Ntformetog.fun Ads
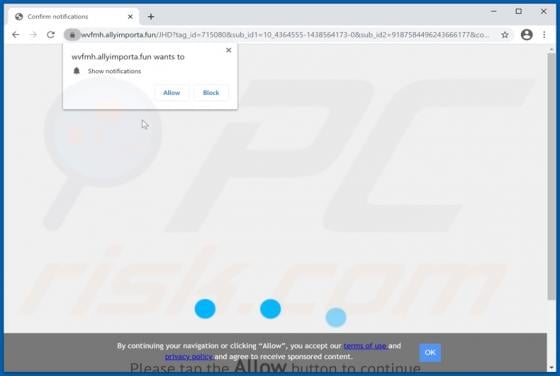
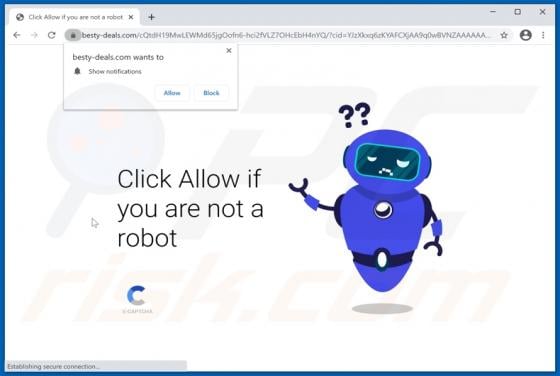
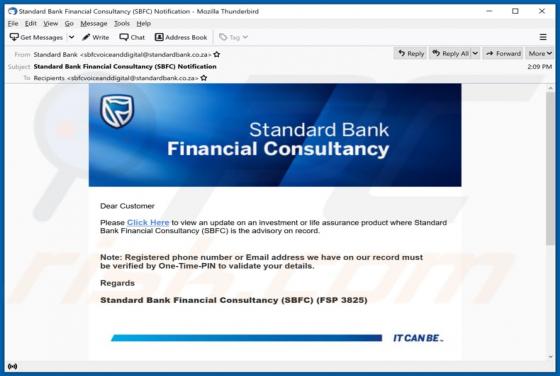
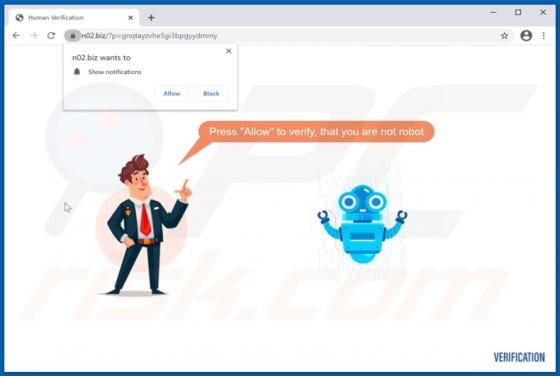
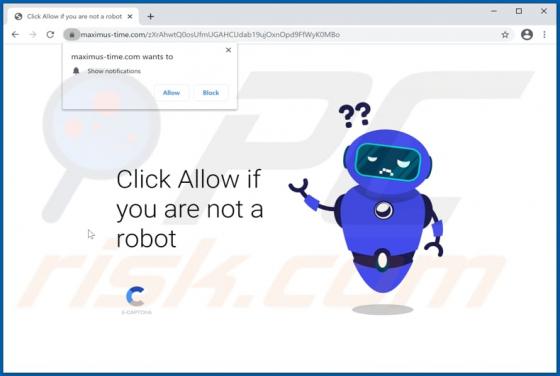
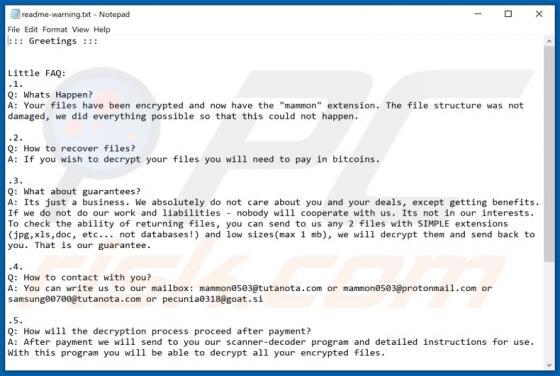
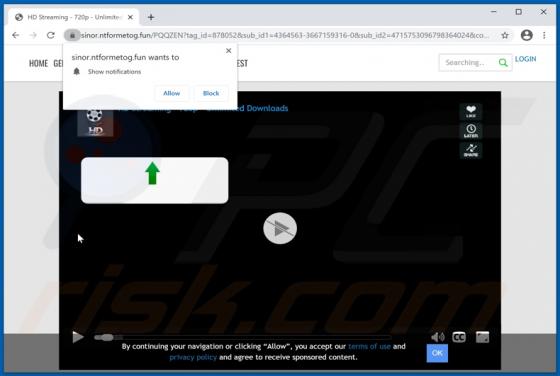
Ntformetog[.]fun is an untrustworthy website, which operates by presenting visitors with dubious material and/or redirecting them to different unreliable/malicious pages. Sites like ntformetog[.]fun, n02.biz, maximus-time.com, video-change.digital, and thousands of other untrustworthy webpages are