How to identify malicious spam mail like the "Purchase Order" emails
Phishing/ScamAlso Known As: Purchase Order spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "Purchase Order Email Virus"?
"Purchase Order Email Virus" is another spam email campaign that shares similarities with Client Requirements Email Virus, Order Confirmation Email Virus, and many others. As usual, this campaign is used to proliferate malware (to be specific, Pony trojan).
Developers send thousands of emails that contain deceptive messages encouraging users to open a malicious attachment. Once opened, the file immediately infects the system.
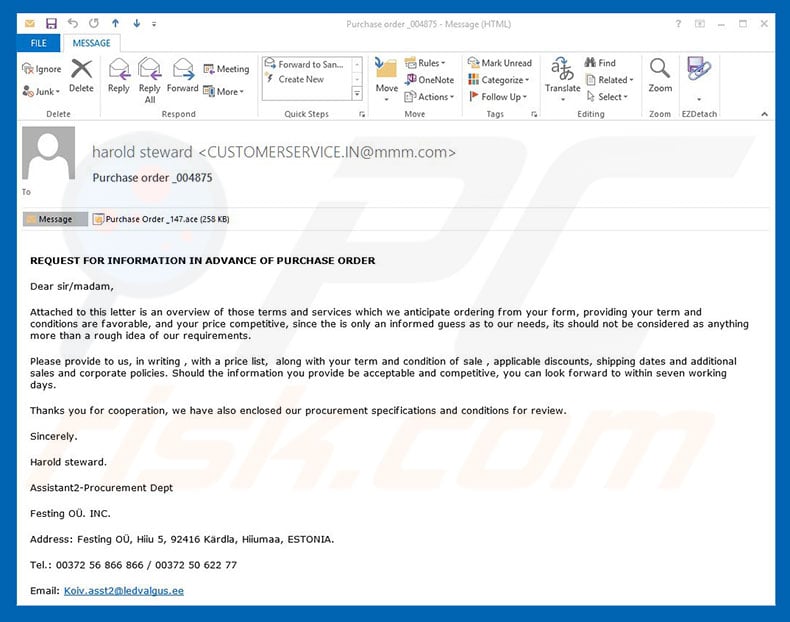
"Purchase Order Email Virus" overview
"Purchase Order Email Virus" campaign emails contain a message encouraging users to read an overview (in the attached file) of a purchase. This is a scam - the opened document downloads and installs Pony trojan onto the system. The email may seem official, but this is an attempt to give the impression of legitimacy.
Cyber criminals often hide behind names of legitimate companies or governmental agencies to increase the number of infections. Users are much more likely to open files that are received from familiar names. Pony is high-risk information collection malware.
This virus is capable of obtaining logins/passwords saved in over a hundred applications, including web browsers, FTP clients, VPNs, and so on. Cyber criminals might gain access to victims' personal accounts in social networks, banks, etc.
These people aim to generate as much revenue as possible and are very likely to misuse hijacked accounts to achieve their goals (online purchases, money transferring, etc.). The presence of an information-tracking trojan such as Pony can lead to financial loss and even identity theft.
If you have already opened "Purchase Order Email Virus" campaign's attachments, immediately eliminate all suspicious applications and browser plug-ins.
| Name | Purchase Order spam |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Spam-proliferated malware examples
Pony shares many similarities with Adwind, FormBook, TrickBot, LokiBot, Emotet, and dozens of other trojan-type viruses. Most are distributed using spam email campaigns and gather sensitive information. In some cases, however, these trojans (e.g., Hancitor), proliferate other viruses, thereby causing chain infections.
In any case, all pose a significant threat to your privacy and computer safety, and thus removing them is extremely important.
How did "Purchase Order Email Virus" infect my computer?
This email campaign proliferates an archive (.ace) of files by presenting it as a file detailing purchase information. In fact, the compressed files are malicious - executing them results in infiltration of the Pony trojan. Fortunately, this malware targets the Microsoft Windows Operating System only and users of other platforms (e.g., Linux, MacOS, and so on) are safe.
How to avoid installation of malware?
To prevent this situation, be very cautious when browsing the Internet. Carefully analyze each email attachment received. Irrelevant files and those received from suspicious/unrecognizable email addresses should never be opened.
Furthermore, have a reputable anti-virus/anti-spyware suite installed and running, since these tools are likely to detect and eliminate malicious files before they perform any actions. Lack of knowledge and careless behavior are the main reasons for computer infections.
The key to safety is caution. If you have already opened a "Purchase Order Email Virus" attachment, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "Purchase Order Email Virus" email message:
Subject: Purchase order
REQUEST FOR INFORMATION IN ADVANCE OF PURCHASE ORDER
Dear sir/madam,
Attached to this letter is an overview to those terms and services witch we anticipate from your form, providing you term and conditions are favourable, and your price competitive, since the is only informed guess as to our needs, its should not be considered as anything more than a rough idea of our requirements.
Please provide to use, in writing, with a price list, along with your term and condition of sale, applicable discounts, shipping dates and additional sales and corporate policies. Should the information you provide be acceptable and competitive, you can look forward to within seven working days.
Thanks you for cooperation, we have also enclosed our procurement specifications and conditions for review.
Sincerely,
Harold stewad.
Assistant2-Procurement Dept
Festing OU. INC
Address: Festing, OU, Hiiu 5, 92416 Kardla, Hiiumaa, ESTONIA
Pony trojan process in Windows Task Manager:

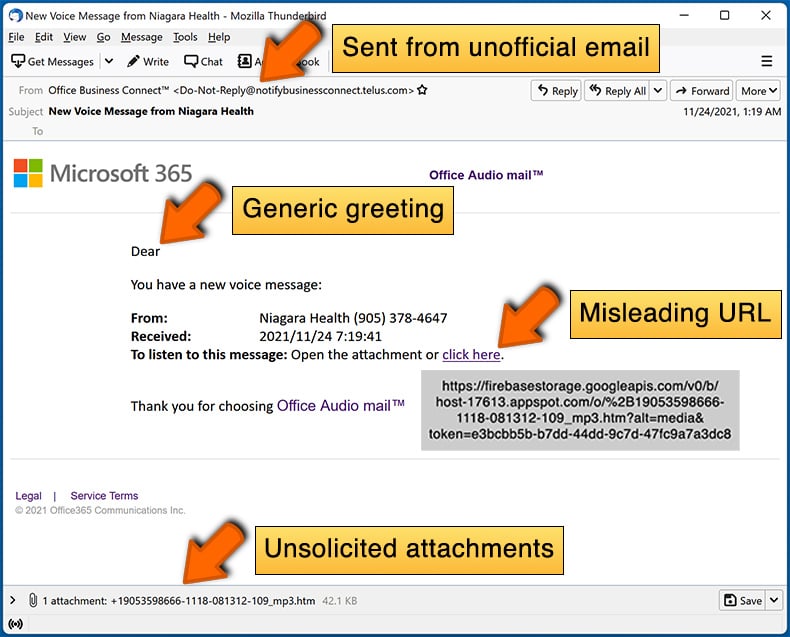
Another variant of "Purchase Order" email spam campaign. In this case, the spam emails are used for phishing purposes - emails contain links to malicious/unreliable websites with an intention of extracting various valuable information or tricking recipients into downloading files:

Text presented within this email:
Subject: PO0000110 - Purchase Order
Hi
My name is Whitney, and we want to place an urgent order.
Please see attached our order sheet in PDF. Kindly check and give us your best price ASAP
Waiting your earliest response
Thanks and best regards
Whitney
Head, Marketing Unit
Houston General Trading L.L.CSharjah Expo Business Centre, 1st FLoor
Al Taawun, Sharjah
PO Box 26676
__
1=Attachment ~ 253.kb
View Online | Download
__
Yet another example of Purchase Order-themed spam email promoting a malicious executable (NanoCore RAT):

Text presented within:
Subject: PURCHASE ORDER
Good day.
We are in urgent need of attached listed products, kindly refer to attached purchase order and acknowledge in return.
Kindly advise delivery date, please send your PI immediately for advance payment.
Thank you.
Best Regards,Choo Siew Fern
Purchase ExecutiveAl kabous group Limited
Al-Qaser Street. Al-Kbous Building
No. (1) Beside The Cultural House,
Sana'a - Rep. of Yemen
Tel: +967 1 270800
Fax: +967 1 275014
Email: commercial@alkbousgroup.com
trading@alkbousgroup.com
Yet another example of purchase order-themed spam email used to spread malware (njRAT):

Text presented within:
Subject: Purchase Order SACOM_413128
Hello,
Good day,
With reference to above subject kindly find the attached Purchase Order SACOM_413128
Please confirm.
Could you please update me the best possible ship date ?
Best regards,
Truong Cong Anh
Purchase / Pricing Specialist
JOINT STOCK TRADE AND VALUATION COMPANY - SACOMVALUE
REPRESENTATIVE office in Hanoi: Floor 4, 80 Chua Lang,
dong da District, ha noi CITY. Ha Noi
Tel: (024) 32298404
Email: purchase01@sacomvalue.com.vn
Tax code: 0311748870
Yet another example of purchase order-themed spam email used to promote malware (in this case, FormBook):

Text presented within:
Subject: RE: REQUEST INVOICE
Dear supplier
Your invoice didn’t match our PO. Please check attached before we process payment.
Thanks.
Best regards,
Account Clerk | Finance Department
Another example of purchase order-themed spam email spreading Agent Tesla malware:

Text presented within:
Subject: Purchase order. Our order number PO108678 [Order]
Dear
Good day,
PO108678 as attached for your kind attention.
Please forward PI to arrange full payment.
Thank you
Syahirah
Admin Assistant
Wei Dat Steel Wire Sdn Bhd
Office: +6 05 3666220 | Fax: +6 05 3665220 |
E-mail: syahirah@weidat.com | Website: www.weidat.com
Another example of Purchase Order-themed spam email promoting an HTML attachment used for phishing purposes:

Text presented within:
Subject: [MESSAGE ENCRYPTED] Purchase Order sent to eligijus on Wednesday, October 5, 2022 1:27 p.m.
Hi - ,
Attached PO for your reference.
Pls check new order as excel or pdf file and arrange sending Proforma Invoice for payment, then shipment urgently to us.
Thanks!
请检查单价,如有问题请于两天内提出。
Meng Engly
MP| Purchasing
M: +855 97 835 3804
hxxp://www.epfootwear.com
Binhjhun Production Zone, Binhjhun County,
Thuan An City,
Binh Duong Province,
Vietnam
Screenshot of the distributed HTML document:

Yet another example of purchase order-themed spam email spreading a malicious MS Word document:

Text presented within:
Subject: 1st time Purchase order (P.O.)
Dear -,
Please find attched 1st time Purchase Order (P.O.) for your action.
Confirm the avaliablitiy and possible delivery before december
Thanks & Regards
Screenshot of the attached MS Word document:

Yet another example of purchase order-themed spam email spreading a malicious MS Excel document:

Text presented within:
Subject: ARIX SRLVl PURCHASE ORDER 22567
Good day,
Please find attached PO in document and also take note of the underline
items in RED COLOR.Please kindly revert with proforma,
Should you have any queries please do not hesitate to contact us.Kind Regards
Valentini LuizExport Manager EU & Overseas Markets
ARIX SRLVl (MN) - Italy
CF e P.IVA IT 006 24 60 05 07
Tel. +39 0375 832 111 - fax +39 0375 780 304
Mob. +39 342 70 32 852
euoverseas@autoflex.it
Screenshot of the malicious MS Excel document used to inject Formbook into the system:

Yet another example of purchase order-themed spam email spreading malware:

Text presented within:
Subject: Proof of Payment
Greetings,
We would like to inform you that we have made a pay-ment of (47,000 USD) Forty Seven Thousand (USD) by wire transfer to your towards the amount outstanding on your in-voice 785635 dated Sept 12 2022 for the supplier of Goods to my company .We we release the balance pay-ment post-delivery of ordered goods to us as agreed under the purchaseorder.
Kindly acknowledge the receipt.
Yours Faithfully
Thomas Valdes
Accounting
Yet another example of Purchase Order (PO)-themed spam email spreading a malicious PDF document:

Text presented within:
Subject: 1 New File Received (PO# -00004092)
Hello there,
Please find attached PO along with Trade Reference and W-9 as well.
I will appreciate a reply at your earliest convenience.
Best Regards
Abraham Phillips
General Manager
Jones Memorial Hospital
191 North Main Street, Wellsville, NY 14895
shainalukas@yahoo.com
315-633-4857
Screenshot of the attached PDF document which redirects users to a phishing site:

An example of purchase order-themed spam email promoting a phishing site:

Text presented within:
Purchase Order NH-PO-7528 / Sales Contract Documents
sent to
-
1 item, 6090.35 KB in total · Available for download
Get your files
1 item
Documents.pdf
Folder·1 item
Another example of purchase order-themed spam email promoting a phishing site:

Text presented within:
Subject: New_Order#SQ031776
Dodwell Sample List003211.pdf
Purchase_Order_Enquiry.pdf
You have received some files via Pdf files.
2 item, 1.4MB in total ・ Expires on 29 February, 2023
Download Pdf files
2 Items
Purchase order.pdf
18.2 KB
Specifications.pdf
6.17 KBTo make sure our emails arrive, please add noreply@Download your Pdf to your contact.
Yet another example of an email from "Purchase Order" spam campaign:

Text presented within:
Subject: Urgent Order 4772137
Good day -,
Kindly refer to the attached our purchase order and provide us with a Quotation of your best prices.
Best regards .
Sales Manager
Brite Recruitment Ltd
PDF Purchase Order-4772137Download (14KB).pdf
Screenshot of the promoted phishing site:

Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Purchase Order spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:
What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal. Cyber criminals send thousands of them, hoping that at least some of the recipients will fall for their scam. Therefore, many users receive identical letters.
I have read this spam email but didn't open the attachment, is my computer infected?
No, merely reading a spam email will not trigger any malware download/installation processes. Infection chains are jumpstarted when the attachments or links in such letters are opened/clicked.
I have downloaded and opened a file attached to this spam email, is my computer infected?
Whether an infection occurred - depends on the file's format. If it was an executable (.exe, .run, etc.) - most likely, yes - your system was infected. However, if it was a document (.doc, .xls, .pdf, etc.) - you might have avoided malware infiltration. In some instances, document formats require additional user interaction (e.g., enabling macro commands) - to begin downloading/installing malicious software.
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner can detect and eliminate most of the known malware infections. It can also scan downloaded files for malicious content. It must be emphasized that sophisticated malware usually hides deep within systems - therefore, running a full system scan is crucial.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion