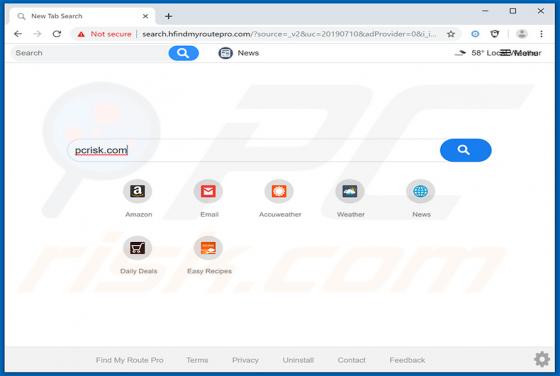
Find My Route Browser Hijacker
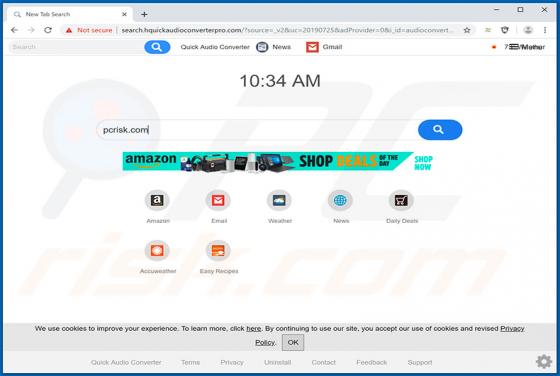
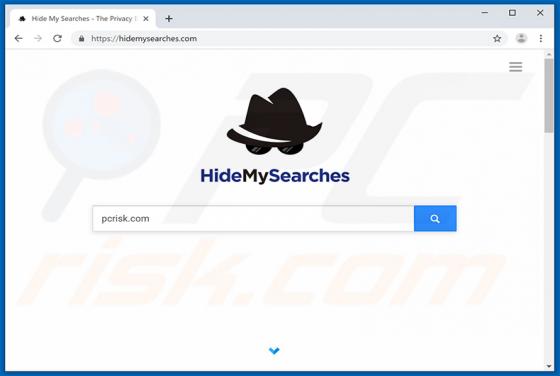
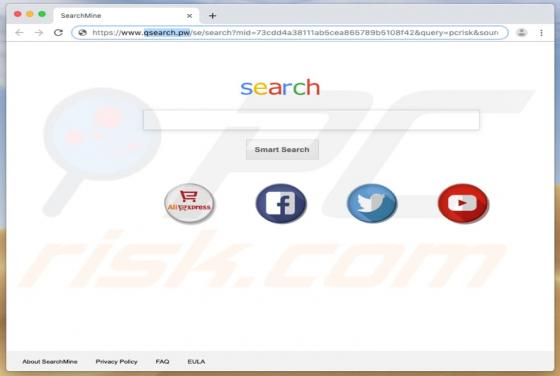
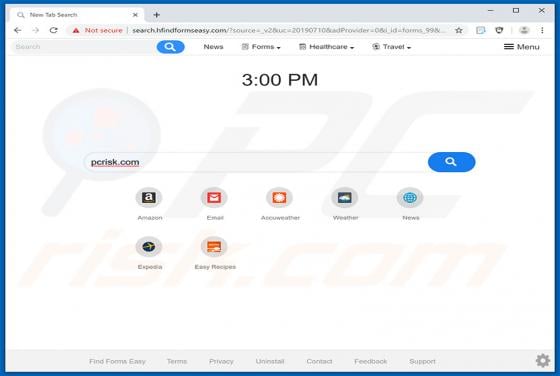
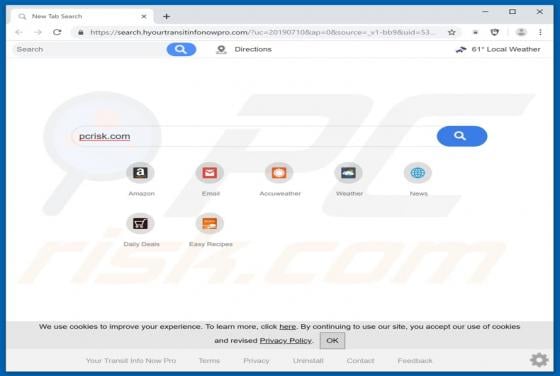
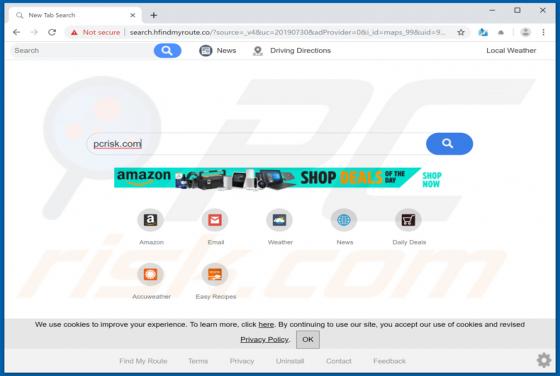
Find My Route is advertised as an application that provides free and quick access to driving directions and maps. This is supposedly a legitimate app, however, it is categorized as a browser hijacker, a potentially unwanted app (PUA). During the installation process, another PUA called Hide My Sea