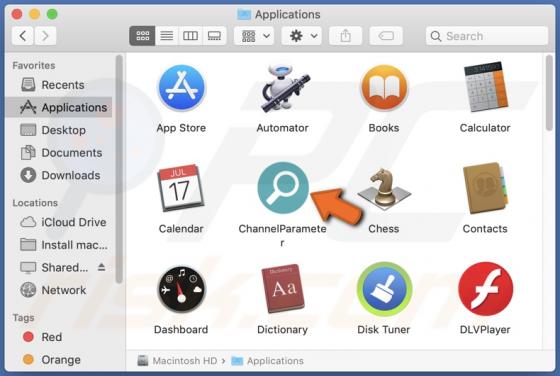
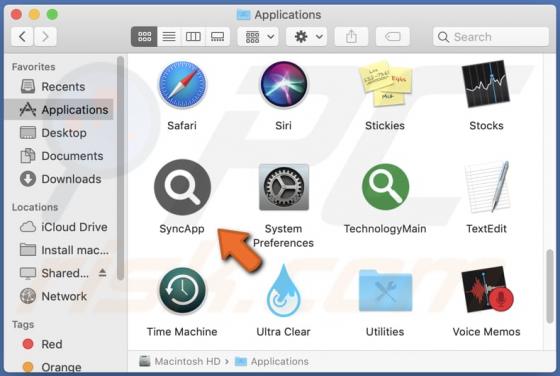
ExtendedRotator Adware (Mac)
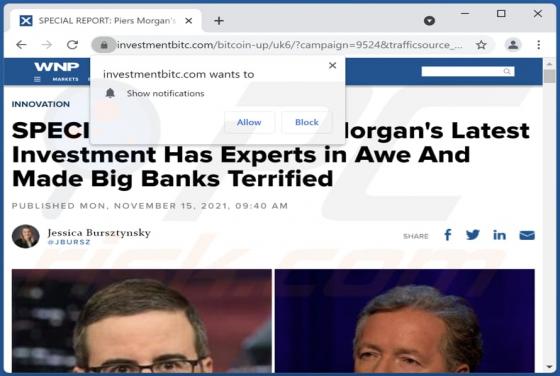
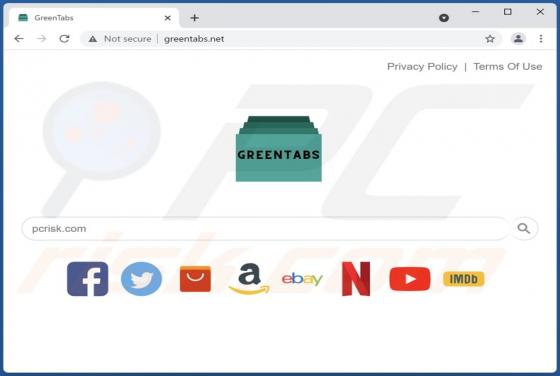
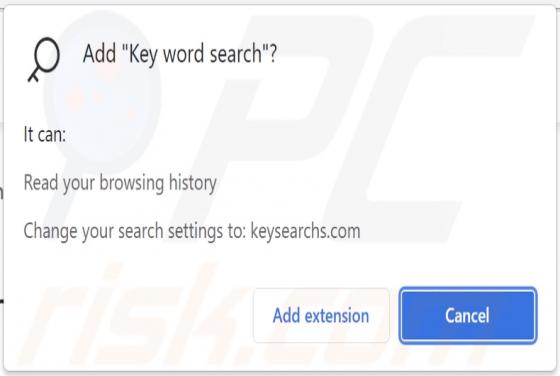
ExtendedRotator generates advertisements and hijacks a web browser to promote a fake search engine. The majority of users install apps like ExtendedRotator inadvertently. Apps installed (and downloaded) in such circumstances are called potentially unwanted applications (PUAs). Advertisem