System Smart Security
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What is System Smart Security?
System Smart Security is malicious software installed by tricking computer users into believing that their computers are infected with viruses and that this program will help to remove them. This fake computer scanner is propagated via infected websites.
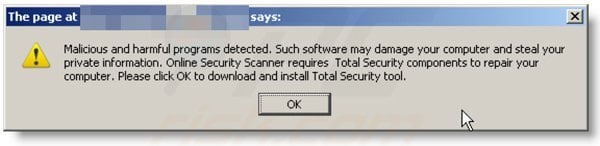
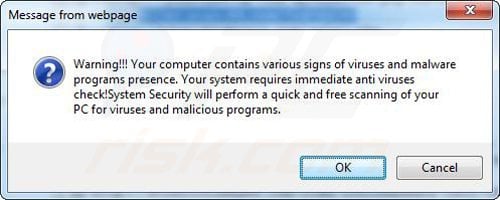
In most cases, when you enter these sites, you will observe a fake security scan running and reporting infections on your computer.

When you start your computer you will see the main window of this rogue scanner performing a security check-up. This fake scanner will report that your computer is infected with multiple spyware and malware.
If you then click 'Remove All', you will be asked to purchase a full version of the program. You should not buy this program, it is scam.
The scans and security warning messages are fake, and the program merely imitates the process of a security scan. System Smart Security attempts to scare you into purchasing a non-existent license.
Remove this rogue scanner from your system as soon as you notice this fake program. If you have already purchased System Smart Security, contact your credit card company and explain that you have been tricked into purchasing a fake computer security scanner.
This fake security software is derived from a large family of rogue applications called "FakeVimes". Programs from this family share the same interface and use similar tactics to infect users' computers.
In fact, System Smart Security does not actually scan your PC for security threats - the processes displayed by this rogue software are imitated to coerce you into buying a full version.
The following fake security messages will be generated by System Smart Security:
"System warning. No real-time malware, spyware, or virus protection was found. Click here to activate."
"Warning! Identity theft attempt detected. Hidden connection IP: 128.154.26.11 Target: Microsoft Corporation keys."
"Warning Warning! Virus detected."
These security warnings are fake. System Smart Security should be removed from your computer as soon as possible.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is System Smart Security?
- STEP 1. Remove System Smart Security using a registration key.
- STEP 2. Remove System Smart Security using Safe Mode with Networking.
- STEP 3. Remove System Smart Security manually by deleting files and registry entries.
Automatic removal of System Smart Security:
Before downloading, enter the System Smart Security registration key U2FD-S2LA-H4KA-UEPB in the registration window. It will not remove the infection, but will enable some of the disabled Windows features.
System Smart Security virus removal instructions on infected PC
1. Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK.
During your computer starting process press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, then select Safe Mode with Networking from the list.

Video showing how to start Windows in "Safe Mode with Networking":
Windows XP:
Windows 7:
Windows 8:
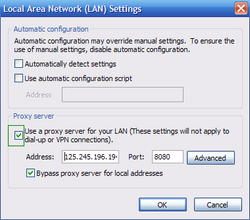
2. Open Internet Explorer, click Tools and select Internet Options. Select "Connections".


3.Click LAN settings, if 'Use a proxy server for your LAN' is checked, uncheck it and press OK.

4. Download and install spyware remover to completely remove the infection.
5. After you have cleaned your computer. Check your Hosts file.
Locate your Hosts file. You should find it at %systemroot% \system32\drivers\etc (most commonly it will be c:\windows\system32\drivers\etc) Open the Hosts file with Notepad and check that no unusual values have been added to it.
These are the default values. Yours should be the same.
For Windows XP
# Copyright (c) 1993-1999 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
127.0.0.1 localhost
For Windows Vista
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
127.0.0.1 localhost
::1 localhost
For Windows 7
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# localhost name resolution is handle within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
If you are unable to remove System Smart Security, you can use these manual removal instructions. Use them at your own risk, since if you do not have strong computer knowledge, you could harm your operating system.
Use them only if you are an experienced computer user. (Instructions on how to end processes, remove registry entries...)
End these System Smart Security processes:
[random].exe
Delete these System Smart Security registry entries:
HKEY_CLASSES_ROOT\PersonalSS.DocHostUIHandlerHKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download “RunInvalidSignatures” = “1?HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings “ProxyServer” = “http=127.0.0.1?HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “System Smart Security?HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “[random].exe?HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options “Debugger” = “svchost.exe”
Delete these System Smart Security files:
%Documents and Settings%\All Users\Application Data\[random]\%Documents and Settings%\All Users\Application Data\[random]\[random].exe%Documents and Settings%\All Users\Application Data\[random]\[random].mof%Documents and Settings%\All Users\Application Data\[random]\[random].dll%Documents and Settings%\All Users\Application Data\[random]\[random].ocx%Documents and Settings%\All Users\Application Data\[random]\[random]\%UserProfile%\Application Data\System Smart Security\%UserProfile%\Application Data\System Smart Security\cookies.sqlite%UserProfile%\Application Data\System Smart Security\Instructions.ini
Summary:
The fake antivirus programs (also known as "rogue antivirus programs" or "scareware") are applications that tries to lure computer users into paying for their non-existent full versions to remove the supposedly detected security infections (although the computer is actually clean). These bogus programs are created by cyber criminals who design them to look as legitimate antivirus software. Most commonly rogue antivirus programs infiltrate user's computer using poop-up windows or alerts which appear when users surf the Internet. These deceptive messages trick users into downloading a rogue antivirus program on their computers. Other known tactics used to spread scareware include exploit kits, infected email messages, online ad networks, drive-by downloads, or even direct calls to user's offering free support.
A computer that is infected with a fake antivirus program might also have other malware installed on it as rogue antivirus programs often are bundled with Trojans and exploit kits. Noteworthy that additional malware that infiltrates user's operating system remains on victim's computer regardless of whether a payment for a non-existent full version of a fake antivirus program is made. Here are some examples of fake security warning messages that are used in fake antivirus distribution:
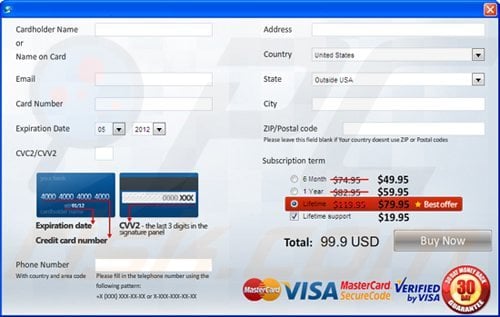
Computer users who are dealing with a rogue security software shouldn't buy it's full version. By paying for a license key of a fake antivirus program users would send their money and banking information to cyber criminals. Users who have already entered their credit card number (or other sensitive information) when asked by such bogus software should inform their credit card company that they have been tricked into buying a rogue security software. Screenshot of a web page used to lure computer users into paying for a non-existent full version of system smart security rogue and other rogue antivirus programs:
To protect your computer from system smart security rogue and other rogue antivirus programs users should:
- Keep their operating system and all of the installed programs up-to-date.
- Use legitimate antivirus and anti-spyware programs.
- Use caution when clicking on links in social networking websites and email messages.
- Don't trust online pop-up messages which state that your computer is infected and offers you to download security software.
Symptoms indicating that your operating system is infected with a fake antivirus program:
- Intrusive security warning pop-up messages.
- Alerts asking to upgrade to a paid version of a program to remove the supposedly detected malware.
- Slow computer performance.
- Disabled Windows updates.
- Blocked Task Manager.
- Blocked Internet browsers or inability to visit legitimate antivirus vendor websites.
If you have additional information on system smart security rogue or it's removal please share your knowledge in the comments section below.

▼ Show Discussion