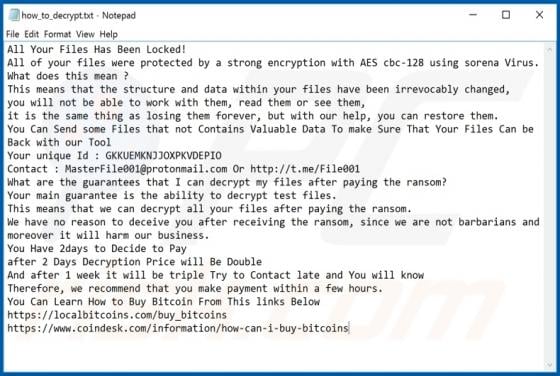
Dewar Ransomware
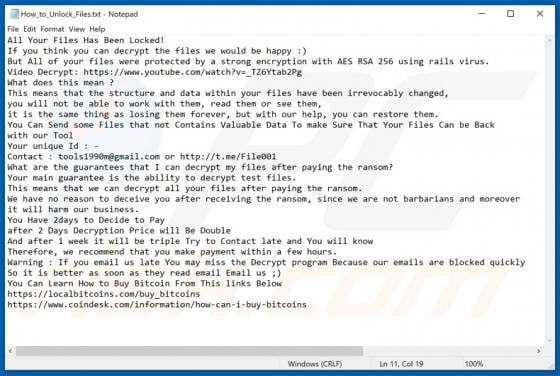
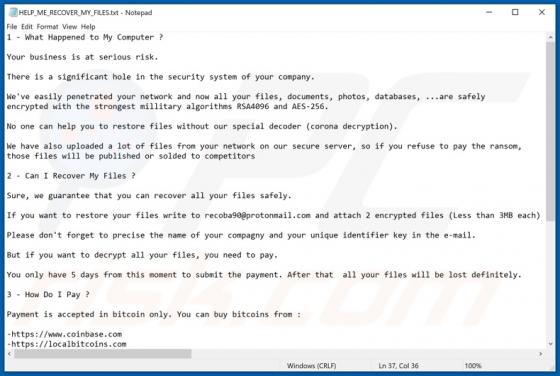
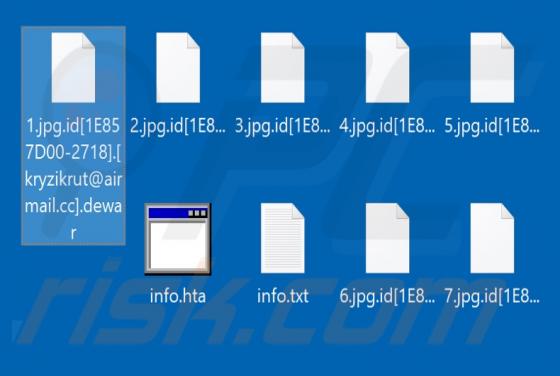
Dewar is a malicious program belonging to the Phobos ransomware family. Systems infected with this malware have their data encrypted and users receive ransom demands for decryption. During the encryption process, all affected files are renamed according to the following pattern: original filename,