Eliminate redirects to and from sinentoldrewhap.pro
Notification SpamAlso Known As: sinentoldrewhap.pro pop-up
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is sinentoldrewhap[.]pro?
sinentoldrewhap[.]pro is very similar to redtext[.]biz, ciessimple[.]pro, storynnews[.]com and many other rogue sites that redirect visitors to untrustworthy, potentially malicious websites or display dubious content.
In most cases, people visit sinentoldrewhap[.]pro inadvertently, since they are redirected by potentially unwanted applications (PUAs) or through clicked intrusive advertisements. Generally, people download and install these apps by accident. After installation, they cause redirects to dubious web pages, collect sensitive browsing data, and feed users with intrusive ads.
![sinentoldrewhap[.]pro pop-up redirects](/images/stories/screenshots201904/sinentoldrewhap-homepage.jpg)
After installation, a PUA continually forces the browser to open sinentoldrewhap[.]pro in a new tab or window. Users are then redirected to other (about two or three) untrustworthy websites, or they are shown dubious content. Some of the sites opened through sinentoldrewhap[.]pro might contain malicious content. As mentioned, PUAs can also display intrusive ads.
These conceal underlying content of visited websites and, if clicked, redirect users to other dubious sites. Some might be designed to run scripts that download/install other potentially unwanted apps. Furthermore, PUAs collect browsing-related information such as entered search queries, URLs of opened websites, IP addresses, geolocations, and so on.
They might also gather personal details. The developers generate revenue by sharing the information with third parties (potentially, cyber criminals) who misuse it to generate revenue. Therefore, uninstall all PUAs immediately.
| Name | sinentoldrewhap.pro pop-up |
| Threat Type | Push notifications ads, Unwanted ads, Pop-up ads |
| Detection Names | Full List Of Detections (VirusTotal) |
| Serving IP Address | 104.27.174.202 |
| Observed Domains | d6yx.sinentoldrewhap[.]pro, lxsn.sinentoldrewhap[.]pro, c25f.sinentoldrewhap[.]pro, pixel.sinentoldrewhap[.]pro, euft.sinentoldrewhap[.]pro, yg9d.sinentoldrewhap[.]pro, p4.sinentoldrewhap[.]pro, p2.sinentoldrewhap[.]pro, p3.sinentoldrewhap[.]pro, p6.sinentoldrewhap.[]pro, p5.sinentoldrewhap[.]pro |
| Symptoms | Seeing advertisements not originating from the sites you are browsing. Intrusive pop-up ads. Decreased Internet browsing speed. |
| Distribution Methods | Deceptive pop-up ads, potentially unwanted applications (adware) |
| Damage | Decreased computer performance, browser tracking - privacy issues, possible additional malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
PUAs developers usually advertise their software by offering "useful" tools, features, etc, however, these are merely attempts to trick people into downloading and installing rogue programs. PUAs deliver none of the functionality promised or any other real value.
Typically, they generate revenue for their developers by serving unwanted ads, causing redirects to dubious sites, and gathering browsing data.
How did adware install on my computer?
These apps are usually downloaded and installed through intrusive ads (if clicked, they run scripts designed to download/install) or through set-ups of other programs.
Developers commonly distribute PUAs by bundling them into other software set-ups. Information about the inclusion of these additional downloads/installations is usually hidden in setup options such as "Custom", "Advanced", and so on. Unwanted downloads/installations of PUAs are caused when set-up options remain unchecked and unchanged.
How to avoid installation of potentially unwanted applications?
Download and install software with caution. Do not complete set-ups without first dismissing offers to download or install programs that are not required. Typically, PUAs are bundled into set-ups of free software. In any case, all software should be downloaded from official websites.
Do not trust or use other channels such as Peer-to-Peer networks, dubious websites, third party downloaders, and so on. Do not click ads that are displayed on sites relating to gambling, adult dating, pornography, etc. These might lead to unwanted downloads/installations or open dubious sites.
Typically, browsers cause unwanted redirects and display ads when there are PUAs installed. If this is a common problem, check for any unwanted apps (extensions, add-ons, and plug-ins) installed on the browser and remove them. The same applies to unwanted (suspicious) software that is installed on the operating system.
If your computer is already infected with rogue applications, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Appearance of sinentoldrewhap[.]pro website (GIF):
![sinentoldrewhap[.]pro website appearance (GIF)](/images/stories/screenshots201904/sinentoldrewhap-appearance.gif)
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is sinentoldrewhap.pro pop-up?
- STEP 1. Remove spam notifications from Google Chrome
- STEP 2. Remove spam notifications from Google Chrome (Android)
- STEP 3. Remove spam notifications from Mozilla Firefox
- STEP 4. Remove spam notifications from Microsoft Edge
- STEP 5. Remove spam notifications from Safari (macOS)
Disable unwanted browser notifications:
Video showing how to disable web browser notifications:
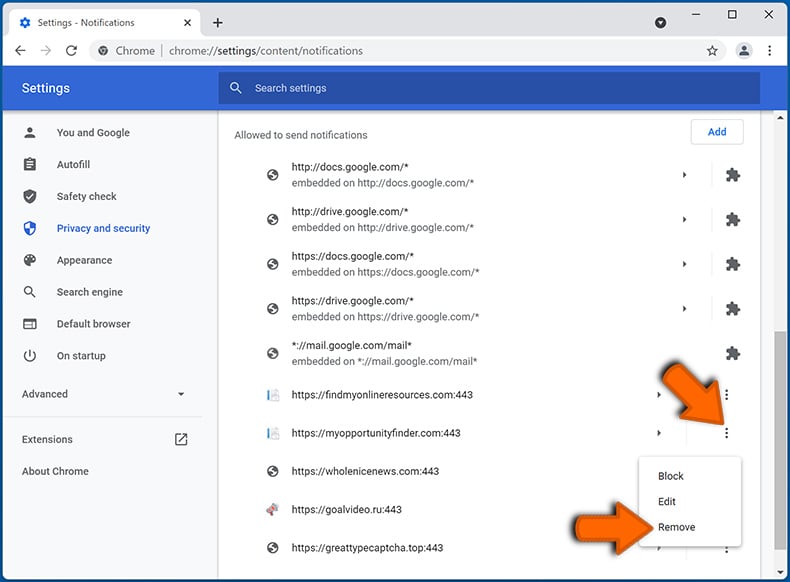
 Remove spam notifications from Google Chrome:
Remove spam notifications from Google Chrome:
Click the Menu button (three dots) on the right upper corner of the screen and select "Settings". In the opened window select "Privacy and security", then click on "Site Settings" and choose "Notifications".
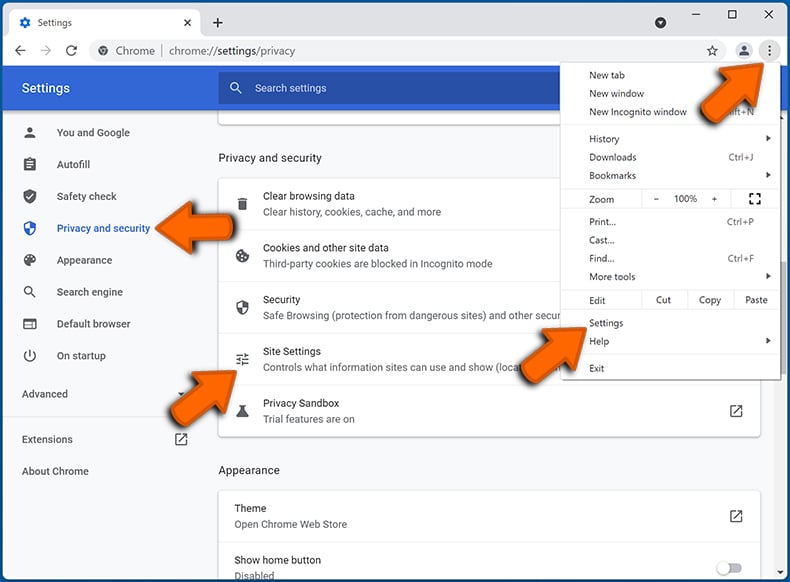
In the "Allowed to send notifications" list search for websites that you want to stop receiving notifications from. Click on the three dots icon near the website URL and click "Block" or "Remove" (if you click "Remove" and visit the malicious site once more, it will ask to enable notifications again).
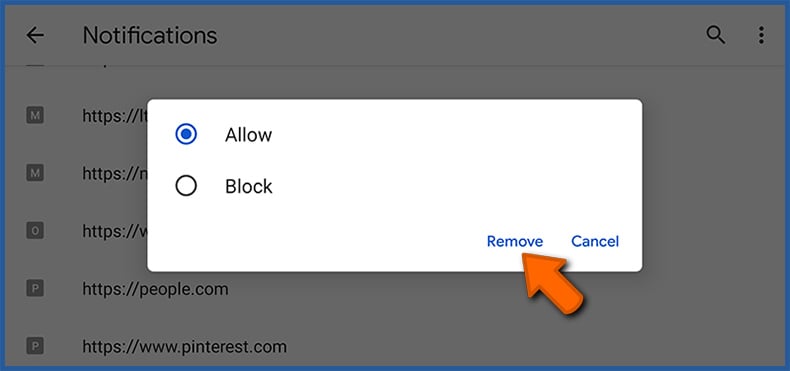
 Remove spam notifications from Google Chrome (Android):
Remove spam notifications from Google Chrome (Android):
Tap the Menu button (three dots) on the right upper corner of the screen and select "Settings". Scroll down, tap on "Site settings" and then "Notifications".
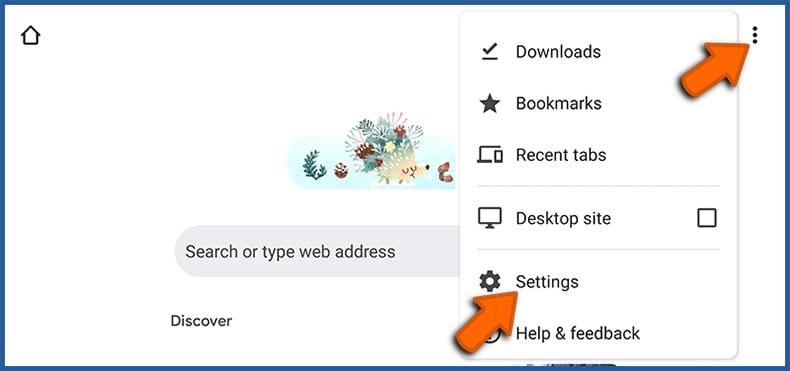
In the opened window, locate all suspicious URLs and tap on them one-by-one. Once the pop-up shows up, select either "Block" or "Remove" (if you tap "Remove" and visit the malicious site once more, it will ask to enable notifications again).
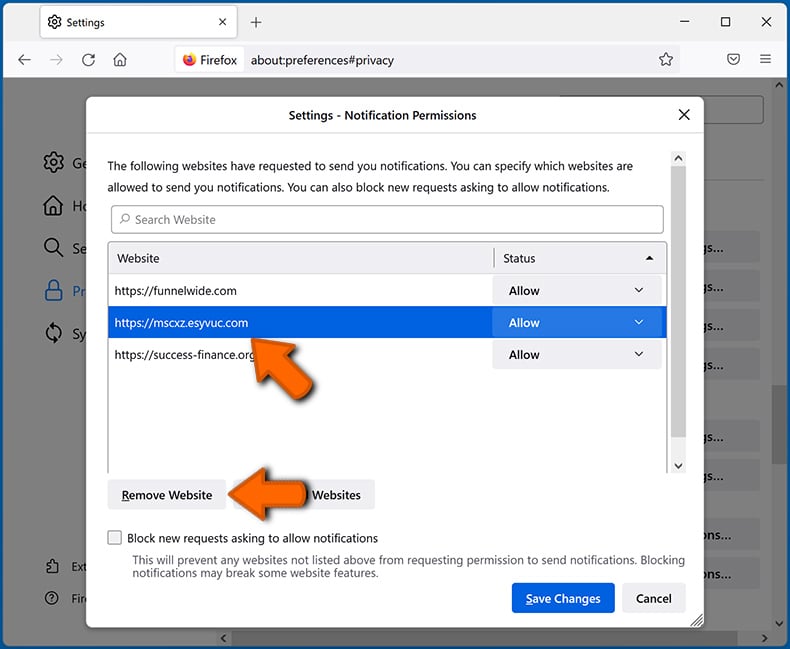
 Remove spam notifications from Mozilla Firefox:
Remove spam notifications from Mozilla Firefox:
Click the Menu button (three bars) on the right upper corner of the screen. Select "Settings" and click on "Privacy & Security" in the toolbar on the left hand side of the screen. Scroll down to the "Permissions" section and click the "Settings" button next to "Notifications".
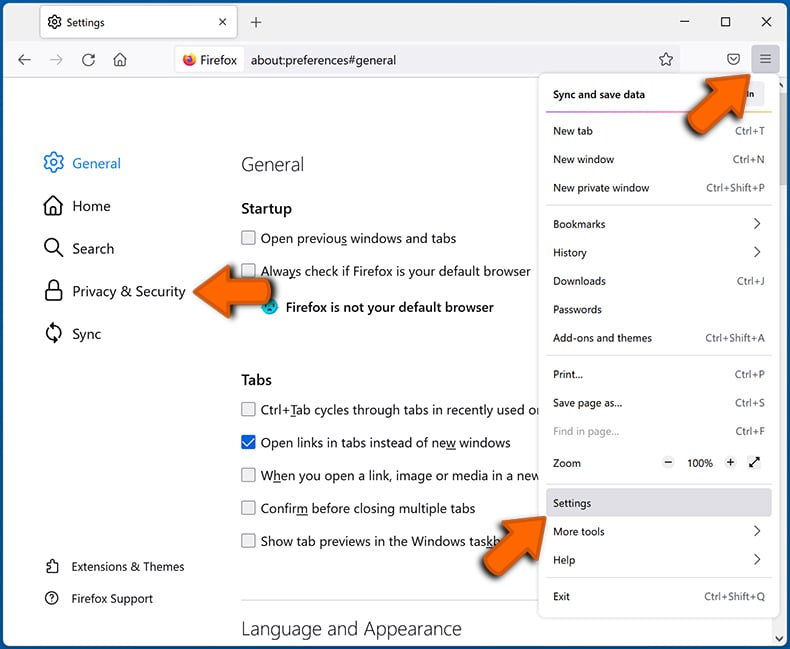
In the opened window, locate all suspicious URLs and block them using the drop-down menu or either remove them by clicking "Remove Website" at the bottom of the window (if you click "Remove Website" and visit the malicious site once more, it will ask to enable notifications again).
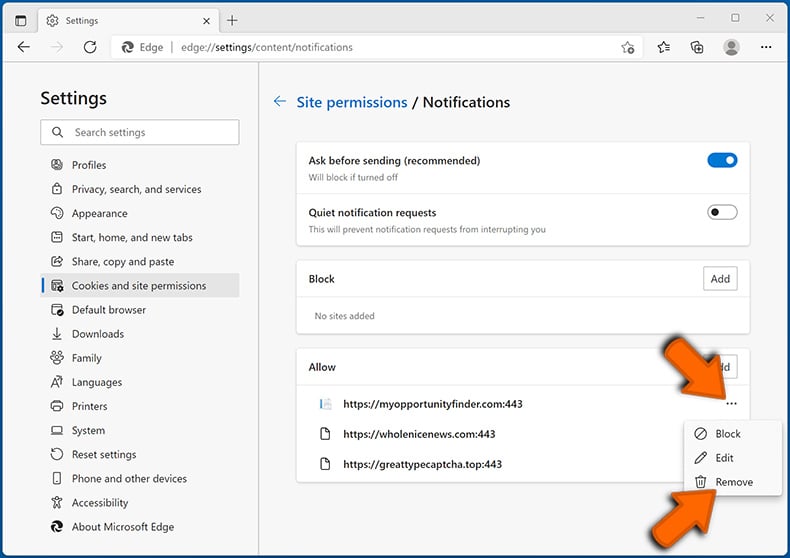
 Remove spam notifications from Microsoft Edge:
Remove spam notifications from Microsoft Edge:
Click the menu button (three dots) on the right upper corner of the Edge window and select "Settings". Click on "Cookies and site permissions" in the toolbar on the left hand side of the screen and select "Notifications".
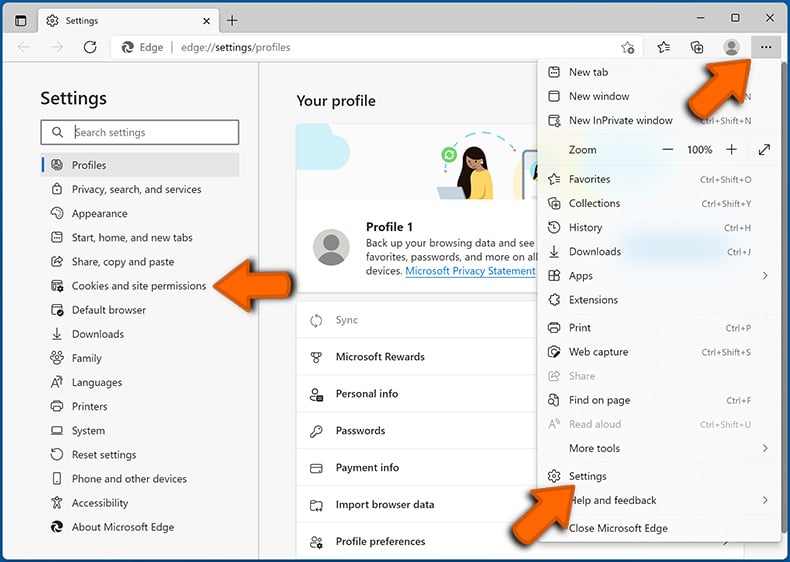
Click three dots on the right hand side of each suspicious URL under "Allow" section and click "Block" or "Remove" (if you click "Remove" and visit the malicious site once more, it will ask to enable notifications again).
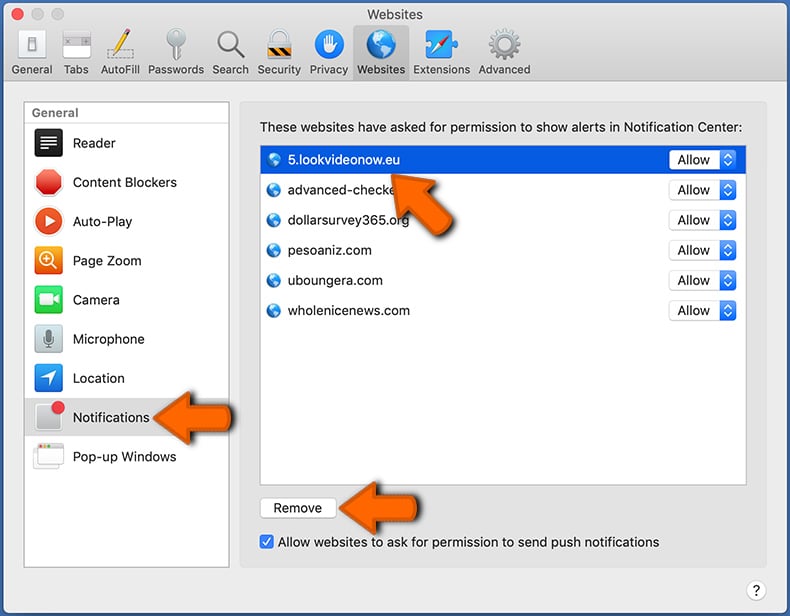
 Remove spam notifications from Safari (macOS):
Remove spam notifications from Safari (macOS):
Click "Safari" button on the left upper corner of the screen and select "Preferences...". Select the "Websites" tab and then select "Notifications" section on the left pane.
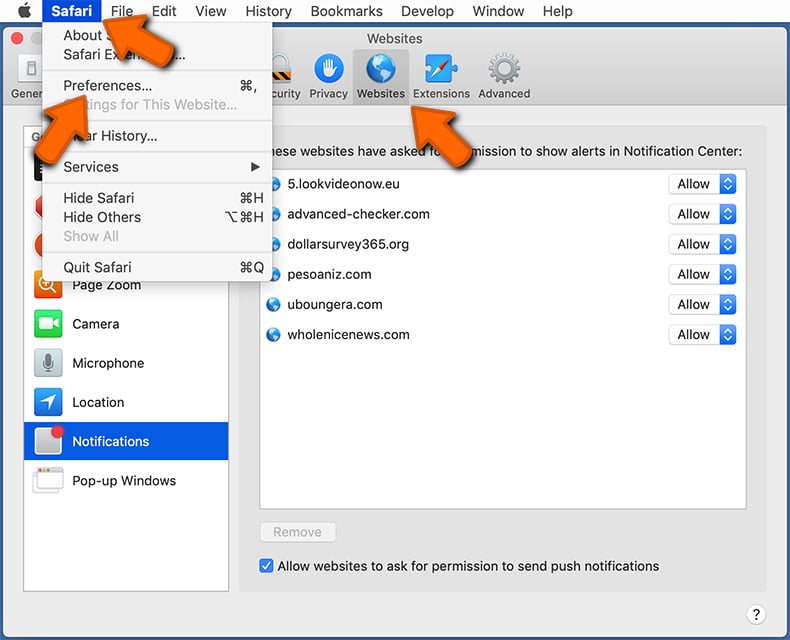
Check for suspicious URLs and apply the "Deny" option using the drop-down menu or either remove them by clicking "Remove" at the bottom of the window (if you click "Remove" and visit the malicious site once more, it will ask to enable notifications again)
How to avoid browser notification spam?
Internet users should be very skeptical when being asked to allow notifications. While this is a useful feature that allows you to receive timely news from websites you like, deceptive marketers frequently abuse it.
Only allow notifications from websites that you fully trust. For added security - use an anti-malware application with a real-time web browsing monitor to block shady websites that tries to trick you into allowing spam notifications. We recommend using Combo Cleaner Antivirus for Windows.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion