload-AD [Trj]), AVG (MacOS:Adload-AD [Trj]), ESET-NOD32 (A Variant Of OSX/TrojanDownloader.Adload.AE), Kaspersky (Not-a-virus:HEUR:AdWare.OSX.Cimpli.k), Full List (VirusTotal) |
| Symptoms | Your Mac becomes slower than normal, you see unwanted pop-up ads, you are redirected to dubious websites. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake Flash Player installers, torrent file downloads. |
| Damage | Internet browser tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites, loss of private information. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
DataQuest, LookupModule and ProcessSign are just some apps also categorized as adware. Developers promote these apps as supposedly delivering various features or are useful in other ways, however, most adware-type application promote fake search engines and gather browsing-related details. They do not operate as advertised and simply cause problems.
How did LookupConsole install on my computer?
Research shows that LookupConsole can be installed through a fake installer, which supposedly installs Adobe Flash Player, however, this is not the only way that adware and other PUAs are spread.
PUAs are often included into the download or installation set-ups as additional offers, however, these are usually hidden in "Custom", "Advanced" and other settings of the set-ups. Distribution of unwanted apps through the set-ups of other programs is known "bundling".
Developers often use this technique to trick users into downloading and installing unwanted software together with other, regular software that they wish to download and install. People allow unwanted apps to be downloaded and installed by leaving settings that are available in the set-ups unchanged.
Additionally, unwanted downloads and installations can be caused by clicking deceptive advertisements that run certain scripts.
How to avoid installation of potentially unwanted applications
Do not download or install software through dubious websites, Peer-to-Peer networks (e.g., torrent clients, eMule), third party downloaders, installers or other similar channels. These are often monetized by promoting dubious apps. They can also be used to distribute malware.
Software should be downloaded from official websites and through direct links. Check all download and installation setups for "Custom", "Advanced" and other settings. Dismiss offers to download or install potentially unwanted applications before finishing the process.
It is not safe to click ads that are displayed on dubious web pages - they can run scripts to download or install unwanted apps. They can also open untrusted websites. Remove any unwanted apps (extensions, plug-ins, add-ons) installed on the browser immediately.
Also remove programs of this kind that are installed on the operating system. If your computer is already infected with LookupConsole, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate this adware.
Files related to DataQuest adware that need to be removed:
- ~/Library/Application Support/com.LookupConsole/LookupConsole
- ~/Library/Application Support/com.LookupConsoleDaemon/LookupConsole
- ~/Library/LaunchAgents/com.LookupConsole.plist
- ~/Library/LaunchDaemons/com.LookupConsoleDaemon.plist
IMPORTANT NOTE! Rogue setups/apps that promote the LookupConsole adware are designed to create a new device profile. Therefore, before taking any further removal steps, perform these actions:
1) Click the "Preferences" icon in the menu bar and select "Profiles"

2) Select the "LookupConsole" profile and delete it.

3) Perform a full system scan with Combo Cleaner anti-virus suite.
After performing these actions, you can proceed with further removal steps for this adware.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is LookupConsole?
- STEP 1. Remove LookupConsole related files and folders from OSX.
- STEP 2. Remove LookupConsole ads from Safari.
- STEP 3. Remove LookupConsole adware from Google Chrome.
- STEP 4. Remove LookupConsole ads from Mozilla Firefox.
Video showing how to remove adware and browser hijackers from a Mac computer:
LookupConsole adware removal:
Remove LookupConsole-related potentially unwanted applications from your "Applications" folder:

Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX", "NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware-related files and folders
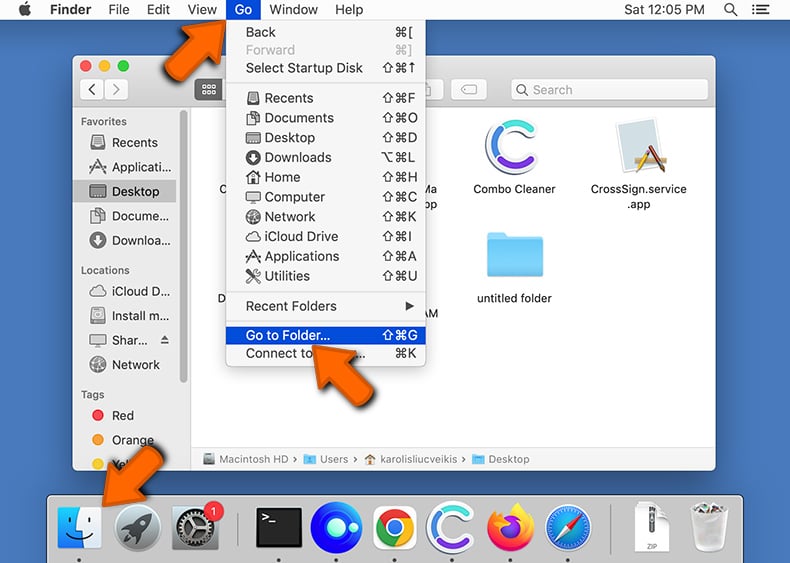
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
 Check for adware generated files in the /Library/LaunchAgents/ folder:
Check for adware generated files in the /Library/LaunchAgents/ folder:
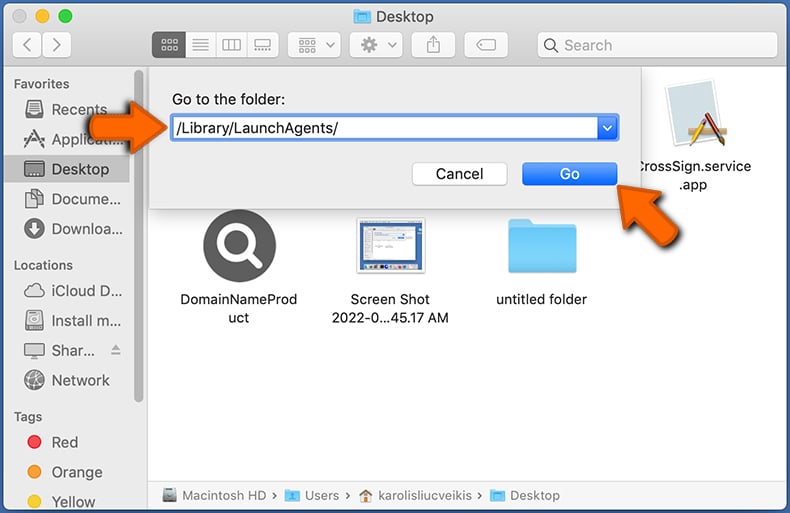
In the Go to Folder... bar, type: /Library/LaunchAgents/
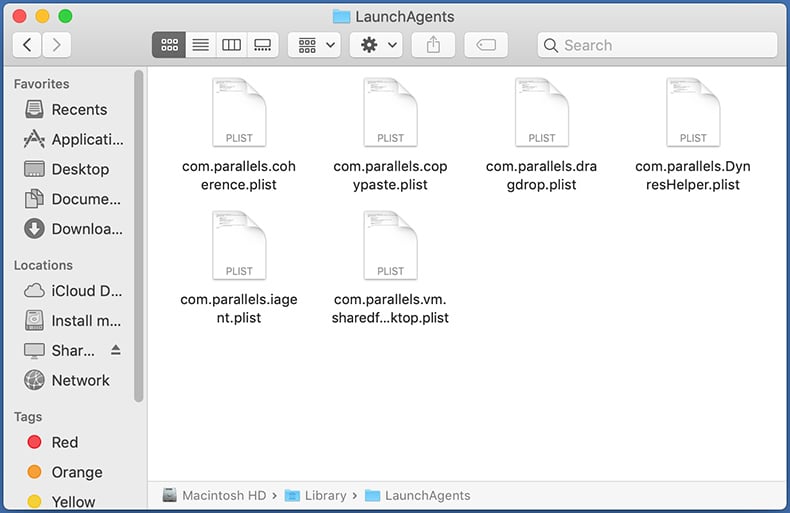
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the ~/Library/Application Support/ folder:
Check for adware generated files in the ~/Library/Application Support/ folder:
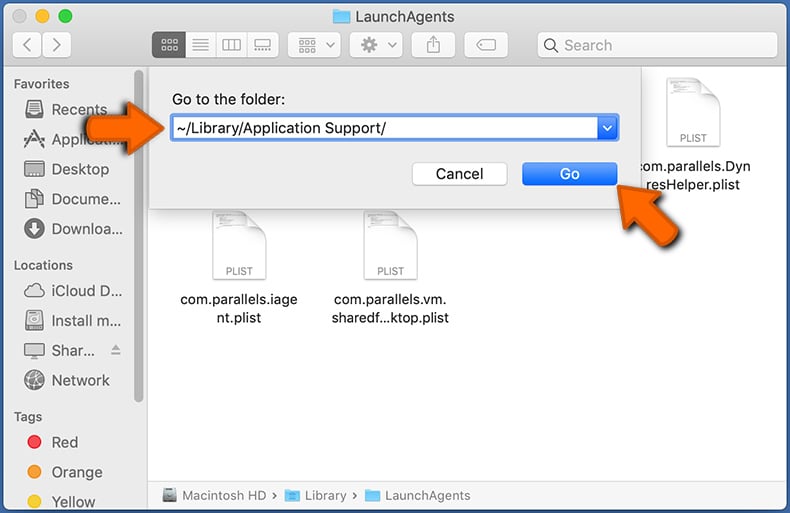
In the Go to Folder... bar, type: ~/Library/Application Support/
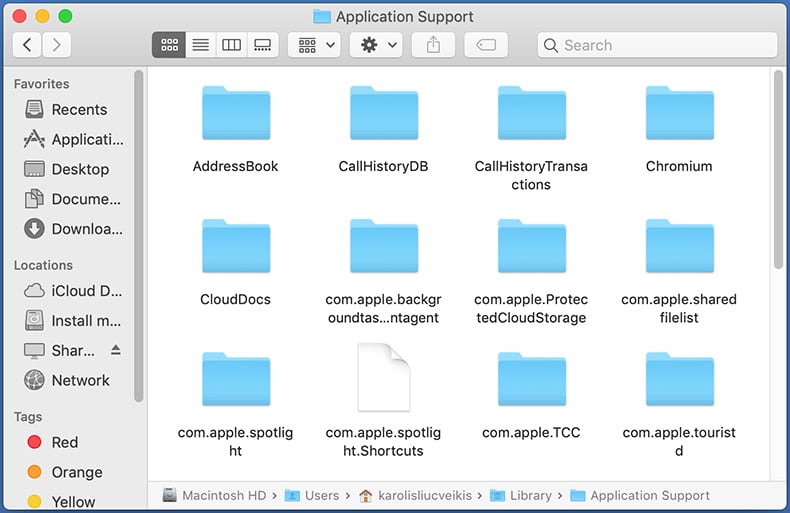
In the "Application Support" folder, look for any recently-added suspicious folders. For example, "MplayerX" or "NicePlayer", and move these folders to the Trash.
 Check for adware generated files in the ~/Library/LaunchAgents/ folder:
Check for adware generated files in the ~/Library/LaunchAgents/ folder:
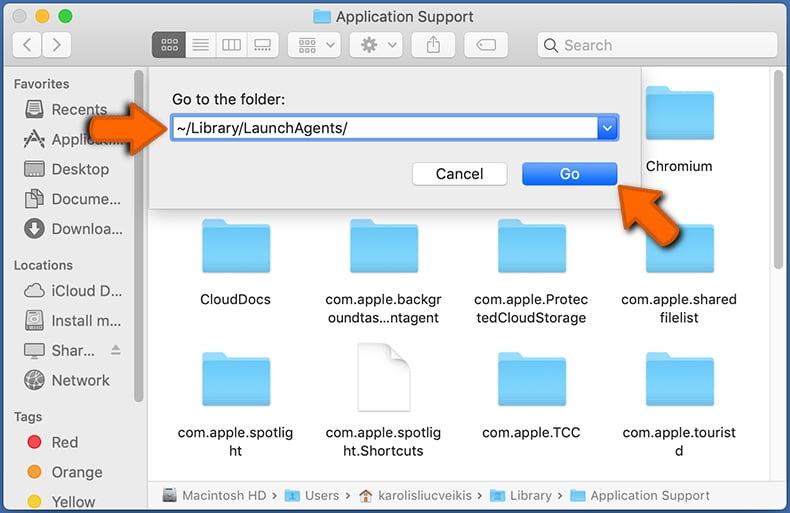
In the Go to Folder... bar, type: ~/Library/LaunchAgents/
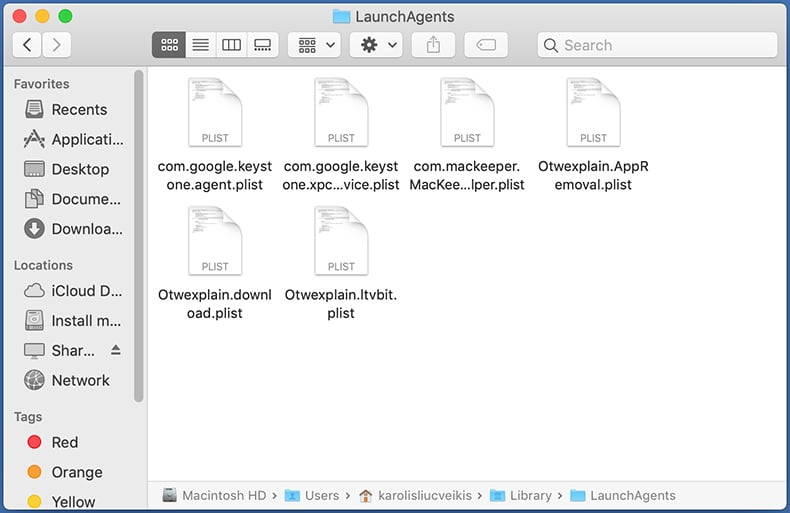
In the "LaunchAgents" folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - "installmac.AppRemoval.plist", "myppes.download.plist", "mykotlerino.ltvbit.plist", "kuklorest.update.plist", etc. Adware commonly installs several files with the exact same string.
 Check for adware generated files in the /Library/LaunchDaemons/ folder:
Check for adware generated files in the /Library/LaunchDaemons/ folder:
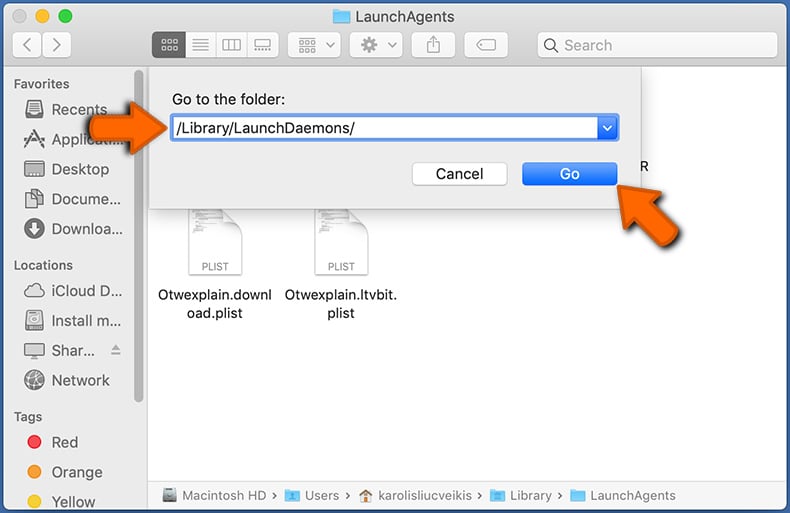
In the "Go to Folder..." bar, type: /Library/LaunchDaemons/
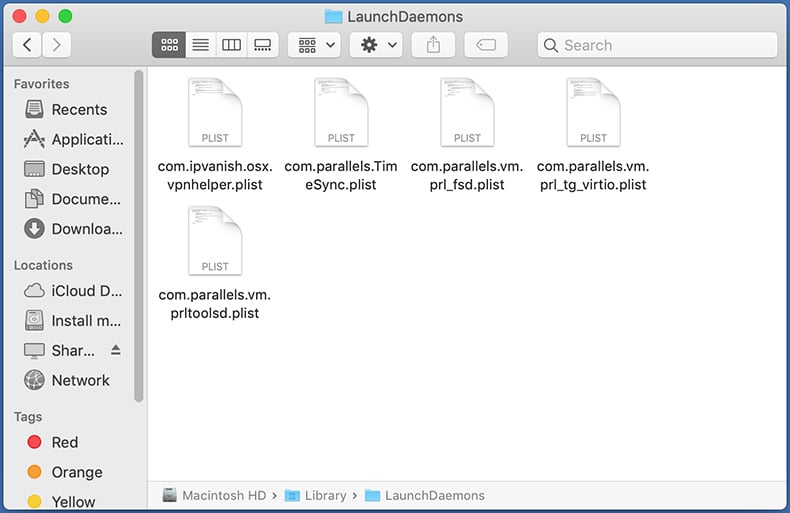
In the "LaunchDaemons" folder, look for recently-added suspicious files. For example "com.aoudad.net-preferences.plist", "com.myppes.net-preferences.plist", "com.kuklorest.net-preferences.plist", "com.avickUpd.plist", etc., and move them to the Trash.
 Scan your Mac with Combo Cleaner:
Scan your Mac with Combo Cleaner:
If you have followed all the steps correctly, your Mac should be clean of infections. To ensure your system is not infected, run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file, double click combocleaner.dmg installer. In the opened window, drag and drop the Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates its virus definition database and click the "Start Combo Scan" button.
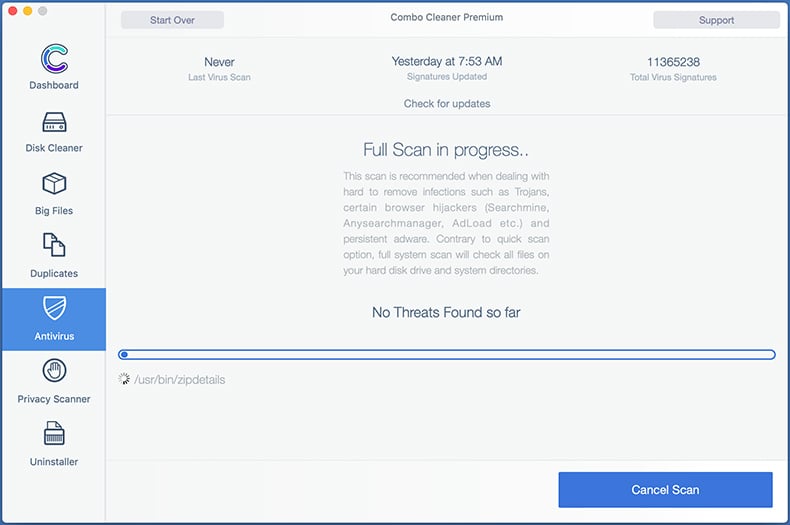
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays "no threats found" - this means that you can continue with the removal guide; otherwise, it's recommended to remove any found infections before continuing.
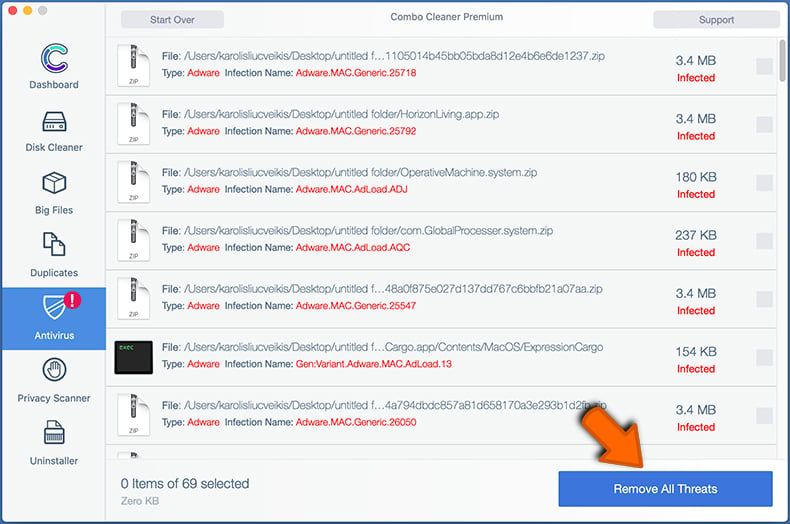
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
Remove malicious extensions from Internet browsers
 Remove malicious Safari extensions:
Remove malicious Safari extensions:
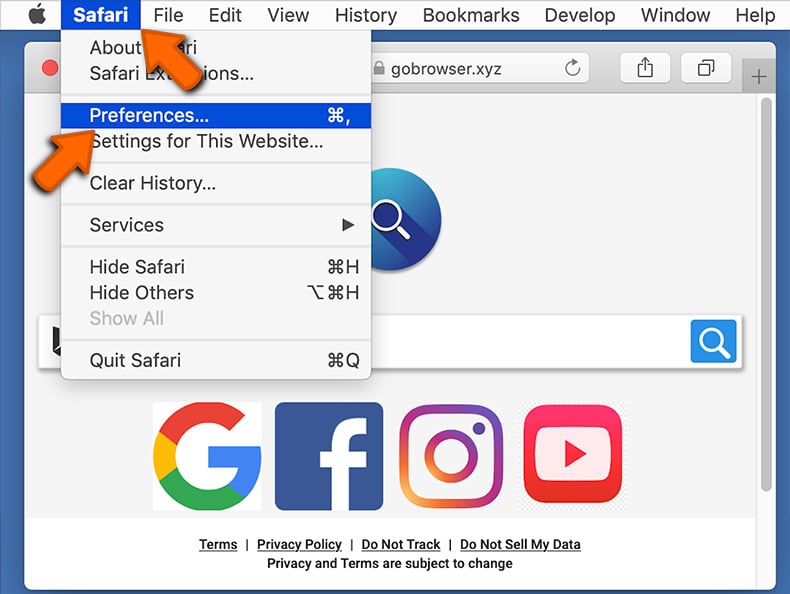
Open the Safari browser, from the menu bar, select "Safari" and click "Preferences...".
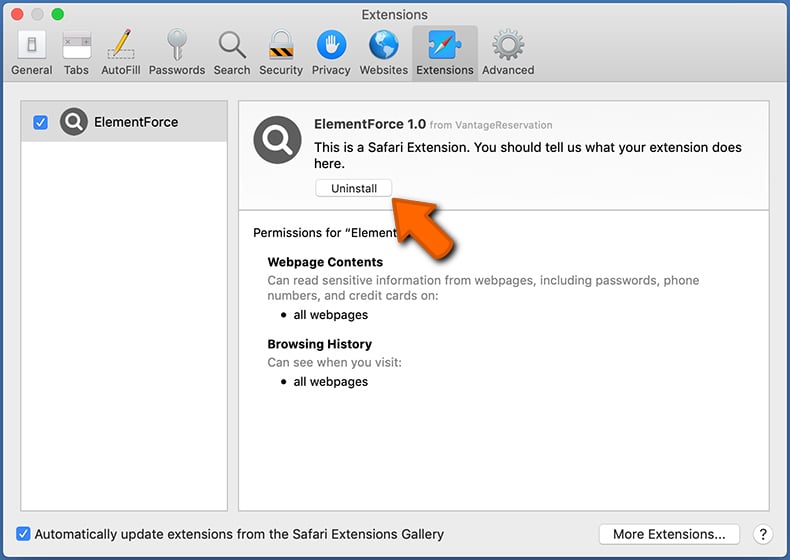
In the preferences window, select "Extensions" and look for any recently-installed suspicious extensions. When located, click the "Uninstall" button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for regular browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
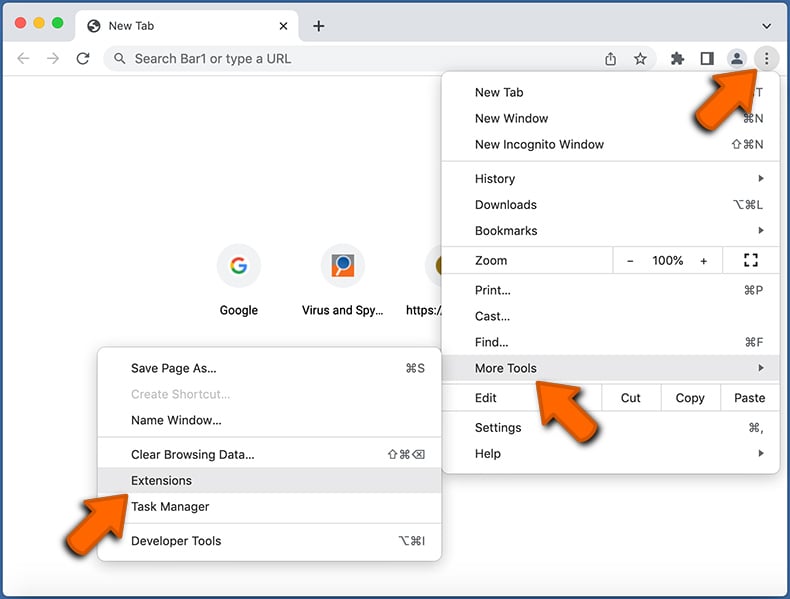
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More Tools" and click "Extensions". Locate all recently-installed suspicious extensions, select these entries and click "Remove".
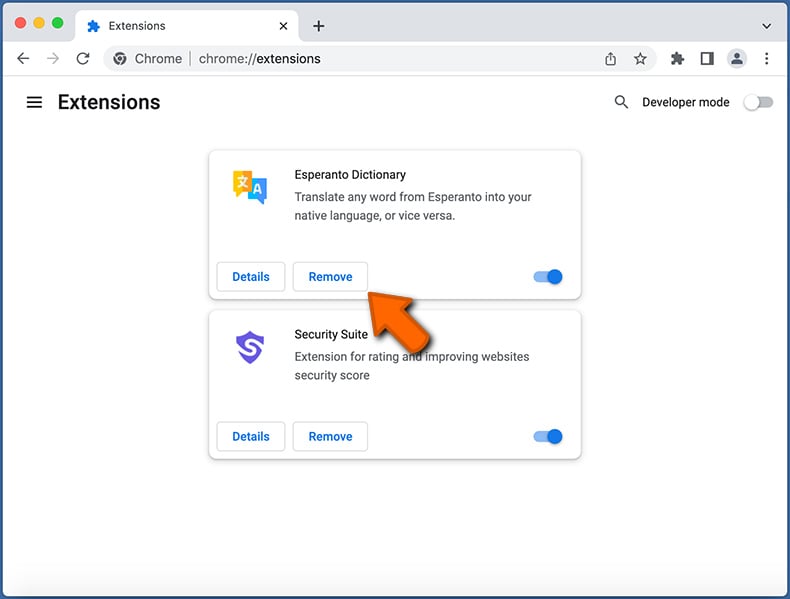
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
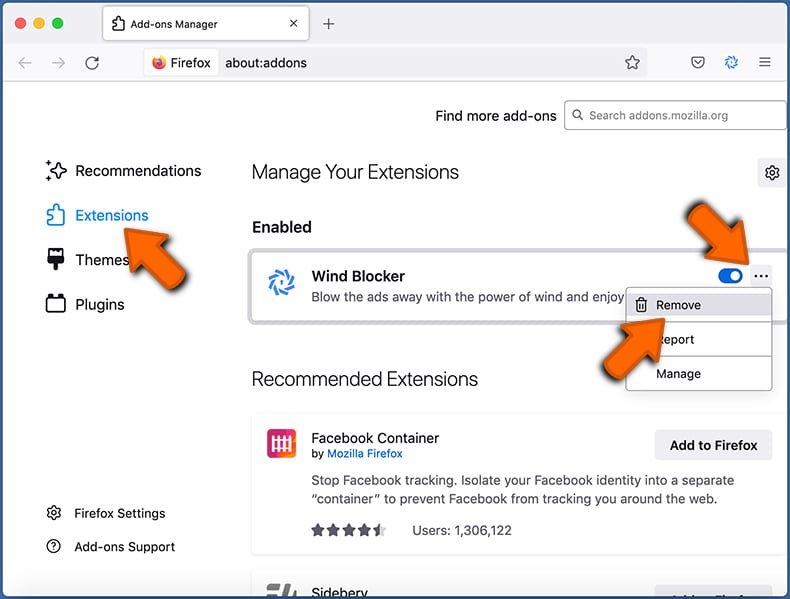
 Remove malicious extensions from Mozilla Firefox:
Remove malicious extensions from Mozilla Firefox:
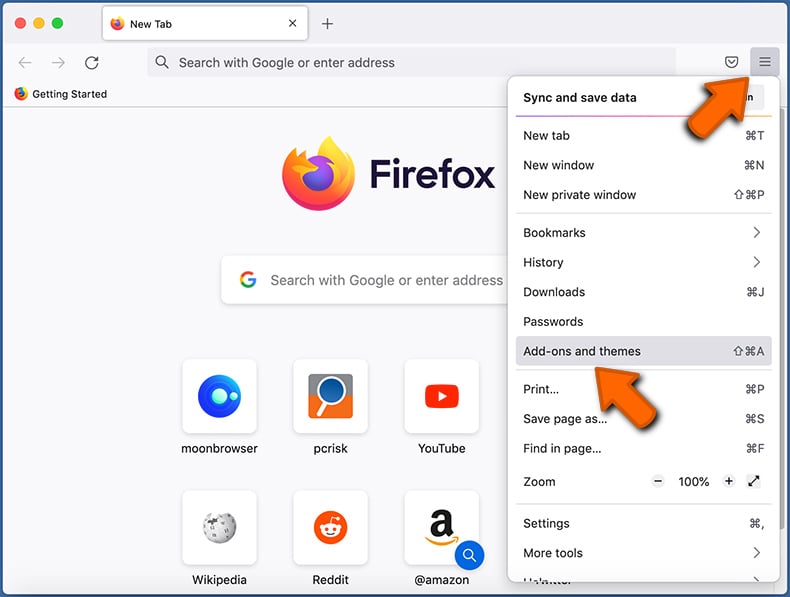
Click the Firefox menu ![]() (at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window) and select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion