How to remove Latrodectus malware from the operating system
TrojanAlso Known As: Latrodectus malware loader
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Latrodectus?
Latrodectus is a type of malware categorized as a loader. Loaders are a class of malicious software designed to infiltrate a target system and execute additional payloads. Once infiltrated, Latrodectus acts as a gateway for more harmful malware to be deployed onto the infected system, thereby exacerbating the potential damage and threat to the victim's privacy and security.

More about Latrodectus
Latrodectus, a loader malware, is capable of executing various types of malicious payloads, including ransomware, Remote Access Trojans (RATs), banking Trojans, information stealers, keyloggers, and other forms of malware. It is known that one of the payloads distributed via Latrodectus is a stealer called Lumma.
Ransomware encrypts data on the victim's system and demands payment for the decryption key, effectively barring users from accessing their own files until the ransom is paid. RATs grant cybercriminals access to infected systems, enabling them to remotely manipulate the victim's computer, pilfer sensitive information, or execute malicious actions without the user's awareness or consent.
Banking Trojans target sensitive financial information, including login credentials and credit card details, on victims' devices. Designed to steal such data, they pose a significant risk to users' financial security and privacy.
Information stealers are designed to clandestinely collect and exfiltrate sensitive information from infected systems, including login credentials, personal documents, and browsing history. They can compromise users' privacy and facilitate identity theft or other forms of cybercrime.
Keyloggers secretly record and log all keystrokes entered by the user, including usernames, passwords, and other sensitive information. They can covertly capture valuable data without the user's knowledge, posing a significant threat to privacy and security.
| Name | Latrodectus malware loader |
| Threat Type | Loader |
| Detection Names | Avast (Win64:Malware-gen), Combo Cleaner (Trojan.GenericKD.71594280), ESET-NOD32 (Win64/Agent.DMO), Kaspersky (VHO:Trojan-Banker.Win64.IcedID.gen), Microsoft (Trojan:Win64/IcedID.XZ!MTB), Full List (VirusTotal) |
| Payload | Lumma, and other threats (e.g., ransomware or Trojans) |
| Symptoms | Loaders are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine until damage is already done. |
| Distribution methods | Infected email attachments, fake Azure (and possibly other) websites, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet, data encryption, monetaru loss, and more. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
In conclusion, Latrodectus represents a significant threat as a loader malware capable of executing various types of malicious payloads. Its ability to infiltrate systems and deploy harmful malware underscores the importance of robust cybersecurity measures to mitigate its impact and protect against potential data breaches and privacy violations.
More examples of malware acting as a loader Ande Loader, PrivateLoader, and DBatLoader.
How did Latrodectus infiltrate my computer?
Latrodectus is commonly distributed through phishing emails, which deceive recipients into visiting websites hosting the malware. These emails often employ social engineering tactics to lure users into clicking on malicious links or downloading infected attachments.
One known example of how the malware is distributed involves a chain of interconnected steps. It starts with a website's contact form email containing a link leading to a counterfeit Azure login page. Once the page is accessed, a JavaScript (JS) file is automatically downloaded onto the user's device.
The JS file then retrieves an installer MSI, which, upon execution, implants a Latrodectus Dynamic Link Library (DLL) onto the system. This DLL is configured for persistence, ensuring its continued presence even after system reboots. Finally, the Latrodectus malware establishes communication with its command-and-control (C2) server, allowing malicious actors remote access to the infected device.
How to avoid installation of malware?
Exercise caution when dealing with unsolicited emails, particularly those containing suspicious links or attachments. Opt for official sources when downloading software and files, avoiding peer-to-peer networks, third-party downloaders, or unofficial websites.
Do not interact with pop-ups, ads, and links (or buttons) while visiting shady pages. Ensure that all your programs, including your operating system, are regularly updated. Additionally, maintain proactive protection by conducting routine malware scans using reliable antivirus software to detect and remove any threats.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Fake Azure site distributing Latrodectus loader:

Examples of spam emails spreading Latrodectus malware:
Sample 1:

Text presented within:
Subject: Submission Confirmation
Full Name: **********
Phone
Number: **********
Email: **********
Checkbox
List: **********You are infringing on a copyright -protected images owned by our company (**********)
Take a look at this document with the URLs to our images you utilized at ********** and our previous publications to get the proof of our copyrights.
Download it and see for yourself:
-
I believe that you willfully infringed on our rights under 17 U.S.C. Section 101 et seq. and can be liable for statutory damages of up to $140,000 as set forth in Section 504 (c) (2) of the Digital Millennium Copyright Act (DMCA) therein.This letter is official notification. I demand the elimination of the infringing materials described above. Take note as company, the Dmca requires you to and deactivate access to the copyrighted materials upon receipt of this notification letter. In case you do not cease the use of the aforementioned infringing materials a law suit will likely be commenced against you.
I have a strong self-belief that utilization of the copyrighted materials referenced above as presumably infringing is not permitted by the copyright owner, its agent, as well as legislation.
I swear, under consequence of perjury, that the informatino in this letter is correct and hereby affirm that I am permitted to act on behalf of the proprietor of an exclusive right that is presumably violated.
Best regards,
**********
Legal Officer
**********
**********
**********02/21/2024
Sample 2:

Text presented within:
Subject: [EXTERNAL] Re: Scan Duplication Concerns
Last week your manager asked me to calculate and form a finalized estimate for a next month project.
Confirm it today please, I will be on vacation tomorrow:**********
Please find link Docs
Update April 5, 2024 – Recent developments in the cybersecurity realm have unveiled notable shifts in the tactics surrounding the Latrodectus malware. Threat actors, recognized for their sophisticated methods, have begun impersonating various companies to disseminate legal threats regarding alleged copyright infringement.
Threat actors use personalized messages and unique URLs to deceive targets into downloading malicious JavaScript files. When executed, these files trigger a series of actions, including the deployment of Latrodectus through a simplified string decryption routine.
Update October 22, 2024 – Latrodectus developers have released multiple variants of this malware throughout 2024. The changes between the iterations were mostly rather minuscule, but there were instances of features being removed.
The haste with which these Latrodectus versions have been developed and their number suggest that new ones are likely to be forthcoming. Possibly, this activity is in anticipation of some significant change to the malware. More information on these developments can be found in an article by Albert Zsigovits on VMRay.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Latrodectus?
- STEP 1. Manual removal of Latrodectus malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
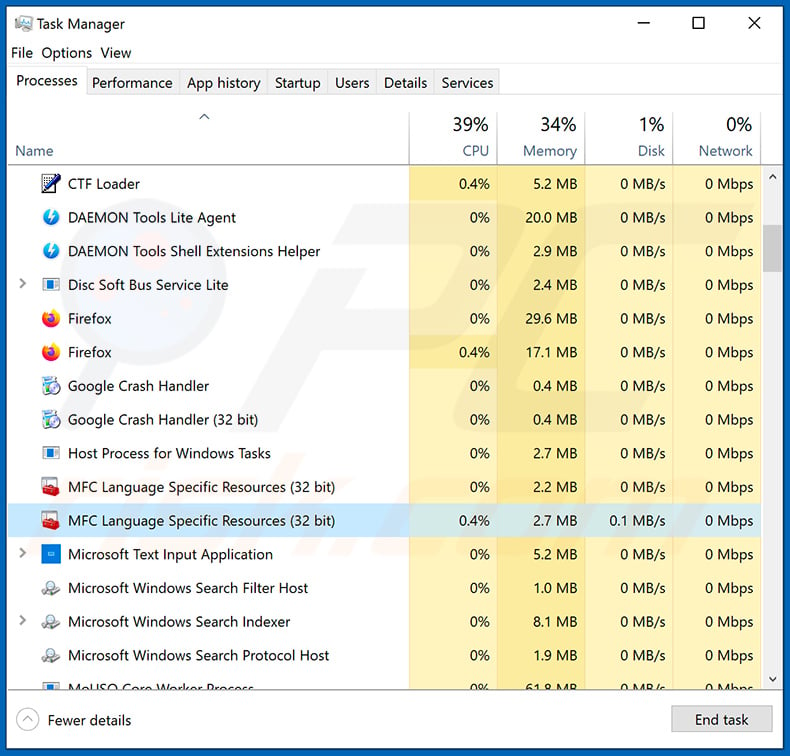
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
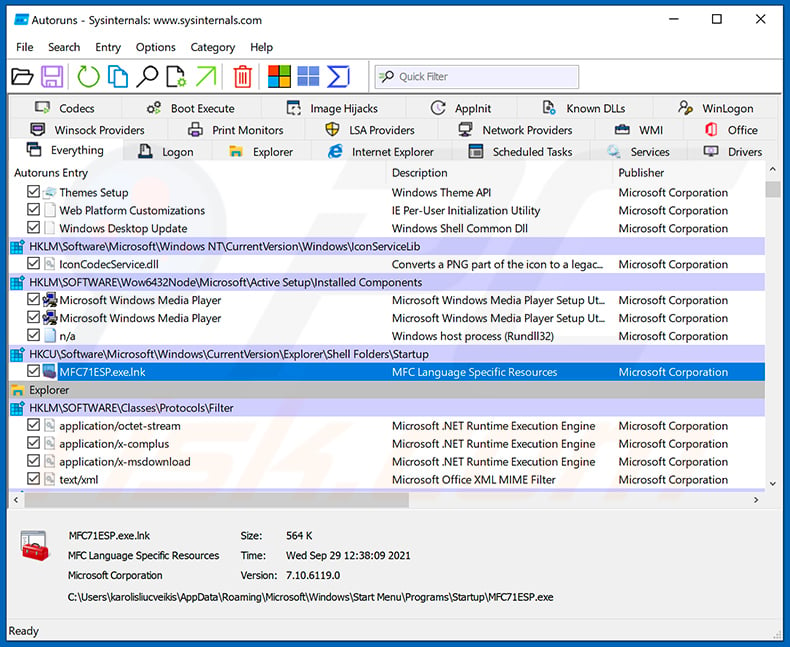
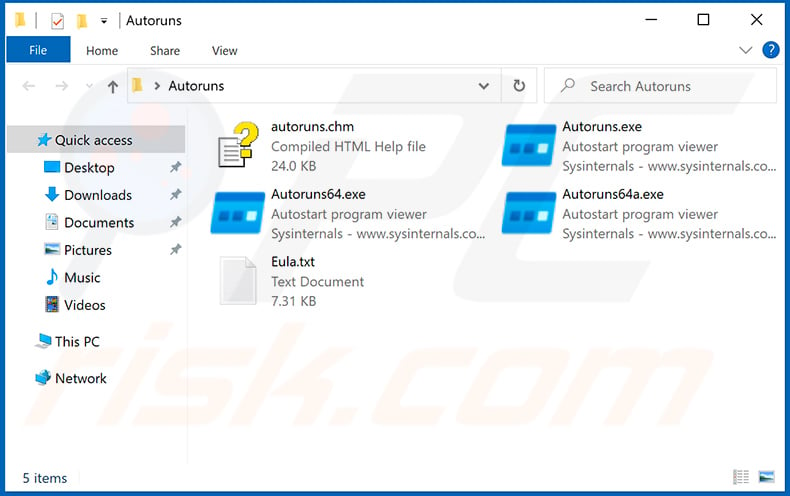
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
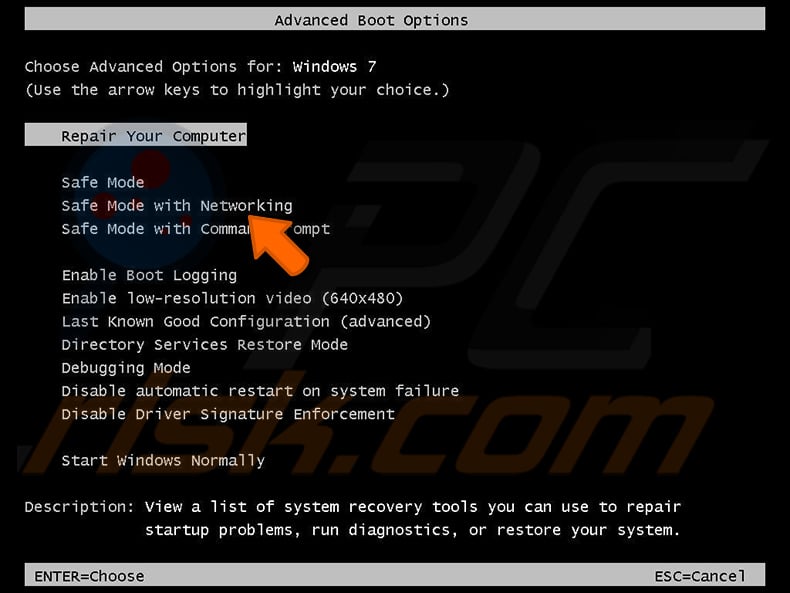
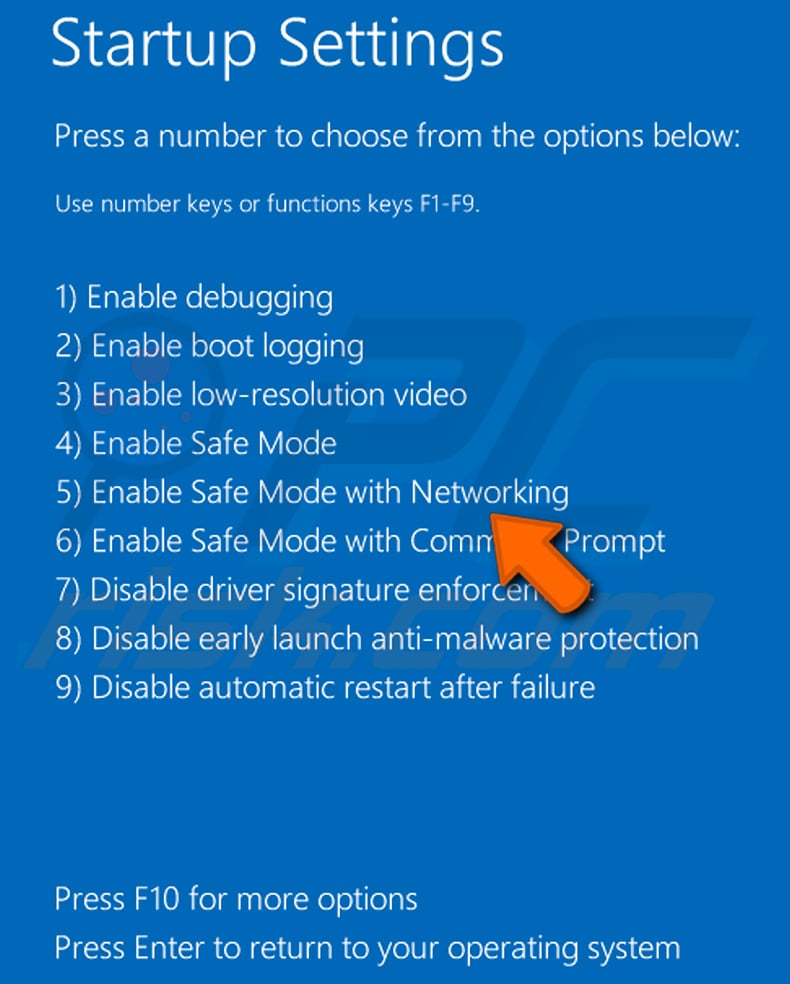
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
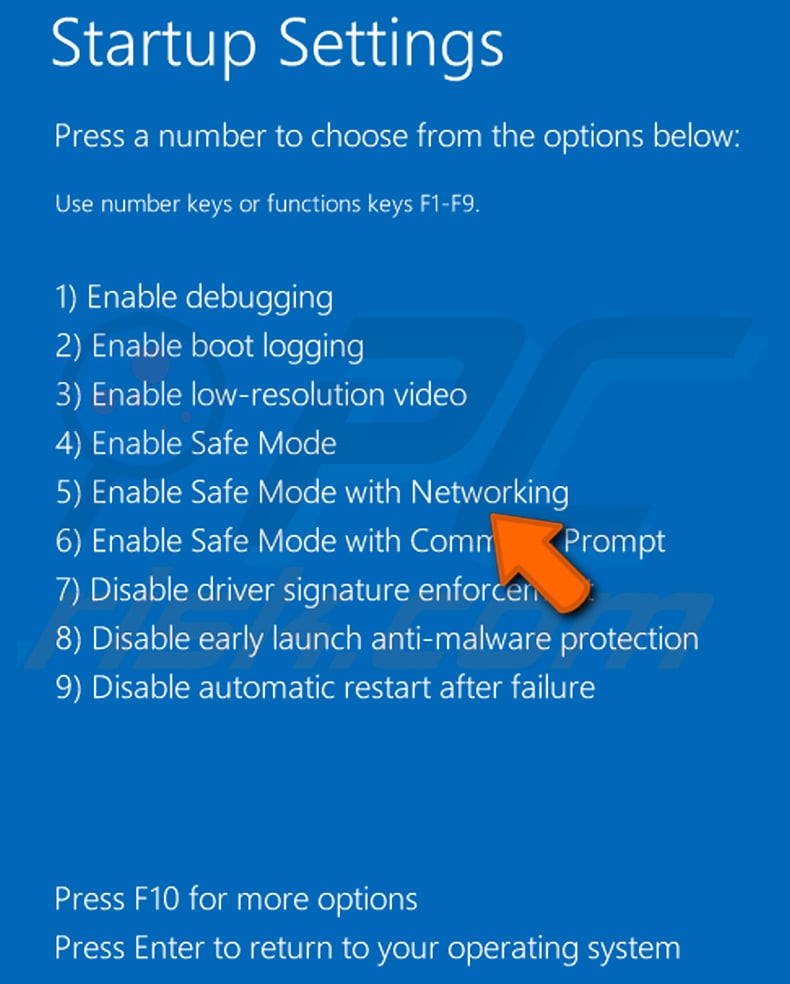
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
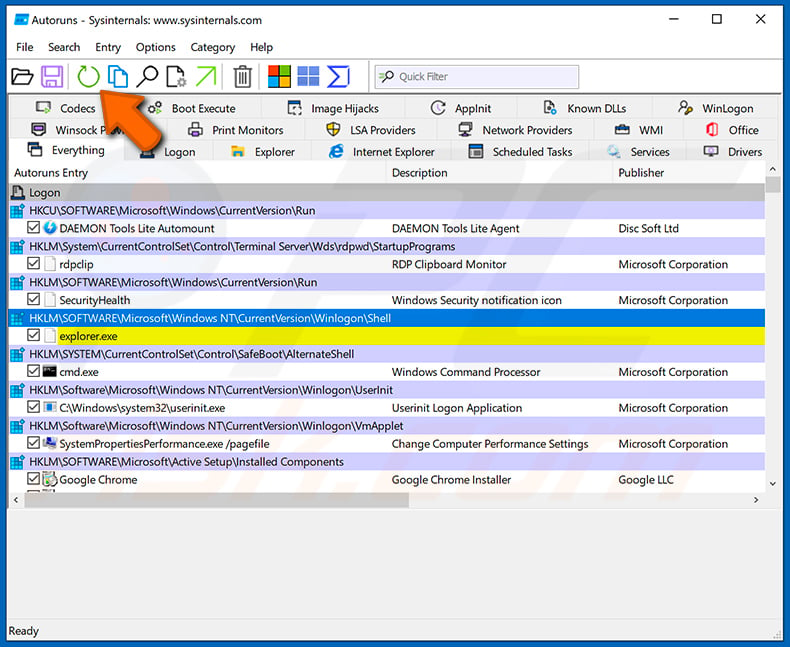
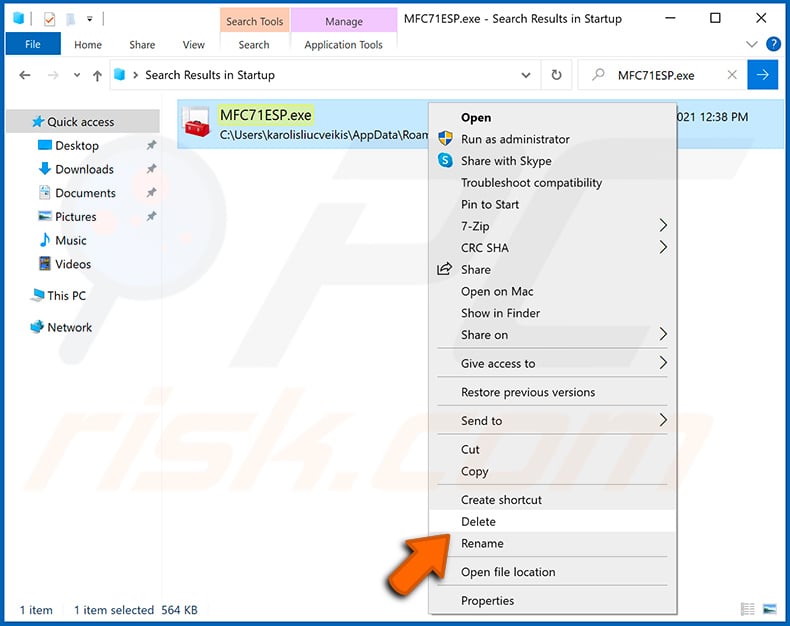
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
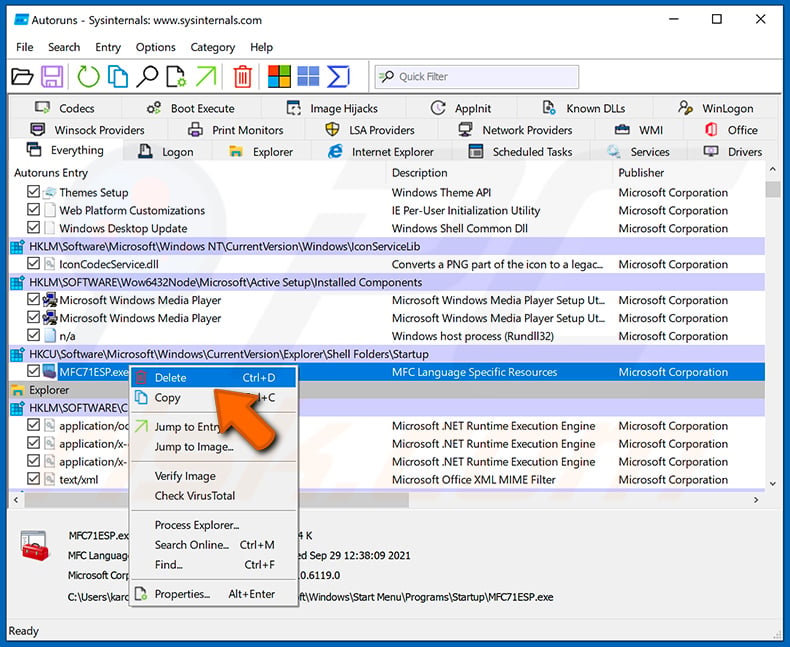
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Latrodectus malware, should I format my storage device to get rid of it?
Formatting your storage device may indeed remove the Latrodectus malware, but it is a drastic measure that will also erase all data on the device. Before resorting to formatting, you should consider less drastic options (such as using a security tool like Combo Cleaner) to remove the malware and preserve your data.
What are the biggest issues that malware can cause?
The consequences of malware infections vary depending on the type of malware involved. They can range from identity theft and financial losses to decreased computer performance and the risk of further infections. Additionally, malware may compromise sensitive data, disrupt system operations, and facilitate unauthorized access to personal or corporate networks.
What is the purpose of Latrodectus?
The purpose of Latrodectus, a loader malware, is to infiltrate target systems and execute additional malicious payloads. It acts as a gateway for deploying various types of malware, including ransomware, remote access trojans (RATs), banking trojans, information stealers, and keyloggers.
How did Latrodectus infiltrate my computer?
In one distribution chain, an email leads to a fake Azure login page, triggering the automatic download of a JavaScript file. This file retrieves an installer MSI, which implants a Latrodectus DLL onto the system, ensuring persistence. Latrodectus then communicates with its command-and-control server, granting remote access to the infected device.
Will Combo Cleaner protect me from malware?
While Combo Cleaner is effective at detecting and removing most known malware infections, it is essential to acknowledge that advanced malware can lurk deeply within the system. Conducting a full system scan is imperative to ensure thorough detection and removal of any hidden threats.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion