Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is RevengeRAT?
RevengeRAT (also known as Revetrat) is high-risk computer infection categorized as a remote access trojan (RAT). The purpose of this malware is to provide cyber criminals with remote access to the infected machine and allow them to manipulate it.
Research shows that cyber criminals proliferate this infection using spam email campaigns (malicious MS Office attachments). Having a trojan-type infection such as RevengeRAT installed on your computer can cause many issues.

RevengeRAT malware overview
RATs allow threat actors (cyber criminals) to manipulate infected machines remotely. Using RevengeRAT, they can manage system services/process/files, edit the Windows Registry entries and hosts file, log keystrokes, steal account credentials, access hardware (e.g., webcam), execute shell commands, and so on. Therefore, these people can cause significant damage.
Firstly, modifications performed to the system might diminish performance, and recovery could be difficult or even impossible. Additionally, by logging keystrokes and stealing account credentials, cyber criminals cause serious privacy issues. Threat actors aim to generate as much revenue as possible.
Therefore, hijacked bank, social network, email, and other accounts can be misused in various ways, such as through direct money transfers, online purchases, borrowing money from users' contacts, and so on. Victims of this trojan could lose savings, accrue significant debt, and have their identities stolen.
RevengeRAT also allows cyber criminals to execute shell commands to control the system in various ways. Be aware that shell commands are used to cause chain infections by injecting additional malware into the system. RATs such as RevengeRAT are typically used to proliferate infections that have different capabilities/purposes (e.g., ransomware, cryptominers, etc.).
In summary, RevengeRAT poses a significant threat to your privacy/computer safety and should be eliminated immediately.
| Name | Revetrat virus |
| Threat Type | Trojan, Password-stealing virus, Banking malware, Spyware |
| Detection Names | Avast (Win32:MalwareX-gen [Trj]), BitDefender (Gen:Variant.Binder.1), ESET-NOD32 (Win32/TrojanDropper.Binder.NBH), Kaspersky (HackTool.Win32.Binder.bs), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Trojan-type malware examples
There are many trojan-type infections that have similar characteristics to RevengeRAT including TrickBot, FormBook, Emotet, Hancitor, and Adwind - the list of examples goes on.
The functionality might slightly differ (some gather information, whilst others cause chain infections, mine cryptocurrency, and so on), however, they all pose threat to your privacy and computer safety. Therefore, remove trojan-type infections immediately.
How did RevengeRAT infiltrate my computer?
As mentioned above, RevengeRAT is typically proliferated using spam email campaigns that deliver malicious Microsoft Office documents, however, to hide their traces and avoid anti-virus detection, cyber criminals perform a sequence of actions to inject malware into the system. Once opened, the deceptive attachment asks to enable macro commands.
Once enabled, the document will use a template injection technique to download and open a OLE document, which contains the malicious macros. This document uses macro commands to download and run an MS Excel file that decodes and executes another command used to download a malicious JavaScript.
The script is hosted on a Blogspot page, the domain of which is shortened using the Bit.ly service. Malicious JavaScript is then executed, which grabs commands from Pastebin pages and ultimately runs them to inject RevengeRAT into the system.
Before performing this, however, the malicious JavaScript kills a number of running processes, including Windows Defender and several apps relating to Microsoft Office. It also disables the Office's Protected View mode. The entire process may seem complicated, however, it is quite simple.
Bear in mind that Blogspot, Bit.ly, and Pastebin are legitimate websites/services and have no association with RevengeRAT malware. These are simply tools used by cyber criminals. Furthermore, RevengeRAT is publicly accessible in hacker forums and, therefore, anyone can download and start proliferating this malware, and the distribution methods are likely to vary.
Trojan-type infections are also often distributed using unofficial software download sources (free file hosting websites, freeware download websites, Peer-to-Peer [P2P] networks, etc.), and fake updaters/cracks.
How to avoid installation of malware?
Handle all email attachments with care. If the received attachment is irrelevant or does not concern you, do not open anything. Files/links received from suspicious/unrecognizable email addresses should be ignored.
Bear in mind that criminals often send emails containing messages that are literally too good to be true (e.g., "you have won a million dollars", "someone transferred money to your bank account", etc.). Attachments are often presented as 'important documents' (e.g., invoices, receipts, bills, etc.). Never fall for these tricks.
Also use 2010 or newer versions of Microsoft Office, since previous versions are not implemented with Protected View mode, which prevents new documents from automatically running macro commands. Download programs from official sources only, preferably using direct download links.
Third party downloaders/installers, often include rogue applications and, therefore, these tools should never be used. Keep installed applications/operating systems up-to-date, however, use only implemented functions or tools provided by the official developer.
Cracking applications should also not be considered, since software piracy is a cyber crime and many cracking tools are fake. Thus, the risk of infections is extremely high. The key to computer safety is caution. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Examples of spam emails used to spread RevengeRAT virus;
Example 1:

Text presented within:
Subject: Contract Standby // Cargo Charter request
Dear on duty,
We are searching for the cargo aircraft to fulfill below contract:1. Flight shall be operated everyday for 5-8 months of continuous operation commencing from 15th May, 2021
2. Cargo details:
Total weight: 2500-4550 kg
Amount of boxes: +- 1000 boxes
Size of boxes: 20x20x20 sm. cube and 40x40x40 sm. cube.
Commodities: Medical Kits (Non DG)
Port of Loading: Shanghai or any preferable option in ChinaPlease provide us with your availability and your best price quotation for the charter flight as per the attached ports of discharging details.
Also include all taxes and fees. If any questions please feel free to ask us.
NOTE: client has received all permits and authorizations in order to proceed with this flight without any further delay.Many thanks in advance and we look forward in setting up this cargo flight with you.
Best Regards
********
Example 2:

Text presented within:
Subject: [REMINDER] Invitation to Airbus Family Worldwide Symposium
Dear Customer,
Airbus is pleased to invite you to the Airbus Family Symposium which will take place from Wednesday 12th to Friday 14th of May 2021.
The event will be an opportunity for us to provide you with an operational overview of what has been done to support all Airbus fleet in January 2021 to April 2021 through various virtual sessions & conferences. We will also focus on what are going to be the next steps in the support & development of the Airbus Family.
The agenda thematics are focusing around the "Customer Support * Fleet efficiency" aspects and are not technically orientated.
Please find attached the global agenda of the event which is based on Toulouse (France) time (GMT+2).
We kindly invite you to confirm your participation and not later than Monday 10th of May by signing on the attached global agenda of the event and revert back immediately.
You will be provided with the connection details, once you have confirmed your participation.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is RevengeRAT?
- STEP 1. Manual removal of RevengeRAT malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically.
To remove this malware we recommend using Combo Cleaner Antivirus for Windows. If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
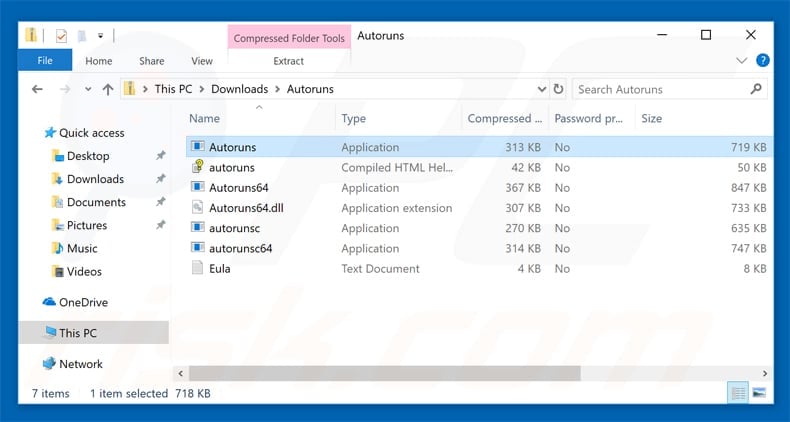
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup. Click the "Restart now" button.
Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings". Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard.
In the "choose an option" window click on the "Troubleshoot", next select "Advanced options". In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.
 In the Autoruns application, click "Options" at the top and uncheck the "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck the "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software.
To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with RevengeRAT malware, should I format my storage device to get rid of it?
No, RevengeRAT's removal does not necessitate formatting.
What are the biggest issues that RevengeRAT malware can cause?
RevengeRAT is a Remote Access Trojan (RAT). Malicious programs of this kind are designed to enable remote control over machines. For example, RevengeRAT can control the device, record information (keylogging, webcam recording, etc.), execute shell commands, and perform other actions. Since this program is capable of installing content onto devices, it may be used to infect systems with additional malware - thereby broadening the scope of the threats it poses. In general, malware infections can result in diminished system performance or failure, data loss, hardware damage, severe privacy issues, financial losses, and even identity theft.
What is the purpose of RevengeRAT malware?
The threats posed by malware (or a maliciously used legitimate program) depend on its capabilities and the attackers' aims. Most malware infections are employed to generate revenue for the cyber criminals. Other potential reasons include - attackers' amusement, process distribution (e.g., websites, services, companies, etc.), personal vendettas, and politically/geopolitically motivated attacks.
How did RevengeRAT malware infiltrate my computer?
Malware is primarily spread through drive-by (stealthy and deceptive) downloads, malicious attachments/links in spam mail, online scams, freeware and third-party download sites, P2P sharing networks (Torrent clients, Gnutella, etc.), illegal software activation tools ("cracks"), and fake updates. Some malicious programs can self-proliferate via local networks and removable storage devices (e.g., external hard drives, USB flash drives, etc.).
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can detect and eliminate almost all known malware infections. It must be stressed that performing a complete system scan is crucial - since high-end malicious programs typically hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion