Avoid getting scammed by fake "Unsuccessful Search For Relatives" emails
Phishing/ScamAlso Known As: "Unsuccessful Search For Relatives" spam email
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "Unsuccessful Search For Relatives"?
After examining two emails, referred to as "Unsuccessful Search For Relatives", we determined that they are spam. These letters are thematically identical; they inform recipients that a wealthy family has passed away in an accident, thus prompting legal representatives to search for surviving relatives. Supposedly, the recipient is a candidate, and they must contact the sender urgently since the inheritable funds will soon be confiscated by the bank.
It must be stressed that all these claims are false and that this is a phishing scam. It is noteworthy that this scheme may also aim to trick victims into sending the scammers money.

"Unsuccessful Search For Relatives" email scam overview
As mentioned in the introduction, the two reviewed versions of "Unsuccessful Search For Relatives" spam are thematically identical, although their presentation differs.
One version – subject "EVANS THOMAS LAW FIRM" – provides all of the information and requests to disclose personally identifiable details in the body of the letter. The other variant – subject "investment" – is brief, and the whole of the false claims are relegated to an attached PDF document ("investment.pdf"). Another thing of note is that this version does not ask for private data but urges the recipient to establish communication.
The "EVANS THOMAS LAW FIRM" spam email introduces the sender as an attorney of a late individual from North America who had worked for the Nigerian branch of the Shell petroleum company (SPDC). The individual and their family had been in a fatal car accident. Thus, their representing law firm had begun efforts to locate extended relatives.
The search was unsuccessful for several years until the recipient was found as the last surviving relative. Therefore, they are now entitled to a share of their deceased relative's property and bank account, the latter being worth 15 million USD.
The matter is urgent as the bank will confiscate the funds within ten work days. Hence, the sender urges the recipient to begin all the necessary procedures. The money will be split 55% to the attorney, 40% to the recipient, and 5% reserved for expenses and tax purposes. The letter reassures that the deal is legitimate.
The recipient is asked to provide the following information: full name, age, gender, nationality, occupation, home address, telephone and fax numbers.
The other email version states that the attachment includes an investment request. The attached file is supposedly written by a legal adviser who worked for a late individual from Portugal. The deceased client was a contractor for AngloGold in South Africa.
As in the other variant, the man died with his family in a vehicular accident. The script likewise details an extensive unsuccessful search for extended family. Again, the story goes that the bank will soon confiscate the funds – this time, the sum is 21 million USD – unless it is properly claimed.
However, this version does not identify the recipient as a relative; rather, the sender expresses their intent to present them as kin or a business associate of the deceased individual. If consented to, the money will be split in half and used to make a lucrative investment.
The sender pleads for confidence yet reassures the recipient that the transactions and paperwork will be dealt with legally. This variant does not request any information but urges to contact the sender immediately.
As previously indicated, all the information provided by these emails is false, and this mail is in no way associated with Shell plc or its subsidiary Shell Nigeria, AngloGold Ashanti, or any other real individuals or entities.
Scammers who target personally identifiable information can use it to steal victims' identities and perform a variety of nefarious deeds.
The disclosure of finance-related data can result in fraudulent transactions or unauthorized online purchases. Cyber criminals typically seek online bank account log-in credentials, banking account details, credit card numbers, and similarly sensitive data.
Spam mail of this ilk often aims to trick victims into making payments under the guise of fees necessary to facilitate the bogus transfers. Criminals prefer difficult-to-trace methods for receiving funds, e.g., cryptocurrencies, pre-paid vouchers, gift cards, or cash hidden in packages and shipped. These methods minimize the chances of persecution and victims retrieving their funds.
If you have provided your log-in credentials to scammers – change the passwords of all possibly exposed accounts and contact their official support without delay. And if you have disclosed other private data (e.g., ID card details, passport photos/scans, credit card numbers, etc.) – immediately contact the appropriate authorities.
| Name | "Unsuccessful Search For Relatives" spam email |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipient will inherit the funds of a wealthy deceased individual due to an unsuccessful search for relatives. |
| Attachment(s) | investment.pdf (filename may vary) |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam campaigns in general
Phishing emails are extremely prevalent; "Web Mail Scam", "ATM Card", "Overdue Invoice", and "NEW DOCUMENT(S) FOR REVIEW ON CLOUD" are merely a few examples of our newest finds.
However, spam mail is used to promote various scams, e.g., callback, tech support, lottery, inheritance, subscription expiration/renewal, failed package or message delivery, account deactivation, etc. Furthermore, deceptive emails are used to proliferate malware (e.g., trojans, ransomware, cryptocurrency miners, etc.).
These letters can be riddled with errors or competently disguised as messages from genuine service providers, companies, institutions, authorities, and other entities.
How do spam campaigns infect computers?
Spam campaigns are commonly used in malware distribution. These emails/messages include malicious files as attachments or download links. Infectious files come in various formats, e.g., documents (Microsoft Office, Microsoft OneNote, PDF, etc.), archives (ZIP, RAR, etc.), executables (.exe, .run, etc.), JavaScript, and so forth.
When a malicious file is opened – the infection chain is initiated. However, some formats may need additional actions to trigger malware download/installation processes. To elaborate, Microsoft Office documents require users to enable macro commands (i.e., editing/content), while OneNote files need them to click embedded links or files.
How to avoid installation of malware?
We strongly recommend treating incoming emails, PMs/DMs, SMSes, and other messages with care. Attachments or links found in suspicious/irrelevant mail must not be opened, as they can be malicious.
It is important to use Microsoft Office versions released after 2010 since their "Protected View" mode prevents automatic macro command execution.
However, malware is distributed using other methods as well. Hence, we advise being cautious while browsing, as fraudulent and malicious online content usually appears legitimate and innocuous.
Furthermore, all downloads must be performed from official and verified sources. Another recommendation is to activate and update programs using genuine functions/tools, as illegal activation tools ("cracks") and third-party updaters may contain malware.
We must emphasize the importance of having a reputable anti-virus installed and kept up-to-date. Security software must be used to run regular system scans and to remove detected threats. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in one variant of the "Unsuccessful Search For Relatives" spam email:
Subject: EVANS THOMAS LAW FIRM
EVANS THOMAS LAW FIRM
SOLICITORS & ADVOCATES
No: 15 Allen Avenue
Ikeja ,Lagos.
Email: {barrevansthomas213@yahoo.co.jp}
Dear Friend
It is obvious that this proposal will come to you as a surprise.This is because we have not met before but I am inspired to sending you this email following the huge fund transfer opportunity that will be of mutual benefit to the two of us.
However, I am Barrister Evans Thomas Attorney to the late Engr.Ronald Johnson, a national of Northern American, who used to work with Shell Petroleum Development Company(SPDC) in Nigeria . On the 11th of November,2008. My client,his wife And their three children were involved in a car accident along Sagamu/Lagos Express Road.
Unfortunately they all lost their lives in the event of the accident, Since then I have made several inquiries to several Embassies to locate any of my clients extended relatives, this has also proved unsuccessful.
After these several unsuccessful attempts, I decided to trace his relatives over the Internet to locate any member of his family but of no avail, hence I contacted you to assist in repatriating the money and property left behind by my client,I can easily convince the bank with my legal practice that you are the only surviving relation of my client. Otherwise the Estate he left behind will be confiscated or declared unserviceable by the bank where this huge deposits were lodged.Particularly, the Bank where the deceased had an account valued at about $15 million U.S dollars(Fifteen million U.S.America dollars).
Consequently,The bank issued me a notice to provide the next of kin or have the account confiscated within the next ten official working days. Since I have been unsuccessful in locating the relatives for over several years now.I seek your consent to present you as the next of kin to the deceased,so that the proceeds of this account valued at $15million U.S dollars can be paid to your account and then you and me can share the money. 55% to me and 40% to you,while 5% should be for expenses or tax as your government may require.
All I require is your honest cooperation to enable us see this deal through and also forward the following to me:
Your Full Name:
Your House Address:
Your Tele-phone And Fax No:
Your Age and Gender :
Your Nationality:
Your Occupation:
I guarantee that this will be executed under a legitimate arrangement that will protect you from any breach of the law.Please get in touch with me VIA this my confidential email {barrevansthomas213@yahoo.co.jp}
Yours Faithfully,
Barr. Evans Thomas . { SAN }
Screenshot of another variant of the "Unsuccessful Search For Relatives" spam email:

Text presented in this variant:
Subject: investment
Attached with my investment request letter.
Best regards,
Mr. D Anderson (ESQ)
Screenshot of the file attached to this variant ("investment.pdf"):

Text presented in this file:
SUBJECT: URGENT ARRANGEMENT.
Dear Sir/Madam,
I know this might come as a surprise to you considering the amount of junk emails we all receive on a daily basis. I can assure
you that I am not one of them; I would appreciate it if the content of this email is kept strictly confidential. I have decided to
contact you due to the urgency of this transaction and the current financial situation of the world at the moment. I am Mr.
Desmond Anderson, of Desmond & Co Cambers. The legal adviser to Chief Engineer Manuel Arriaga, A Portuguese
national who used to be a contractor with (ANGLO GOLD MINES) Mafikeng. Gold Mining/ Exploration Corporation in
South Africa hereinafter shall be referred to as my client.
On February 21, 2010 my client, his wife and their two children were involved in a car accident. All occupants of the vehicle
unfortunately lost their lives. Since then I have made several personal inquiries from the embassy to locate any of my client’s
extended relatives, this has also proved unsuccessful.
After several unsuccessful attempts, I now decided to inform you, hence I contacted you. I have sent you this letter to assist
in repatriating the money left behind by my client before they get confiscated or declared unserviceable by the bank where
this huge deposit was lodged here in South Africa. Where the deceased had an account valued at about $21,000.000.00 USD
(Twenty One Million United States Dollars) the bank has issued me a notice to provide the next of kin/ business associate or
have the account confiscated though in 2020 there are persons of the same nationality here in South Africa none of them is a
direct relative with the deceased and no one had an idea of this deposit. The Private banking sector will by the end of
2023/2024 broadcast a request for statement of claim to my office, failing to receive viable claims they will probably revert
the deposit to the ownership of the SA Government Treasury according to South Africa Banking and financial law.
Since I have been unsuccessful in locating the relatives for over a period of time, I seek your consent to present you as the
next of kin or business associate to the deceased, Although the project is CAPITAL INTENSIVE, I know we will be able to
pull it through following proper banking and legal Channels with your assistance at your end so that the proceeds of this
account valued at $21,000.000.00USD (Twenty One Million United States Dollars) can be transferred into your designated
account and I shall proceed down to your country on confirmation of the fund in your account to discuss with you on how to
invest the money, meanwhile all documents will be obtain in your name and endorse your signature on some of the
documents as the next of kin or business associate to the deceased once the fund has been approved by the bank.
I shall revalidate and notarize all the necessary legal documents that can be used to back up any claim that the bank may
need, this is a risk free transaction because the banker who is in charge of the account section has called to present a next of
kin or business associate. We shall split the money equally and jointly invest it on any lucrative investment as soon as the
transaction is successful. I guarantee you this will be executed under a legitimate arrangement that will protect you from any
breach of the law.
If you are interested please kindly email me with your details and the two references above on: Desmondandcoc@gmail.com Because
I need your strong assurance and confidentiality on this matter.
Please, again, note I am a family man; I have a wife and children. I send you this mail not without a measure of fear as to the
consequences, but I know within me that nothing Ventured is nothing gained" and that success and riches never come easy or
on a platter of gold. This is the one truth I have learned from my private clients. Do not betray my confidence. If we can be of
one accord, we should act swiftly on this.
Please pardon my writing if in any way you pick offence. I await your immediate response indicating your interest ASAP.
Best regards,
Desmond & Co Cambers, Desk of
Barrister. Desmond Anderson.
Yet another example of an email from "Unsuccessful Search For Relatives" spam campaign:

Text presented within:
Subject: Letter Of Proposal
--
Greetings!I hope this mail will get to you in good condition.
First of all, I will start by introducing myself. My name is Alistair Currie, born in Scotland, grew up in Hong Kong, currently working with Barclays Bank London. I have been working here for several years and I have a very good working record with the Bank.
During the recent auditing of bank accounts in our bank, I discovered a bank account that had not been operated for a long period. After an investigation discreetly, I discovered that the owner of this account was a business mogul and Arabian, Dr. Manzoor Hassan who died in a helicopter crash in January 2007, with both his wife, his only son Avraham (who is his next of kin), and his daughter-in-law.
He died leaving a huge sum of £15,800,000.00 in our bank custody.
The choice of contacting you aroused from the geographical nature of where you live particularly due to the sensitivity of the transaction and the confidentiality here.
Before I contacted you, I took my time to thoroughly search for any of the relatives of the Late Dr. Manzoor Hasan but to no avail. I also made a discrete inquiry to find out that Dr. Manzoor Hasan doesn't have any other relatives, and no one else knows of his bank account with Barclays Bank London.
In this regard, I seek your consent to present you as the next of kin/beneficiary to the deceased so the proceeds of this bank account valued at £15.8 Million British Pounds sterling can be paid to you.
I propose for the money to be shared in these percentages, 60% to me and 40% to you, and all the necessary legal documents that can be used to back up this inheritance claim are not a problem.
All I need is to upload your names to the documents and legalize them at the British High Court to prove you as the legitimate beneficiary of this fund, and I guarantee you 100% success if you give me your honest cooperation and trust.
Therefore, your response to this email will be greatly appreciated as we have a short time to run it.
Rest assured that the procedures that will be taken in your favor for the transfer will be official and lawful to protect us against any violation of the law.
You can also ask questions if you have any, but if you are interested in my proposal I will send you more information directing you to further instructions on how we can claim the money in the account successfully.
A quick response from you will be highly appreciated.
Best Regards,
Alistair Currie.
Another example of an email from "Unsuccessful Search For Relatives" spam campaign:

Text presented within:
Subject: DEAR FRIEND
Hermosilla, 3,28001 Madrid Spain Tel: +34 697-902 -740 Fax: +34 911-980-793
Email migulpacoconsult@aol.com
OUR REF: T&NGO/KN3/EUR4524 YOU’RE REF: EUR/INO/ESP DATE: 16/02/2024
________________________________________
DEAR FRIEND,
Firstly, Let me start by first introducing myself properly to you. It may surprise you receiving this letter from me, since there was no previous correspondence between us My name is Barrister Miguel C Paco, (Spanish Lawyer and Doctor in Law) a personal Attorney to Late. Mr. Bruce Padore, an expatriate engineer who has worked with the Mining and Smelting Company (Asturiana de Zinc S.A. Spain).
I must solicit your confidence in this transaction; this is by virtue of its nature as being utterly confidential and top secret. Though I know that a transaction of this magnitude will make any one apprehensive and worried, but I am assuring you that all will be well at the end of the day.
My purpose of contacting you is for you to help me to secure his funds deposited with Spanish Bank before he died, to avoid it being confiscated or declared as unclaimed by the Bank. The fund value is $11,500, 000.00 (E leven Million, Five Hundred Thousand US Dollars), this money was deposited by my late client before he passed away, he died by stroke and cancer on the 16th April 2004, and up till today his relatives remained unknown.
The Bank has issued me a final notice to contact his relative’s/ the next of kin or else the account will be declared unserviceable and the fund will be diverted to the Bank treasury, So far all my efforts to get a hold of some one related to my late client has been in vain. Hence, Since this account is secret and there is no one left to claim the fund I am contacting you. I am actually asking for your consent to present you to the Bank as the Next of Kin/beneficiary of my late client's fund, since you have the same last name, so that the fund will be released to you as his next of kin. All the legal documents to back up your claim as my client's next of Kin are with me. All I require is your honest cooperation and absolute confidentiality in order to guarantee success.
I wish to point out that I want 20% of this money to be shared among the Charity Organizations, while the remaining 80% is shared equally between us. This transaction is entirely risk free. I will use my position as the client’s personal attorney to guarantee the successful execution of this transaction. If you are interested, please contact me Tel: +34 697-902 -740 , Fax: +34. 911-980-793 Email: migulpacoconsult@aol.com upon your response, I shall then provide you with more details and relevant documents that will help you understand more on this transaction.
The intended transaction will be processed under legitimacy,which will protect me and you from any violation of law.
If you wish to achieve the goal with me, please kindly get back to me with your interest for further explanations and better understanding. Also be kind to let me know if you are not interested so that I can further my search to another Citizen that has the same surname with my late client.
Kindest Regards
Bar.Miguel C Paco
Attorney at Law
________________________________________
Divorce, custody and marriage Laws, Corporate and Agreement laws, Incorporation, Rent, eviction, tenancy and Lease Laws, Labor laws, Insurance claim, Citizenship and immigration Laws, Copyright and Consumer Protection Laws, Wills, Trust, Estates and Intellectual Property Laws, Bank, Finance and Monetary Laws, Corporate, Private and Business Laws, Recovery, Joint Venture & Mergers, Civil Right Laws, Tax, sales and Custom Laws, Registration of property, Title search, deeds, mutation relationship, Conveyance. @ López Rodó & Cruz Ferrer Abogados © 2004All rights reserved
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "Unsuccessful Search For Relatives" spam email?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
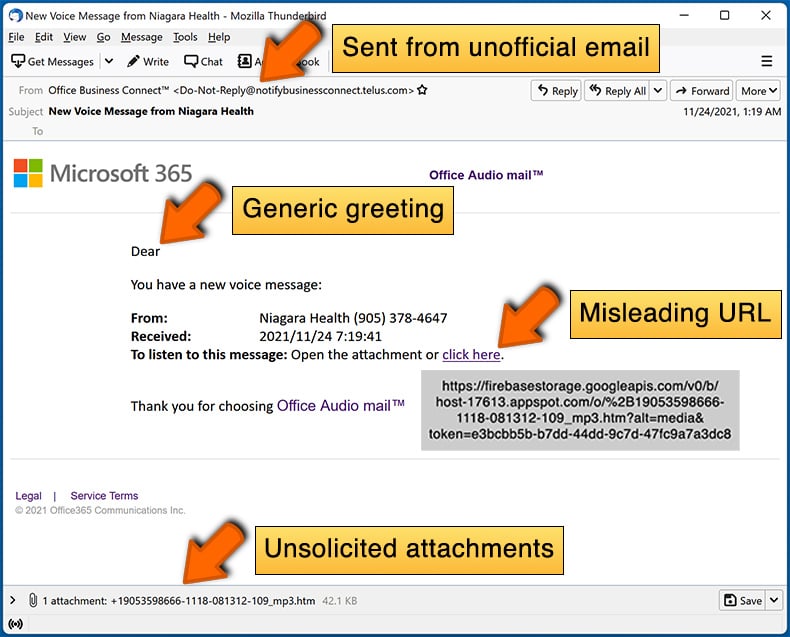
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:
What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. This mail is spread in massive campaigns – hence, thousands of users receive identical emails/messages.
I have provided my personal information when tricked by this spam email, what should I do?
If you have provided your account credentials – change the passwords of all possibly exposed accounts and inform their official support without delay. However, if you've disclosed other private data (e.g., ID card details, passport scans/photos, credit card numbers, etc.) – immediately contact the corresponding authorities.
I have read a spam email but didn't open the attachment, is my computer infected?
No, merely reading an email will not result in a system infection. Devices are infected when malicious attachments or links are opened.
I have downloaded and opened a file attached to a spam email, is my computer infected?
If the opened file was an executable (.exe, .run, etc.) – most likely, yes – your device was compromised. However, you might have avoided an infection if it was a document (.doc, .xls, .pdf, .one, etc.). These formats may need additional actions to start downloading/installing malware (e.g., enabling macro commands, clicking embedded content, etc.).
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is designed to detect and eliminate threats. It is capable of removing practically all known malware infections. Note that performing a full system scan is essential since high-end malicious software typically hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion