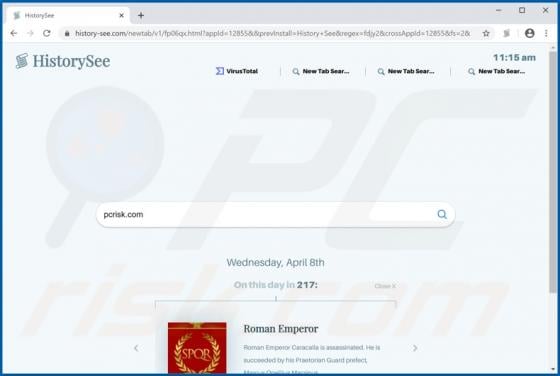
HistorySee Browser Hijacker
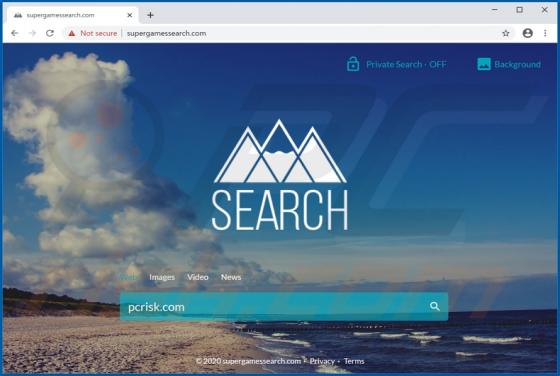
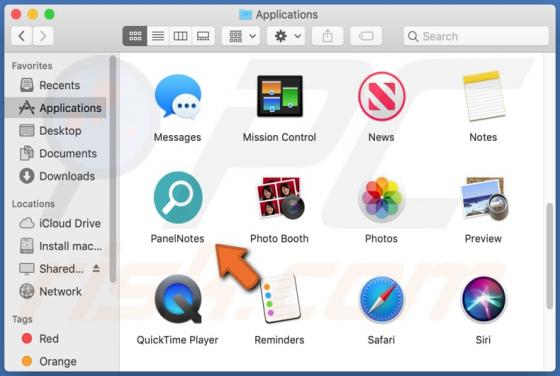
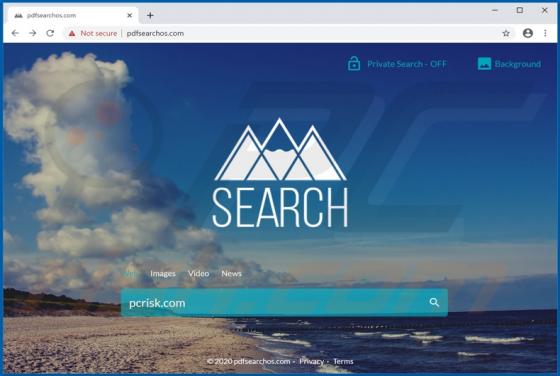
HistorySee is a browser hijacker supposedly capable of providing daily historical facts. This piece of software modifies browsers to promote history-see.com (a fake search engine). Additionally, HistorySee monitors users' browsing habits. Due to the dubious methods used to proliferate this browser