Do not trust "Is Visiting A More Convenient Way To Reach" scam emails
Phishing/ScamAlso Known As: "Is Visiting A More Convenient Way To Reach" sextortion scam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "Is Visiting A More Convenient Way To Reach"?
After reading the "Is Visiting A More Convenient Way To Reach" email, we determined that it is spam. This mail promotes a sextortion scam.
The email claims that the sender has infected the recipient's smartphone and was monitoring them. In addition to obtaining sensitive data, the sender supposedly filmed a sexually explicit video of the recipient. They threaten to leak it if they are not paid.
It must be emphasized that all the claims made by this spam mail are false. Therefore, it poses no threat to the recipients.
"Is Visiting A More Convenient Way To Reach" email scam overview
This spam mail accuses the recipient of having poor Internet browsing habits. The sender claims to have infected an app often used by the recipient with malware, which was then used to gain access to their Apple or Android smartphone.
The trojan was utilized to monitor the user. When they were browsing adult-oriented websites, the nonexistent malware was used to record the screen and the user.
The recipient is instructed to pay 1950 USD in Bitcoin cryptocurrency. If they refuse – the sexually explicit video of the user will be sent to their phone, email, and social media contacts. Twenty-four hours from the moment that the email was opened are given for complying with the demands.
It must be reiterated that the information in this letter is entirely false. Hence, the sender has not infected any devices with malware, nor do they have recipients' information (e.g., no videos). Therefore, all the threats made by the email are empty.
Victims of the "Is Visiting A More Convenient Way To Reach" campaign experience financial loss. Since cryptocurrency transactions are practically untraceable – they cannot be reversed, which means that victims cannot recover their funds.
| Name | "Is Visiting A More Convenient Way To Reach" sextortion scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | If the email sender is not paid, a sexually explicit video featuring the recipient will be sent to their contacts. |
| Cyber Criminal Cryptowallet Address | bc1q23270f3wyklqz2v2t4kh3scg7k670vd4ylw8cu, bc1qjnz6xyudwfy8f3dkprw7zjwp3tw3y9uvdz6y6j, bc1qdalm59ahv8r9hqc8cjceh6h2t0xamep04aheax, bc1qeaxp7pc44xjv68ldzxnvgel333r7xp03l640c2, 19v1ujT6yT5wpamBsHYTx7b5yVprM2pCqo, bc1qxh5zs087ls5w8fszhgl5h3ml97pcz7rjazd43a, 1NSaKPShj9t3rWVQBUit7VhBWmXUY8HHyC, 14ow9AegSM5hX7Gn8wAaF4Uhjm2Bdmk4UP, 1DeT674Vjspp377UJAdThVDjYUQPXy5TdU, 1FBdyGictLn9e25j7hsCjhzcupxQbhNwH7, 12rgJcvSswfVec6FMMmphTvXRVQNmAL6BD, 1M6Qf7LdutNL88zmfM9kE9jG2C5QWzPsBQ, 13fmUAMFGJb9mbv1zX84xcG9TwuvTxf7Hb, 1HDN178FThrkYtdnJVsfZLYUEZ7dT6UDNr, 1Pk9fyA7Ph74fX36vLKdZrHd4nNzRjcmt2 |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Sextortion spam campaign examples
We have written about thousands of spam campaigns; "Malware On Porn Website", "You Are One Of A Kind", "Your System Has Been Cracked", and "Internet Is A Dangerous Place" are just some of our articles on sextortion emails.
Aside from this kind of scam, spam is used to facilitate phishing, tech support, refund, inheritance, lottery, and other schemes. Deceptive mail is also used to proliferate malware.
While the commonly held belief that these emails are poorly crafted and full of grammatical/spelling errors is not untrue, it is not always the case. Spam mail can be competently crafted and even believably disguised as messages from legitimate entities (e.g., service providers, companies, institutions, authorities, etc.).
How do spam campaigns infect computers?
Spam campaigns proliferate malware by distributing malicious files. They can be attached to or linked inside the emails/messages. These files come in various formats, e.g., documents (PDF, Microsoft Office, Microsoft OneNote, etc.), archives (ZIP, RAR, etc.), executables (.exe, .run, etc.), JavaScript, and so on.
The malware download/installation chain is triggered once such a file is opened. Some formats need extra interaction to initiate system infection processes. For example, Microsoft Office files require users to enable macro commands (i.e., editing/content), while OneNote documents need them to click embedded links/files.
How to avoid installation of malware?
It is essential to exercise caution with incoming emails, DMs/PMs, SMSes, and other messages. We advise against opening attachments or links found in dubious/irrelevant mail, as they can be malicious.
It must be mentioned that malware is not spread only through spam mail. Therefore, we recommend being careful while browsing, as the Internet is rife with well-disguised fraudulent and dangerous content.
Another recommendation is to download only from official and trustworthy sources. Additionally, all programs must be activated and updated using legitimate functions/tools, as illegal product activation ("cracking") tools and third-party updaters can contain malware.
It is paramount for device integrity and user safety to have a dependable anti-virus installed and kept updated. Security software must be used to perform regular system scans and to remove threats and issues. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "Is Visiting A More Convenient Way To Reach" spam email letter:
***********
Is visiting ******** a more convenient way to reach in case you don't act
Have been here before?
I suggest you read this message carefully. Take a minute to relax, breathe, and really dig into it. 'Cause we're about to discuss a deal between you and me, and I don't play games. You don't know me but I know ALOT about you and you must be wondering how, correct?
Well, You've been treading on thin ice with your browsing habits, scrolling through those filthy videos and clicking on links, stumbling upon some not-so-safe sites. I actually placed a Spyware called "Pegasus" on a app you frequently use. Pegasus is a spyware that is designed to be covertly and remotely installed on mobile phones running iOS and Android. And while you were busy enjoying those videos, your smartphone initiated working as a RDP (Remote Control) which allowed me complete control over your device. I can look at everything on your display, flick on your cam and mic, and you wouldn't even suspect a thing. Oh, and I've got access to all your emails, contacts, and social media accounts too.
What did I do?
Been keeping tabs on your pathetic life for a while now. It's just your bad luck that I discovered your bad deeds. I gave in more days than I probably should have exploring into your personal life. Extracted quite a bit of juicy info from your system. and I've seen it all. Yeah, Yeah, I've got footage of you doing embarrassing things in your room (nice setup, by the way). I then developed videos and screenshots where on one side of the screen, there's whatever garbage you had been playing, and on the other half, its someone jerking off.
With simply a click, I can send this garbage to every single of your contacts.
What should you do?
I see you are getting anxious, but let's get real. In good faith, I want to wipe the slate clean, and allow you to continue with your life and forget you ever existed. I am about to offer you two options. Either ignore this warning (bad for you and your family) or pay me a small amount. Let us examine those two options in details.
Alternative one is to turn a deaf ear my e mail. Let us see what will happen if you opt this option. I will send your video to all of your contacts. The video was lit, and I can't even fathom the humiliation you'll endure when your colleagues, friends, and fam check it out. But hey, that's life, ain't it? Don't be playing the victim
Wise Second Option is to pay me, and be confidential about it. We'll call it my "privacy charges". Lets discuss what happens if you opt this choice. Your dirty secret will remain private. I'll destroy all the data and evidence once you send payment. You have to make the payment via Bitcoin only. Pay attention, I'm telling you straight:
'We gotta make a deal'. I want you to know Im coming at you with good intentions. My promises are non-negotiable.
Transfer Amount: USD 1950
My BTC Address: 1NSaKPShj9t3rWVQBUit7VhBWmXUY8HHyC
Or, (Here's your Bitcoin QR code, you can scan it):
Let me tell ya, it's peanuts for your tranquility.
Important: You got one day to sort this out. (I've a unique pixel within this e-mail, and right now I know that you have read this email message). My system will catch that Bitcoin payment and wipe out all the dirt I got on you. Don't even think about replying to this, it's pointless. The email and wallet are custom-made for you, untraceable. I don't make mistakes, Robert. If I suspect that you've shared or discussed this email with anyone abu, these or view is any se geting sept your contacts. And don't even think about tuming off
Honestly, those online tips about covering your camera aren't as useless as they seem.
Don't dwell on it. Take it as a little lesson and keep your guard up in the future.
Appearance of the "Is Visiting A More Convenient Way To Reach" spam email (GIF):
Other examples of emails from "Is Visiting A More Convenient Way To Reach" spam campaign:
Sample 1:
Text presented within:
I know that calling ******** or visiting ********. would be a better way to contact you if you
don’t cooperate. Don’t even try to hide from this. You’ve no idea what I’m capable of in ********.
I suggest you read this message carefully. Take a moment to chill, breathe, and analyze it thoroughly. 'Cause we’re about to
discuss a deal between you and me, and I ain’t playinggames. You don’t know anythingabout me however I know you
very well and right now, you are thinkinghow, correct?Well, you’ve been a bit careless lately, scrollingthrough those videos and clickingon links, stumblingupon some not-sosafe sites. I actually placed a Malware on a porn website & you accessed it to watch(you know what I mean). And while
you were busy enjoyingour videos, your device initiated workingas a RDP (Remote Protocol) which provided me total
control over your device. I can peep at everythingon your screen, switch on your cam and mic, and you wouldn’t even
suspect a thing. Oh, and I’ve got access to all your emails, contacts, and social media accounts too.Been keepingtabs on your pathetic existence for a while now. It is just your bad luck that I saw your blunder. I gave in
more days than I probably should have digginginto your personal life. Extracted quite a bit of juicy info from your
system. and I’ve seen it all. Yeah, Yeah, I’ve got footage of you doingfilthy things in your house (nice setup, by the way).
I then developed videos and screenshots where on one side of the screen, there’s whatever garbage you were playing, and
on the other half, its you jerkingoff. With just a click, I can send this garbage to all of your contacts.Your confusion is clear, but don’t expect sympathy. Actually, I’m ready to wipe the slate clean, and allow you to move on
with your life and wipe your slate clean. I will present you two alternatives.First Option is to turn a deaf ear this e-mail. You should know what is goingto happen if you pick this option. I will send
your video to all of your contacts. The video was lit, and I can’t even fathom the humiliation you’ll endure when your
colleagues, friends, and fam watch it. But hey, that’s life, ain’t it? Don’t be playingthe victim here.Second option is to pay me, and be confidential about it. We’ll call this my “confidentiality charges”. let me tell you what
will happen when you opt this choice. Your filthy secret remains private. I will wipe everythingclean once you send
payment. You have to make the payment via Bitcoin only. Pay attention, I’m tellingyou straight: ‘We gotta make a deal’. I
want you to know I’m comingat you with good intentions. I will keep my end of the bargain.Amount to be sent: $1950
BITCOIN ADDRESS IS: 14ow9AegSM5hX7Gn8wAaF4Uhjm2Bdmk4UPLet me tell ya, it’s peanuts for your tranquility.
Notice: You got one day to sort this out and I will only accept Bitcoins (I’ve a specific pixel within this e-mail, and right
now I know that you have read through this email message). My system will catch that Bitcoin payment and wipe out all
the dirt I got on you. Don’t even think about replyingto this or negotiating, it’s pointless. The email and wallet are
custom-made for you, untraceable. If I suspect that you’ve shared or discussed this email with anyone else, your shitty
video will instantly start gettingsent to your contacts. And don’t even think about turningoff your phone or resettingit to
factory settings. It’s pointless. I don’t make mistakes, ********.Can you notice somethinghere?
-
Honestly, those online tips about coveringyour camera aren’t as useless as they seem. I am waitingfor my payment…
Sample 2:
Text presented within:
Is visiting ******** a more convenient way to reach in case you don't act
It's important you pay attention to this message right now. Take a moment to chill, breathe, and analyze it thoroughly. 'Cause we're about to discuss a deal between you and me, and I don't play games. You don't know me whereas I know EVERYTHING about you and right now, you are wondering how, right?
Well, you've been treading on thin ice with your browsing habits, clicking through those girlie videos and venturing into the darker corners of cyberspace. I installed a Malware on a porn website and you accessed it to watch (know what I mean?). And while you were busy enjoying those videos, your system started out functioning as a RDP (Remote Device) which provided me total accessibility to your device. I can peep at everything on your display, switch on your cam and mic, and you wouldn't even suspect a thing. Oh, and I have got access to all your emails, contacts, and social media accounts too.
Been keeping tabs on your pathetic life for a while now. It's simply your misfortune that I accessed your blunder. I put in more time than I probably should have investigating into your life. Extracted quite a bit of juicy info from your system, and I've seen it all. Yeah, Yeah, I've got footage of you doing embarrassing things in your house (nice setup, by the way). I then developed videos and screenshots where on one side of the screen, there's the videos you had been watching, and on the other part, its your vacant face. With simply a single click, I can send this video to all of your contacts.
I feel your worry and confusion. In good faith, I am ready to wipe the slate clean, and let you get on with your daily life and forget you ever existed. I will provide you two options.
First Alternative is to disregard this e mail. Let's see what is going to happen if you select this path. I will send your video to your entire contacts. The video is straight fire, and I can't even fathom the embarrassment you'll endure when your colleagues, friends, and fam watch it. But hey, that's life, ain't it? Don't be playing the victim here.
Option 2 is to pay me, and be confidential about it. We'll name this my “keep the secret charges”. Lets discuss what will happen if you go with this path. Your secret will remain your secret. I'll wipe everything clean once you come through with the payment. You'll transfer the payment via Bitcoin only. Pay attention, I'm telling you straight: 'We gotta make a deal'. I want you to know I'm coming at you with good intentions. I'm a person of integrity.
Required Amount: $2000
My Bitcoin Address: bc1qh0nvkfghlqyfy2awzkaccp3ytc4dnzez8laxe8
Let me tell ya, it's peanuts for your tranquility.
Notice: You have one day to transfer the amount and I will only accept Bitcoins (I have a special pixel within this email message, and now I know that you've read this e-mail). My system will catch that Bitcoin payment and wipe out all the dirt I got on you. Don't even think about replying to this or negotiating, it's pointless. The email and wallet are custom-made for you, untraceable. If I catch that you've shared or discussed this email with someone else, the garbage will instantly start getting sent to your contacts. And don't even think about turning off your phone or resetting it to factory settings. It's pointless. I don't make mistakes, -.
Honestly, those online tips about covering your camera aren't as useless as they seem. I am waiting for my payment..
Sample 3:
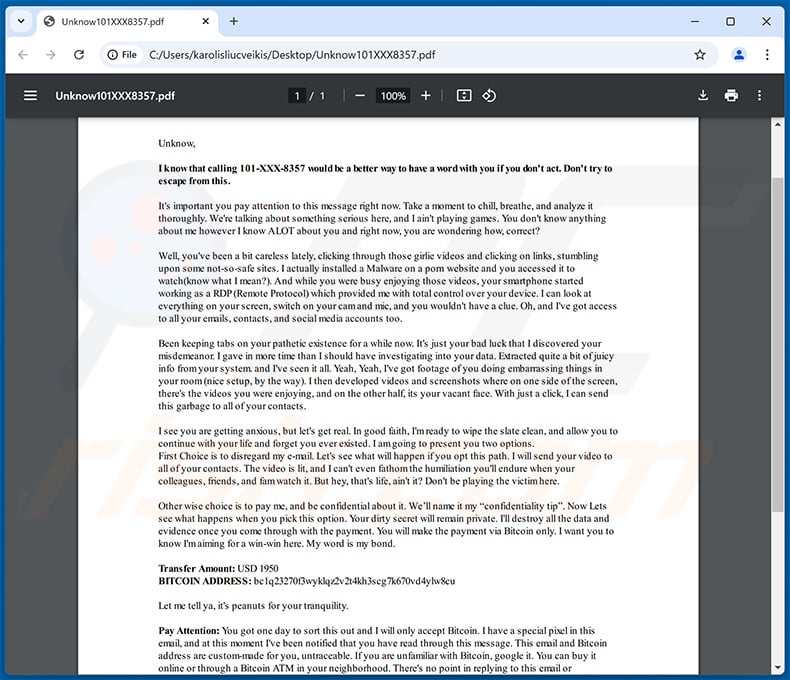
Text presented within:
Unknow,
I knowthat calling 101-XXX-8357 would be a better way to have a wordwith you if you don't act. Don't try to
escape from this.
It's important you pay attention to this message right now. Take a moment to chill, breathe, and analyze it
thoroughly. We're talking about something serious here, and I ain't playing games. You don't know anything
about me however I know ALOT about you and right now, you are wondering how, correct?
Well, you've been a bit careless lately, clicking through those girlie videos and clicking on links, stumbling
upon some not-so-safe sites. I actually installed a Malware on a porn website and you accessed it to
watch(know what I mean?). And while you were busy enjoying those videos, your smartphone started
working as a RDP (Remote Protocol) which provided me with total control over your device. I can look at
everything on your screen, switch on your camand mic, and you wouldn't have a clue. Oh, and I've got access
to all your emails, contacts, and social media accounts too.
Been keeping tabs on your pathetic existence for a while now. It's just your bad luck that I discovered your
misdemeanor. I gave in more time than I should have investigating into your data. Extracted quite a bit of juicy
info fromyour system. and I've seen it all. Yeah, Yeah, I've got footage of you doing embarrassing things in
your room(nice setup, by the way). I then developed videos and screenshots where on one side of the screen,
there's the videos you were enjoying, and on the other half, its your vacant face. With just a click, I can send
this garbage to all of your contacts.
I see you are getting anxious, but let's get real. In good faith, I'mready to wipe the slate clean, and allow you to
continue with your life and forget you ever existed. I amgoing to present you two options.
First Choice is to disregard my e-mail. Let's see what will happen if you opt this path. I willsend your video to
all of your contacts. The video is lit, and I can't even fathomthe humiliation you'll endure when your
colleagues, friends, and famwatch it. But hey, that's life, ain't it? Don't be playing the victimhere.
Other wise choice is to pay me, and be confidential about it. We’ll name it my “confidentiality tip”. Now Lets
see what happens when you pick this option. Your dirty secret will remain private. I'll destroy all the data and
evidence once you come through with the payment. You will make the payment via Bitcoin only. I want you to
know I'maiming for a win-win here. My word is my bond.
Transfer Amount: USD 1950
BITCOIN ADDRESS: bc1q23270f3wyklqz2v2t4kh3scg7k670vd4ylw8cu
Let me tell ya, it's peanuts for your tranquility.
Pay Attention: You got one day to sort this out and I will only accept Bitcoin. I have a special pixel in this
email, and at this moment I've been notified that you have read through this message. This email and Bitcoin
address are custom-made for you, untraceable. If you are unfamiliar with Bitcoin, google it. You can buy it
online or through a Bitcoin ATM in your neighborhood. There's no point in replying to this email or
negotiating, it's pointless my price is fixed. As soon as you send the complete payment, my systemwill inform
me and I will wipe out all the dirt I got on you. Remember if I notice that you've shared or discussed this
message with someone else, the sh**y video will instantly start getting sent to your contacts and I will post a
physical tape to all of your neighborhood next week. And don't even think about turning off your phone or
resetting it to factory settings, I already have all your data. I don't make mistakes, Unknow.
Honestly, those online tips about covering your camera aren't as useless as they seem. Now, I amwaiting for
my payment..
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "Is Visiting A More Convenient Way To Reach" sextortion scam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
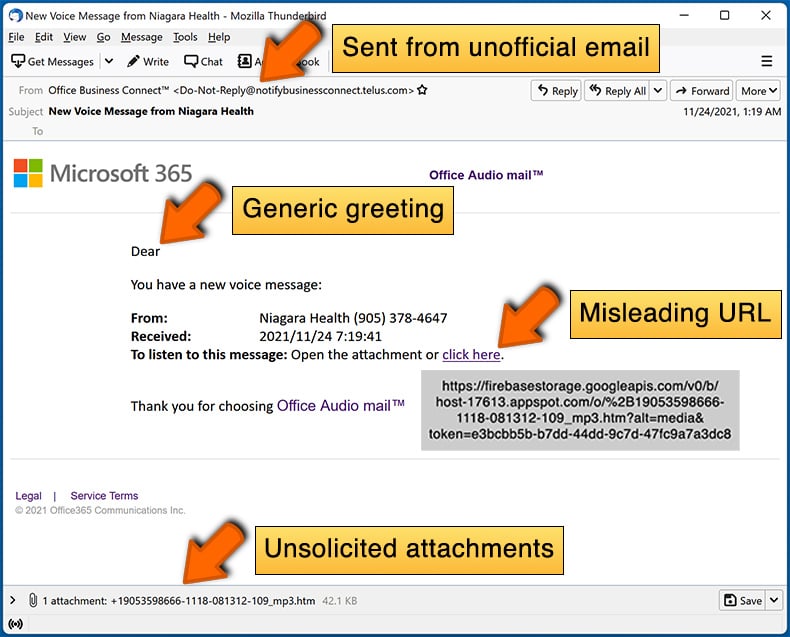
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:
What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal, even if they include details relevant to the recipients. If such information is present, it is likely to have been acquired through publicly available sources or phishing scams. Cyber criminals distribute this mail in large-scale campaigns – hence, thousands of users receive identical (or incredibly similar) emails.
Was my computer actually hacked and does the sender have any information?
No, all the claims made by the "Is Visiting A More Convenient Way To Reach" email are false. This means that your devices were not infected by the sender, nor do they have any of your information (including any compromising recordings). Therefore, this email poses no threat.
How did cyber criminals get my email password?
In some cases, cyber criminals use recipients' own email accounts to send them scam messages – this is to create an impression of legitimacy for their false claims. The account passwords are most commonly obtained via phishing scams. It is less likely for this data to have been acquired through a data breach on your or a service provider's end.
I have sent cryptocurrency to the address presented in this email, can I get my money back?
No, cryptocurrency transactions cannot be reversed because of their nearly untraceable nature. Hence, victims of scams like this "Is Visiting A More Convenient Way To Reach" email cannot recover their funds.
I have provided my personal information when tricked by a spam email, what should I do?
If you have provided your log-in credentials – change the passwords of all potentially compromised accounts and inform their official support without delay. And if the disclosed information was of a different personal nature (e.g., ID card details, credit card numbers, etc.) – immediately contact the appropriate authorities.
I have read a spam email but didn't open the attachment, is my computer infected?
No, opening/reading an email poses no infection threat. Devices are infected when malicious attachments or links are opened/clicked.
I have downloaded and opened a file attached to a spam email, is my computer infected?
If the opened file was an executable (.exe, .run, etc.) – most likely, yes – your device was compromised. However, you might have avoided the infection if it was a document (.doc, .xls, .one, .pdf, etc.). These formats may need additional user interaction to initiate system infection processes (e.g., enabling macros, clicking embedded content, etc.).
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is capable of detecting and removing practically all known malware infections. It must be stressed that running a complete system scan is essential since high-end malicious programs typically hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion