How to remove LPEClient from infected computers
![]() Written by Tomas Meskauskas on
Written by Tomas Meskauskas on
What kind of malware is LPEClient?
The LPEClient malware is a known threat that came to light in 2020. This malicious software is designed with the primary purpose of gathering information from the victims it infects and then downloading additional malicious payloads from a remote server. These payloads are executed in the computer's memory, which helps to maintain stealth and avoid detection.

More about LPEClient
The LPEClient malware has a history of existence and prior inclusion in cybersecurity alerts. Nevertheless, it has undergone recent refinements aimed at enhancing its sophistication and evasiveness. The malicious actors responsible for its development have diligently endeavored to render it less conspicuous and resistant to detection.
LPEClient is a key part of the Lazarus group's cyber activities. It is the tool they use to first infect a target computer. Once inside, it gathers information about the victim and helps deliver more harmful software. Over time, they have used LPEClient in different attacks, particularly focusing on defense contractors and nuclear engineers.
In one case, they tricked victims into downloading LPEClient by disguising it as VNC or Putty software, which then caused an intermediate infection. In a more recent attack in July 2023, the group went after the cryptocurrency industry for financial gain. They used another piece of malware called Gopuram, which was connected to a supply chain attack on 3CX.
What is interesting is that they still relied on LPEClient to deliver their final malicious software, even though they introduced a new tool. This shows that LPEClient continues to be an important part of their attack strategy in 2023, even when they change their initial attack methods.
| Name | LPEClient dropper |
| Threat Type | Malware Dropper |
| Detection Names | ALYac (Win32.Floxif.A), Baidu (Win32.Virus.Floxif.a), Kingsoft (Win32.Pioneer.CZ.2433), MaxSecure (Virus.W32.Pioneer.CZ), Symantec (W32.Fixflo.B!inf), Full List (VirusTotal) |
| Payload | LPEClient may be used to delivered different types of malware (e.g., ransomware or keyloggers). |
| Symptoms | This malware is designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Social engineering, Trojanized software (e.g., VNC or Putty clients), malware droppers like SIGNBT. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Conclusion
In conclusion, the ongoing evolution of the LPEClient malware underscores the persistent dedication of threat actors to enhancing the effectiveness and stealth of their malicious tools. This software's capacity to infiltrate systems, gather sensitive information, and download additional payloads from remote servers poses a considerable threat.
The potential damage resulting from LPEClient's infiltration includes data breaches, espionage, and the deployment of further destructive payloads (e.g., ransomware).
How did LPEClient infiltrate my computer?
LPEClient is typically delivered through a variety of deceptive means, primarily involving social engineering tactics and Trojanized software. In some instances, it has been disguised as legitimate applications, such as Trojanized VNC or Putty clients, which, when downloaded and executed, lead to an intermediate infection, enabling the malware to infiltrate the system.
It is also known that LPEClient has been delivered via a malware loader called SIGNBT. The latter is distributed using software vulnerabilities and possibly other methods.
How to avoid installation of malware?
In order to mitigate the risk of infecting a computer with malware like LPEClient, several preventive measures should be implemented. First, maintaining robust cybersecurity practices is crucial, including regular software updates and patches to address known vulnerabilities. Employing reputable antivirus solutions alongside firewalls can act as a barrier against malicious software.
Also, exercise caution when downloading and executing files, especially from unknown or unverified sources, and be wary of unsolicited email attachments or suspicious links. Do not interact with ads (e.g., pop-ups) while visiting suspicious sites. Never download pirated software or unofficial tools that activate legitimate software.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is LPEClient?
- STEP 1. Manual removal of LPEClient malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:
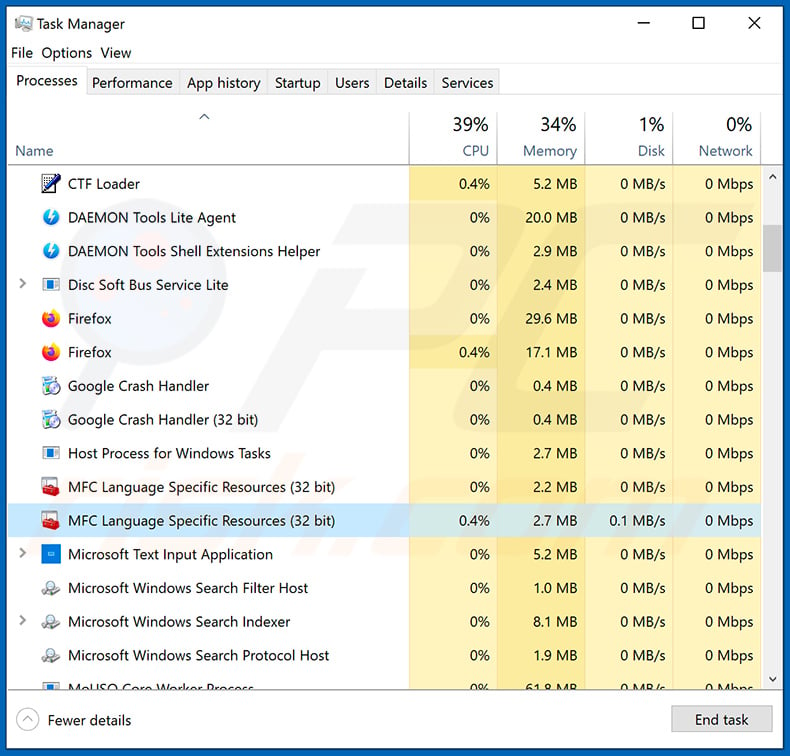
If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
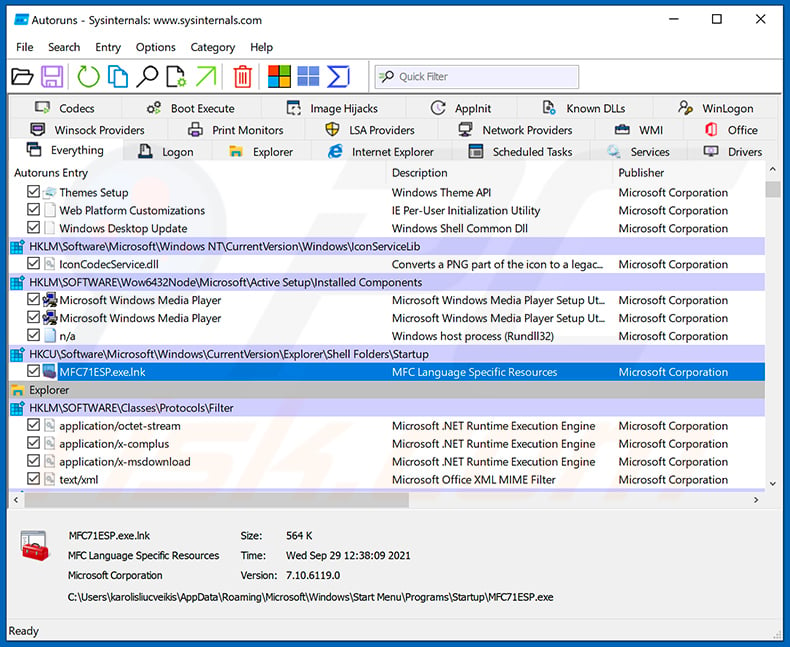
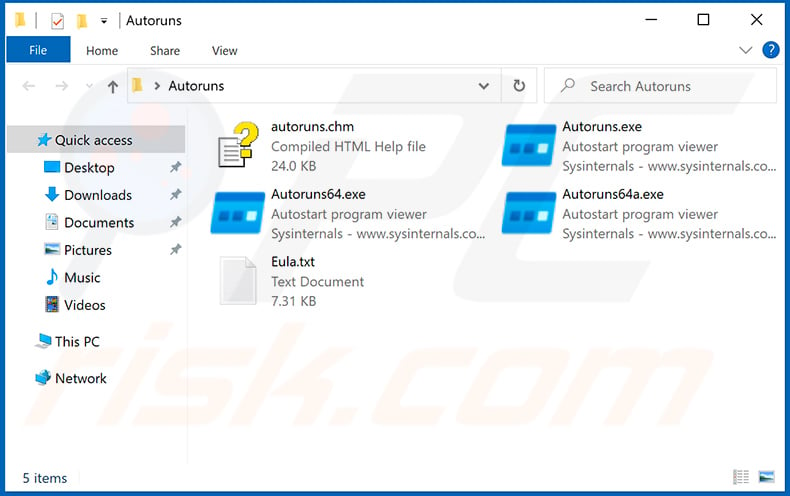
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
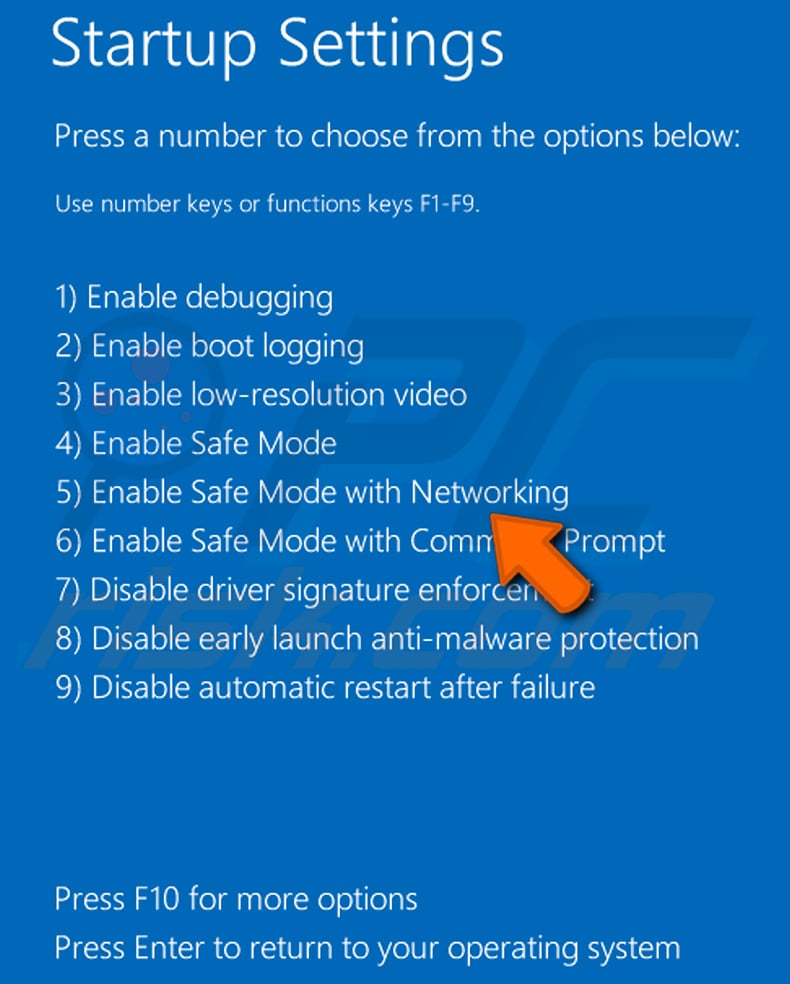
 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.
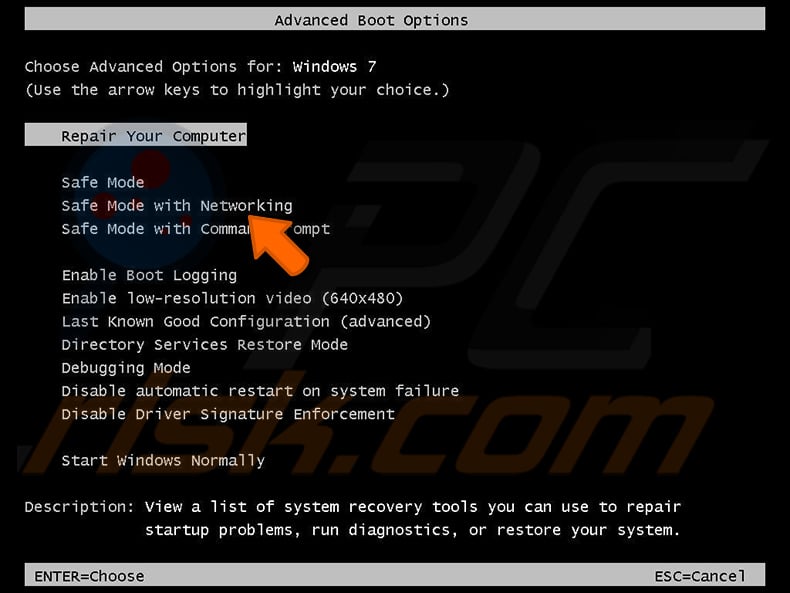
Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.
Video showing how to start Windows 8 in "Safe Mode with Networking":
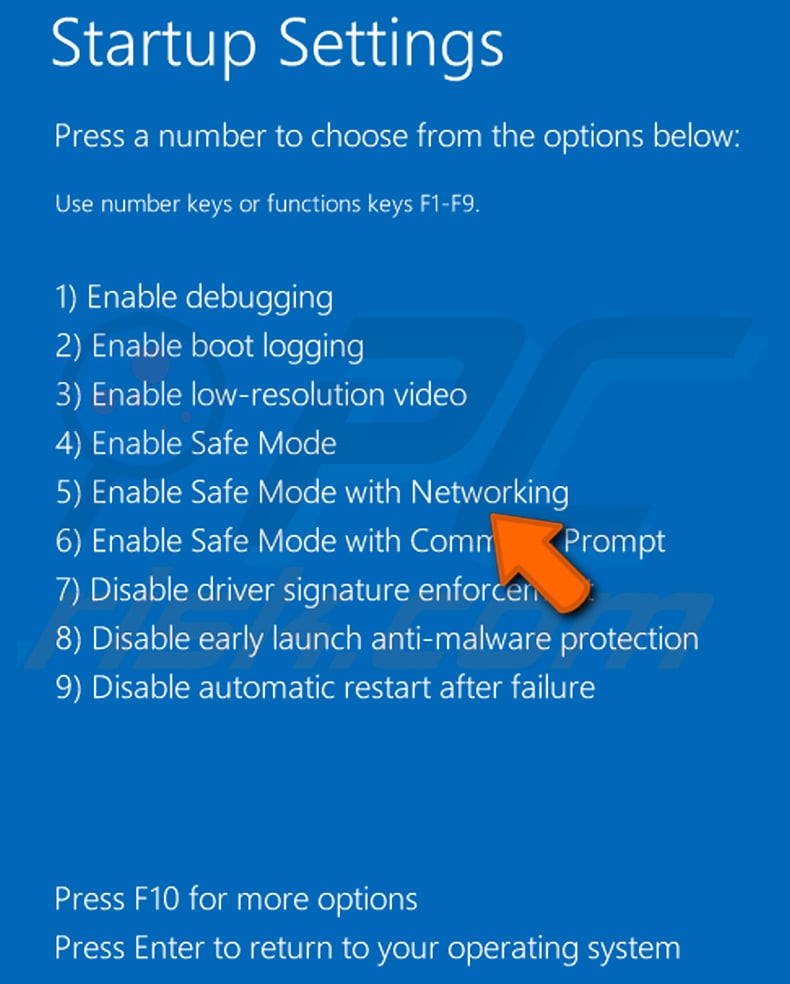
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.
Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
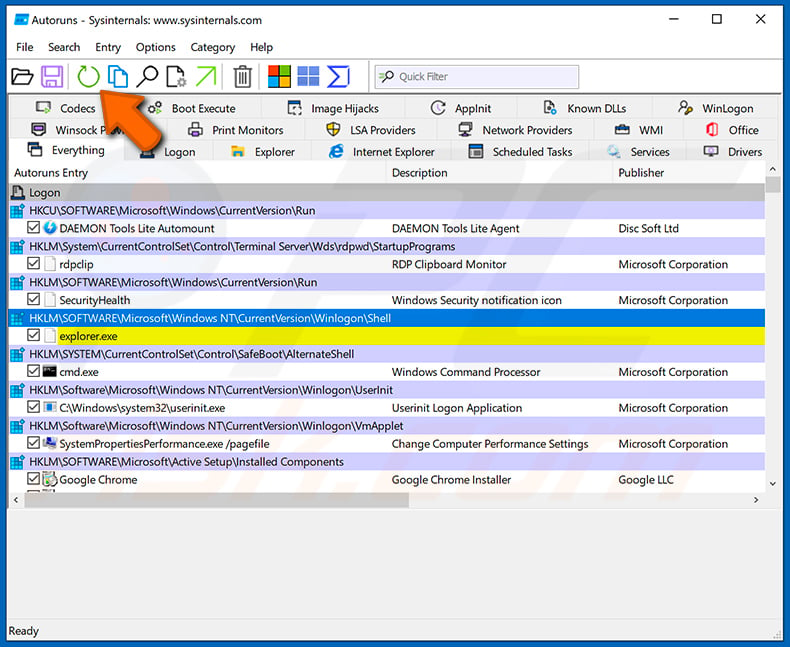
 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
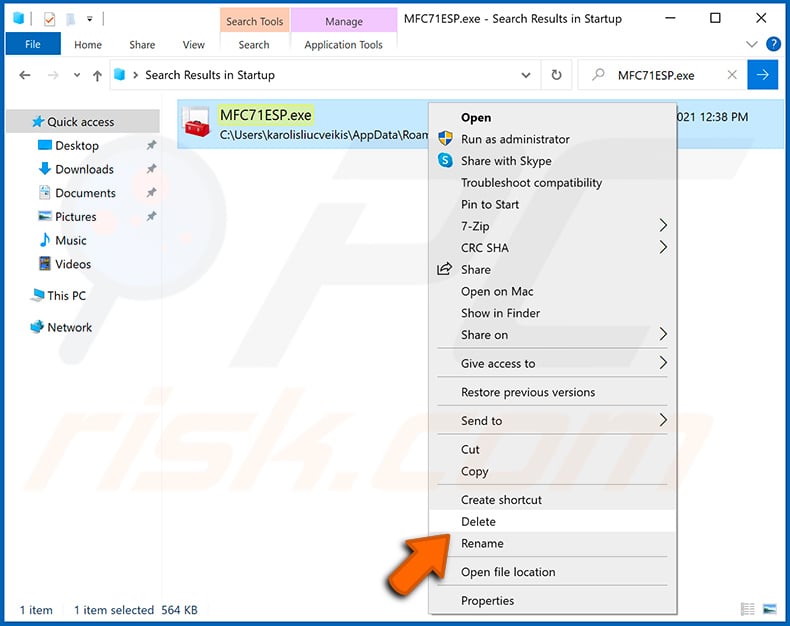
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".
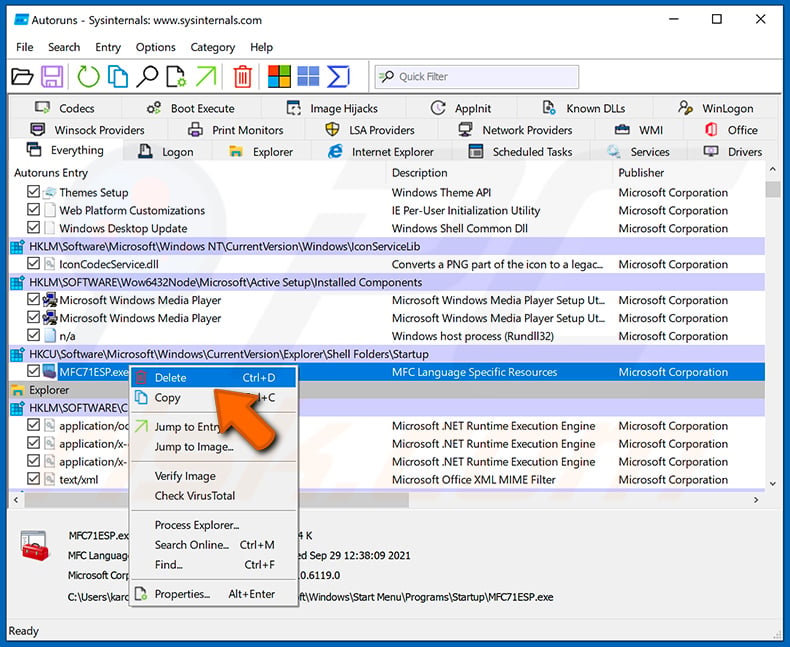
After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.
Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with LPEClient malware, should I format my storage device to get rid of it?
When dealing with the LPEClient malware infection on your computer, it represents a critical situation, and reformatting your storage device should be contemplated as a final recourse. Before resorting to such an extreme measure, it is advisable to conduct a scan using a reputable antivirus or anti-malware program on your system.
What are the biggest issues that malware can cause?
Malware presents substantial risks, encompassing data breaches, financial liabilities, and system disturbances. It has the potential to exfiltrate sensitive data, including personal and financial information, jeopardize online accounts, and instigate identity theft. Moreover, malware can provide unauthorized entry into systems, paving the way for cyberattacks or espionage activities.
What is the purpose of LPEClient?
The primary purpose of LPEClient is to act as a malicious tool designed for unauthorized access, data exfiltration, and the execution of additional malicious payloads on infected systems. It serves as an initial infection vector in cyberattacks, allowing threat actors to gather victim information and download further malware from remote servers to carry out various malicious activities.
How did LPEClient infiltrate my computer?
In certain instances, the malware was introduced to its targets through an infected VNC or Putty client, resulting in an interim infection. It's crucial to understand that the delivery approach for LPEClient can differ depending on the particular campaign and the strategies adopted by the malicious actors. Notably, SIGNBT has also been identified as a method for delivering LPEClient.
Will Combo Cleaner protect me from malware?
Combo Cleaner effectively detects and removes most malware. Full system scans are essential for tackling advanced threats since high-end malware tends to be hidden deep in the system.

▼ Show Discussion