Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Lidl email scam?
Usually, phishing emails are disguised as official letters from legitimate companies, organizations (for example, banks, couriers). Scammers use these emails to trick recipients into providing personal information (for example, credit card details, login credentials).
This particular email is disguised as a letter from Lidl (a European grocery store). Scammers use it to trick recipients into entering personal information on a phishing website.
Lidl phishing scam in detail
As written in this phishing email, whoever received this email has been chosen from 250 people to get a gift in exchange for participation in a survey. It contains a link ("STARTEN" button) that opens a fake survey.
After answering a couple of questions on that website, it opens another page designed to trick visitors into entering some personal information. That other page suggests that visitors need to enter their name, surname, country, city, home, and email address to receive an iPhone 12 Pro for €1.50 (or some other electronic device).
Typically, scammers behind emails like this one attempt to trick recipients into believing that they will receive some gift after paying a small amount of money (e.g., administration, shipping, or another fee). In this particular case, scammers seek to trick recipients into believing that they have a chance to get up to a 95% discount on an electronic device.
It is important to mention that scams of this type usually are used to trick recipients into providing their credit card details, including CVV code and expiry date. In order to avoid becoming a victim of identity theft, suffer monetary loss, or other similar issues, it is highly advisable not to trust phishing emails and websites.
| Name | Lidl Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipients where chosen to get a gift for participation in a survey |
| Disguise | Letter from Lidl |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Phishing emails in general
There are many examples of phishing emails, a couple of them are "DBS Bank Email Scam", "RingCentral Email Scam", and "Bonifico Effettuato Email Scam". As mentioned in the first paragraph, phishing emails can be used to trick recipients into providing email addresses, usernames, passwords, or other login credentials as well.
It is important to mention that email can be used as a channel to deliver malware. The main difference between an email used to trick recipients into providing personal information and installing malware on their computers is that the second type of email contains a malicious link or attachment.
How do spam campaigns infect computers?
As a rule, emails used to distribute malicious software contain a malicious file (attachment) or a link to a malicious website. In one way or another, the purpose of emails of this type is to trick recipients into executing a malicious file.
Usually, cybercriminals use executable files like EXE, archive files like ZIP, RAR, JavaScript files, PDF documents or Microsoft Office documents to deliver malware via emails. Quite often, those files are disguised as important, official document (e.g., invoices, purchase orders, documents related to COVID-19).
It is worth mentioning that malicious Microsoft Office documents do not infect systems unless users enable editing or content (macros commands) in them. Although, documents opened with older MS Office versions (with versions released before the year 2010) do not have the "Protected View" mode that prevents malicious documents from automatically infecting computers.
How to avoid installation of malware?
Installed software has to be updated and activated with tools or functions provided by the official developers. It is never safe to use third-party, unofficial tools for that. Also, it it is illegal to use cracked software (or use cracking tools to bypass software activation).
Files, links in irrelevant emails received from unknown, suspicious addresses should be left unopened. It is common that emails of this kind are designed to look like important, official letters from legitimate companies and contain malicious links or files.
Programs (and files) should be downloaded from official, trustworthy websites. It is not safe to use other channels, sources for that. Virus scans should be performed regularly, and it should be achieved using a reputable antivirus or anti-spyware software. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
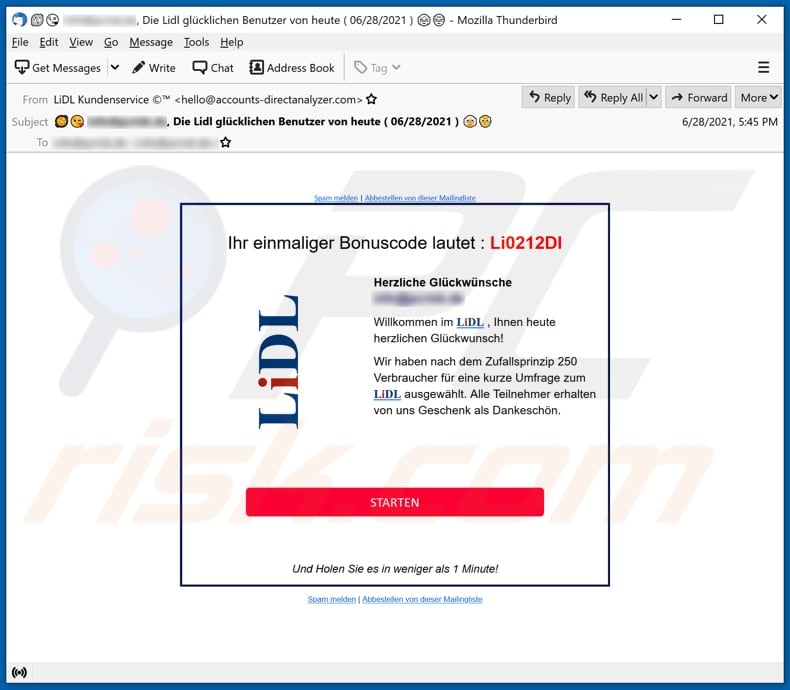
Text presented in the Lidl email scam (German variant):
Suject: ********, Die Lidl glücklichen Benutzer von heute ( 06/28/2021 )
Spam melden | Abbestellen von dieser Mailingliste
Ihr einmaliger Bonuscode lautet : Li0212Dl
LiDL
Herzliche Glückwünsche
********Willkommen im LiDL , Ihnen heute herzlichen Glückwunsch!
Wir haben nach dem Zufallsprinzip 250 Verbraucher für eine kurze Umfrage zum LiDL ausgewählt. Alle Teilnehmer erhalten von uns Geschenk als Dankeschön.
STARTEN
Und Holen Sie es in weniger als 1 Minute!
Spam melden | Abbestellen von dieser Mailingliste
Appearance of the fake survey and deceptive website used to extract personal information (GIF):

Text in the first page:
Lidl.de - Lidl lohnt sich.Juli 2 2021
% DEAL DES TAGES %
Lieber Glückspilz!
Beeilen Sie sich: Beantworten Sie unsere Befragung und erhalten Sie ein Geschenk.
Sie haben vier Minuten Zeit, um die folgenden Fragen zu beantwortenBis Zu 95% Rabatt
Was ist dein Geschlecht?
Männlich
Weiblich© 2021 Alle Rechte vorbehalten.
Diese Website steht in keiner Verbindung mit Lidl, wird nicht von Lidl unterstützt und erhebt keinen Anspruch darauf, Marken, Handelsnamen oder Rechte zu vertreten, die mit den jeweiligen Produkten in Zusammenhang stehen.
HOLEN SIE SICH IHR KOSTENLOSES GESCHENK!
Wir haben 250 Konsumenten aus Deutschland, um an einer kurzen Befragung von Lidl teilzunehmen. Alle Teilnehmer werden (1) optionale Belohnung erhalten. Sie haben die Wahl zwischen Elektronikartikeln und vielem mehr.
Ihr einmaliger Bonuscode lautet :Li0212Dl
Klicken Sie auf "STARTEN", um fortzufahren
A Dutch variant of Lidl-themed email scam:
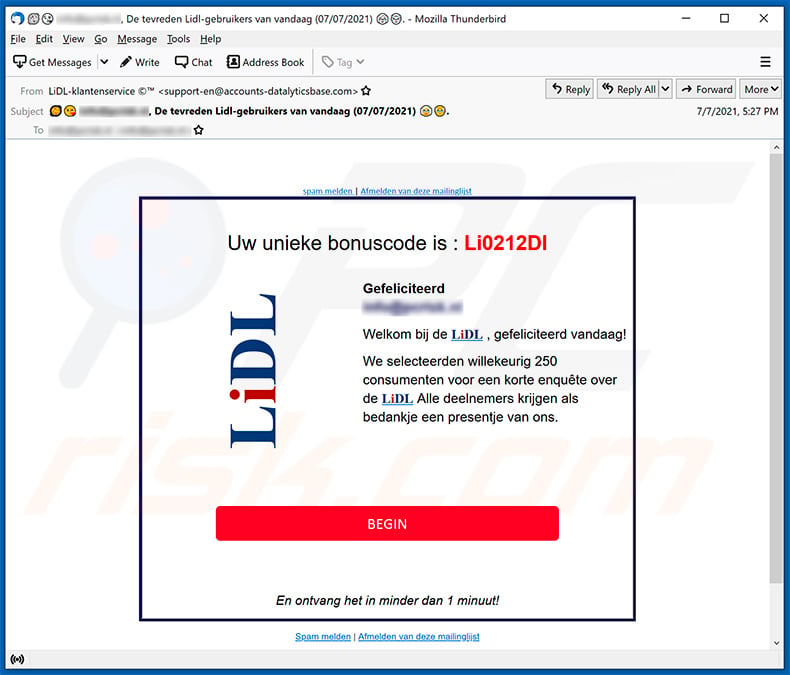
Text presented within:
Subject: ********, De tevreden Lidl-gebruikers van vandaag (07/07/2021)
spam melden | Afmelden van deze mailinglijst
Uw unieke bonuscode is : Li0212DlLiDL
Gefeliciteerd
********Welkom bij de LiDL , gefeliciteerd vandaag!
We selecteerden willekeurig 250 consumenten voor een korte enquête over de LiDL Alle deelnemers krijgen als bedankje een presentje van ons.
BEGINEn ontvang het in minder dan 1 minuut!
Spam melden | Afmelden van deze mailinglijst
Appearance of the promoted phishing website:

Text presented within:
Lidl.nl July 8 2021
% DEAL VAN DE DAG %
Beste Gelukkige Klant!
Schiet op: beantwoord onze vragenlijst en ontvang een cadeautje.
U heeft vier minuten om de volgende vragen te beantwoorden.Tot 95% korting
Wat is je geslacht?
Mens Vrouw© 2021 Alle rechten voorbehouden.
Deze website is niet gelieerd aan Lidl, wordt niet ondersteund door Lidl en claimt niet merken, handelsnamen of rechten te vertegenwoordigen die verband houden met de respectievelijke producten.
ONTVANG JE GRATIS CADEAU!
We hebben 250 consumenten uit Nederland om deel te nemen aan een korte Lidl-enquête. Alle deelnemers ontvangen (1) optionele beloningen. U heeft de keuze tussen elektronica en nog veel meer.
Uw unieke bonuscode is: Li0212Dl
Klik op "BEGIN" om door te gaan
A French variant of Lidl-themed email scam:

Text presented within:
Subject: ********, Les utilisateurs satisfaits de Lidl d'aujourd'hui (07/07/2021)
signaler comme spam | Se désinscrire de cette liste de diffusion
Votre code bonus unique est : Li0212DlLiDL
Toutes nos félicitations
********Bienvenue à LiDL , Félicitations à vous aujourd'hui!
Nous avons obtenu au hasard 250 consommateurs pour un sondage rapide LiDL . Tous les participants reçoivent un cadeau de notre part en guise de remerciement.
DÉMARRER
Et obtenez-le en moins d'1 minute!
signaler comme spam | Se désinscrire de cette liste de diffusion
Appearance of the promoted phishing website:

Text presented within:
Lidl.fr - Lidl en vaut la peine.July 8 2021
% OFFRES DU JOUR %
Cher Chanceux!
Dépêchez-vous : répondez à notre questionnaire et recevez un cadeau.
Vous disposez de quatre minutes pour répondre aux questions suivantesJusqu'à 95% de remise
Quel est votre sexe ?
Homme
Femelle© 2021 Tous droits réservés.
Ce site Web n'est pas affilié à Lidl, n'est pas pris en charge par Lidl et ne prétend pas représenter des marques, des noms commerciaux ou des droits associés aux produits respectifs.
OBTENEZ VOTRE CADEAU GRATUIT!
Nous avons 250 consommateurs de France pour participer à une courte enquête Lidl. Tous les participants recevront (1) récompenses facultatives. Vous avez le choix entre l'électronique et bien plus encore.
Votre code bonus unique est : Li0212Dl
Cliquez sur "DÉMARRER" pour continuer
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Lidl spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
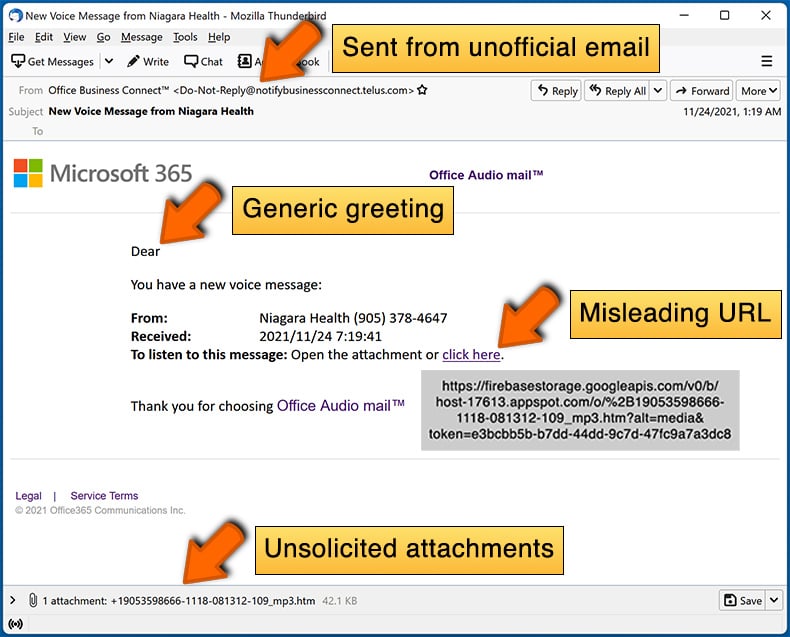
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:
What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. Cyber criminals distribute these letters by the thousand with the hopes that at least some of the recipients will fall for their scams.
I have provided my personal information when tricked by this spam email, what should I do?
If you have disclosed log-in credentials - change the passwords of all possibly exposed accounts and inform their official support without delay. And if you've provided other private data (e.g., ID card details, credit card numbers, etc.) - immediately contact the corresponding authorities.
I have read a spam email but didn't open the attachment, is my computer infected?
No, opening/reading an email will not initiate any system infection processes. Malware download/installation chains are triggered when the attachments or links found in spam mail are opened/clicked.
I have downloaded and opened a file attached to a spam email, is my computer infected?
If it was an executable (.exe, .run, etc.) - most likely, yes - your device was infected. And if it was a document (.doc, .pdf, .xls, etc.) - you might have avoided jumpstarting an infection chain. These formats may require additional user interaction (e.g., enabling macro commands) to start downloading/installing malware.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is capable of detecting and eliminating nearly all known malware infections. It has to be mentioned that sophisticated malicious software typically hides deep within systems - therefore, performing a full system scan is essential.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion