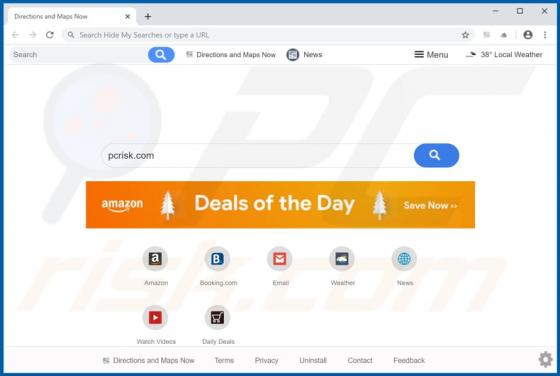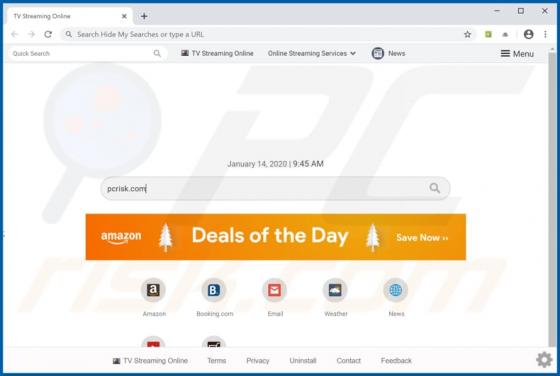
TV Sreaming Online Browser Hijacker
TV Streaming Online is one of many applications that gather browsing data and promote a fake search engine (in this case, search.watch-tvlivetab.com) by changing browser settings. Apps of this type are classed as browser hijackers and potentially unwanted applications (PUAs), since people usually