How to stop clipboard from pasting 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F
TrojanAlso Known As: 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F clipper
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F?
17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F is a clipper-type malicious program, which our researchers discovered while inspecting "cracked" software download websites. Also known as "clipboard hijackers", malware of this type is designed to replace the data copied into the clipboard. Clippers are used to redirect outgoing cryptocurrency transactions into the attackers' digital wallets.

17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F malware overview
Having analyzed this malicious program, we can conclude that it detects when the victim copies a Bitcoin cryptocurrency wallet address into the clipboard (i.e., copy-paste buffer). When the copied content is pasted - this clipper pastes a different cryptowallet address. Hence, instead of the sum being transferred to the intended wallet, it is redirected to one owned by the cyber criminals.
We have observed this clipboard hijacker pasting the "17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F" and "3PxkHEMPaNMPMyiiHpHEj6ZgWzShh54N65" Bitcoin wallet addresses.
Based on our experience with similar clippers proliferated via "crack" sites, we have to mention the possibility of this malware's installation setup being bundled with other harmful software (e.g., adware, browser hijackers, PUAs, etc.). Therefore, if your clipboard is pasting either "17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F" or "3PxkHEMPaNMPMyiiHpHEj6ZgWzShh54N65", it is possible that other threats are present on the system as well.
In summary, clipper infections can result in significant financial losses. Software infiltrated alongside these malicious programs could also cause system infections, severe privacy issues, and even identity theft.
If you suspect/know that your device is infected with this clipper, we strongly advise using an anti-virus to eliminate all threats without delay.
| Name | 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F clipper |
| Threat Type | Trojan, Malware, Clipper, Clipboard Hijacker. |
| Cyber Criminals' Cryptowallet Addresses | 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F (Bitcoin), 3PxkHEMPaNMPMyiiHpHEj6ZgWzShh54N65 (Bitcoin) |
| Detection Names (malicious installer) | K7AntiVirus (Trojan ( 0056e6d11 )), K7GW (Trojan ( 0056e6d11 )), Full List Of Detections (VirusTotal) |
| Symptoms | When a cryptocurrency (BTC) wallet address is copied into the clipboard, the malware changes it to one in possession of the cyber criminals. |
| Distribution Methods | 'Cracked' software websites, infected email attachments, malicious online advertisements, social engineering. |
| Damage | Decreased computer performance, privacy issues, possible additional malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Clipper malware examples
We have analyzed countless clippers; 1xExujJunyRVG8MWnEgxdHkVwW7xSzntZ and 89N3PDyZzakoH7W6n8ZrjGDDktjh8iWFG6eKRvi3kvpQ are just a couple examples of the latest.
It is noteworthy that malware can have varied functionalities, which can be in different combinations. Hence, malicious programs can have clipboard-hijacking as one of their many features; KryptoCibule, Jester Stealer, and S-400 RAT are such programs.
However, regardless of how malware operates - its presence endangers device and user safety. Therefore, it is crucial to eliminate all threats immediately upon detection.
How did 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F install on my computer?
We discovered 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F being promoted on a website offering "cracked" software downloads. However, malware is not spread exclusively through illegal program activation ("cracking") tools and their download sources.
The most common distribution methods also include: drive-by (stealthy and deceptive) downloads, malicious attachments/links in spam emails and messages, freeware and third-party download sites, Peer-to-Peer sharing networks (Torrent clients, Gnutella, eMule, etc.), online scams, and fake updates.
Infectious files can be in various formats, e.g., executables (.exe, .run, etc.), archives (RAR, ZIP, etc.), Microsoft Office and PDF documents, JavaScript, and so forth. When such a file is executed, run, or otherwise opened - the infection chain is jumpstarted.
How to avoid installation of malware?
We highly recommend downloading only from official and verified sources. Additionally, all programs must be activated and updated with tools/functions provided by genuine developers, as those obtained from third-parties may contain malware.
We advise against opening the attachments and links found in dubious/irrelevant emails and messages - as they may cause system infections.
Furthermore, having a reputable anti-virus installed and updated is paramount to device/user safety. Security software must be used to run regular system scans and to remove detected threats. If your computer is already infected with 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate this malware.
Appearance of 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F malware pasting changed clipboard data (GIF):

Screenshot of the "cracked" software download website used to promote 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F malware:

Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F?
- STEP 1. Uninstall punwanted applications using Control Panel.
- STEP 2. Remove unwanted ads from Google Chrome.
- STEP 3. Remove unwanted ads from Mozilla Firefox.
- STEP 4. Remove unwanted extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F removal:
Windows 11 users:
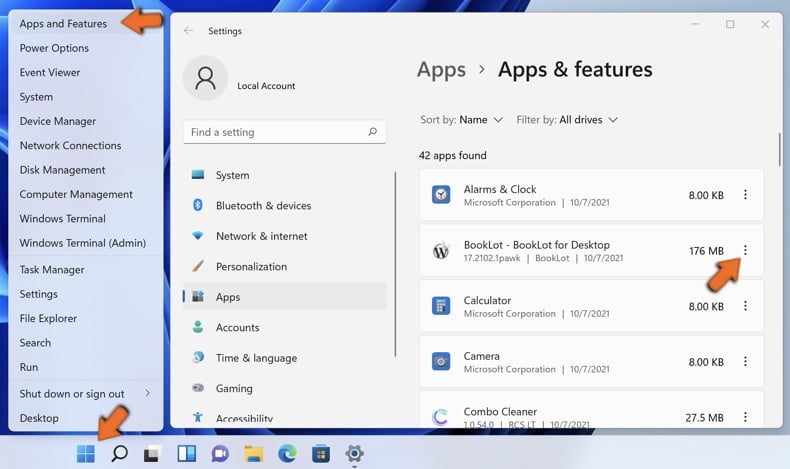
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
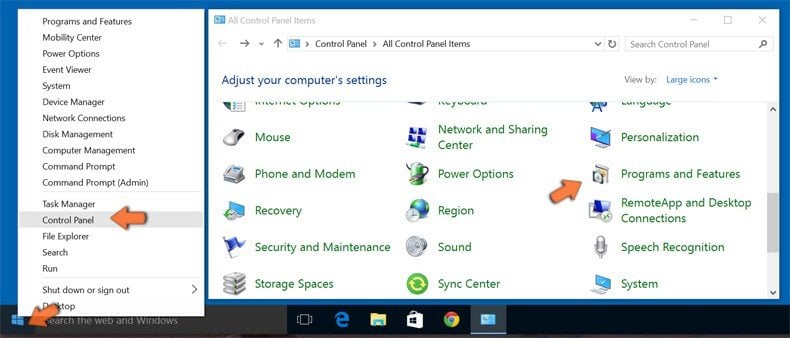
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.

In the uninstall programs window, look for any questionable application, select this entry and click "Uninstall" or "Remove".
After uninstalling the potentially unwanted application, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware from Internet browsers:
17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F may be installed together with unwanted browser plug-ins on Microsoft Edge, Google Chrome, or Mozilla Firefox. Therefore, you are advised to remove all potentially unwanted browser add-ons from your Internet browsers.
Video showing how to remove potentially unwanted browser add-ons:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:

Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons and remove them.
(at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons and remove them.

Optional method:
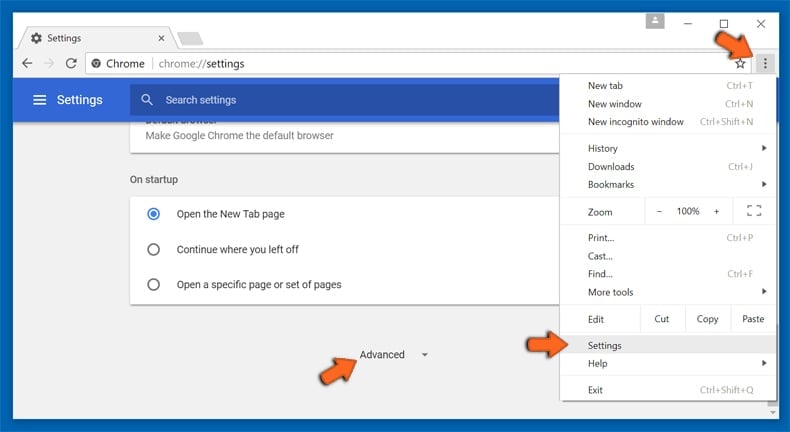
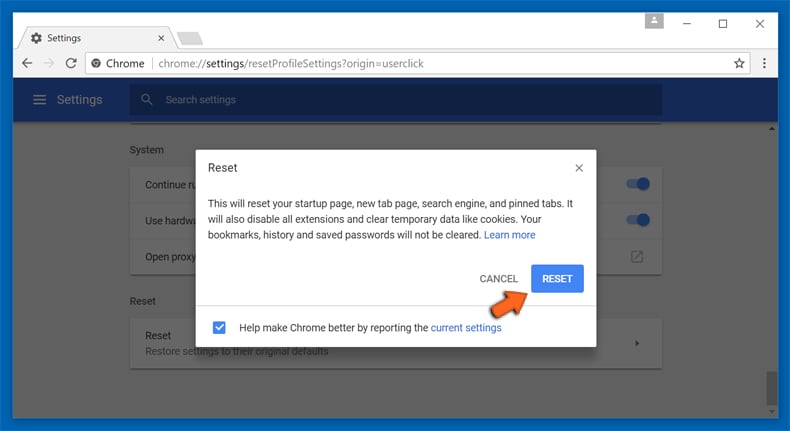
If you continue to have problems with removal of the 17uoetuihi6lsg4hdedt7puhf4fngbpd2f clipper, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
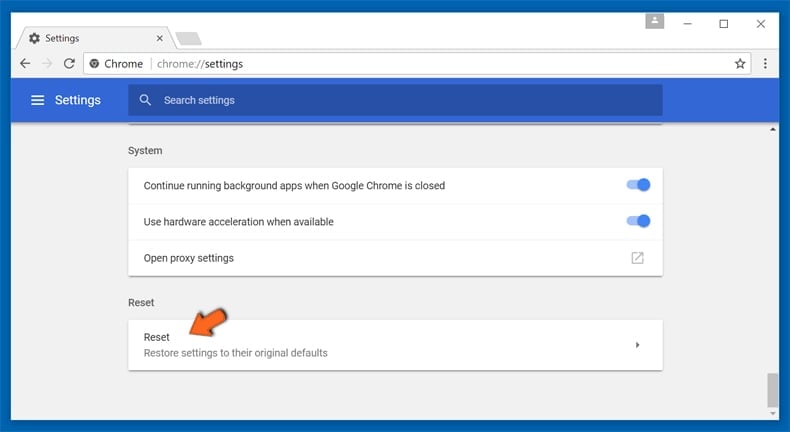
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plugins from Mozilla Firefox:
Remove malicious plugins from Mozilla Firefox:

Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons". Click on "Extensions", in the opened window remove all recently-installed suspicious browser plug-ins.
(at the top right corner of the main window), select "Add-ons". Click on "Extensions", in the opened window remove all recently-installed suspicious browser plug-ins.

Optional method:
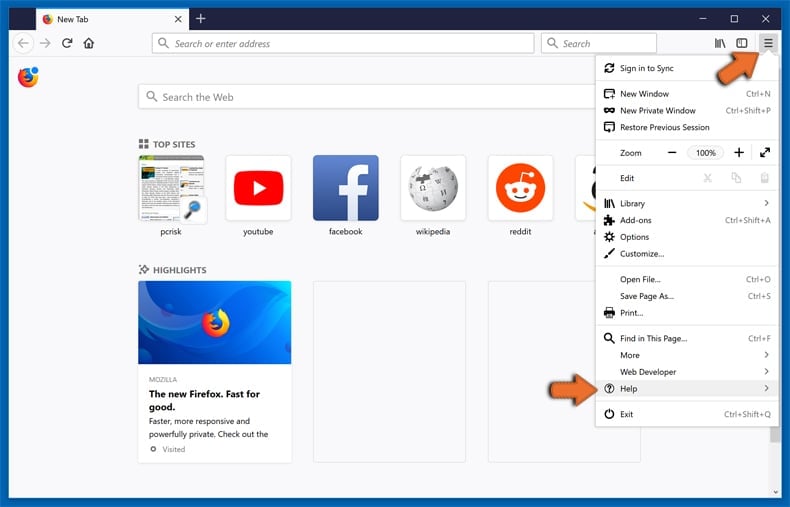
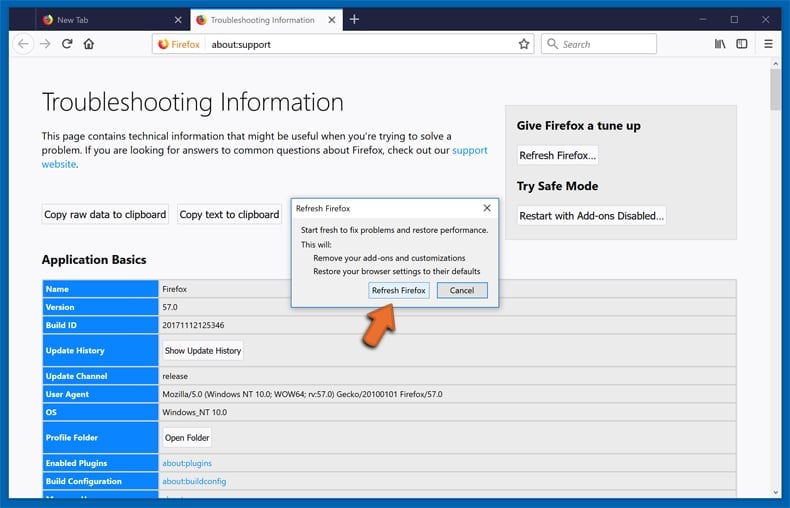
Computer users who have problems with 17uoetuihi6lsg4hdedt7puhf4fngbpd2f clipper removal can reset their Mozilla Firefox settings.
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
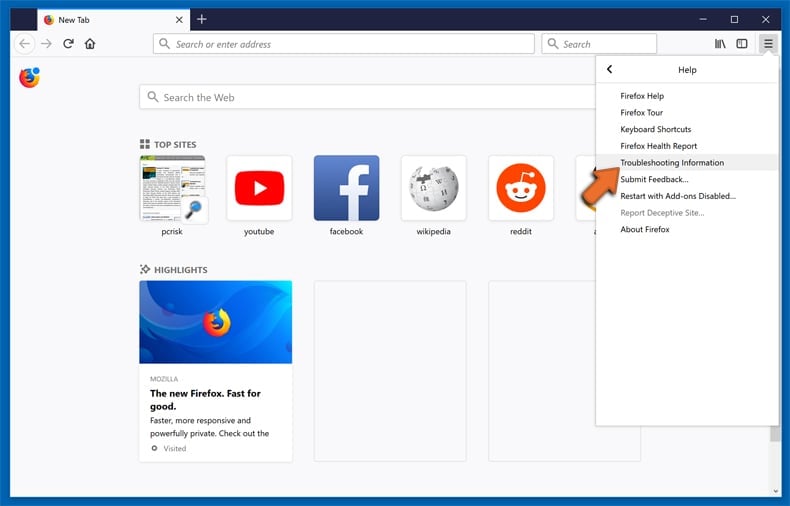
Select Troubleshooting Information.
In the opened window, click the Refresh Firefox button.
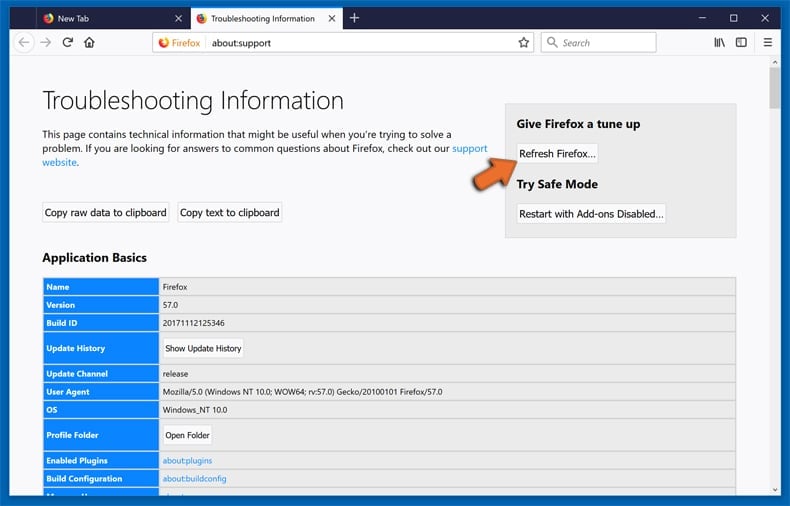
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
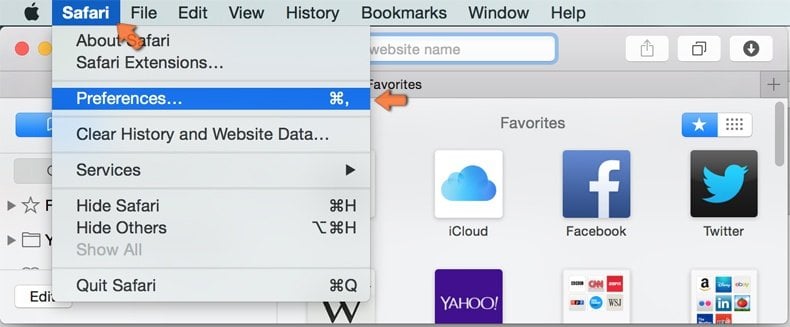
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
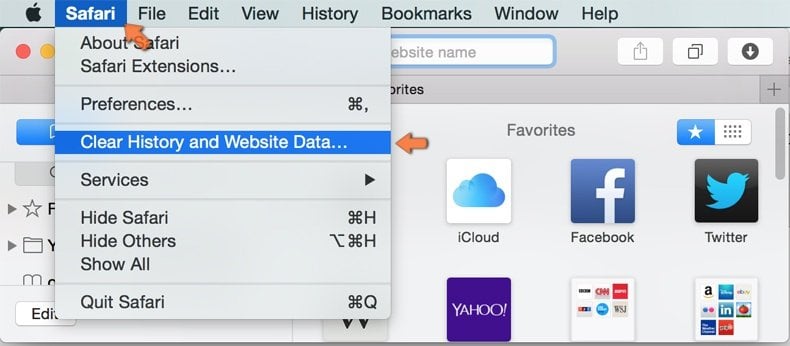
In the opened window select all history and click the Clear History button.

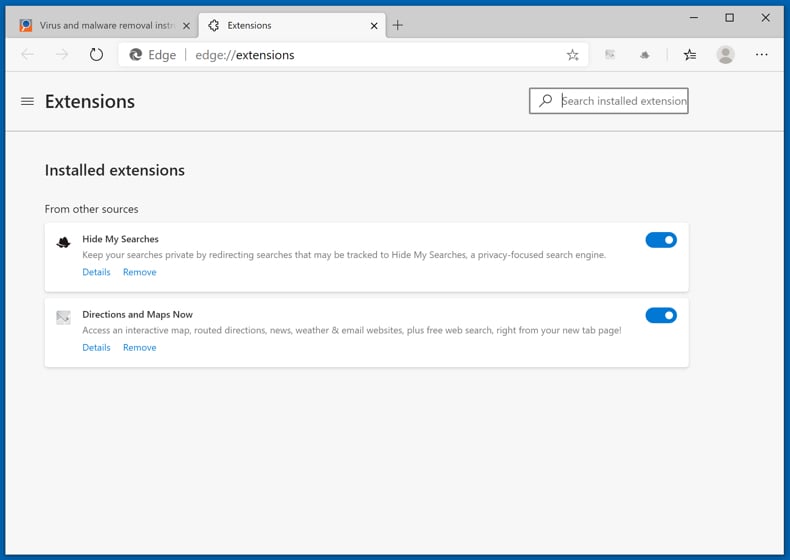
 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
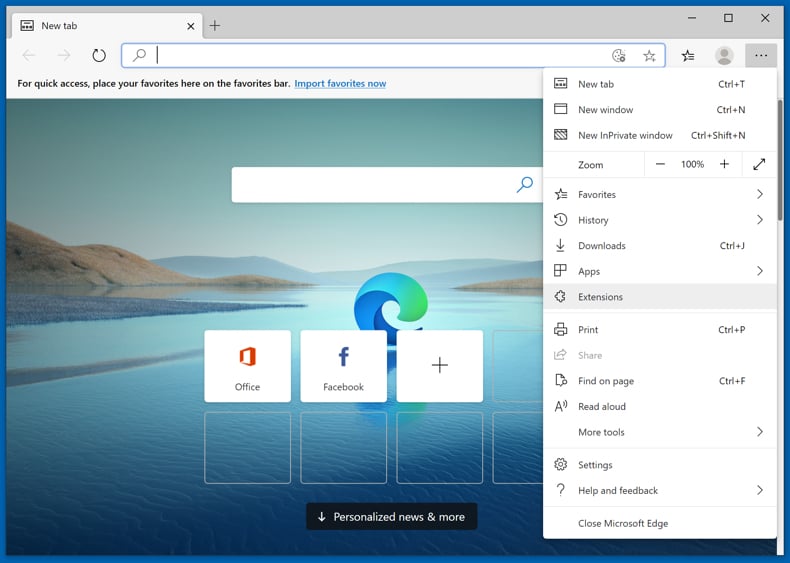
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
Optional method:
If you continue to have problems with removal of the 17uoetuihi6lsg4hdedt7puhf4fngbpd2f clipper, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
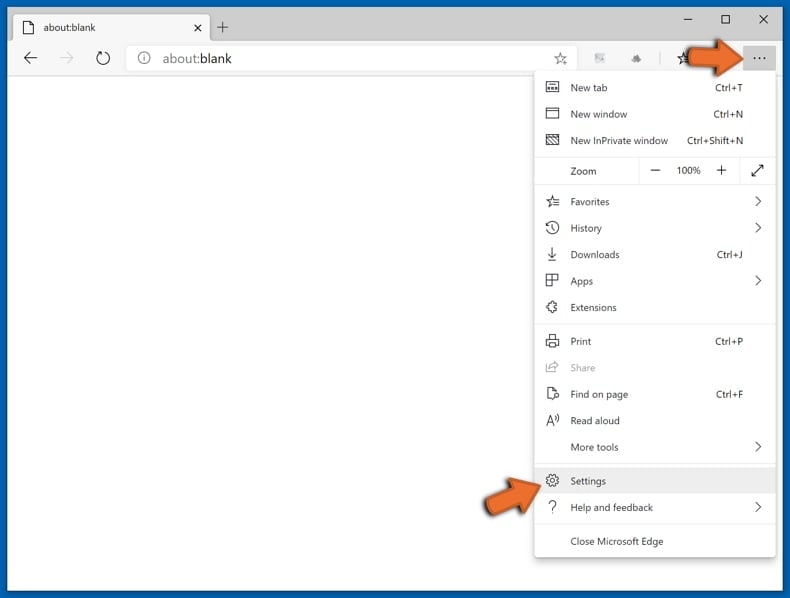
In the opened settings menu select Reset settings.
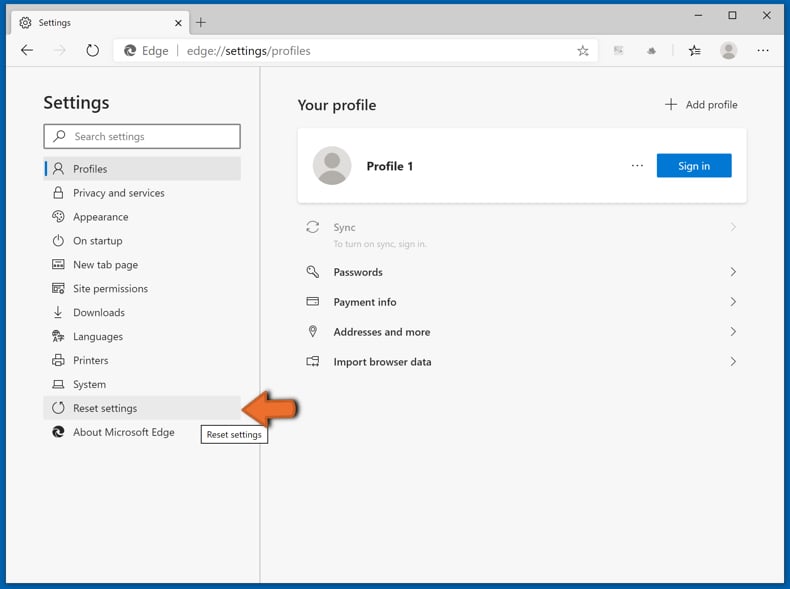
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
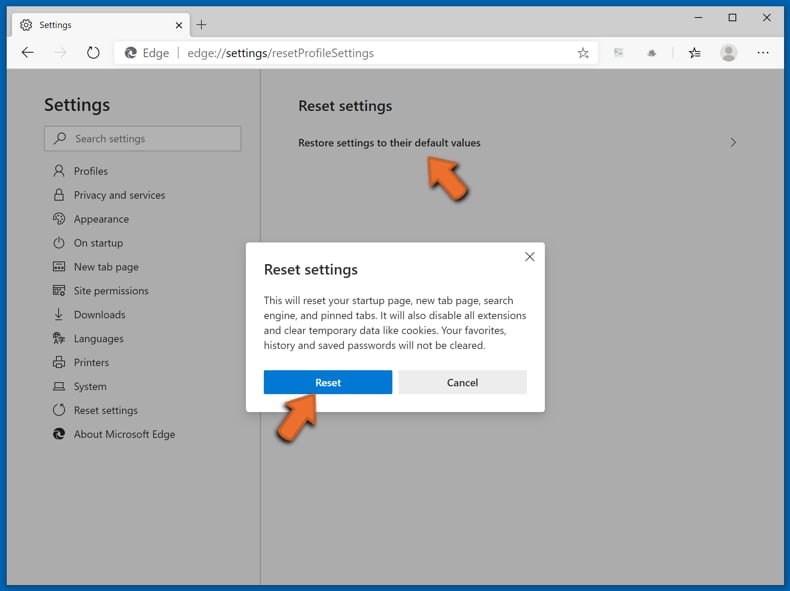
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Frequently Asked Questions (FAQ)
My computer is infected with 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F malware, should I format my storage device to get rid of it?
No, this clipper malware can be removed without formatting.
What are the biggest issues that 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F malware can cause?
What threats a malicious program poses - depends on its functionalities and the cyber criminals' aims. 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F is a clipper; it is designed to replace the cryptocurrency wallet addresses copied into the clipboard (copy-paste buffer) with those in the criminals' possession - thereby rerouting outgoing transactions to the attackers' wallets. Therefore, clipper infections can result in significant financial losses.
What is the purpose of 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F malware?
17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F operates by changing Bitcoin cryptocurrency wallet addresses copied into the clipboard with those owned by the cyber criminals. Thereby, when the victim makes an outgoing transaction - it is redirected. In other words, this malicious program is designed to generate revenue at victims' expense.
How did 17uoEtuihi6Lsg4hdedT7PUhF4FNgBPD2F malware infiltrate my computer?
We discovered this clipper through a website offering "cracked" software downloads. However, malicious programs are spread using various deceptive methods. The most popular distribution techniques include: illegal software activation tools ("cracks"), drive-by downloads, spam emails and messages, online scams, dubious download sources (e.g., unofficial and freeware sites, P2P sharing networks, etc.), and fake updates. Furthermore, some malware is capable of self-spreading via local networks and unplugged storage devices (e.g., external hard drives, USB flash drives, etc.).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and eliminate most of the known malware infections. It has to be stressed that running a complete system scan is crucial - since sophisticated malicious software typically hides deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion