How to stop redirects to and from essaemiaaut.com
Notification SpamAlso Known As: essaemiaaut.com pop-up
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is essaemiaaut[.]com?
Similar to newsredirect.net, giantttraffic.com, ewaglongoo.com, and thousands of others, essaemiaaut[.]com is a rogue website. It operates by presenting dubious content and/or redirects visitors to other untrustworthy web pages.
Most users enter these sites unintentionally when they are redirected by intrusive ads or Potentially Unwanted Applications (PUAs) already infiltrated into the system. These apps do not need explicit user permission to be installed onto devices. PUAs generate redirects, run intrusive ad campaigns, and record browsing-related information.
![essaemiaaut[.]com pop-up redirects](/images/stories/screenshots201909/essaemiaautcom-homepage.gif)
Once accessed, essaemiaaut[.]com first checks visitors' IP addresses to learn their geolocations. This is key in determining the site's further course of action. Depending on their geolocations, users are redirected elsewhere and/or are presented with highly dubious content.
This web page also uses browser notifications, the consent option to which it hides beneath 'clickbait' ("Please click the ALLOW to stream"). If users are tricked into granting consent to these notifications, it allows essaemiaaut[.]com to begin running intrusive ad campaigns.
Advertisements of this kind (e.g. pop-ups, banners, coupons, surveys, etc.) are more than a nuisance, they are also a risk to system health and user safety. When clicked, they redirect to sale-oriented, untrustworthy, compromised, deceptive/scam and malicious websites.
Some ads can be triggered to execute scripts designed to stealthily download/install PUAs. As mentioned, unwanted applications force-open similarly harmful pages and can run intrusive ad campaigns. They implement various tools to enable third party graphical content to be displayed on any site.
Hence, delivering ads that significantly diminish the browsing experience and carry the aforementioned risks, however, by far the most dangerous capability that PUAs possess is data tracking. By monitoring users' browsing activity (URLs visited, search queries typed, etc.), they collect personal information (IP addresses, geolocations and other details).
This private data can then be shared with third parties (potentially, cyber criminals) seeking to misuse it for profit.
Therefore, PUAs can cause browser/system infiltration and infections, and lead to serious privacy issues, financial loss and identity theft. To protect device integrity and user safety, remove all dubious applications and browser extensions/plug-ins immediately upon detection.
| Name | essaemiaaut.com pop-up |
| Threat Type | Push notifications ads, Unwanted ads, Pop-up ads. |
| Detection Names | Full List Of Detections (VirusTotal) |
| Serving IP Address | 104.18.6.101 |
| Observed Domains | z0rv.essaemiaaut[.]com; slo8.essaemiaaut[.]com; bpsk.essaemiaaut[.]com; k12o.essaemiaaut[.]com; wf32.essaemiaaut[.]com; ort3.essaemiaaut[.]com |
| Symptoms | Seeing advertisements not originating from the sites you are browsing. Intrusive pop-up ads. Decreased Internet browsing speed. |
| Distribution Methods | Deceptive pop-up ads, potentially unwanted applications (adware) |
| Damage | Decreased computer performance, browser tracking - privacy issues, possible additional malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
PUAs appear legitimate and entice users to install with offers of "useful" and "beneficial" functions, however, the only purpose of these apps is to generate revenue for their developers. Therefore, the advertised features are usually nonoperational, which makes unwanted applications useless to users.
Rather than delivering any real value, PUAs cause redirects to untrustworthy and malicious sites, deliver intrusive ads and gather sensitive information.
How did adware install on my computer?
PUAs often infiltrate systems is via the download/install setups of other programs. This deceptive marketing tactic of packing ordinary software with unwanted or malicious content is called "bundling".
Rushing download and installation processes (e.g. ignoring terms, using pre-set options, skipping steps and sections, etc.) increases the risk of potential infiltration and infections. Once clicked, intrusive advertisements can execute scripts to download/install PUAs without users' consent.
How to avoid installation of potentially unwanted applications
Research all content to verify its legitimacy, before downloading/installing. Use only official and verified download channels. Do not use P2P sharing networks (BitTorrent, Gnutella, eMule, etc.), free file-hosting sites, third party downloaders, or similar sources - they are untrusted.
Treat download/Installation processes with caution. Therefore, it is important to read the terms, study all available options, use the "Custom/Advanced" settings and decline downloading/installing additional apps, tools, functions and so on.
Intrusive advertisements rarely seem suspicious, however, they redirect to dubious web pages (e.g. gambling, pornography, adult-dating and others). If you encounter such ads/redirects, inspect the device and remove all suspect applications and/or browser extensions/plug-ins without delay.
If your computer is already infected with rogue applications, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is essaemiaaut.com pop-up?
- STEP 1. Remove spam notifications from Google Chrome
- STEP 2. Remove spam notifications from Google Chrome (Android)
- STEP 3. Remove spam notifications from Mozilla Firefox
- STEP 4. Remove spam notifications from Microsoft Edge
- STEP 5. Remove spam notifications from Safari (macOS)
Disable unwanted browser notifications:
Video showing how to disable web browser notifications:
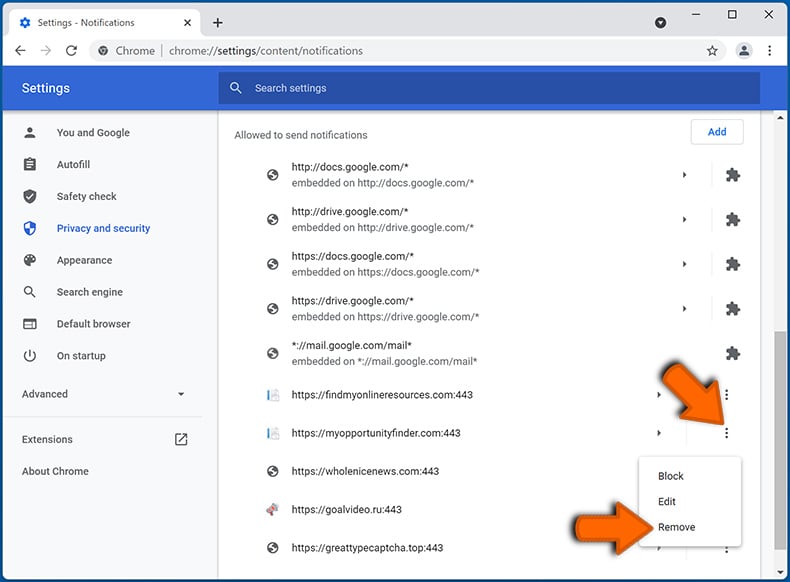
 Remove spam notifications from Google Chrome:
Remove spam notifications from Google Chrome:
Click the Menu button (three dots) on the right upper corner of the screen and select "Settings". In the opened window select "Privacy and security", then click on "Site Settings" and choose "Notifications".
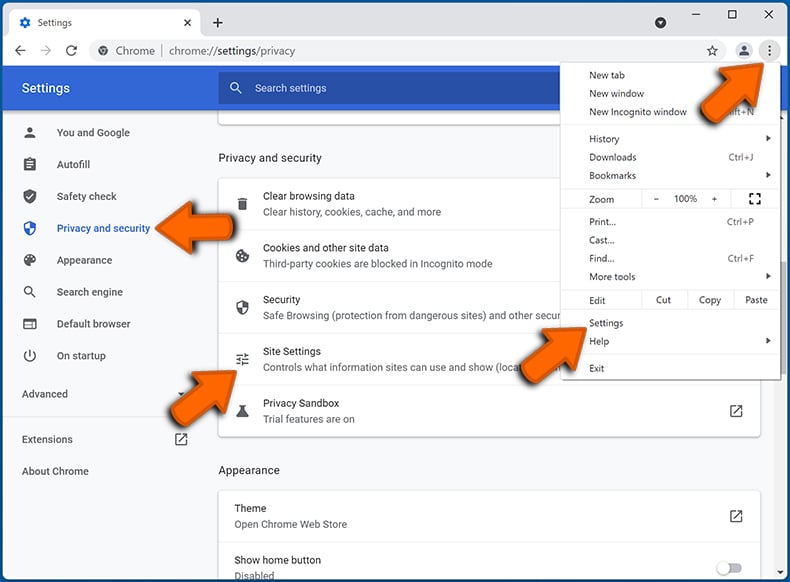
In the "Allowed to send notifications" list search for websites that you want to stop receiving notifications from. Click on the three dots icon near the website URL and click "Block" or "Remove" (if you click "Remove" and visit the malicious site once more, it will ask to enable notifications again).
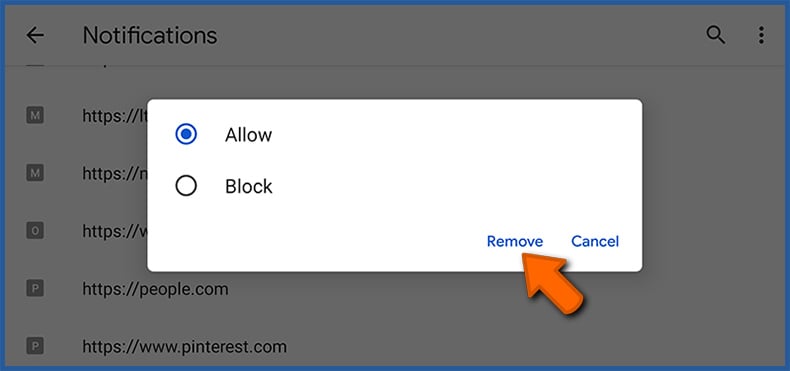
 Remove spam notifications from Google Chrome (Android):
Remove spam notifications from Google Chrome (Android):
Tap the Menu button (three dots) on the right upper corner of the screen and select "Settings". Scroll down, tap on "Site settings" and then "Notifications".
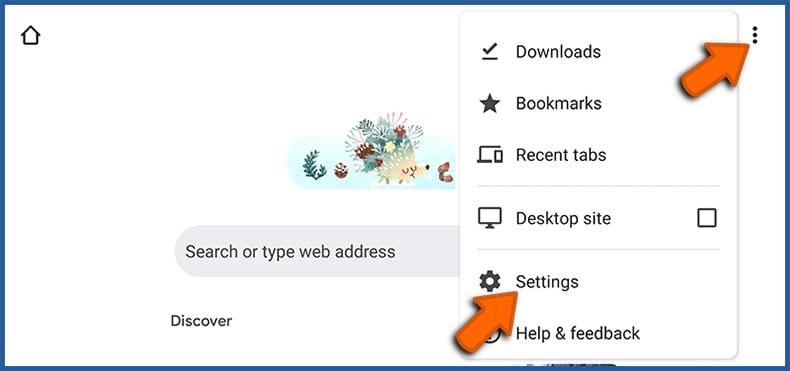
In the opened window, locate all suspicious URLs and tap on them one-by-one. Once the pop-up shows up, select either "Block" or "Remove" (if you tap "Remove" and visit the malicious site once more, it will ask to enable notifications again).
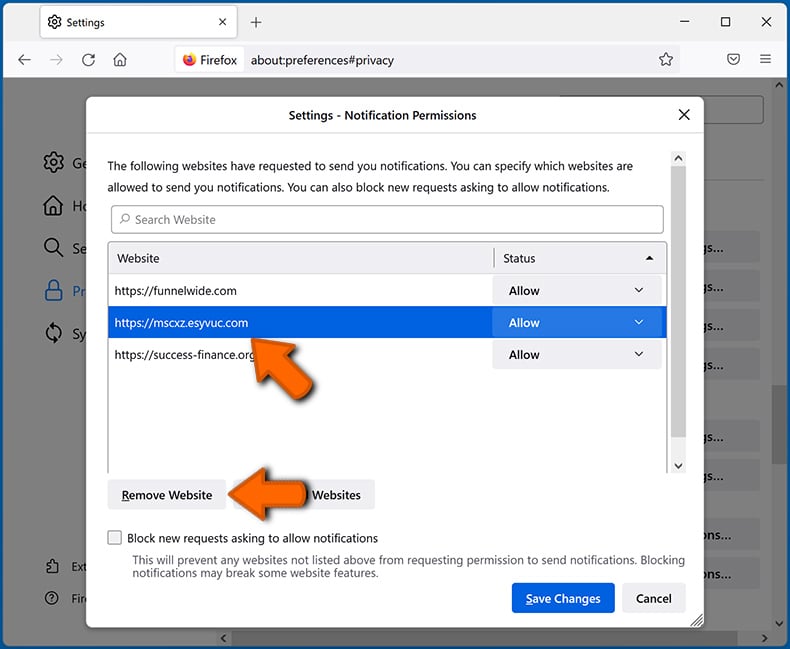
 Remove spam notifications from Mozilla Firefox:
Remove spam notifications from Mozilla Firefox:
Click the Menu button (three bars) on the right upper corner of the screen. Select "Settings" and click on "Privacy & Security" in the toolbar on the left hand side of the screen. Scroll down to the "Permissions" section and click the "Settings" button next to "Notifications".
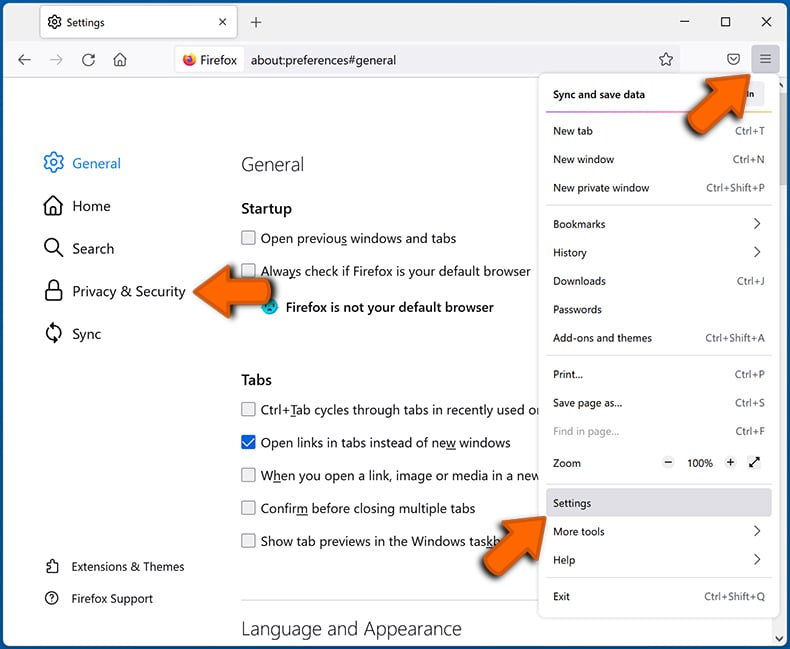
In the opened window, locate all suspicious URLs and block them using the drop-down menu or either remove them by clicking "Remove Website" at the bottom of the window (if you click "Remove Website" and visit the malicious site once more, it will ask to enable notifications again).
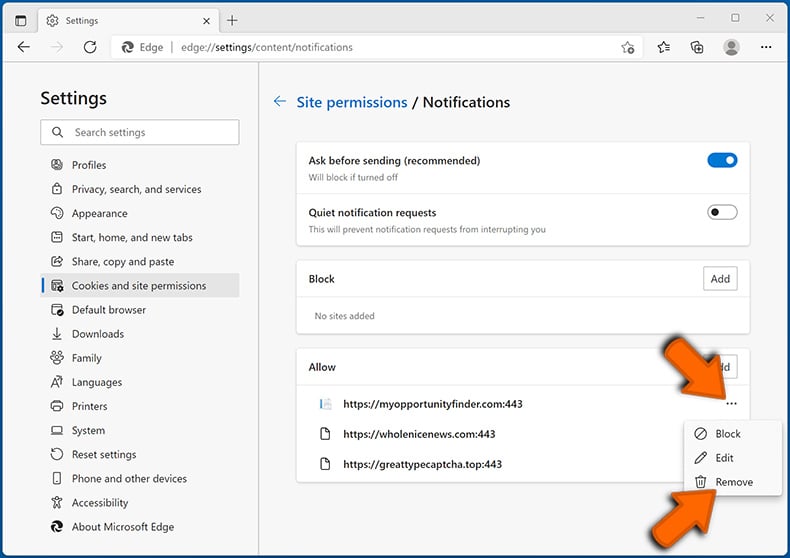
 Remove spam notifications from Microsoft Edge:
Remove spam notifications from Microsoft Edge:
Click the menu button (three dots) on the right upper corner of the Edge window and select "Settings". Click on "Cookies and site permissions" in the toolbar on the left hand side of the screen and select "Notifications".
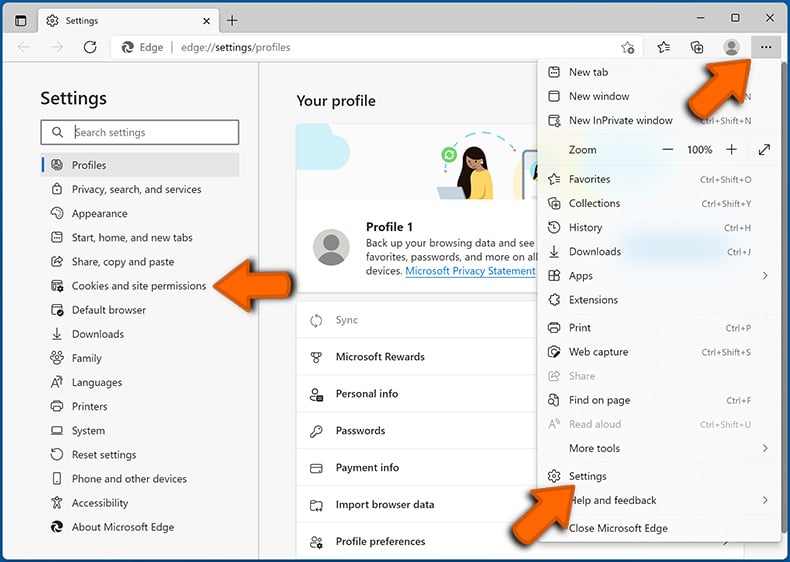
Click three dots on the right hand side of each suspicious URL under "Allow" section and click "Block" or "Remove" (if you click "Remove" and visit the malicious site once more, it will ask to enable notifications again).
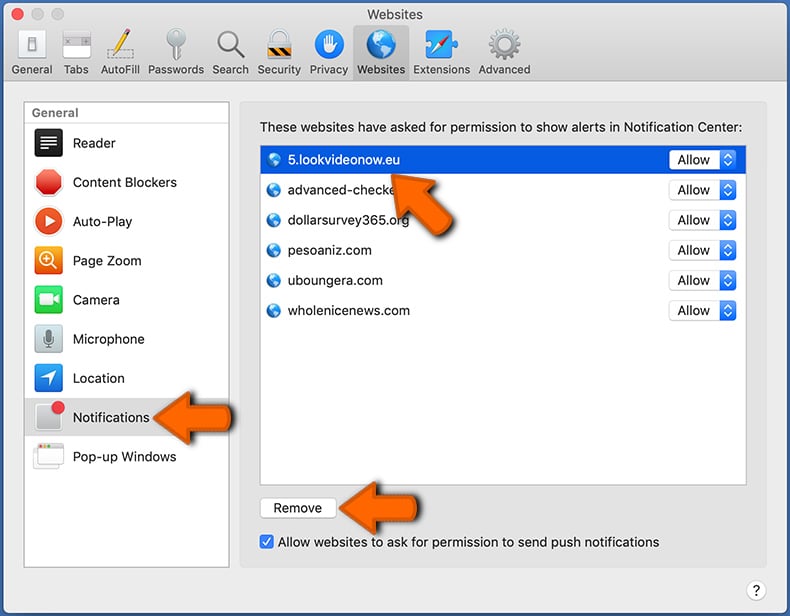
 Remove spam notifications from Safari (macOS):
Remove spam notifications from Safari (macOS):
Click "Safari" button on the left upper corner of the screen and select "Preferences...". Select the "Websites" tab and then select "Notifications" section on the left pane.
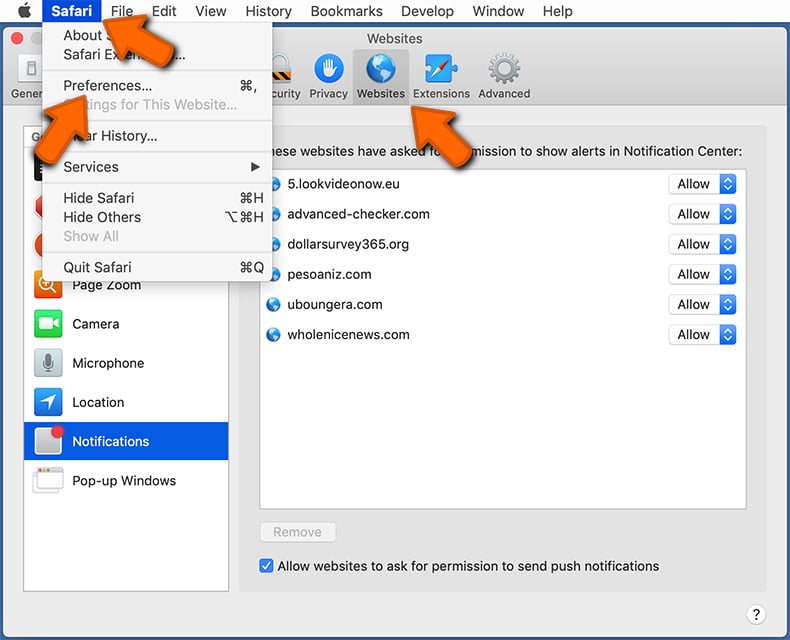
Check for suspicious URLs and apply the "Deny" option using the drop-down menu or either remove them by clicking "Remove" at the bottom of the window (if you click "Remove" and visit the malicious site once more, it will ask to enable notifications again)
How to avoid browser notification spam?
Internet users should be very skeptical when being asked to allow notifications. While this is a useful feature that allows you to receive timely news from websites you like, deceptive marketers frequently abuse it.
Only allow notifications from websites that you fully trust. For added security - use an anti-malware application with a real-time web browsing monitor to block shady websites that tries to trick you into allowing spam notifications. We recommend using Combo Cleaner Antivirus for Windows.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion