Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Google App scam?
Scammers are using a fake Google application to steal CoinBase login credentials. They use malicious installers to inject modified Chrome browser or similar software that changes the Google Chrome shortcut target. When users try to access a legitimate CoinBase page, they get redirected to a fake one.

Google App scam in detail
This fake Google application gets installed on the operating system as "Chrome Software". Its setup alters Google Chrome (or installs a modified Chrome version). It sets the Chrome target to "C:\Users\[username]\AppData\Local\Google\Chrome Software\Chrome Software.exe" and adds the "google app" extension to a browser.
Also, the modified browser has the "Managed by your organization" feature added to it. The purpose of this fake Google app is to redirect users to a fake CoinBase page (coinbase.security[.]com) when they enter the address of a legitimate CoinBase page and steal entered login credentials (CoinBase accounts).
| Name | Google Software Scam |
| Threat Type | Fake Google application |
| Related Domain | coinbase[.]security.com |
| Detection Names (Installer) | Avast (Win32:Trojan-gen), Combo Cleaner (Gen:Variant.Jaik.47957), ESET-NOD32 (Multiple Detections), Kaspersky (Trojan.Win32.Mixer.t), Microsoft (Trojan:Win32/Downloader.GA!MTB), Full List Of Detections (VirusTotal) |
| Detection Names (Malicious Application) | MaxSecure (Trojan.Malware.300983.susgen), SentinelOne (Static ML) (Static AI - Suspicious Archive), Full List Of Detections (VirusTotal) |
| Detection Names (coinbase.security[.]com) | N/A (VirusTotal) |
| Distribution Methods | Deceptive pop-up ads and websites, fake installers |
| Damage | Stolen CoinBase accounts |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
More details about a fake Google application
Additionally, the "google app" extension can read and change all users' data on all websites and manage installed apps, extensions, and themes. This fake Google Chrome browser and its components must be removed from the affected operating systems and browsers as soon as possible.
How did this app got installed on my computer?
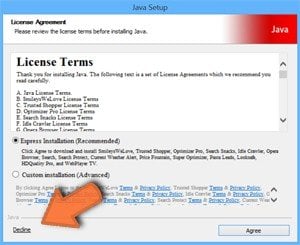
The installer for the fake Google Chrome (or its modifier) likely is distributed through some deceptive website or advertisements designed to run certain scripts. It is also possible that it is available for download on other unreliable sources like Peer-to-Peer networks, free file hosting pages, freeware download sites.
How to avoid installation of unwanted applications?
Use official websites as sources for downloading software and files and avoid using other sources (like P2P networks, unofficial sites). Do not click on advertisements appearing on dubious websites. Do not download and install programs until all unwanted apps included in their downloaders and installers are deselected.
If your computer is already infected with rogue applications, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Fake Google application redirects to a fake CoinBase website used to steal login credentials (GIF):

Screenshot of the fake CoinBase website:

Screenshot of the Chrome shortcut target changed to "C:\Users\[username]\AppData\Local\Google\Chrome Software\Chrome Software.exe":

Screenshot of the "google app" description:

Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Google App scam?
- STEP 1. Uninstall adware applications using Control Panel.
- STEP 2. Remove rogue plug-ins from Google Chrome.
- STEP 3. Remove adware-type extensions from Mozilla Firefox.
- STEP 4. Remove malicious extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Unwanted software removal:
Windows 11 users:
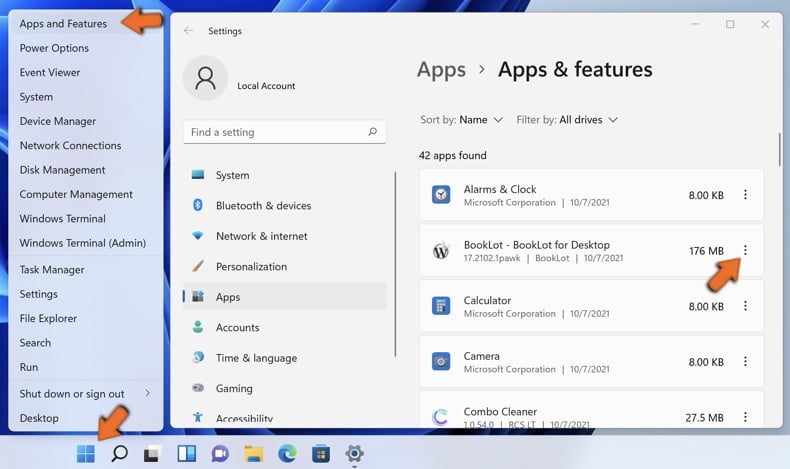
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
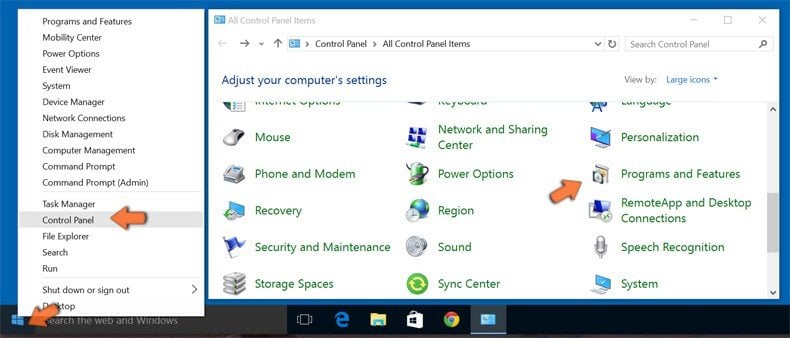
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.

In the uninstall programs window, look for any potentially unwanted applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the potentially unwanted application that causes Google App scam redirects, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware from Internet browsers:
Video showing how to remove potentially unwanted browser add-ons:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:

Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate "google app" and other recently-installed suspicious browser add-ons and remove them.
(at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate "google app" and other recently-installed suspicious browser add-ons and remove them.

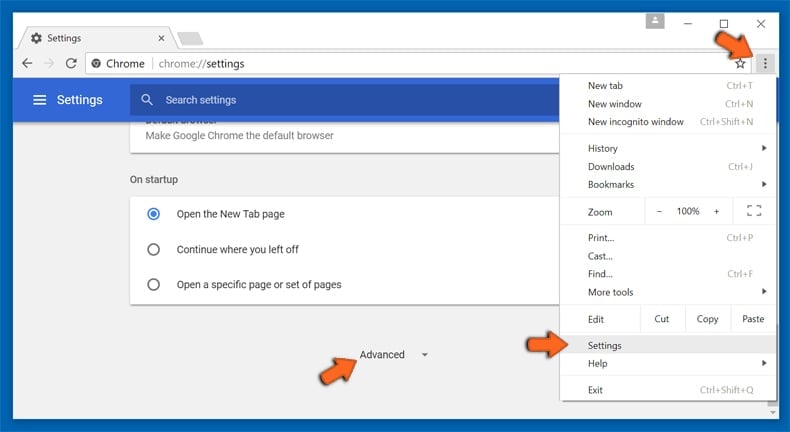
Optional method:
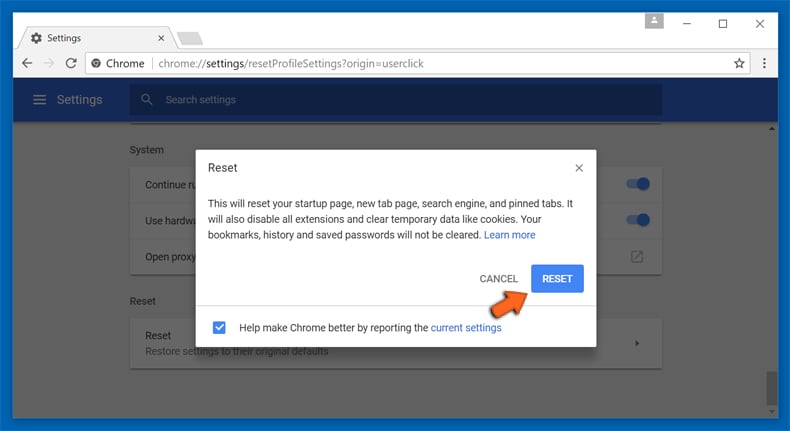
If you continue to have problems with removal of the google software scam, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
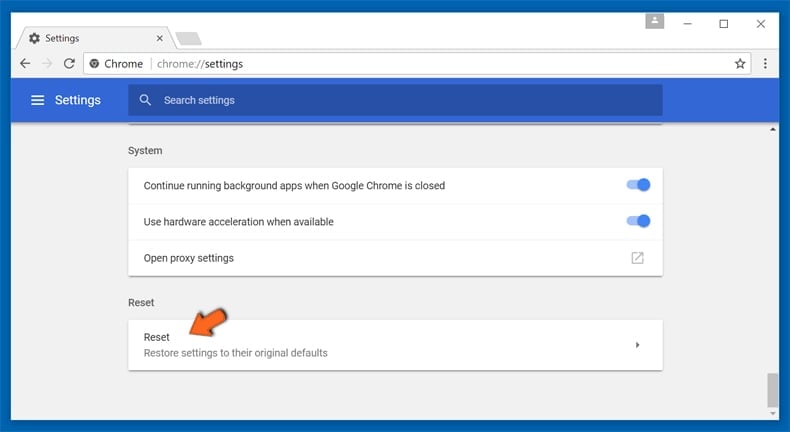
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plug-ins from Mozilla Firefox:
Remove malicious plug-ins from Mozilla Firefox:

Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons". Click "Extensions", in the opened window, remove all recently-installed suspicious browser plug-ins.
(at the top right corner of the main window), select "Add-ons". Click "Extensions", in the opened window, remove all recently-installed suspicious browser plug-ins.

Optional method:
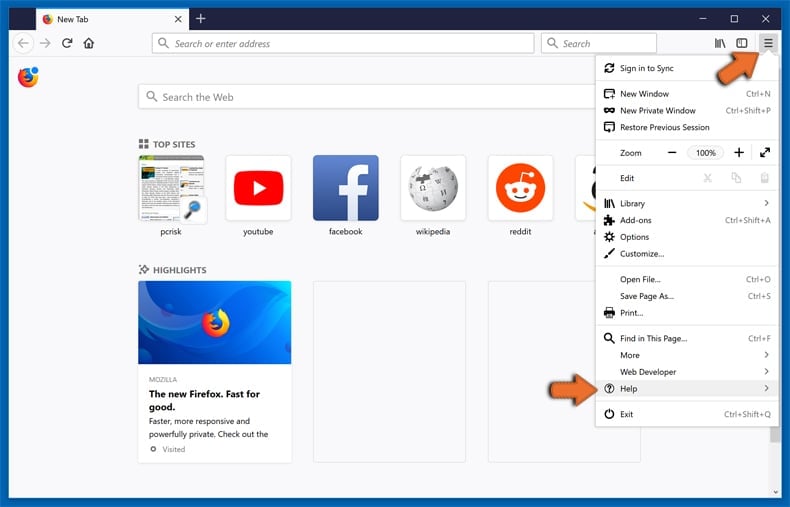
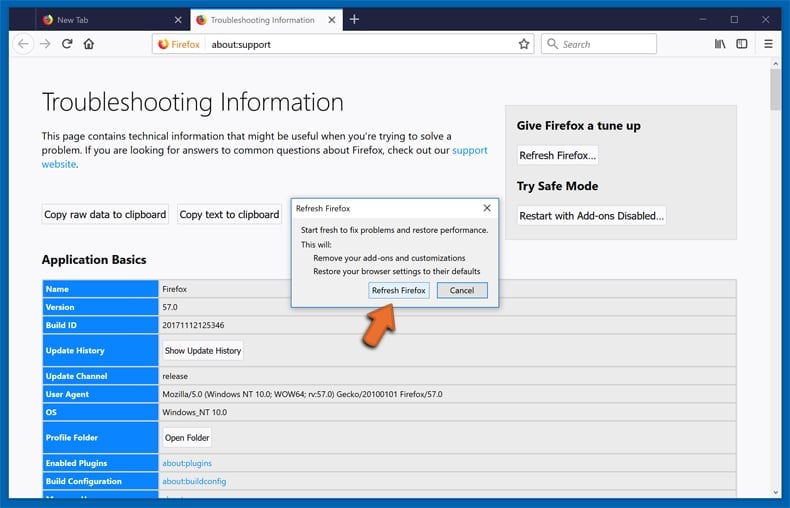
Computer users who have problems with google software scam removal can reset their Mozilla Firefox settings.
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
Select Troubleshooting Information.
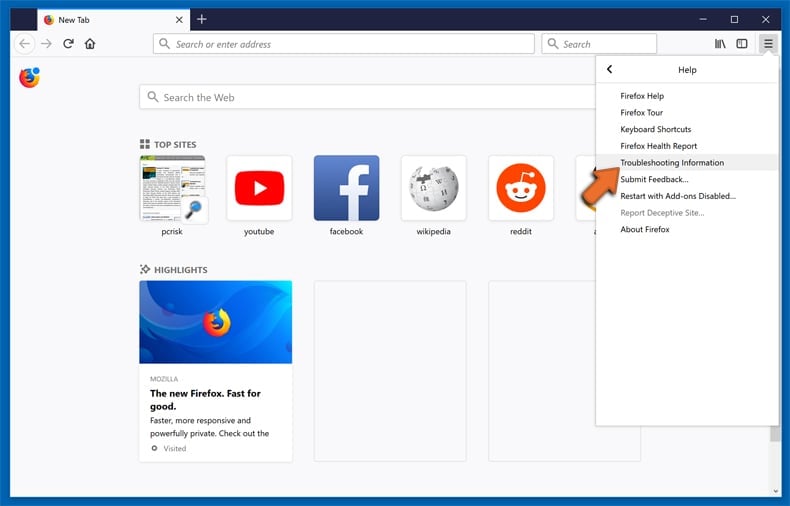
In the opened window, click the Refresh Firefox button.
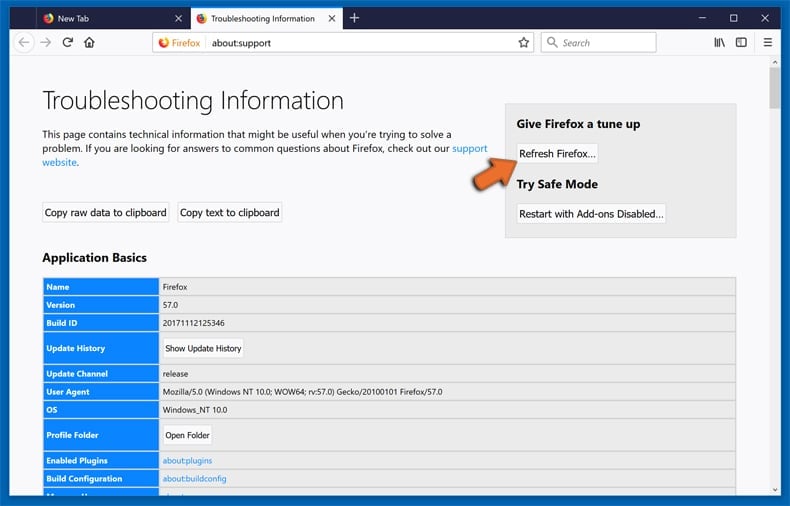
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
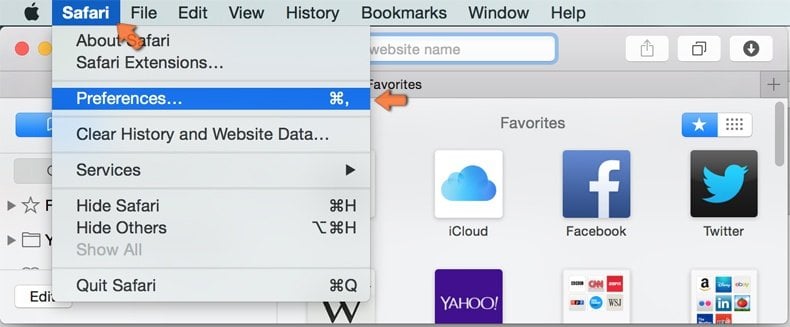
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
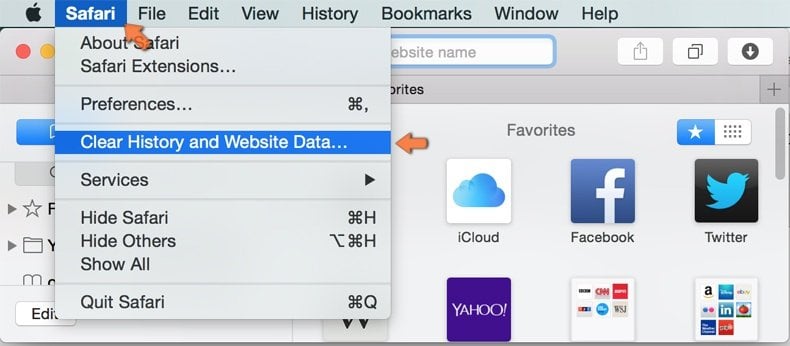
In the opened window select all history and click the Clear History button.

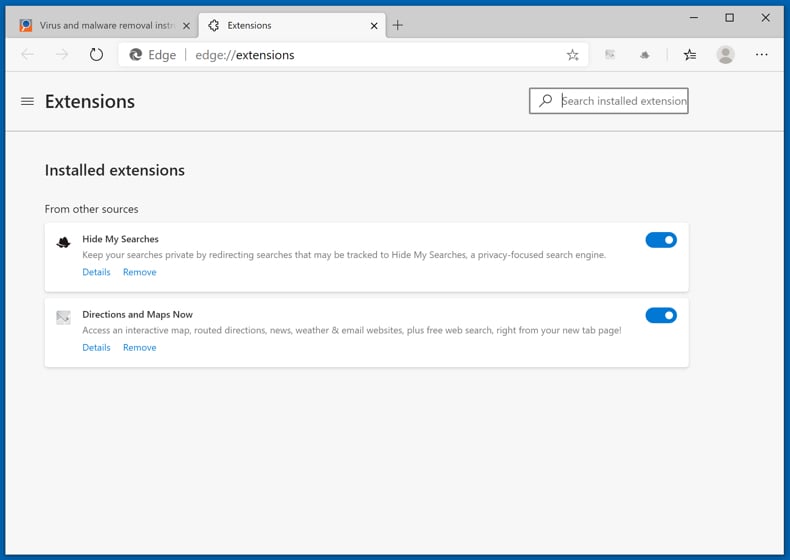
 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
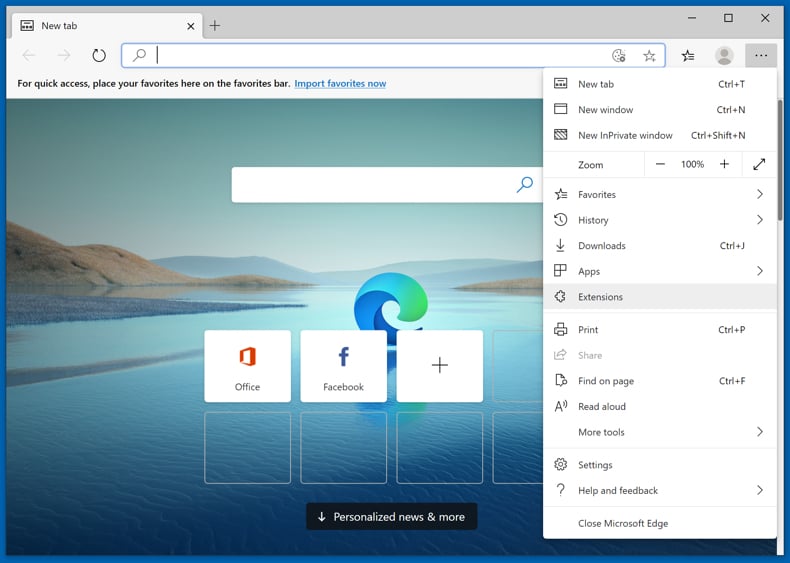
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
Optional method:
If you continue to have problems with removal of the google software scam, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
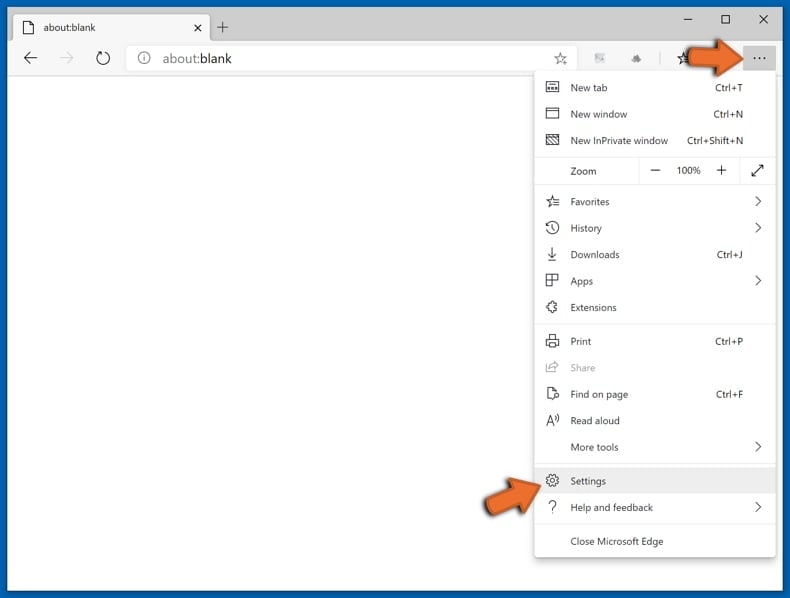
In the opened settings menu select Reset settings.
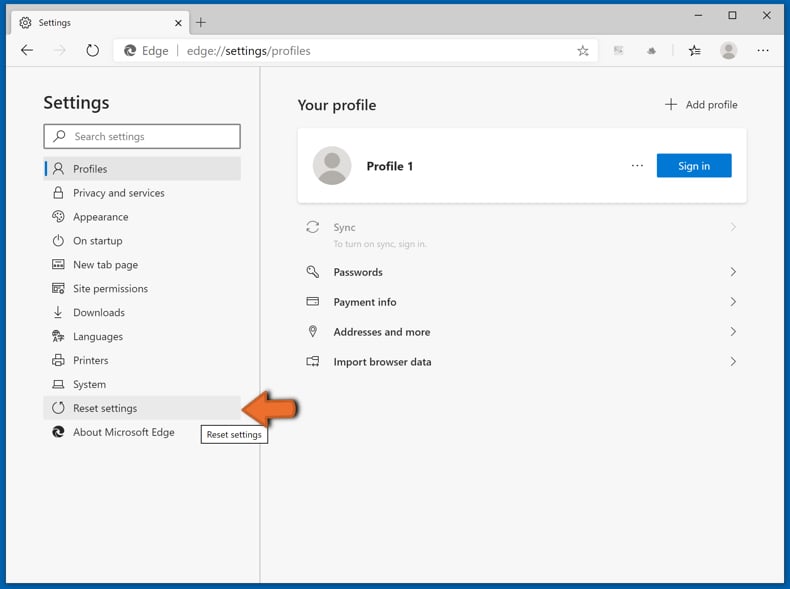
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
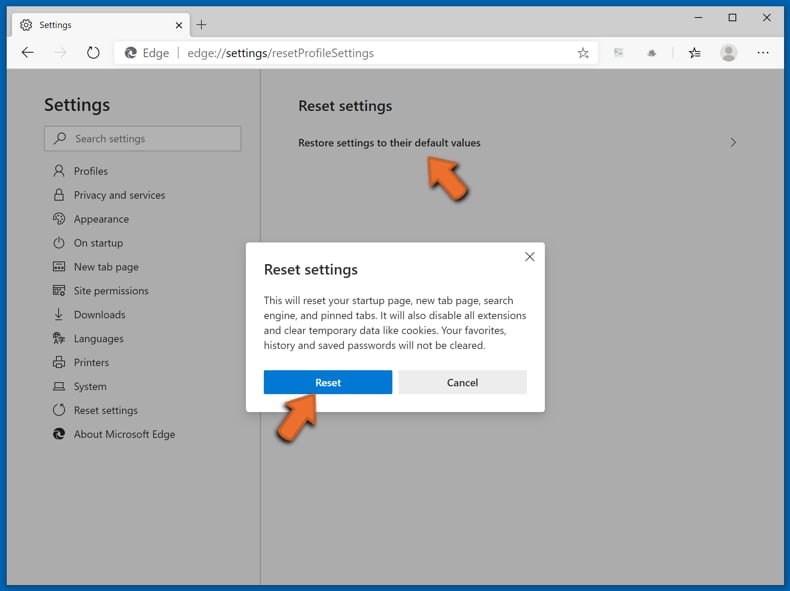
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
 Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Post a comment:
If you have additional information on google software scam or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
My computer is infected with a fake Google Chrome application, should I format my storage device to get rid of it?
This fake application/Chrome modifier can be removed without formatting. Removal guide for such software is provided above
What are the biggest issues that malware can cause?
It depends on the type of malware. Having a computer infected with malware can lead to identity theft, financial losses, decreased computer performance, further infections, and other problems.
What is the purpose of a fake Google Chrome browser/Chrome modifier?
The purpose of this app is to redirect users to a fake CoinBase website and obtain login credentials.
How did a malware infiltrate my computer?
In most cases, malicious apps are distributed using various phishing and other social engineering techniques (like malicious emails, fake system warning messages), drive-by downloads, Peer-to-Peer networks, software cracking tools.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and eliminate almost all known malware infections. It is recommended to scan the operating system fully (using a full scan option) because malware can be hiding deep in the operating system.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion