System Keeper Unwanted Application
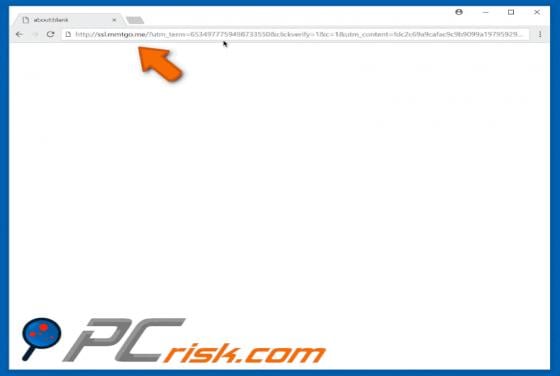
System Keeper is a rogue application that supposedly helps to remove junk files, optimize the system, and eliminate various errors and threats. Judging on appearance alone, System Keeper may seem legitimate and useful, however, this app is classed as a potentially unwanted program (PUP), since it