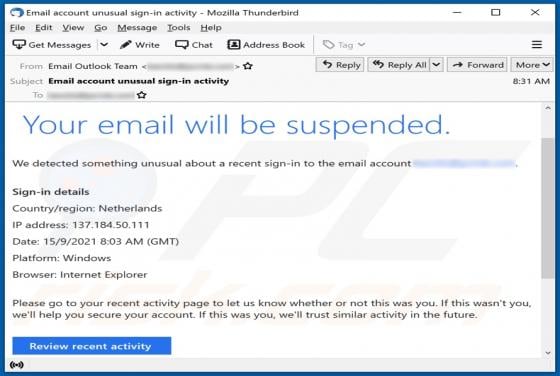
Your Email Will Be Suspended Scam
"Your email will be suspended Scam" refers to a spam campaign. These letters are presented as notifications concerning an impending suspension of the recipients' email accounts due to detected suspicious activity. The goal of the scam emails is to trick users into attempting to sign into their ema