Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is XiaoBa?
First discovered by MalwareHunterTeam, XiaoBa is a ransomware-type virus that stealthily infiltrates systems and encrypts stored files. During encryption, XiaoBa appends filenames with the ".Encrypted[BaYuCheng@yeah.net].XiaBa" extension (e.g., "sample.jpg" is renamed to "sample.jpg.Encrypted[BaYuCheng@yeah.net].XiaBa").
Following successful encryption, XiaoBa creates two files ("_XiaoBa_Info_.hta" and "_XiaoBa_Info_.bmp"), placing them on the desktop. It also opens the .hta file and sets the .bmp file as the desktop wallpaper. Other variants of this ransomware use ".[BaYuCheng@yeah.net].china" and .[xiaoba_666@163.com]Encrypted_(victim ID).XIAOBA extensions for encrypted files.
The opened .hta file displays a pop-up window with a ransom-demand message. The .bmp file also contains a similar, yet shorter message. The entire window and text is very similar to that of GlobeImposter and its newer variants. The message states that files are encrypted and that the victim must pay a ransom to decrypt them.
It is currently unknown which type of cryptography (symmetric or asymmetric) XiaoBa uses - this information is not provided, however, it is safe to assume that decryption requires unique keys generated for each victim. These keys are stored on a remote server controlled by XiaoBa's developers.
Users are encouraged to pay a ransom by contacting developers via an email address provided. The cost depends on how quickly victims make contact. In most cases, cyber criminals demand $500-$1500 in Bitcoins or another cryptocurrency.
Victims are also permitted to attach up to five selected files (up to 10 Mb in total), which are then decrypted and returned to the victim free of charge. This, supposedly to 'guarantee' that decryption is possible. Despite this, cyber criminals should never be trusted. Research shows that these people often ignore victims, once payments are submitted.
Therefore, you are strongly advised to ignore all requests to contact these people or pay any ransoms. In most cases, paying gives no positive result and you will be scammed. Unfortunately, there are currently no tools capable of restoring files encrypted by XiaoBa. Therefore, the only solution is to restore everything from a backup.
Screenshot of a message encouraging users to pay a ransom to decrypt their compromised data:

XiaoBa is virtually identical to GANDCRAB, SUSPENDED, DataKeeper, Saturn, and dozens of other ransomware-type viruses. Although these viruses are developed by different cyber criminals, all have identical behavior - they encrypt data and make ransom demands. In most cases, the size of ransom and type of encryption algorithm used are the only major differences.
Research shows that, unfortunately, most of these viruses employ algorithms (e.g., RSA, AES, and so on) that generate unique decryption keys.
Therefore, unless these viruses have certain bugs/flaws (e.g., the keys are stored locally, they are hard-coded or similar), file decryption manually without involvement of developers (contacting these people is not recommended) is impossible.
Ransomware is one of the main reasons why you should keep regular data backups, however, backup files must be stored on a remote server or unplugged external storage, otherwise they will also be encrypted.
How did ransomware infect my computer?
To proliferate ransomware, developers typically use spam emails, unofficial download sources, fake software updaters, and trojans. Spam emails might contain infectious attachments (e.g., MS Office documents, JavaScript files, and so on) that, once opened, download and install malware.
Third party download sources (peer-to-peer networks, freeware download websites, free file hosting websites, etc.) present malicious executables as legitimate software, thereby tricking users into downloading and installing malware. Fake update tools infect the system by exploiting outdated softwares bugs/flaws or downloading/installing viruses rather than software updates.
Trojans are the simplest - they merely open "backdoors" for other viruses to infiltrate the system. Ultimately, the main reasons for computer infections are poor knowledge and careless behavior.
| Name | XiaoBa virus |
| Threat Type | Ransomware, Crypto Virus, Files locker |
| Encrypted Files Extension | .XiaoBa, .XIAOBA, .china, .XiaBa |
| Ransom Demanding Message | _XiaoBa_Decryption_Method_.txt, _XiaoBa_Decryption_Method_.bmp, _XiaoBa_Info_.hta, _XiaoBa_Info_.bmp |
| Cyber Criminal Contact | BaYuCheng@yeah.net, xiaoba_666@163.com, B32588601@163.com |
| Detection Names | Avast (Win32:Malware-gen), BitDefender (Gen:Variant.Ransom.208), ESET-NOD32 (A Variant Of Win32/Filecoder.NOP), Kaspersky (UDS:Trojan.Win32.Generic), Microsoft (Program:Win32/Wacapew.C!ml), Full List Of Detections (VirusTotal) |
| Symptoms | Cannot open files stored on your computer, previously functional files now have a different extension (for example, my.docx.locked). A ransom demand message is displayed on your desktop. Cyber criminals demand payment of a ransom (usually in bitcoins) to unlock your files. |
| Distribution methods | Infected email attachments (macros), torrent websites, malicious ads. |
| Damage | All files are encrypted and cannot be opened without paying a ransom. Additional password-stealing trojans and malware infections can be installed together with a ransomware infection. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
How to protect yourself from ransomware infections?
Be very cautious when browsing the Internet. Never open files received from suspicious/unrecognizable email addresses. These emails should be deleted immediately, without reading. It is also important to download/install your applications from official sources only, using direct download links.
Bear in mind that criminals proliferate rogue apps via third party download/installation set-ups, and thus, these tools should never be used.
Keep installed applications updated and use a legitimate anti-virus/anti-spyware suite, however, since criminals proliferate ransomware using fake update tools, you are advised to use implemented updated features or tools provided by the official developer only. The key to computer safety is caution.
Text presented in XiaoBi ransomware pop-up ("_XiaoBa_Info_.hta"):
All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail BaYuCheng@yeah.net
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 5 files for free decryption. The total size of files must be less than 10Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click 'Buy bitcoins', and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Screenshot of XiaoBa desktop wallpaper:

Screenshot of files encrypted by XiaoBa (".Encrypted[BaYuCheng@yeah.net].XiaBa" extension):

Screenshots of a desktop wallpaper set by another variant of XiaoBa ransomware:

Appearance of a text file dropped by another variant of XiaoBa ransomware (GIF):

Text presented within the wallpaper and text file:
Simplified Chinese:
很抱歉,你的所有文件已经被"XiaoBa"加密了
你只需付一点小费用就可以解密所有文件!
将0.01个比特币发送到下面的地址:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
在这个地址购买比特币:
hxxps://localbitcoins.com/buy_bitcoins
比特币到账后即可进行解密工作
付款后向"B32588601@163.com"这个邮箱发送你的ID和付款信息
验证完成后你会得到一个解密工具和一个Key
打开解密工具输入Key,然后选择你需要解密的文件进行解密工作
解密你的文件方法就是这么简单!
赶快付款吧!别犹豫了,我绝不会骗你的。
注意:被加密的文件只有我们的解密工具才能解密,不要相信其他人的解密工具
不要尝试破解文件,破解文件可能导致文件损坏!
如果两天内不付款,价格将翻倍
如果七天内没有付款,我们将不再支持解密文件
English:
Sorry, all your files have been "XiaoBa" encrypted
You can decrypt all your files with a little tip!
Send 0.01 bitcoins to the following address:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Buy bitcoins at this address:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin can be decrypted after crediting
After payment, send your ID and payment information to "B32588601@163.com"
After verification you will get a decryption tool and a Key
Open the decryption tool Enter Key, and then select the files you need to decrypt the decryption work
The way to decrypt your files is that simple!
Quickly pay it! Do not hesitate, I will not lie to you.
Note: Encrypted files can only be decrypted by our decryption tools. Do not trust other people's decryption tools
Do not try to crack the file, crack the file may cause file corruption!
If you do not pay within two days, the price will double
If there is no payment within seven days, we will no longer support the decryption of documents
Japanese:
申し訳ありませんが、あなたのすべてのファイルは "XiaoBa"暗号化されています
ちょっとしたヒントですべてのファイルを解読できます!
次のアドレスに0.01 bitcoinsを送信します。
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
このアドレスでビットコインを購入する:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoinはクレジット処理後に復号化できます
お支払い後、IDとお支払い情報を「B32588601@163.com」にお送りください
確認の後、解読ツールとキーを取得します
復号化ツールEnterキーを開き、復号化作業の復号化に必要なファイルを選択します
あなたのファイルを解読する方法は簡単です!
すぐにそれを支払う! 私はあなたに嘘をつきません。
注:暗号化されたファイルは、私たちの解読ツールでのみ解読できます。他人の解読ツールを信用しないでください
ファイルを解読しようとしないで、ファイルを解読してファイルの破損を引き起こす可能性があります!
2日以内に支払いをしないと、価格は2倍になります
7日以内に支払いがない場合、私たちはもはや文書の解読をサポートしません
русский:
Извините, все ваши файлы были «XiaoBa» зашифрованы
Вы можете расшифровать все свои файлы с помощью небольшого наконечника!
Отправьте 0.01 биткойны по следующему адресу:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Купите биткойны по этому адресу:
hxxps://localbitcoins.com/buy_bitcoins
Биткойн можно расшифровать после кредитования
После оплаты отправьте свой идентификатор и платежную информацию на "B32588601@163.com"
После проверки вы получите инструмент дешифрования и ключ
Откройте инструмент дешифрования Enter Key, а затем выберите файлы, необходимые для расшифровки работы дешифрования
Способ дешифрования файлов - это просто!
Быстро заплатите! Не стесняйтесь, я не буду врать вам.
Примечание. Зашифрованные файлы могут быть дешифрованы только нашими инструментами дешифрования. Не доверяйте инструментам дешифрования других людей
Не пытайтесь взломать файл, взломать файл может привести к повреждению файла!
Если вы не заплатите в течение двух дней, цена удвоится
Если в течение семи дней нет оплаты, мы больше не будем поддерживать расшифровку документов
한국어:
죄송합니다. 모든 파일은 "XiaoBa"암호화되어 있습니다.
당신은 작은 팁으로 모든 파일을 해독 할 수 있습니다!
0.01 비트 코인을 다음 주소로 보냅니다.
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
이 주소에서 비트 코를 구입하십시오.
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin은 신용 한 후에 해독 할 수 있습니다.
지불 후 ID와 지불 정보를 "B32588601@163.com"으로 보내십시오.
확인 후 암호 해독 도구와 키를 받게됩니다.
암호 해독 도구 Enter 키를 누른 다음 암호 해독 작업의 암호 해독에 필요한 파일을 선택하십시오
파일을 해독하는 방법은 간단합니다!
빨리 지불하십시오! 망설이지 마라, 나는 너에게 거짓말하지 않을 것이다.
참고 : 암호화 된 파일은 당사의 암호 해독 도구로만 해독 할 수 있습니다. 다른 사람의 암호 해독 도구를 신뢰하지 마십시오.
파일을 해독하려고하지 마십시오, 파일을 부수는 파일 손상을 일으킬 수 있습니다!
2 일 이내에 지불하지 않으면 가격이 두 배가됩니다.
7 일 이내에 지불이 없으면 더 이상 문서 해독을 지원하지 않습니다.
Deutsch:
Entschuldigung, alle Ihre Dateien wurden "XiaoBa" verschlüsselt
Sie können alle Ihre Dateien mit einem kleinen Tipp entschlüsseln!
Senden Sie 0,01 Bitcoins an die folgende Adresse:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Kaufen Sie Bitcoins unter dieser Adresse:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin kann nach der Gutschrift entschlüsselt werden
Nach der Zahlung senden Sie Ihre ID und Zahlungsinformationen an "B32588601@163.com"
Nach der Überprüfung erhalten Sie ein Entschlüsselungstool und einen Schlüssel
Öffnen Sie das Entschlüsselungswerkzeug Enter Key und wählen Sie dann die Dateien aus, die Sie zum Entschlüsseln der Entschlüsselungsarbeiten benötigen
Die Art, Ihre Dateien zu entschlüsseln, ist so einfach!
Bezahlen Sie es schnell! Zögere nicht, ich werde dich nicht anlügen.
Hinweis: Verschlüsselte Dateien können nur mit unseren Entschlüsselungstools entschlüsselt werden. Vertrauen Sie nicht den Entschlüsselungstools anderer Benutzer
Versuchen Sie nicht, die Datei zu knacken, die Datei zu knacken kann zur Beschädigung der Datei führen!
Wenn Sie nicht innerhalb von zwei Tagen bezahlen, verdoppelt sich der Preis
Wenn innerhalb von sieben Tagen keine Zahlung erfolgt, werden wir die Entschlüsselung von Dokumenten nicht mehr unterstützen
Français:
Désolé, tous vos fichiers ont été "XiaoBa" cryptés
Vous pouvez déchiffrer tous vos fichiers avec un petit conseil!
Envoyer 0,01 bitcoins à l'adresse suivante:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Acheter des bitcoins à cette adresse:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin peut être déchiffré après avoir crédité
Après paiement, envoyez votre identifiant et vos informations de paiement à "B32588601@163.com"
Après vérification, vous obtiendrez un outil de décryptage et une clé
Ouvrez l'outil de décryptage Entrée clé, puis sélectionnez les fichiers dont vous avez besoin pour décrypter le travail de décryptage
La façon de déchiffrer vos fichiers est aussi simple que cela!
Rapidement le payer! Ne hésitez pas, je ne vais pas vous mentir.
Note: Les fichiers cryptés ne peuvent être décryptés que par nos outils de décryptage Ne faites pas confiance aux outils de déchiffrement des autres
N'essayez pas de casser le fichier, casser le fichier peut causer la corruption de fichier!
Si vous ne payez pas dans les deux jours, le prix doublera
S'il n'y a pas de paiement dans les sept jours, nous ne prendrons plus en charge le décryptage des documents
Ελληνικά:
Λυπούμαστε, όλα τα αρχεία σας έχουν κρυπτογραφηθεί "XiaoBa"
Μπορείτε να αποκρυπτογραφήσετε όλα τα αρχεία σας με μια μικρή συμβουλή!
Στείλτε 0.01 bitcoins στην ακόλουθη διεύθυνση:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Αγοράστε bitcoins σε αυτή τη διεύθυνση:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin μπορεί να αποκρυπτογραφηθεί μετά την πίστωση
Μετά την πληρωμή, στείλτε τα στοιχεία ταυτότητας και πληρωμής σας στο "B32588601@163.com"
Μετά την επαλήθευση θα έχετε ένα εργαλείο αποκρυπτογράφησης και ένα κλειδί
Ανοίξτε το εργαλείο αποκρυπτογράφησης Enter Key και, στη συνέχεια, επιλέξτε τα αρχεία που χρειάζεστε για να αποκρυπτογραφήσετε το έργο αποκρυπτογράφησης
Ο τρόπος για να αποκρυπτογραφήσετε τα αρχεία σας είναι τόσο απλό!
Πληρώστε γρήγορα! Μη διστάσετε, δεν θα σας ψέψω.
Σημείωση: Τα κρυπτογραφημένα αρχεία μπορούν να αποκρυπτογραφηθούν μόνο από τα εργαλεία αποκρυπτογράφησης. Μην εμπιστεύεστε τα εργαλεία αποκρυπτογράφησης άλλων ανθρώπων
Μην προσπαθήσετε να σπάσετε το αρχείο, ρωγμή το αρχείο μπορεί να προκαλέσει διαφθορά αρχείο!
Αν δεν πληρώσετε εντός δύο ημερών, η τιμή θα διπλασιαστεί
Αν δεν υπάρξει πληρωμή εντός επτά ημερών, δεν θα υποστηρίζουμε πλέον την αποκρυπτογράφηση εγγράφων
বাংলা ভাষার:
দুঃখিত, আপনার সমস্ত ফাইল এনক্রিপ্ট হয়েছে "XiaoBa" হয়েছে
আপনি একটু টিপ সঙ্গে আপনার ফাইল ডিক্রিপ্ট করতে পারেন!
নিম্নোক্ত ঠিকানায় 0.01 বিটকয়েন প্রেরণ করুন:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
এই ঠিকানায় বিটকয়েন কিনুন:
hxxps://localbitcoins.com/buy_bitcoins
ক্রেডিট করার পরে বিটকয়েনকে ডিক্রিপ্ট করা যায়
অর্থ প্রদানের পরে, আপনার আইডি এবং পেমেন্ট তথ্য "B32588601@163.com" তে পাঠান
যাচাই করার পর আপনি একটি ডিক্রিপশন টুল এবং একটি কী পাবেন
ডিক্রিপশন টুলটি খুলুন কি কী প্রবেশ করান, এবং তারপরে ডিক্রিপশন কাজটি ডিক্রিপ্ট করতে আপনার প্রয়োজনীয় ফাইলগুলি নির্বাচন করুন
আপনার ফাইল decrypt উপায় যে সহজ!
দ্রুত তা পরিশোধ! দ্বিধা করবেন না, আমি আপনার কাছে মিথ্যা বলব না।
দ্রষ্টব্য: এনক্রিপ্ট করা ফাইলগুলিকে শুধুমাত্র আমাদের ডিক্রিপশন সরঞ্জামগুলি দ্বারা ডিক্রিপ্ট করা যায়। অন্য লোকেদের ডিক্রিপশন সরঞ্জামগুলিতে বিশ্বাস করবেন না
ফাইল ক্র্যাক করার চেষ্টা করবেন না, ফাইল দুর্নীতি ফাইল হতে পারে ক্র্যাক!
যদি আপনি দুই দিনের মধ্যে পরিশোধ না করেন, দাম দ্বিগুণ হবে
যদি সাত দিনের মধ্যে কোনো পেমেন্ট না থাকে, তাহলে আমরা নথিগুলির ডিক্রিপশনকে আর সমর্থন করব না
繁體中文:
很抱歉,你的所有文件已經被"XiaoBa"加密了
你只需付一點小費用就可以解密所有文件!
將0.01個比特幣發送到下面的地址:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
在這個地址購買比特幣:
hxxps://localbitcoins.com/buy_bitcoins
比特幣到賬後即可進行解密工作
付款後向"B32588601@163.com"這個郵箱發送你的ID和付款信息
驗證完成後你會得到一個解密工具和一個Key
打開解密工具輸入Key,然後選擇你需要解密的文件進行解密工作
解密你的文件方法就是這麼簡單!
趕快付款吧!別猶豫了,我絕不會騙你的。
注意:被加密的文件只有我們的解密工具才能解密,不要相信其他人的解密工具
不要嘗試破解文件,破解文件可能導致文件損壞!
如果兩天內不付款,價格將翻倍
如果七天內沒有付款,我們將不再支持解密文件
Español:
Lo sentimos, todos sus archivos han sido encriptados con "XiaoBa"
¡Puedes descifrar todos tus archivos con un pequeño consejo!
Enviar 0,01 bitcoins a la siguiente dirección:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Compre bitcoins en esta dirección:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin se puede descifrar después de acreditar
Después del pago, envíe su ID y la información de pago a "B32588601@163.com"
Después de la verificación, obtendrá una herramienta de descifrado y una clave
Abra la herramienta de descifrado Enter Key, y luego seleccione los archivos que necesita para descifrar el trabajo de descifrado
¡La forma de descifrar tus archivos es así de simple!
Pague rápidamente! No lo dudes, no te mentiré.
Nota: las herramientas de descifrado solo pueden descifrar los archivos cifrados. No confíe en las herramientas de descifrado de otras personas.
¡No intente descifrar el archivo, crackear el archivo puede causar daños en el archivo!
Si no paga dentro de dos días, el precio se duplicará
Si no se realiza el pago dentro de los siete días, ya no admitiremos el descifrado de documentos.
Portugues:
Desculpe, todos os seus arquivos foram "XiaoBa" criptografados
Você pode descriptografar todos os seus arquivos com uma pequena dica!
Envie 0.01 bitcoins para o seguinte endereço:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Compre bitcoins neste endereço:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin pode ser descriptografado após o crédito
Após o pagamento, envie suas informações de identificação e pagamento para "B32588601@163.com"
Após a verificação, você obterá uma ferramenta de descriptografia e uma Chave
Abra a ferramenta de descriptografia Enter Key e selecione os arquivos que você precisa para descriptografar o trabalho de descriptografia
A maneira de descriptografar seus arquivos é tão simples!
Rapidamente pague! Não hesite, não vou mentir para você.
Nota: Os arquivos criptografados só podem ser descriptografados por nossas ferramentas de descriptografia. Não confie nas ferramentas de descriptografia de outras pessoas
Não tente quebrar o arquivo, quebrar o arquivo pode causar corrupção de arquivos!
Se você não paga no prazo de dois dias, o preço irá dobrar
Se não houver pagamento dentro de sete dias, não iremos suportar o decodificação de documentos
Монгол хэл:
Уучлаарай, бүх файлууд нь "XiaoBa" шифрлэгдсэн байна
Та бүх файлаа бага зэрэг оройгоор буцааж шифрлэх боломжтой!
0.01 bitcoins-ыг дараах хаягаар илгээх:
1BkUrBsssxg3q6XQdJikCSHTN85AzKXcyN
Энэ хаягаар bitcoins худалдаж авах:
hxxps://localbitcoins.com/buy_bitcoins
Bitcoin кредит хийсний дараа буцааж шифрлэх боломжтой
Төлбөр хийгдсэний дараа таны ID болон төлбөрийн мэдээллийг "B32588601@163.com"
Баталгаажсаны дараа та шифрлэх хэрэгсэл болон түлхүүр авах болно
Шифрлэх хэрэгслийг Түлхүүрийг оруулаад, дараа нь шифрлэхийг буцааж шифрлэхэд шаардлагатай файлуудыг сонго
Файлуудыг буцааж шифрлэх арга нь ийм хялбар юм!
Хурдан төлөх! Бүү эргэлзээрэй, би чамайг худал хэлэхгүй.
Тэмдэглэл: Шифрлэгдсэн файлыг зөвхөн манай шифрлэх хэрэгслийг буцааж шифрлэх боломжтой. Бусад хүмүүсийн шифрлэх хэрэгслийг ашиглахгүй байх
Файлыг эвдэх гэж бүү оролдоорой, файлыг файлын эвдрэлд хүргэж болзошгүй!
Хэрэв та хоёр хоногийн дотор төлөхгүй бол үнэ хоёр дахин нэмэгдэх болно
Хэрэв 7 хоногийн дотор төлбөр төлөөгүй бол бид баримт бичгийн шифрийг цаашид дэмжихгүй болно
Screenshot of files encrypted by this XiaoBa ransomware variant:

XiaoBa ransomware removal:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Video suggesting what steps should be taken in case of a ransomware infection:
Quick menu:
- What is XiaoBa virus?
- STEP 1. Reporting ransomware to authorities.
- STEP 2. Isolating the infected device.
- STEP 3. Identifying the ransomware infection.
- STEP 4. Searching for ransomware decryption tools.
- STEP 5. Restoring files with data recovery tools.
- STEP 6. Creating data backups.
If you are a victim of a ransomware attack we recommend reporting this incident to authorities. By providing information to law enforcement agencies you will help track cybercrime and potentially assist in the prosecution of the attackers. Here's a list of authorities where you should report a ransomware attack. For the complete list of local cybersecurity centers and information on why you should report ransomware attacks, read this article.
List of local authorities where ransomware attacks should be reported (choose one depending on your residence address):
USA - Internet Crime Complaint Centre IC3
United Kingdom - Action Fraud
Spain - Policía Nacional
France - Ministère de l'Intérieur
Germany - Polizei
Italy - Polizia di Stato
The Netherlands - Politie
Poland - Policja
Portugal - Polícia Judiciária
Isolating the infected device:
Some ransomware-type infections are designed to encrypt files within external storage devices, infect them, and even spread throughout the entire local network. For this reason, it is very important to isolate the infected device (computer) as soon as possible.
Step 1: Disconnect from the internet.
The easiest way to disconnect a computer from the internet is to unplug the Ethernet cable from the motherboard, however, some devices are connected via a wireless network and for some users (especially those who are not particularly tech-savvy), disconnecting cables may seem troublesome. Therefore, you can also disconnect the system manually via Control Panel:
Navigate to the "Control Panel", click the search bar in the upper-right corner of the screen, enter "Network and Sharing Center" and select search result: 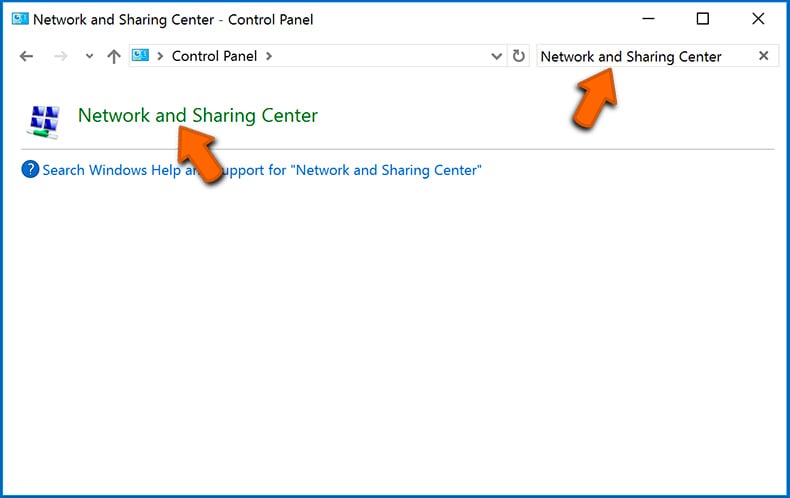
Click the "Change adapter settings" option in the upper-left corner of the window: 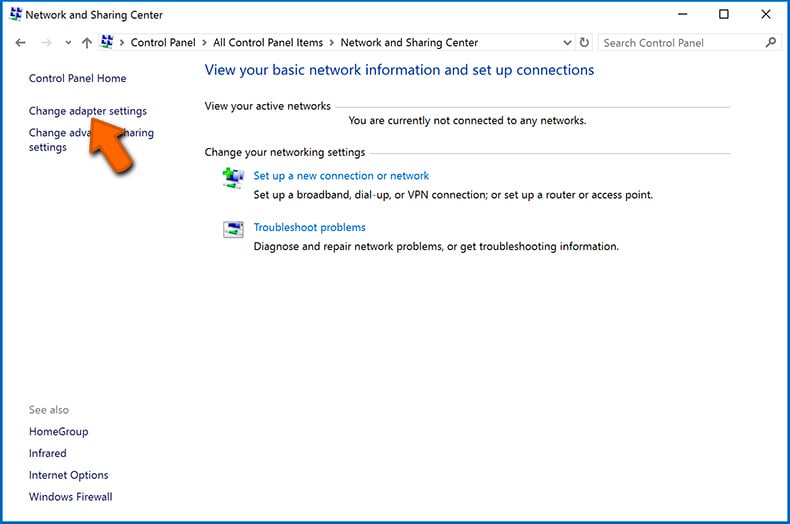
Right-click on each connection point and select "Disable". Once disabled, the system will no longer be connected to the internet. To re-enable the connection points, simply right-click again and select "Enable". 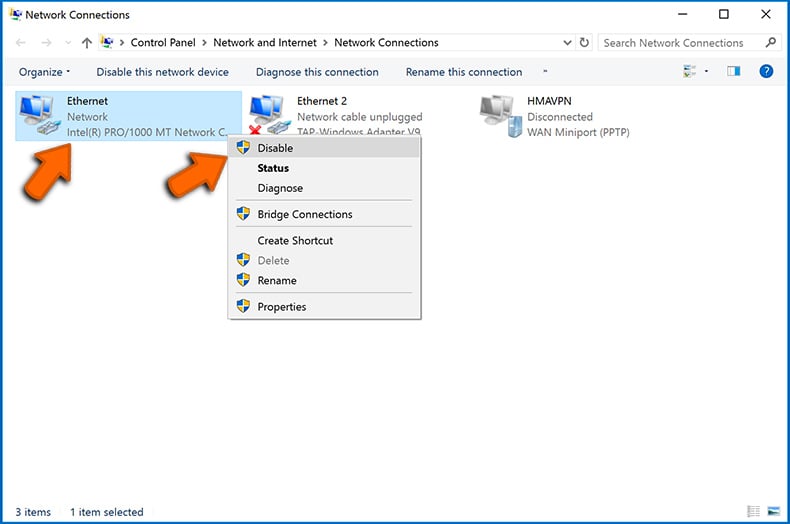
Step 2: Unplug all storage devices.
As mentioned above, ransomware might encrypt data and infiltrate all storage devices that are connected to the computer. For this reason, all external storage devices (flash drives, portable hard drives, etc.) should be disconnected immediately, however, we strongly advise you to eject each device before disconnecting to prevent data corruption:
Navigate to "My Computer", right-click on each connected device, and select "Eject": 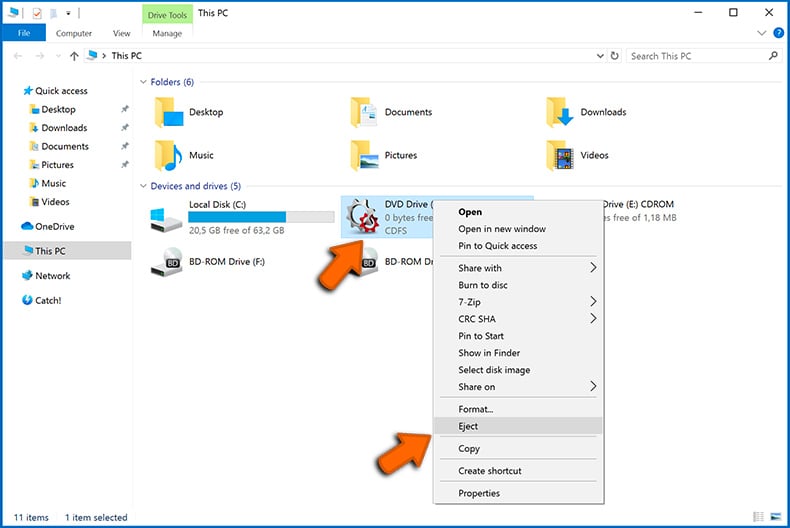
Step 3: Log-out of cloud storage accounts.
Some ransomware-type might be able to hijack software that handles data stored within "the Cloud". Therefore, the data could be corrupted/encrypted. For this reason, you should log-out of all cloud storage accounts within browsers and other related software. You should also consider temporarily uninstalling the cloud-management software until the infection is completely removed.
Identify the ransomware infection:
To properly handle an infection, one must first identify it. Some ransomware infections use ransom-demand messages as an introduction (see the WALDO ransomware text file below).
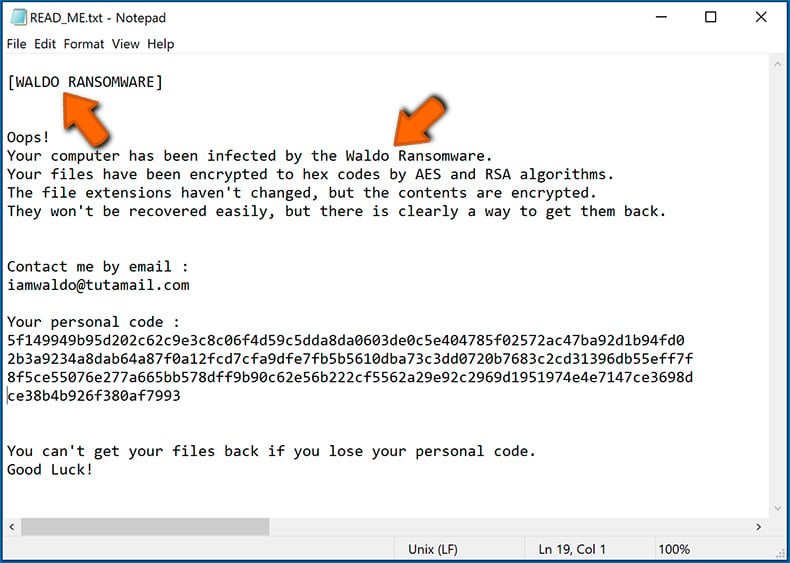
This, however, is rare. In most cases, ransomware infections deliver more direct messages simply stating that data is encrypted and that victims must pay some sort of ransom. Note that ransomware-type infections typically generate messages with different file names (for example, "_readme.txt", "READ-ME.txt", "DECRYPTION_INSTRUCTIONS.txt", "DECRYPT_FILES.html", etc.). Therefore, using the name of a ransom message may seem like a good way to identify the infection. The problem is that most of these names are generic and some infections use the same names, even though the delivered messages are different and the infections themselves are unrelated. Therefore, using the message filename alone can be ineffective and even lead to permanent data loss (for example, by attempting to decrypt data using tools designed for different ransomware infections, users are likely to end up permanently damaging files and decryption will no longer be possible even with the correct tool).
Another way to identify a ransomware infection is to check the file extension, which is appended to each encrypted file. Ransomware infections are often named by the extensions they append (see files encrypted by Qewe ransomware below).
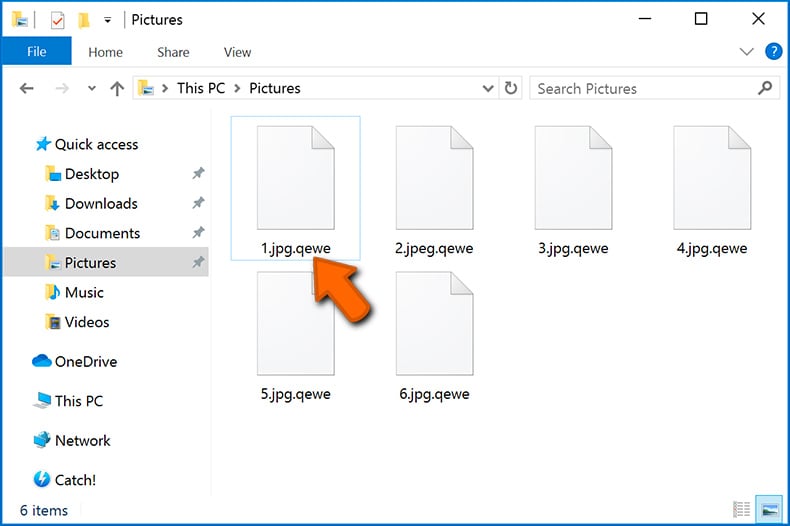
This method is only effective, however, when the appended extension is unique - many ransomware infections append a generic extension (for example, ".encrypted", ".enc", ".crypted", ".locked", etc.). In these cases, identifying ransomware by its appended extension becomes impossible.
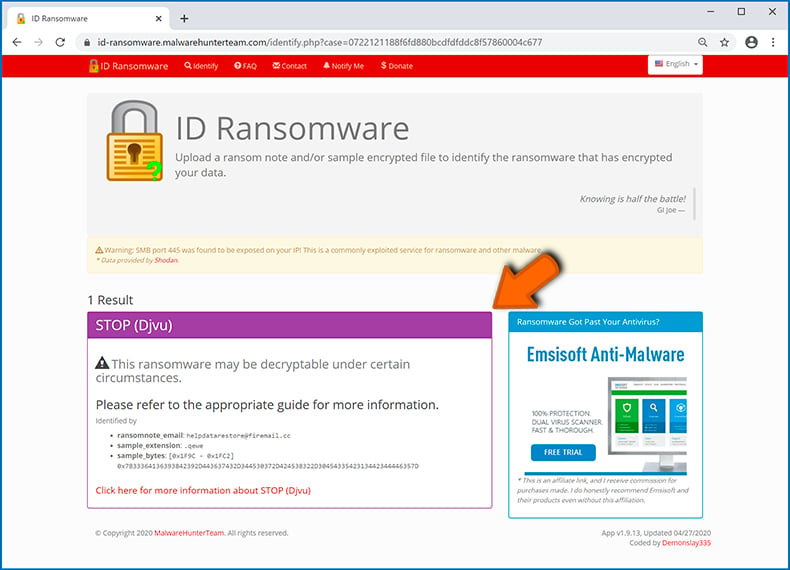
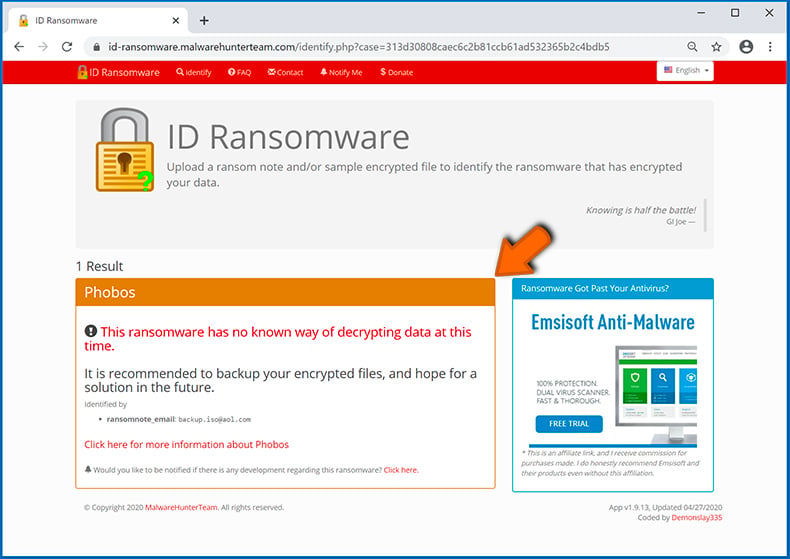
One of the easiest and quickest ways to identify a ransomware infection is to use the ID Ransomware website. This service supports most existing ransomware infections. Victims simply upload a ransom message and/or one encrypted file (we advise you to upload both if possible).

The ransomware will be identified within seconds and you will be provided with various details, such as the name of the malware family to which the infection belongs, whether it is decryptable, and so on.
Example 1 (Qewe [Stop/Djvu] ransomware):
Example 2 (.iso [Phobos] ransomware):
If your data happens to be encrypted by ransomware that is not supported by ID Ransomware, you can always try searching the internet by using certain keywords (for example, a ransom message title, file extension, provided contact emails, crypto wallet addresses, etc.).
Search for ransomware decryption tools:
Encryption algorithms used by most ransomware-type infections are extremely sophisticated and, if the encryption is performed properly, only the developer is capable of restoring data. This is because decryption requires a specific key, which is generated during the encryption. Restoring data without the key is impossible. In most cases, cybercriminals store keys on a remote server, rather than using the infected machine as a host. Dharma (CrySis), Phobos, and other families of high-end ransomware infections are virtually flawless, and thus restoring data encrypted without the developers' involvement is simply impossible. Despite this, there are dozens of ransomware-type infections that are poorly developed and contain a number of flaws (for example, the use of identical encryption/decryption keys for each victim, keys stored locally, etc.). Therefore, always check for available decryption tools for any ransomware that infiltrates your computer.
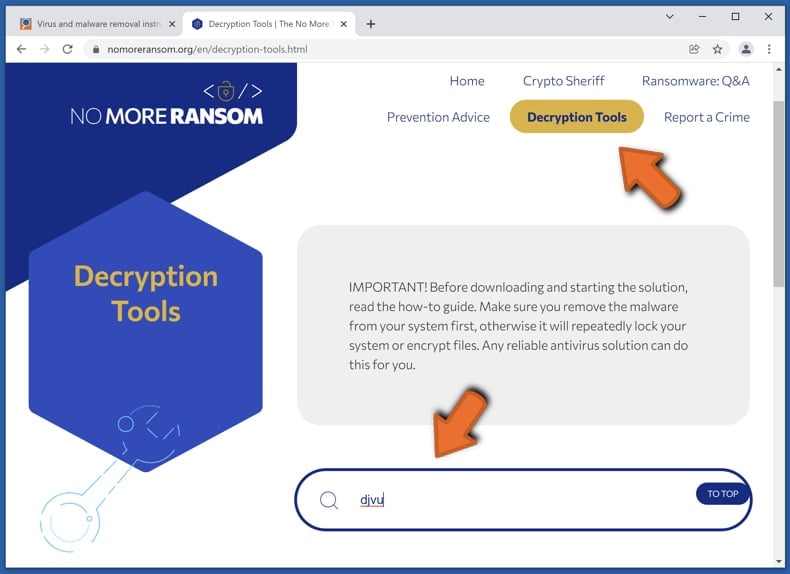
Finding the correct decryption tool on the internet can be very frustrating. For this reason, we recommend that you use the No More Ransom Project and this is where identifying the ransomware infection is useful. The No More Ransom Project website contains a "Decryption Tools" section with a search bar. Enter the name of the identified ransomware, and all available decryptors (if there are any) will be listed.
Restore files with data recovery tools:
Depending on the situation (quality of ransomware infection, type of encryption algorithm used, etc.), restoring data with certain third-party tools might be possible. Therefore, we advise you to use the Recuva tool developed by CCleaner. This tool supports over a thousand data types (graphics, video, audio, documents, etc.) and it is very intuitive (little knowledge is necessary to recover data). In addition, the recovery feature is completely free.
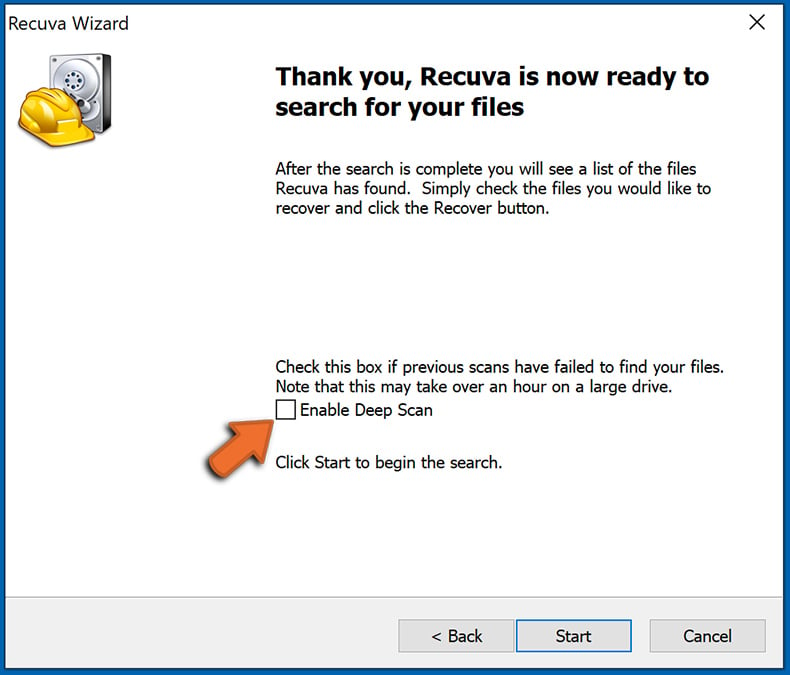
Step 1: Perform a scan.
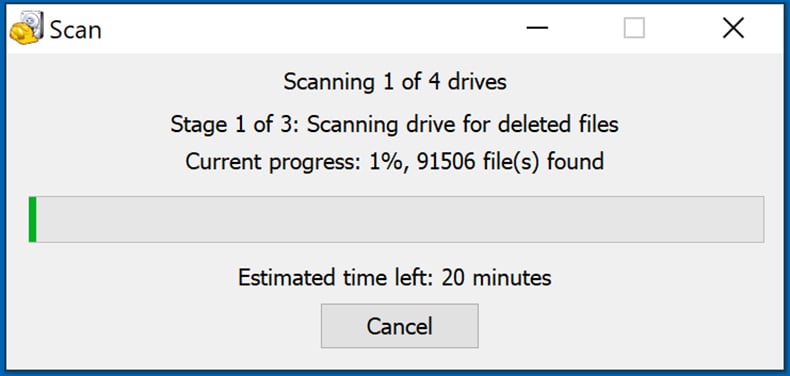
Run the Recuva application and follow the wizard. You will be prompted with several windows allowing you to choose what file types to look for, which locations should be scanned, etc. All you need to do is select the options you're looking for and start the scan. We advise you to enable the "Deep Scan" before starting, otherwise, the application's scanning capabilities will be restricted.
Wait for Recuva to complete the scan. The scanning duration depends on the volume of files (both in quantity and size) that you are scanning (for example, several hundred gigabytes could take over an hour to scan). Therefore, be patient during the scanning process. We also advise against modifying or deleting existing files, since this might interfere with the scan. If you add additional data (for example, downloading files/content) while scanning, this will prolong the process:
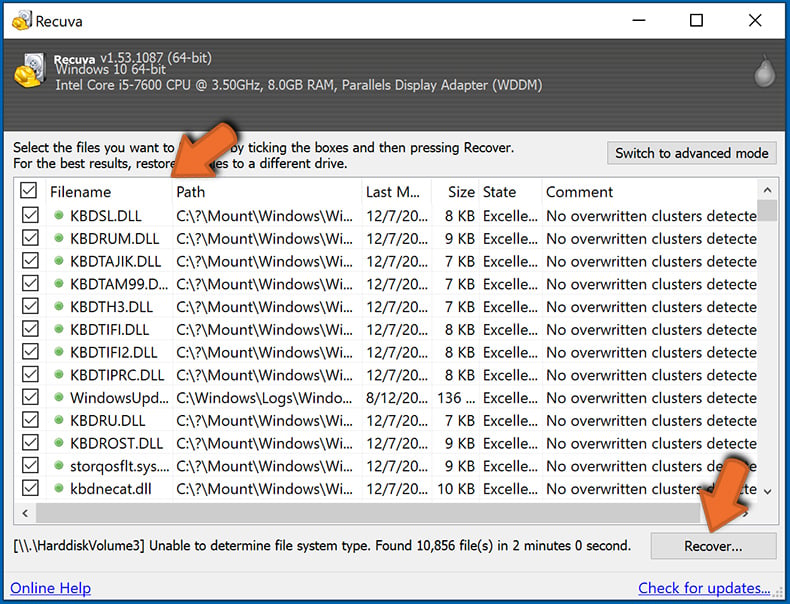
Step 2: Recover data.
Once the process is complete, select the folders/files you wish to restore and simply click "Recover". Note that some free space on your storage drive is necessary to restore data:
Create data backups:
Proper file management and creating backups is essential for data security. Therefore, always be very careful and think ahead.
Partition management: We recommend that you store your data in multiple partitions and avoid storing important files within the partition that contains the entire operating system. If you fall into a situation whereby you cannot boot the system and are forced to format the disk on which the operating system is installed (in most cases, this is where malware infections hide), you will lose all data stored within that drive. This is the advantage of having multiple partitions: if you have the entire storage device assigned to a single partition, you will be forced to delete everything, however, creating multiple partitions and allocating the data properly allows you to prevent such problems. You can easily format a single partition without affecting the others - therefore, one will be cleaned and the others will remain untouched, and your data will be saved. Managing partitions is quite simple and you can find all the necessary information on Microsoft's documentation web page.
Data backups: One of the most reliable backup methods is to use an external storage device and keep it unplugged. Copy your data to an external hard drive, flash (thumb) drive, SSD, HDD, or any other storage device, unplug it and store it in a dry place away from the sun and extreme temperatures. This method is, however, quite inefficient, since data backups and updates need to be made regularly. You can also use a cloud service or remote server. Here, an internet connection is required and there is always the chance of a security breach, although it's a really rare occasion.
We recommend using Microsoft OneDrive for backing up your files. OneDrive lets you store your personal files and data in the cloud, sync files across computers and mobile devices, allowing you to access and edit your files from all of your Windows devices. OneDrive lets you save, share and preview files, access download history, move, delete, and rename files, as well as create new folders, and much more.
You can back up your most important folders and files on your PC (your Desktop, Documents, and Pictures folders). Some of OneDrive’s more notable features include file versioning, which keeps older versions of files for up to 30 days. OneDrive features a recycling bin in which all of your deleted files are stored for a limited time. Deleted files are not counted as part of the user’s allocation.
The service is built using HTML5 technologies and allows you to upload files up to 300 MB via drag and drop into the web browser or up to 10 GB via the OneDrive desktop application. With OneDrive, you can download entire folders as a single ZIP file with up to 10,000 files, although it can’t exceed 15 GB per single download.
OneDrive comes with 5 GB of free storage out of the box, with an additional 100 GB, 1 TB, and 6 TB storage options available for a subscription-based fee. You can get one of these storage plans by either purchasing additional storage separately or with Office 365 subscription.
Creating a data backup:
The backup process is the same for all file types and folders. Here’s how you can back up your files using Microsoft OneDrive
Step 1: Choose the files/folders you want to backup.
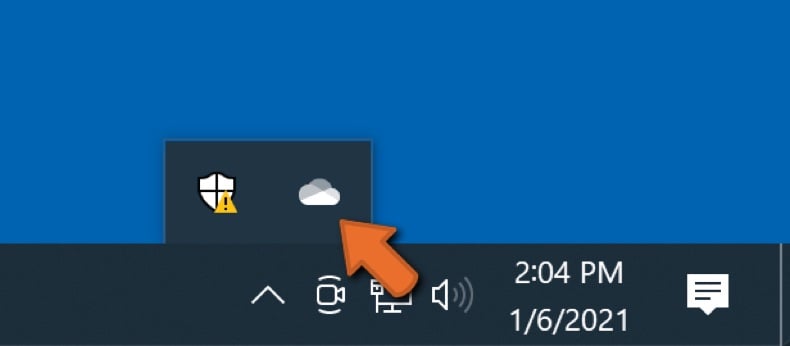
Click the OneDrive cloud icon to open the OneDrive menu. While in this menu, you can customize your file backup settings.
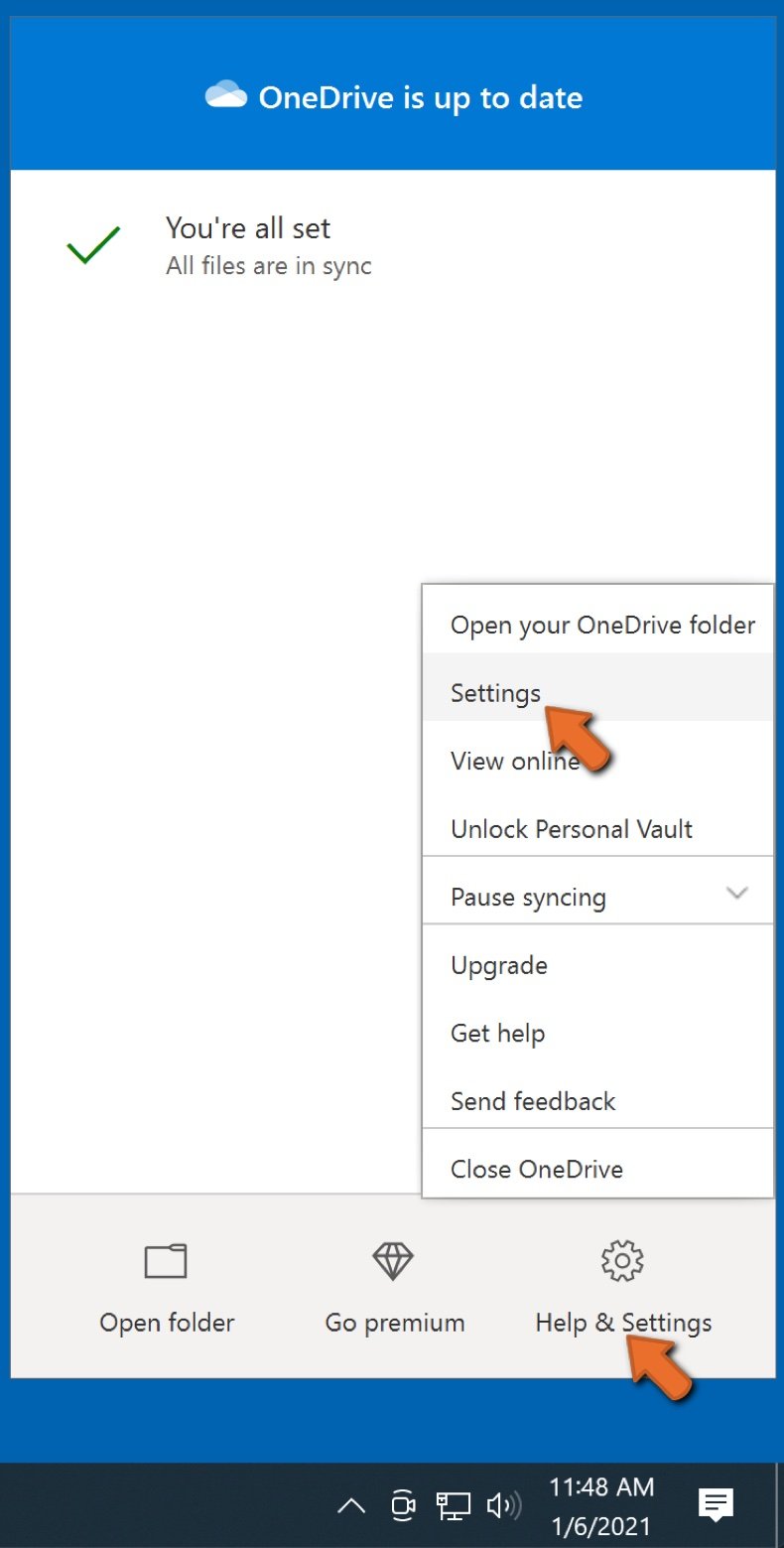
Click Help & Settings and then select Settings from the drop-down menu.
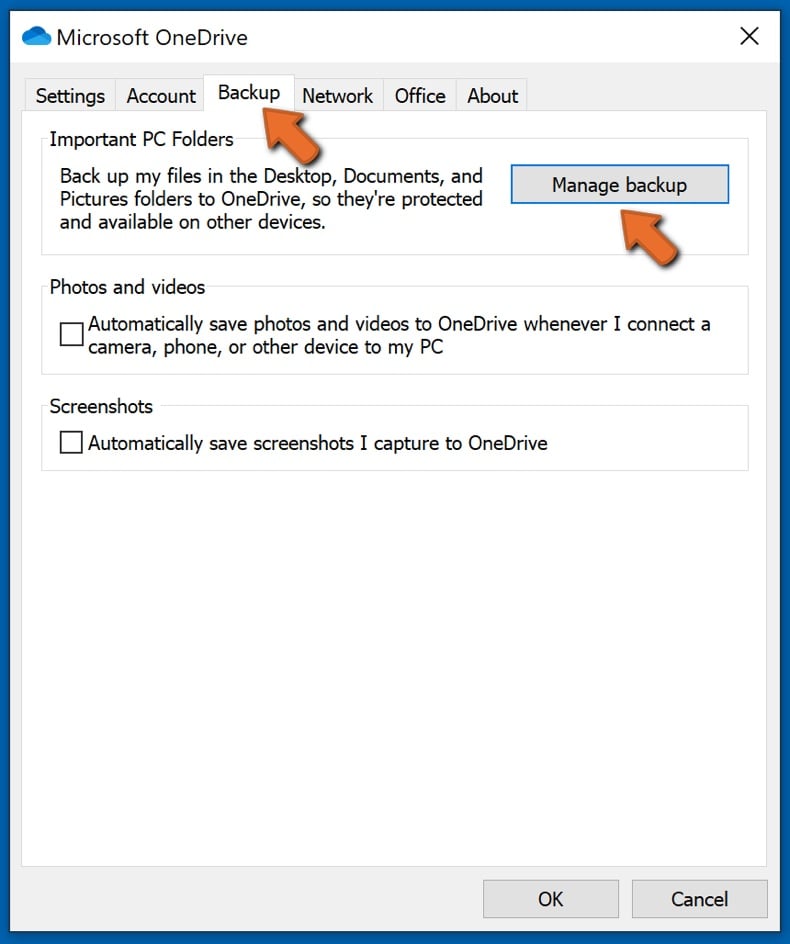
Go to the Backup tab and click Manage backup.
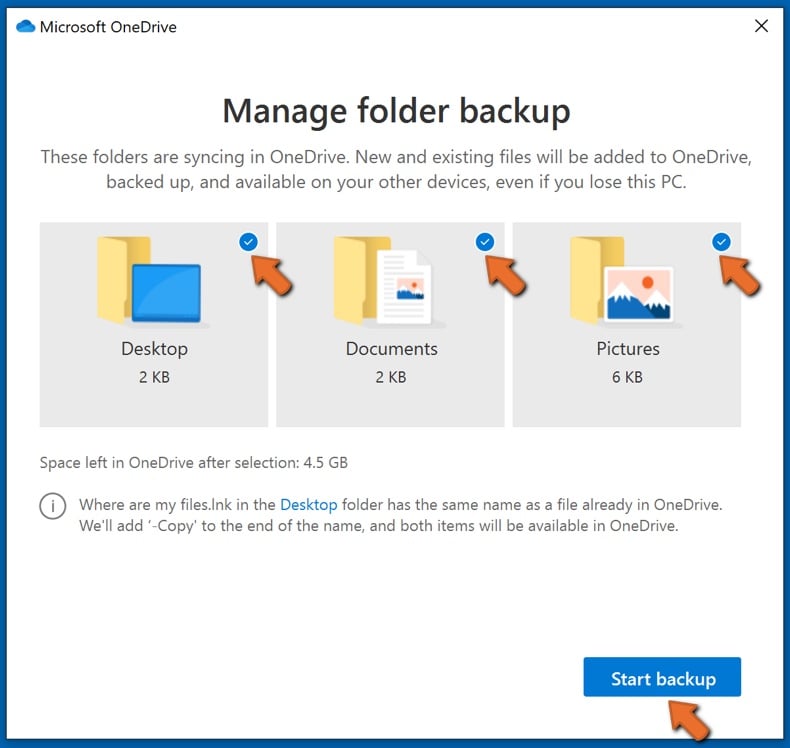
In this menu, you can choose to backup the Desktop and all of the files on it, and Documents and Pictures folders, again, with all of the files in them. Click Start backup.
Now, when you add a file or folder in the Desktop and Documents and Pictures folders, they will be automatically backed up on OneDrive.
To add folders and files, not in the locations shown above, you have to add them manually.
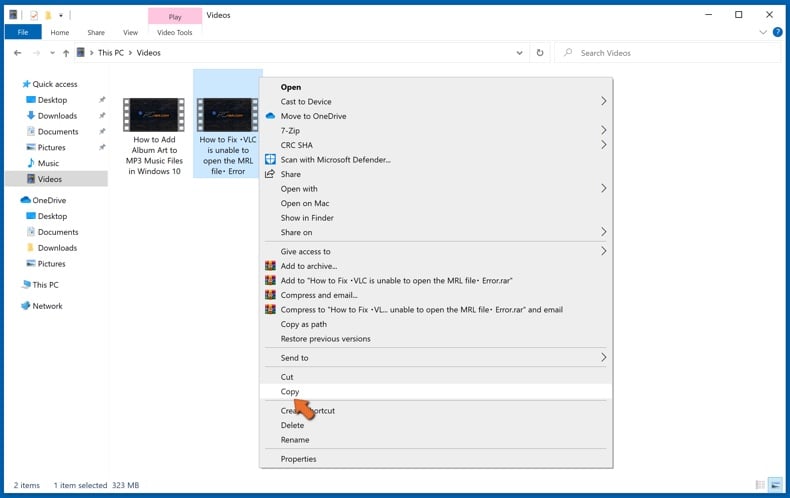
Open File Explorer and navigate to the location of the folder/file you want to backup. Select the item, right-click it, and click Copy.
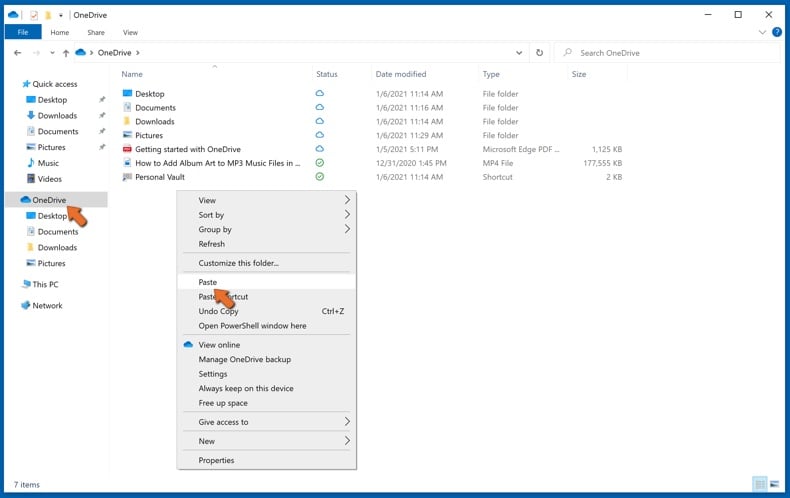
Then, navigate to OneDrive, right-click anywhere in the window and click Paste. Alternatively, you can just drag and drop a file into OneDrive. OneDrive will automatically create a backup of the folder/file.
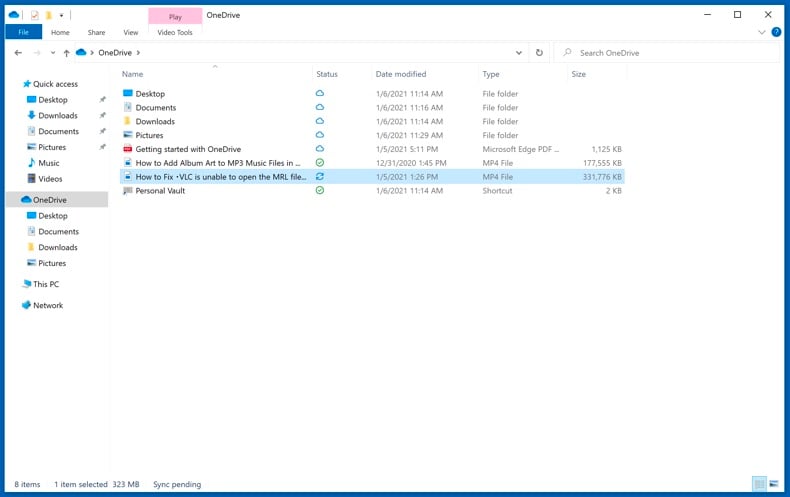
All of the files added to the OneDrive folder are backed up in the cloud automatically. The green circle with the checkmark in it indicates that the file is available both locally and on OneDrive and that the file version is the same on both. The blue cloud icon indicates that the file has not been synced and is available only on OneDrive. The sync icon indicates that the file is currently syncing.
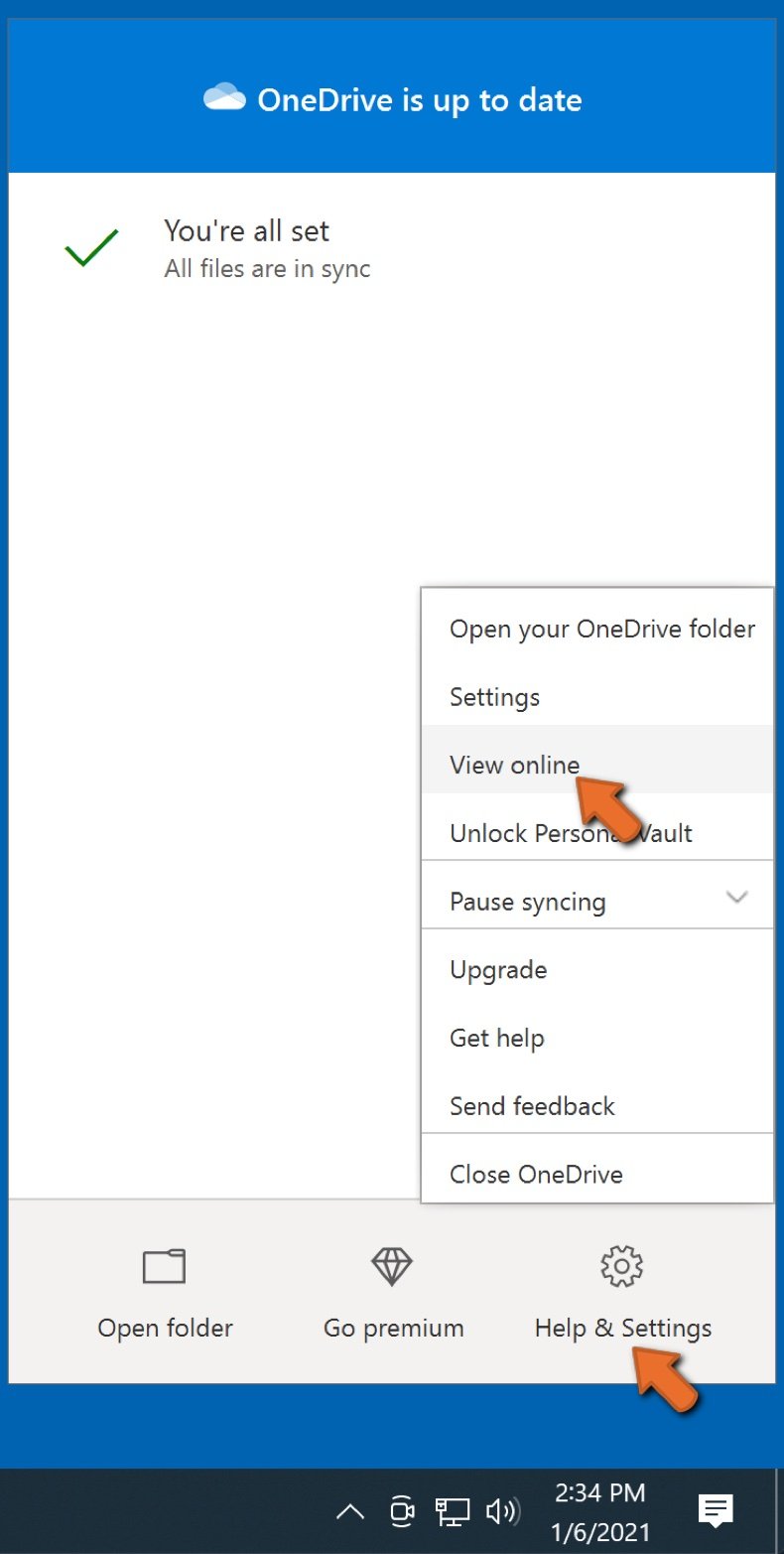
To access files only located on OneDrive online, go to the Help & Settings drop-down menu and select View online.
Step 2: Restore corrupted files.
OneDrive makes sure that the files stay in sync, so the version of the file on the computer is the same version on the cloud. However, if ransomware has encrypted your files, you can take advantage of OneDrive’s Version history feature that will allow you to restore the file versions prior to encryption.
Microsoft 365 has a ransomware detection feature that notifies you when your OneDrive files have been attacked and guide you through the process of restoring your files. It must be noted, however, that if you don’t have a paid Microsoft 365 subscription, you only get one detection and file recovery for free.
If your OneDrive files get deleted, corrupted, or infected by malware, you can restore your entire OneDrive to a previous state. Here’s how you can restore your entire OneDrive:
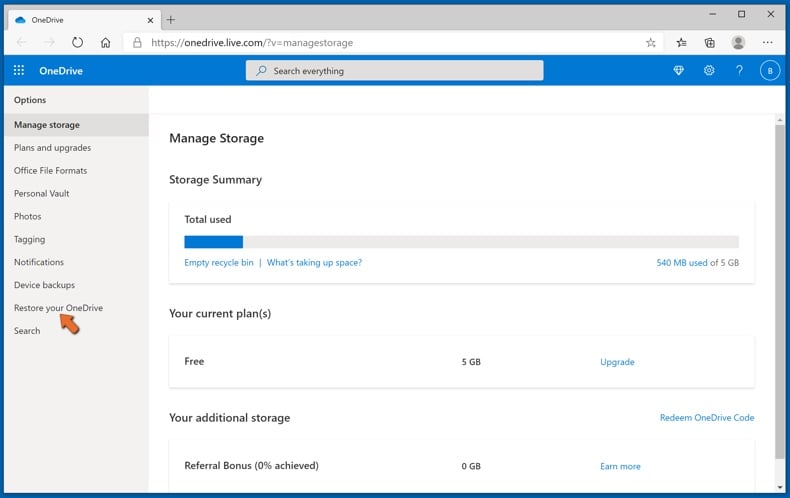
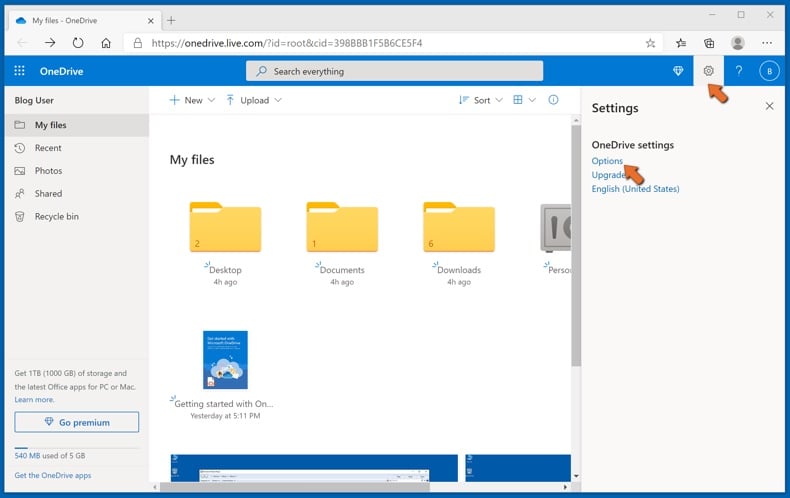
1. If you're signed in with a personal account, click the Settings cog at the top of the page. Then, click Options and select Restore your OneDrive.
If you're signed in with a work or school account, click the Settings cog at the top of the page. Then, click Restore your OneDrive.
2. On the Restore your OneDrive page, select a date from the drop-down list. Note that if you're restoring your files after automatic ransomware detection, a restore date will be selected for you.
3. After configuring all of the file restoration options, click Restore to undo all the activities you selected.
The best way to avoid damage from ransomware infections is to maintain regular up-to-date backups.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion