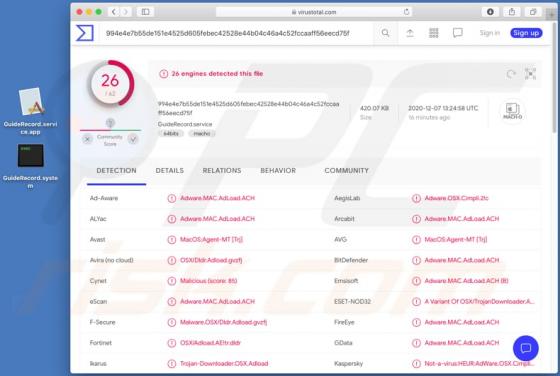
GuideRecord Adware (Mac)
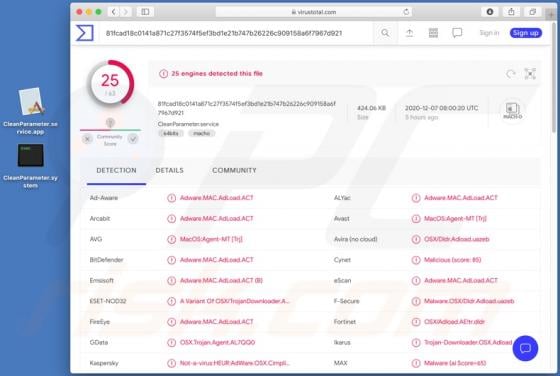
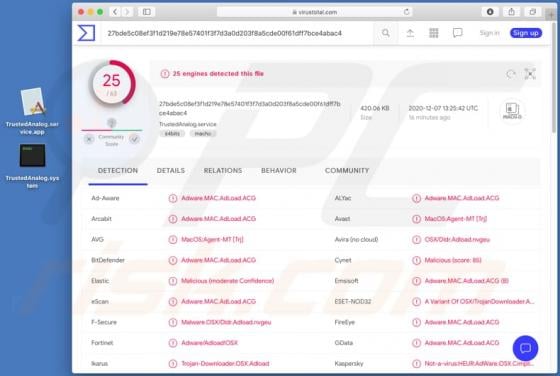
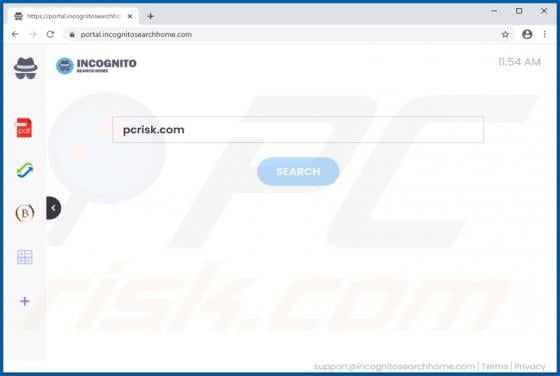
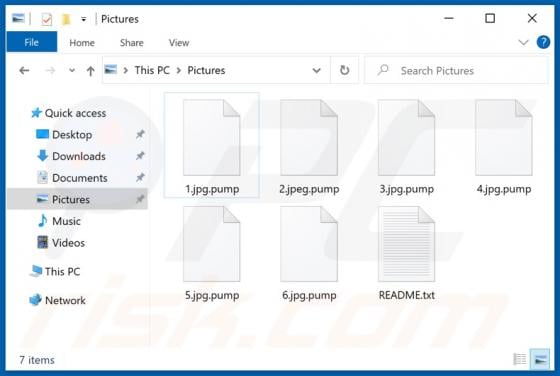
GuideRecord serves advertisements, modifies browser settings and possibly collects browsing details (and other) data. Therefore, this app functions as adware and as a browser hijacker. People mostly download and install apps such as GuideRecord inadvertently and, therefore, they are classified a