Su Ordenador Está Bloqueado Scam
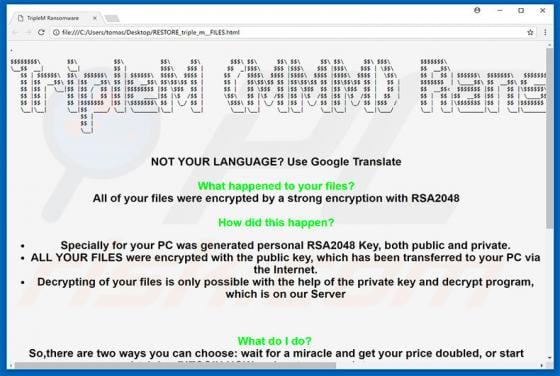
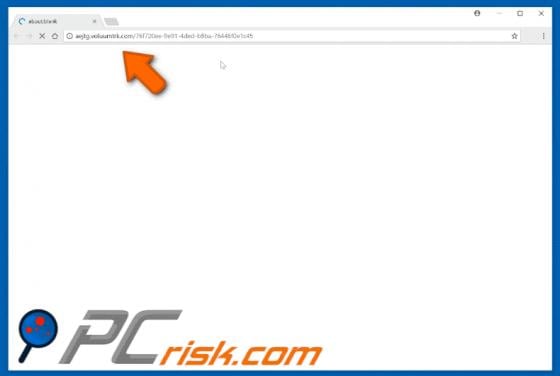
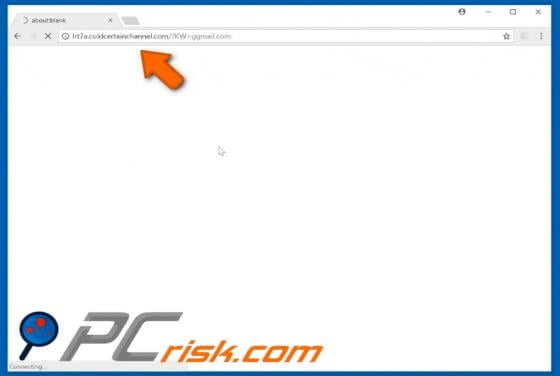
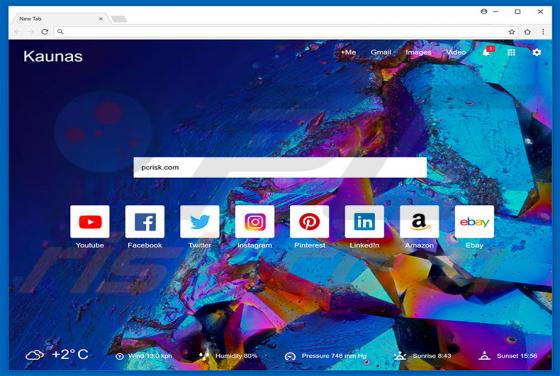
"Su Ordenador Está Bloqueado" is another fake error message displayed by a deceptive website. According to our research, users are redirected to this website by various potentially unwanted programs (PUPs) without their consent. In most cases, PUPs infiltrate systems without permission. In additi